In 2020, Australians lost over $850 million to scams. A new report by the Australian Competition & Consumer Commission found phishing was the most reported type of scam across the country, rising to “unprecedented levels” in comparison to 2019. “Phishing activity thrived during the pandemic. Over 44,000 reports were received, representing a 75% increase,” the report stated.
While phishing scams have been around for several decades (the notorious Nigerian Prince scam is an early example), their continued success at bringing down organisations show us that we’re dealing with an adversary that is continuously evolving its’ tactics to exploit systems and users. COVID-19 reminded us of this – with cybercriminals launching opportunistic phishing emails that used pandemic-themed lures to trick users. These included sending e-bulletins impersonating the World Health Organization, through to replicating government announcements about economic stimulus packages (like JobKeeper) within hours.
Many COVID-19 themed email scams worked because they exploited fears and uncertainties around the pandemic – powerful emotions that motivated users to do the emails’ bidding without pausing to check for their legitimacy.
As businesses continue navigating the unprecedented challenges brought on by COVID -19 (like remote working) phishing scams pose a more dangerous threat than ever before. Microsoft, for example, uncovered a phishing email scam targeting businesses in May this year that exploited business relationships and communications between professionals:
“Cybercriminals continue to target businesses to trick recipients into approving payments, transferring funds, or, in this case, purchasing gift cards. This kind of email attack is called business email compromise (BEC)—a damaging form of phishing designed to gain access to critical business information or extract money through email-based fraud,” Microsoft stated.
Observing a similar trend, our team at MailGuard has continued to intercept sophisticated phishing emails this year, impersonating well-known brands like DHL, Netflix and Microsoft, lulling users into a false sense of security. Playing on the fact that we’re all time-poor, with full inboxes, cybercriminals are hoping we won’t think twice about clicking emails from the brands we know and trust. Here’s our hit list of brands that are frequently mimicked by cybercriminals.
With phishing continuing to be one of the most significant risk vectors facing businesses today, here’s a refresher of the different types of phishing scams that continue to target businesses, and the type of emotions and behaviours they typically exploit in order to trick users.
Types of phishing attacks
Bulk phishing
Bulk phishing emails go to a wide group of people, and don’t target anyone group or individual specifically. It’s like a fisherman casting a wide net to see what he can catch. The attackers know that not everyone will respond, but they know that if they send enough emails out, enough people will take the bait. Emails of this nature don’t make any attempt to personalise the content.
Here's a recent example of a bulk phishing email purporting to be from DHL, simply addressed to “Dear Customer”:
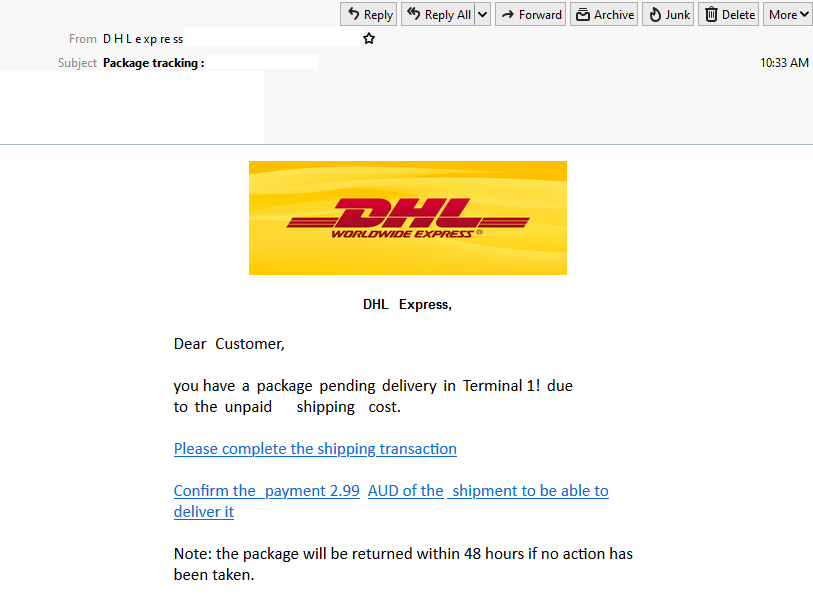
Emails like these work because they are unexpected. Because it’s human nature to be curious, we click on unfamiliar links in seemingly intriguing email messages, even if they are not addressed directly to us. In this case, scammers attempt to convince users that there actually is an unexpected package waiting to be delivered to them by DHL. We all love getting something (aside from a bill) in the mail, and with online shopping more popular than ever, it’s sometimes hard to keep track of what parcels we’re expecting. Cybercriminals know this, and prey on people’s busy lives and curiosity to trick them. The inclusion of DHL’s branding – a popular global freight company – serves to convince users of the legitimacy of the email, further motivating them to click on the links within the email.
Emotions commonly triggered: Fear of Missing Out, Curiosity, Excitement
Spear phishing
Spear phishing scams target a specific individual or group of people. It might be employees of a specific company, customers of a specific company, or even a specific person. The greeting is likely to be personalised, rather than a generic ‘Dear sir/madam’, and the email is designed to look like it has come from someone familiar. Here’s an example of a spear phishing email we intercepted recently impersonating popular entertainment company, Netflix:
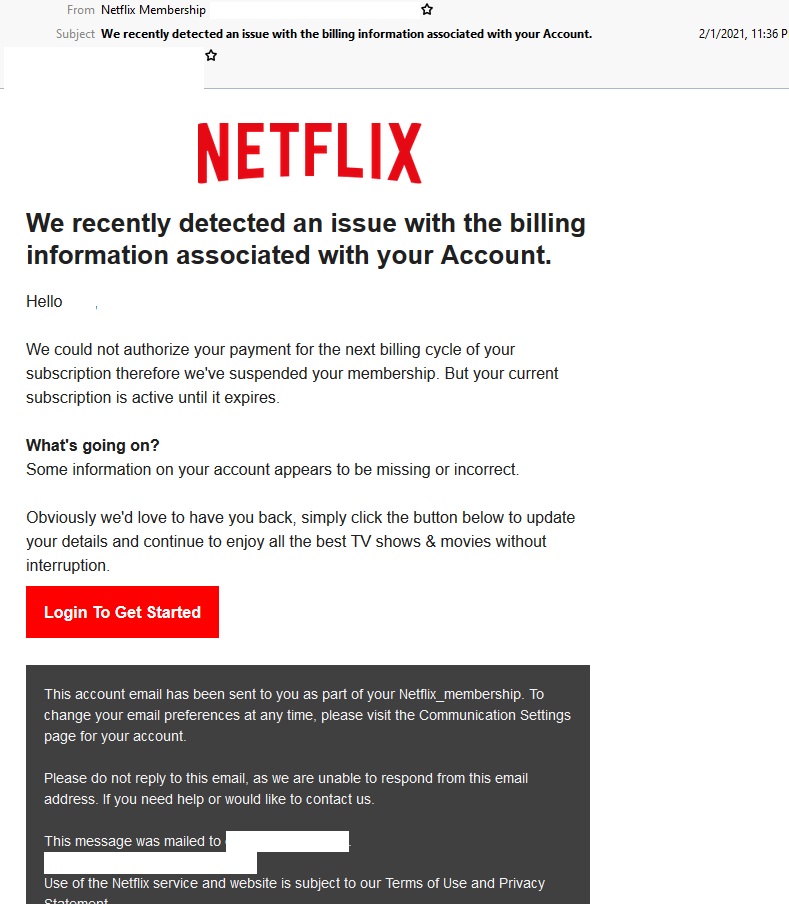
Netflix is a regular target for cybercriminals. With more than 203 million subscribers worldwide, there’s a high likelihood that many of those that are receiving the email are subscribers and that a portion of those will be too time poor to check the details in the email. The use of an alarming subject line and body informing recipients that their account has been suspended creates a sense of urgency and anxiety, motivating users to take action immediately without checking on the email’s authenticity. In addition, the mention of the recipient’s name and email address in the email body helps convince users that the email isn’t a generic notification but is actually addressed to them, further boosting its legitimacy.
Emotions commonly triggered: Anxiety, Fear, Alarm
Whaling
Whaling or Business Email Compromise (BEC) is a more complex form of spear phishing, typically impersonating influential executives. In the context of an organisation, this may be the CEO (known as CEO Fraud), other C-Suite members or even people in charge of important company resources, such as finance (the purse strings), HR (for information mining) or IT (for access to data and networks).
These attacks typically involve cybercriminals posing as senior executives or businesses via a personalised email and demanding urgent action from an unsuspecting recipient. These actions normally include making an unapproved financial transfer or revealing valuable confidential information – actions that can lead to immensely costly and serious repercussions. In 2020, Australian businesses lost $128 million to BEC scams.
We’ve seen that in certain cases of a BEC scam, there is in-depth confidential information within the email that only someone with the right authority would be privy to. This includes the company’s banking details, registration numbers, specific email addresses, and so on. Hackers may obtain this information by expanding their scope of research and gathering data on the company and individuals involved via the Dark Web or from previous data breaches. Before the first email is sent, the hackers normally conduct thorough reconnaissance to research the company. Often much of the information that the attackers require is easily available from company websites and social networks like LinkedIn.
Right now, the odds of this hack being successful are skyrocketing. Current BEC scams are exploiting the immensely fragile psychological state of many professionals who are dealing with a torrent of unprecedented challenges triggered by the ongoing COVID-19 pandemic. These professionals are likely navigating changes to work processes while working in remote environments (all against the backdrop of a global health emergency) and may not be able to immediately contact or get in touch with their colleagues to verify the legitimacy of any unexpected, urgent requests.
In the examples provided, we’ve changed the recipient and ‘sender’ details to protect their identity, but as you can see, the email appears to come from the CEO, asking the CFO to make an urgent payment:
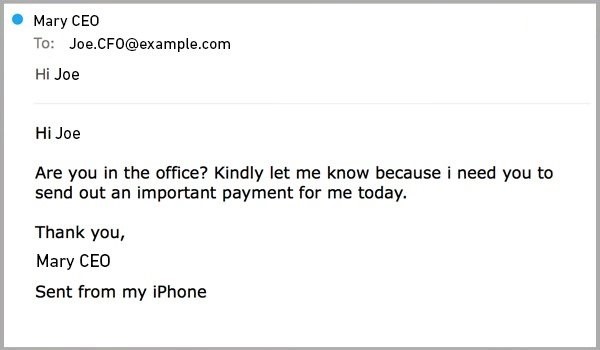
Here’s another example of a whaling attack, designed to create a sense of urgency, motivating the recipient to act quickly:
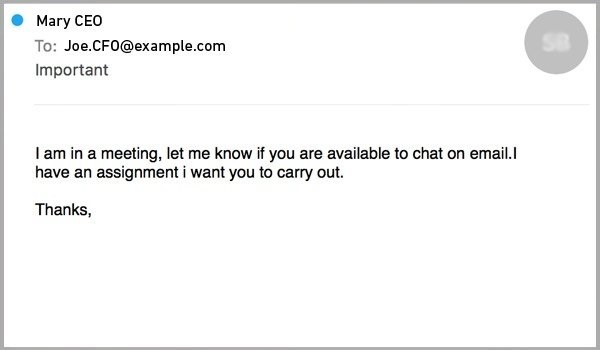
You can see how simple these scams are, yet they are extremely effective. With little time and cost invested, a cybercrime network can easily assume the identity of a high profile executive and pressure other employees within the business to make a payment or to reveal sensitive credentials.
Emotions commonly triggered: Urgency, Sense of Duty, Anxiety
Extortion phishing
Extortion phishing is a form of online blackmail via email that attempts to trick victims into handing over ransom money, often as cryptocurrency. This includes “sextortion” emails – a particular branch of extortion phishing that threatens to reveal incriminating and compromising footage or data (like videos of victims watching adult content).
Amid an ongoing pandemic like COVID-19, the conditions are just right, with people already on edge. The hallmark of these scams lies in exploiting a fragile psyche and state of mind. In cybersecurity, we see criminals continuously re-inventing campaigns to trick users and to beat the algorithms behind their email security filters. Extortion phishing scams, similarly, are often sent in waves – when one fails another emerges. And each time a threat is blocked, the scammers invent new methods to bypass the email filters that blocked them.
Here is an example of a sextortion email that our team at MailGuard intercepted:
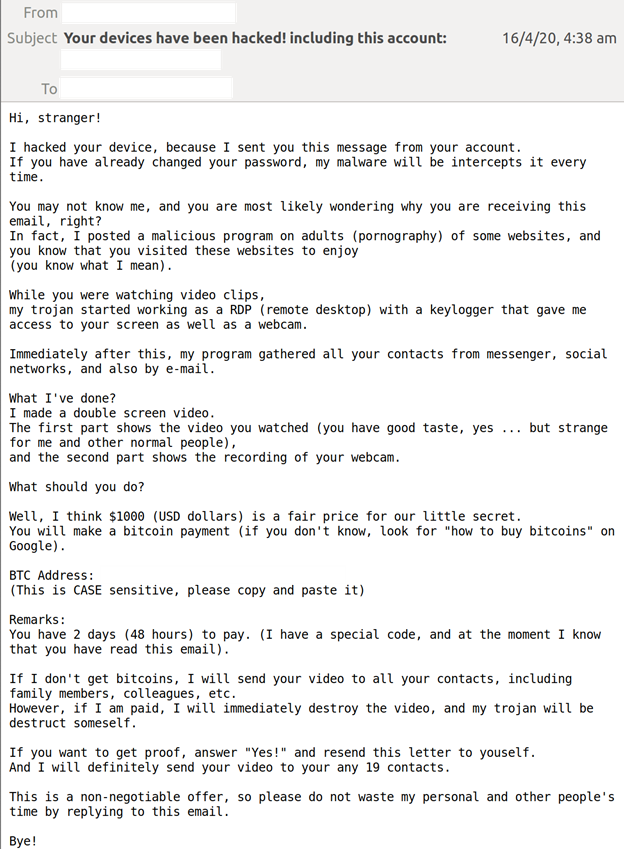
In this instance, the subject line includes the users’ email address to demonstrate that the cybercriminals have access to the account. It claims that a trojan malware installed by the hackers enabled them to record the recipient watching adult content. In other examples that we have seen, cybercriminals included users’ old passwords in the subject lines as attention-grabbing proof that their accounts have actually been hacked. Typically, these passwords are obtained from previous data breaches that have leaked mass amounts of personal information.
Most extortion phishing scams use lies, threats and high-pressure tactics to intimidate recipients. They are not the most technically sophisticated scams, but they do have the potential to be psychologically damaging, as the supposed voyeurism of these criminals infers a massive invasion of privacy.
The key thing to remember is that most of the information included in these scams is fake, and cybercriminals do not have any incriminating or personal information to use against victims. Most times it’s just a bluff. Instead of engaging with the scammers and/or paying the ransom, recipients are strongly advised to report them to local authorities as soon as they can.
Emotions commonly triggered: Shame, Fear, Restlessness, Urgency
Keeping businesses protected
Prevention is always better than a cure, and the best defence is to encourage businesses to proactively boost their company’s cyber resilience levels to avoid being hit by ransomware in the first place. The fact that a staggering 94% of malware attacks are delivered by email, makes email an extremely important vector for businesses to fortify.
No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
Fortify your defences
No one vendor can stop all threats, so don’t leave your business exposed. If you are using Microsoft 365 or G Suite, you should also have third-party solutions in place to mitigate your risk. For example, using a specialist cloud email security solution like MailGuard to enhance your Microsoft 365 security stack.
For more information about how MailGuard can help defend your inboxes, reach out to my team at expert@mailguard.com.au.






