As many of you know by now, Australian Prime Minister Scott Morrison announced in a press conference last month that Australian private & public sector companies are being targeted in a massive cyber-attack by a "sophisticated state-based cyber actor".
"This activity is targeting Australian organisations across a range of sectors, including all levels of government, industry, political organisations, education, health, essential service providers and operators of other critical infrastructure," he said.
The PM’s announcement is a wake-up call for organisations across all industries to review and enhance their existing cybersecurity strategies to meet this growing threat. Standing next to the PM during the press conference, Defence Minister Linda Reynolds reminded “all Australians that cybersecurity is a shared responsibility of us all", adding that it is "vital that all Australian organisations are alert to this threat and take steps to protect their own networks."
Detailing the nature of the attack in a new advisory, the Australian Cyber Security Centre (ACSC) has identified the actor behind this attack is utilising various phishing techniques. These include:
- Links to credential harvesting websites,
- Emails with links to malicious files, or with the malicious file directly attached,
- Links prompting users to grant Office 365 OAuth tokens to the actor, and
- Use of email tracking services to identify the email opening and lure click-through events.
It’s a warning that cybersecurity continues to be an existential threat for businesses, and that email is the number one vector of cybercrime. Nine of out 10 cyber-attacks are delivered by email, with business email compromise scams costing Australians $132 million last year. Precisely because email is a critical tool and arguably the most important means of communication among many businesses, it is imperative for businesses to consistently review their email security strategies to ensure they’re doing all that they can to stay safe.
As you continue enhancing your cyber resilience levels, we encourage you to share some real examples of malicious emails that we have intercepted recently with your team. These utilise a few of the techniques identified by the ACSC and can help improve awareness of how to identify and avoid falling victim to them.
Real examples of malicious emails utilising phishing techniques
Example 1: Phishing email spoofing Dropbox and OneDrive
In their advisory, the ACSC mention the actor behind the attack is hosting malicious documents within Dropbox and OneDrive, instead of within the email body, to trick recipients. This is a technique employed intentionally to bypass existing email security filters that normally scan email messages for malicious links.
Last month, we intercepted a similar phishing email scam spoofing Dropbox, a popular file sharing and collaboration platform among businesses. The malicious emails use a display name of “Dropbox”, and were sent from scammers using compromised Dropbox email accounts.
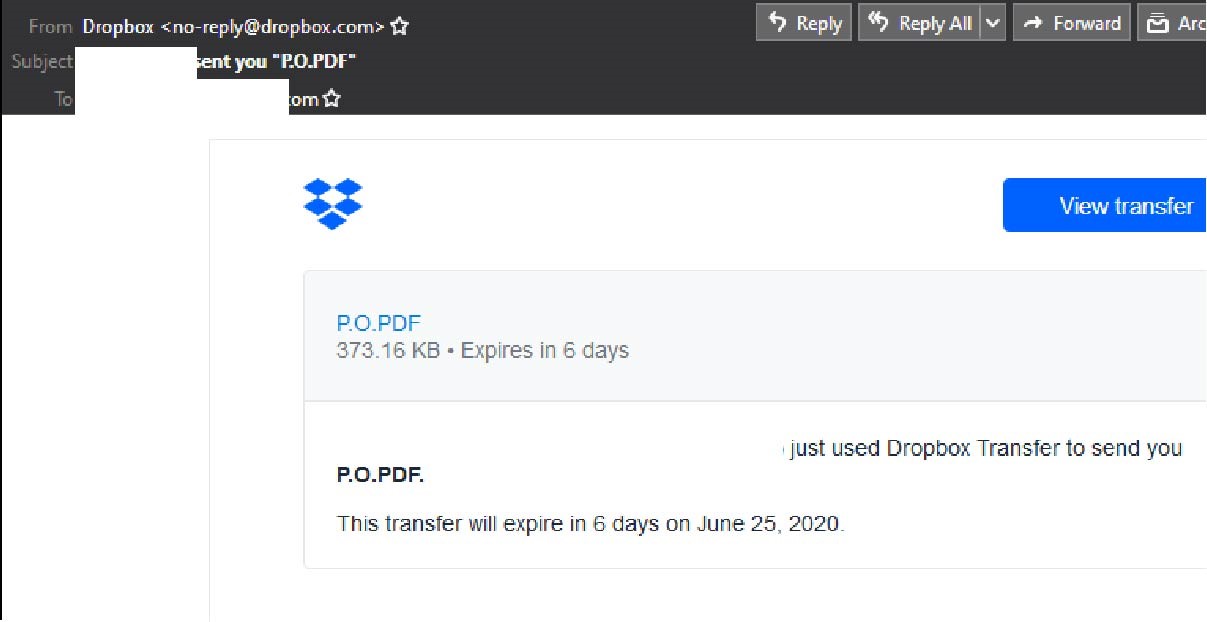
The email body contains the Dropbox logo and is designed to look like an official notification from the file-sharing platform. It informs the recipient that a file titled “PO.PDF” was sent using Dropbox Transfer, and that this file will expire within 6 days.
Here is what the email looks like:
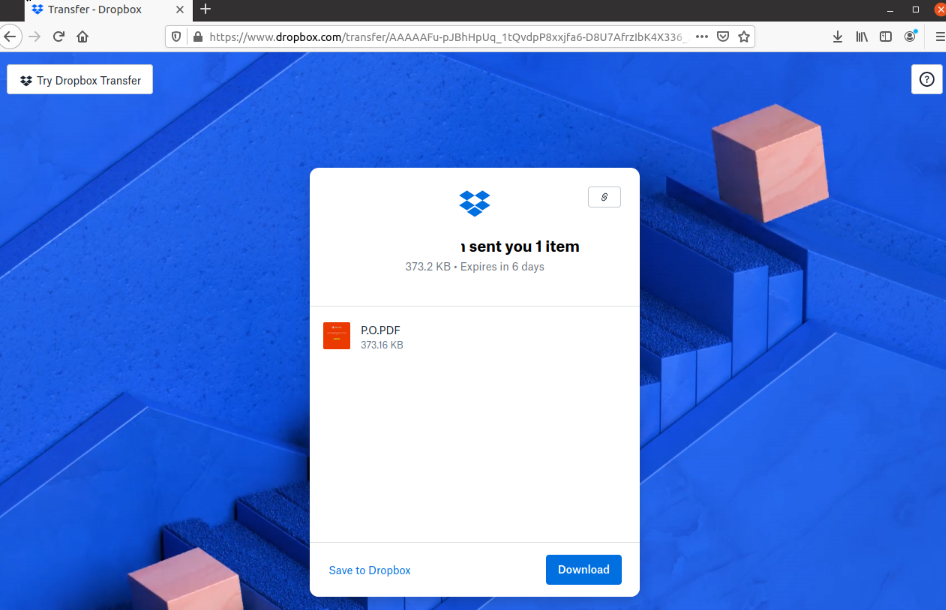
Unsuspecting recipients who click on the link to view file are led to a page hosted on the Dropbox domain. This page looks like a legitimate page from Dropbox, complete with high-quality branding elements, a URL hosted on the Dropbox domain, and links to Dropbox support pages, as per the below:
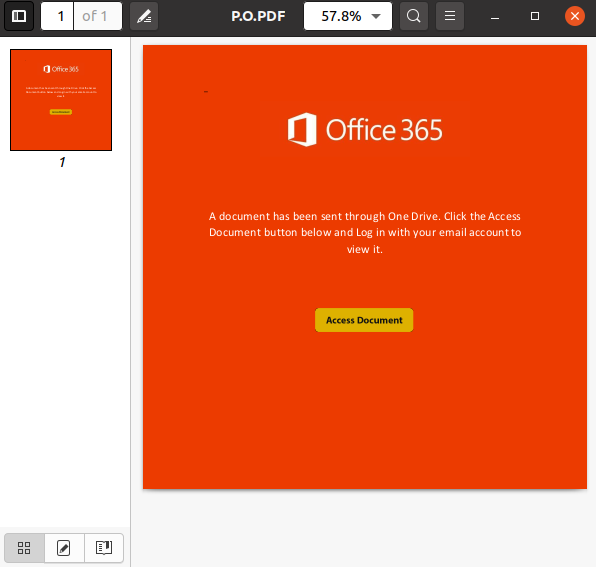
Clicking the button to “Download” initiates the download of a .PDF that contains the Office 365 logo. Users are informed that “a document has been sent through OneDrive” and are advised to click the “Access Document” button to view it.
Clicking the link to access the document takes users to another page hosted on Google Docs titled “OneDrive.” This is a phishing page designed to harvest users’ confidential details. Here, users are told to “sign in” to their email accounts to view the document:
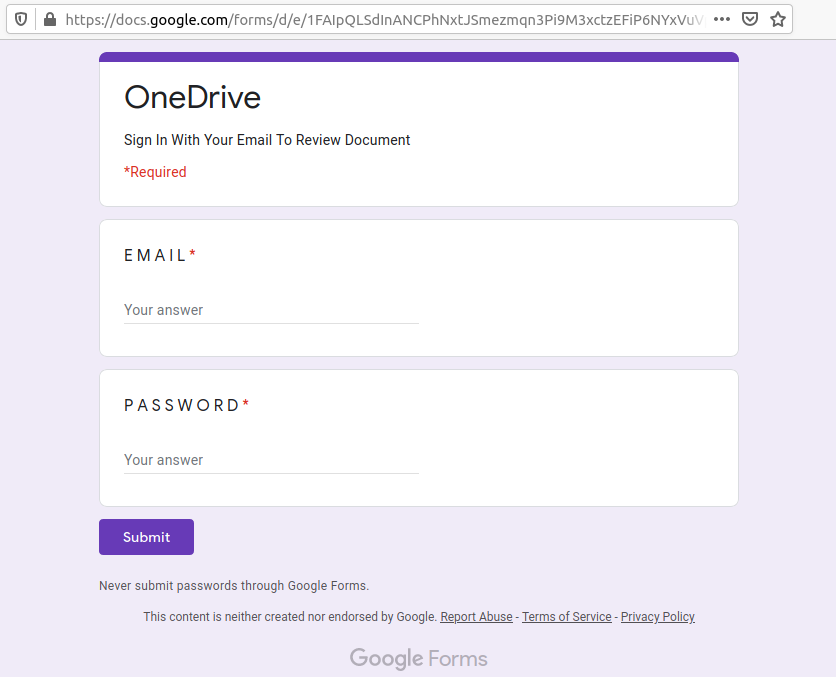
Upon “logging in”, users are finally told that their download “has automatically been saved” to their “Onedrive folder”.
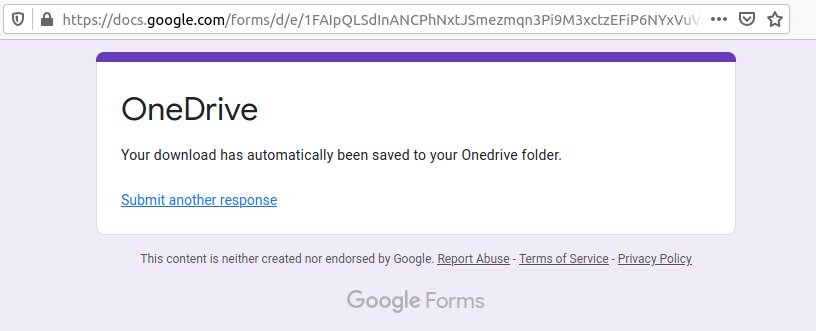
The sole purpose behind this email scam is to harvest users’ email login details when they try to access the document supposedly hosted on OneDrive. Interestingly, it is the downloaded PDF, rather than the email, that contains malicious links to the phishing page hosted on Google Docs – a technique employed intentionally to bypass email security filters.
Cybercriminals frequently exploit the branding of global companies like Dropbox and Office 365 in their scams, because their good reputation lulls victims into a false sense of security, and with such a large number of users, they are an easy and attractive target. Their established brand helps convince recipients that the files being shared via the email are secure. Since the Dropbox service requires users to click a link to view, edit or download files, they are a convenient trojan horse for malicious attacks like this one and may not raise any alarm bells.
More details of this malicious email and how it works can be found here.
Example 2: Phishing email spoofing Australian Taxation Office
As the End of Financial Year (EOFY) approaches and businesses gear up to balance their books and file tax returns, it’s not uncommon to receive notifications from the Australian Taxation Office (ATO). Taking advantage of the rise in valuable data being exchanged online, cybercriminals often use the EOFY period to exploit busy finance professionals. The ATO’s branding and logo are often mimicked via email notifications masquerading as tax errors, returns, documents and the like.
Last month, MailGuard intercepted a similar email scam spoofing the ATO, utilising some of the above-mentioned techniques mentioned in ACSC’s advisory.
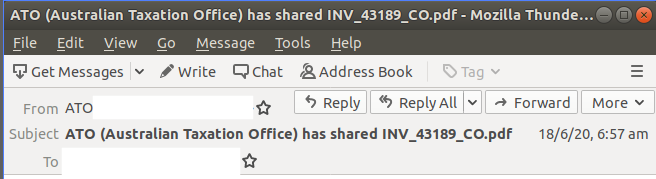
The malicious email uses a display name of “ATO”, followed by an email address beginning with “admin@”. However, the domain used in the sender email address does not belong to ATO. The email is titled “ATO (Australian Taxation Office) has shared INV_43189_CO.pdf”.
The email body includes computer software company Adobe's logo and informs users that a letter is attached "from ATO for your amount owing” and that “to avoid any interest or penalties”, the recipient should “pay the ATO by the payment deadline”.
Here is what the email looks like:
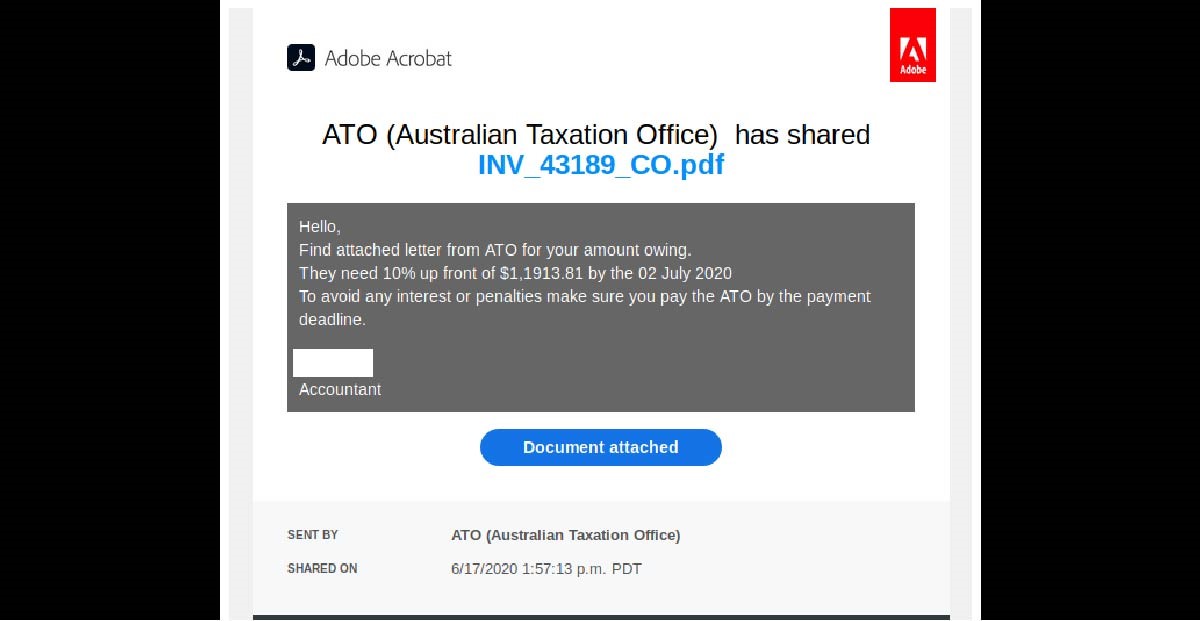
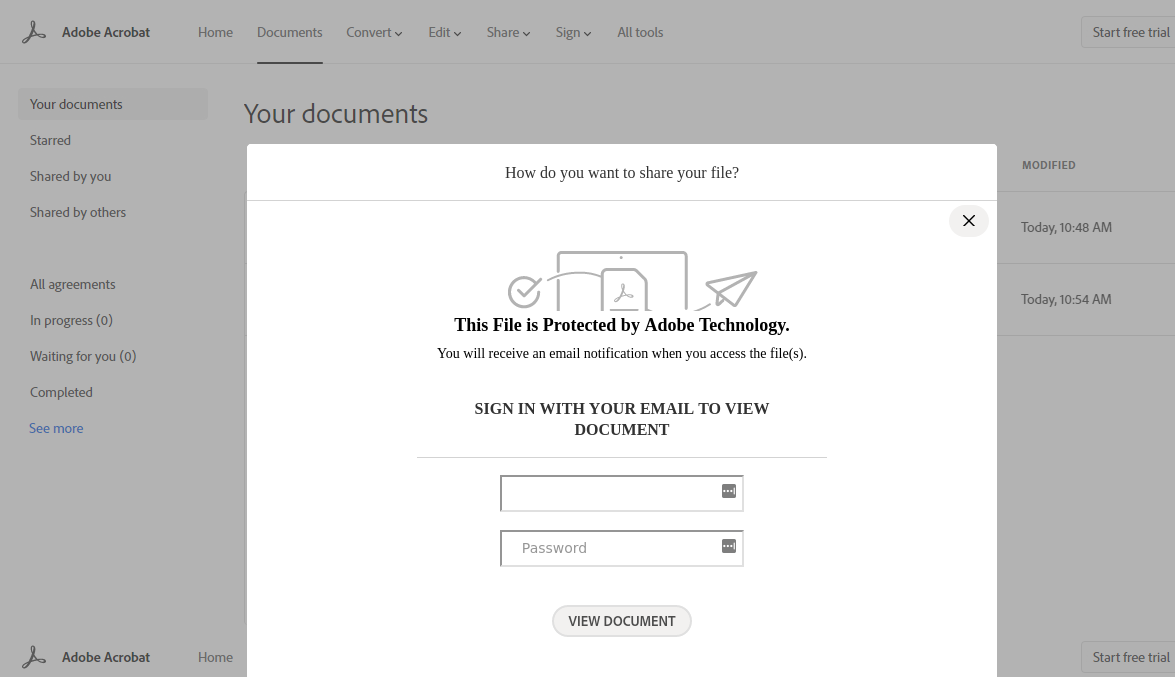
Unsuspecting recipients who click on the link to view the document are led to a page that claims "this file is protected by Adobe Technology", as per the below screenshot. To view the file, users are asked to "log in" with their email address. This is a phishing page that harvests users’ login details as soon as they insert their email address and password.
This email contains several tell-tale signs that commonly belong to fraudulent emails and should help eagle-eyed recipients point to its illegitimacy. These include the fact that the recipient isn't addressed directly, the ‘from’ field in the email doesn’t use a familiar domain and the presence of grammatical errors like: "Find attached letter from ATO for your amount owing”.
The ATO’s website includes this bit of guidance: “If you receive a suspicious email claiming to be from the ATO, do not click on any links, open attachments or respond to the sender. Forward the entire email to ReportEmailFraud@ato.gov.au without changing or adding any additional information and delete from your inbox and sent folder.”
More details about this scam can be found here.
How we can protect our businesses from these attacks
We recommend companies adopt a multi-layered approach to cybersecurity. It’s sometimes referred to as a ‘defence in depth’ approach.
As a business, you may already have native security in place from Google or Microsoft, but to protect your teams’ inboxes in this period of heightened risk, it is also prudent to adopt another layer of protection to combat email threats. For example, using a third-party cloud email solution like MailGuard to complement Office 365.
Along with technology, processes and people are all equally as important when facing cybersecurity challenges.
We’ve seen that in these situations, a strong cybersecurity culture, and awareness & education around being able to spot email scams can help. Here are a few important tips:
As a precaution, avoid clicking links in emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include. Most of the coronavirus-themed emails we have intercepted (including examples mentioned above) didn’t address the recipient directly,
- Are from businesses you’re not expecting to hear from,
- Ask you to download any files and, or
- Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from.
Ongoing education is the key to enlightening staff on the ground. This may be in the form of workshops, meetings, guest speakers, cross-functional teams, tests, and plenty of resources available on your intranet, including weekly cybersecurity updates. You can refer to external resources as well. MailGuard’s blog, for example, is regularly updated with the latest email threats that we see popping up, along with thought leadership articles on the current cyber landscape and how to navigate it.






