Defending against Business Email Compromise (BEC) attacks has long been a key component of many businesses’ cybersecurity strategies.
Also known as whaling or CEO Fraud, these attacks typically involve cybercriminals posing as senior executives or businesses via a personalised email and demanding urgent action from an unsuspecting recipient. These actions normally include making an unapproved financial transfer or revealing valuable confidential information – actions that can lead to immensely costly and serious repercussions.
But are businesses really doing enough to mitigate this very dangerous, and very real, cyber-threat?
The latest research on the issue reveals some worrying figures. The Australian Competition & Consumer Commission (ACCC) found in its newly-released Targeting Scams report that businesses in Australia lost $132 million to BEC scams in 2019. This was, in fact, the highest loss accrued across all scam types last year. The figure was much worse in the US, with the FBI reporting in its 2019 Internet Crime Report that American organisations lost US$1.7B to BEC scams last year. In addition, over a three-year period between June 2016 and July 2019, the FBI recorded 166,349 domestic and international instances of BEC, resulting in a total exposed dollar loss of over $26B.
It’s difficult to get a completely accurate representation of how big the problem is, because due to their highly targeted and personal nature, a lot of BEC attacks go unreported, so the actual number of BEC attacks and their resulting associated losses are likely to be far greater than the official published figures. What we can say with certainty is this: BEC scams continue to be an existential cyber-threat, and if we don’t proactively review & enhance our cyber defence measures, they can destroy our businesses.
In 2019, a man in Lithuania pleaded guilty to stealing $123 million by singlehandedly orchestrating widespread BEC scams that targeted Google and Facebook. By registering a fake company that masqueraded as a legitimate supplier to the two tech giants, he was able to forge invoices, contracts and letters that made his requests appear legitimate to their unsuspecting recipients.
The fact that even two of the most cutting-edge tech giants in the world are susceptible to BEC attacks should serve as a wake-up call for security teams everywhere. These are companies with vast resources and professionals who are likely to have received intensive training in being cyber-savvy. The lesson is simple – if it can happen to them, it can happen to any company, and with catastrophic and widespread consequences. Even intelligent, cyber-savvy CEOs are not safe, when targeted with a cleverly-worded, socially-engineered email. Smart cybercriminals understand this and often target not only professionals within companies, but specifically CEOs of those companies, knowing they are custodians of large amounts of money & valuable data and are hence lucrative targets.
The threat is real and evolving
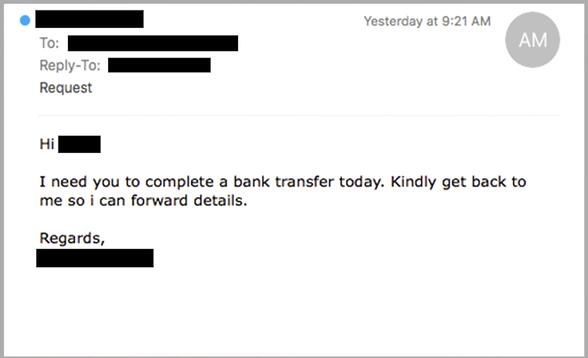
Unfortunately, the chances of this happening are exploding amid the volatility of current times. A BEC attack essentially plays on the psychology of the target. By mimicking a high-ranking executive for example, cybercriminals utilise the power and influence the executive holds to drive immediate, unquestioning action from the target. These attacks are very much a hack against humans, rather than against a computer. And right now, the odds of this hack being successful are sky-rocketing. Current BEC scams are exploiting the immensely fragile psychological state of many professionals who are dealing with a torrent of unprecedented challenges triggered by the ongoing COVID-19 pandemic. These professionals are likely navigating changes to work processes while working in remote environments (all against the backdrop of a global health emergency) and may not be able to immediately contact or get in touch with their colleagues to verify the legitimacy of any unexpected, urgent requests. It won’t be surprising for someone in the finance department to receive an email, supposedly from the CEO, requesting an unexpected bank transfer, like the below:
And this is already happening. Our team at MailGuard are seeing a rise in multi-staged and well-planned BEC attacks. Cybercriminals behind these scams are developing increasingly sophisticated techniques that often include a combination of social engineering, email spoofing and malware.
For example, we’ve seen that in certain cases of a BEC scam, there is in-depth confidential information within the email that only someone with the right authority would be privy to. This includes the company’s banking details, registration numbers, specific email addresses, and so on. We’ve found hackers are obtaining all this information by expanding their scope of research and gathering data on the company and individuals involved via the Dark Web or from previous data breaches. Before the first email is sent, the hackers normally conduct thorough reconnaissance to research the company. Often much of the information that the attackers require is easily available from company websites and social networks like LinkedIn. The scammers are able to gather the organisational structure, contact details, location and role titles of executives and employees.
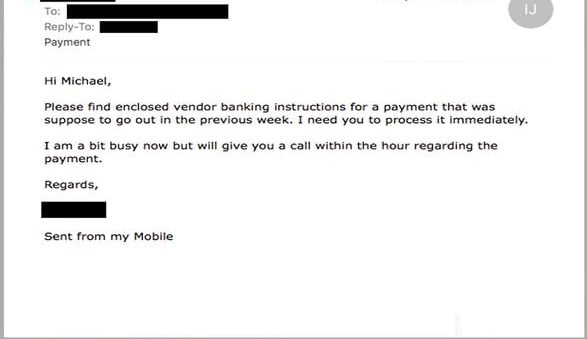
They are also getting increasingly opportunistic, being more conscious of local trends, current news and climates. For example, as tax time approaches for Australians, BEC scams typically tend to rise as requests for tax forms and sensitive financial information normally escalate in this period. Taking advantage of this, cybercriminals tend to imitate or exploit CFOs due to their influence over financial matters, as per the below example:
Specifically, during this period, we have also seen BEC scams that deviate from simple plain-text emails without any attachments to those spoofing popular accounting software such as Xero or MYOB with well-designed invoices demanding payment.
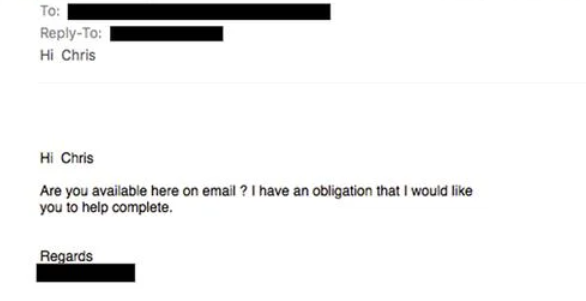
The structure of BEC attacks is also changing. For example, we’ve seen that in some BEC scams there is no damaging action required in the first email sent to the recipient. The first email is simply trying to establish a dialogue and determine if the target is available, as in the below example. The request for a funds transfer, for instance, is made in follow-up emails.
Scammers are also investing more time and effort into producing communications which look and sound more authentic. In some instances, senior graphic designers and/or legal experts are being employed by cybercriminals to design contracts and use high quality branding within emails.
Defending your business from BEC scams
Cyber-attacks like these are unique in that they leverage not only on technical weaknesses of trusted systems, but also heavily on people’s normal behaviours, their psychology and state of mind. To avoid getting tricked by these attacks, here are three tips you and your teams can follow:
1) First, take your time- If you have received an unexpected email, check who it was sent by. Examine the sender or reply-to address and check that it hasn’t been sent from a similar, but recently-registered domain such as example.com instead of example.com.au. Be alert for strange sentence structure, or phrasing uncommon to the apparent sender
- Ensure a formal payment or transfer process is well communicated within the entire office. If employees are ever in doubt about transferring funds, ring the apparent sender on a known number. If they’re not available, wait until they are. An enormous transfer is better to arrive later than to be lost without a trace to an overseas cybercriminal.
- Implement scam-proof approvals processes for financial transfers such as two-factor authentication, which requires two employees to sign off on wire transfers.
- Education is key. Ensure all employees are aware of the formal transfer procedure in place and what to do if they ever received unusual requests.
- Teach staff and employees what fraudulent emails look like. Show them real-life examples of BEC attacks that have been occurred in the past and question them on how they would have responded to the scam emails. Executives should also learn to take special care when posting and sharing information related to work schedules on social media sites.
3) Implement multi-layered security
- We highly recommend companies take a strategic, multi-layered approach when it comes to email security. It’s sometimes referred to as a ‘defence in depth’ approach, designed to defend a system against attacks using several different methods and solutions, in the event that if one fails, the others will stop the threat.
- No one vendor can stop all attacks. While most firms will have native security from their email hosting provider, like Google or Microsoft, since we know that nine out of 10 attacks start with an email, it’s also prudent to employ an additional layer of cloud email security with a solution like MailGuard, that is a specialist at stopping advanced, zero-day threats.
Let this article be a reminder of the need to ensure your business’ cyber defence strategy encompasses all the elements required to beat today’s evolving & sophisticated BEC scams. Have a conversation with your CISO about the above suggestions to see which are best for your company.
What are you doing in your business to defend your systems against BEC scams? Comment below.






