“I am a hacker who has access to your operating system. I also have full access to your account. I’ve been watching you for a few months now. The fact is that you were impacted with malware through an adult site that you visited.”
These are the chilling opening words taken from an actual email we intercepted recently, designed to instil fear and panic into anyone that reads them. The aim? To manipulate the recipient to do the email’s bidding without a second thought.
Welcome to extortion phishing – a form of online blackmail via email that attempts to trick victims into handing over ransom money, often as cryptocurrency.
And right now, these scams are creating a significant buzz worldwide. Including “sextortion” emails – a particular branch of extortion phishing that threatens to reveal incriminating and compromising footage or data (like videos of victims watching adult content).
A newly released report by SophosLabs identified unusual spikes in sextortion spam message traffic sent worldwide between Sept 1, 2019 and Jan 31, 2020, that generated nearly a half-million US dollars in profits for Internet criminals. A warning has also recently been issued by Police Scotland after an email sextortion scam targeted a large number of people across the country, and a similar spike was reported in Malaysia, and in Australia where the Australian Cyber Security Centre revealed earlier this month that it too had received more than 1900 reports in just one week.
Paul Fletcher, Australia’s Minister of Cyber Safety issued a statement warning of “an alarming spike” in sextortion scams: “Australia’s eSafety Commissioner has recorded an increase of up to 300% in some areas of internet harm, including social ‘sextortion’. The spike largely relates to a new scam, which threatens to release intimate videos captured on webcams unless a payment is made,” he stated.
Extortion phishing scams aren’t new. According to the FBI’s Internet Crime Compliant Center (IC3), complaints of digital extortion in 2018 rose 242% to 51,146 reported crimes, with total losses of $83 million. 2019 saw even bigger losses of over US $107 million.
It’s no coincidence that authorities are reporting a rise in extortion phishing. Amid an ongoing pandemic like COVID-19, the conditions are just right, with people already on edge. The hallmark of these scams lies in exploiting a fragile psyche and state of mind. In cybersecurity, we see criminals continuously re-inventing campaigns to trick users and to beat the algorithms behind their email security filters. Extortion phishing scams are often sent in waves – when one fails another emerges. And each time a threat is blocked, the scammers invent new methods to bypass the email filters that blocked them.
To help you and your teams stay protected against these scams, we’ve compiled a list of some trending extortion phishing emails that are infiltrating inboxes. Share these with your teams to make them aware of the threat:
Sextortion email scams
Sextortion scams attempt to blackmail victims by telling them that sensitive, often deeply personal and embarrassing information has been obtained and threatening to publish the content unless a ransom payment is made in bitcoin.
Here is a summary of what these emails typically include:
- ATTENTION! We implanted malware on your computer, which means we have been keeping tabs on you, including grabbing your passwords and getting access to your accounts.
- We also used this malware to film you via your webcam and to take screenshots of your browser.
- We made a video of you on a porn site with the screenshots and the webcam footage side-by-side.
- Oh, and the clock is ticking, so pay us some money pretty darn quickly or we’ll send the video to your friends and family. (We know who they are, because we have your passwords, remember?)
The extortion demand is typically somewhere from $700 to $4,000, payable to a bitcoin address provided in the email.
(via SophosLabs)
Here is an example of an actual sextortion email that our team at MailGuard intercepted last week. In this instance, the subject line includes the users’ email address to demonstrate that the cybercriminals have access to the account. It claims that a trojan malware installed by the hackers enabled them to record the recipient watching adult content.
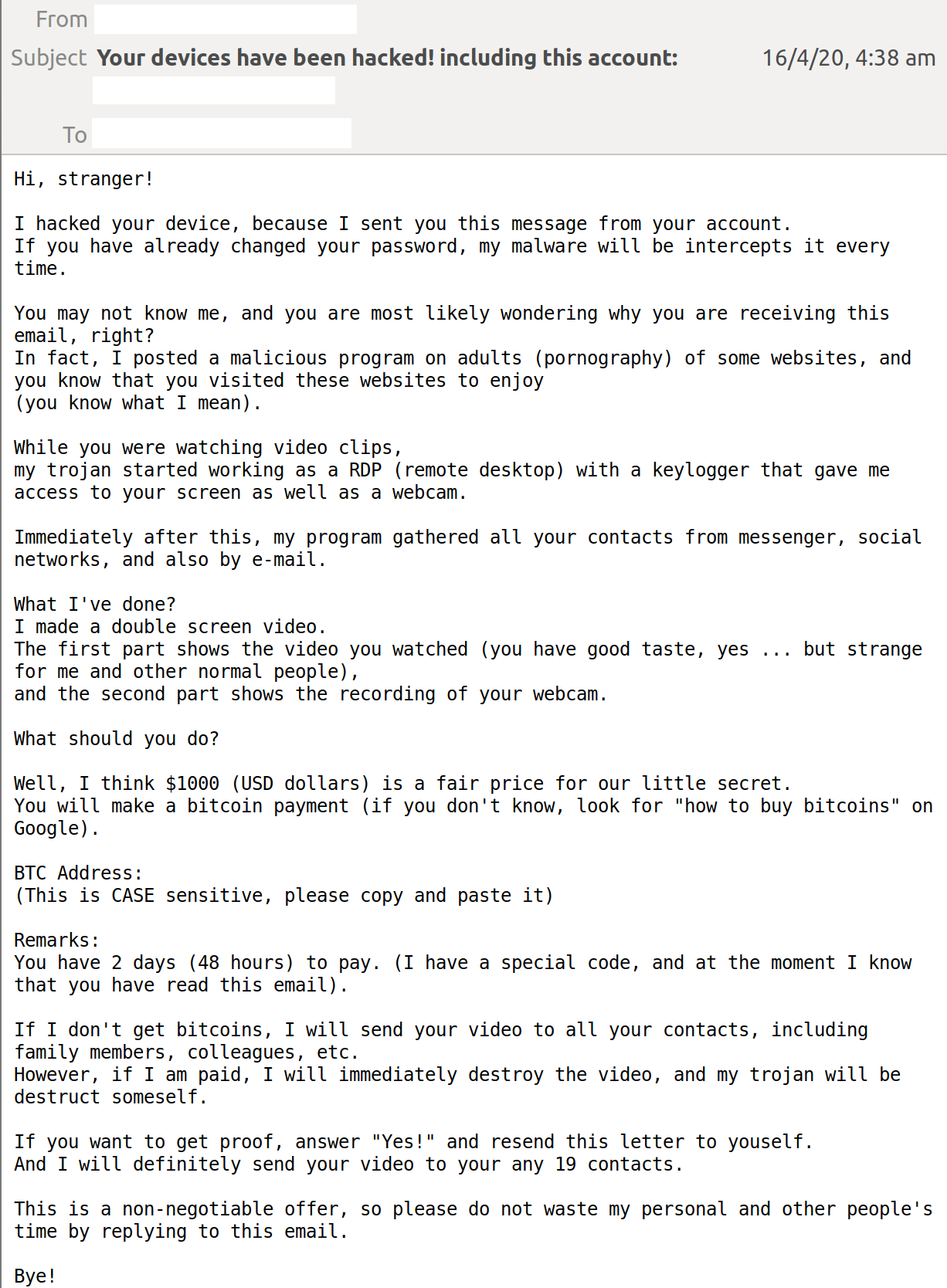
In other examples that we have seen, cybercriminals included users’ old passwords in the subject lines as attention-grabbing proof that their accounts have actually been hacked. Typically, these passwords are obtained from previous data breaches that have leaked mass amounts of personal information, including those from large and well-established companies like Yahoo, eBay, and Sony PlayStation. Data stolen from these companies is often available on the black market for sale.
According to the Krebs on Security blog, recipients of similar scams in the past have observed that the password included in the message was old, some by about a decade, and not currently in use. For those users who haven’t changed their passwords in years, the scam could appear more realistic, and the hustle itself may become fine-tuned as the scammers weave in fresher bits of stolen user data.
Extortion phishing scams exploiting COVID-19
Cyber-attacks exploiting fears around the virus have exploded in frequency, intensity and variety – and it’s no surprise that these include extortion emails.
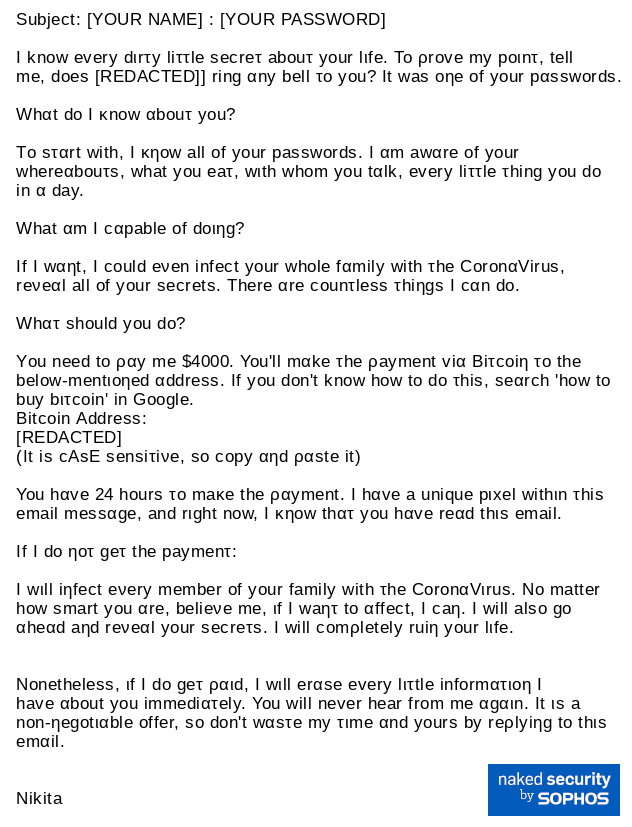
Below is an example published by Sophos. The format of the email is similar to other extortion phishing emails, beginning with proof that the recipient’s password has been obtained, along with “other secrets”. The email threatens recipients to “infect every member of your family with the CoronaVirus” unless $4,000 is paid via bitcoin.
Extortion phishing emails using QR-codes
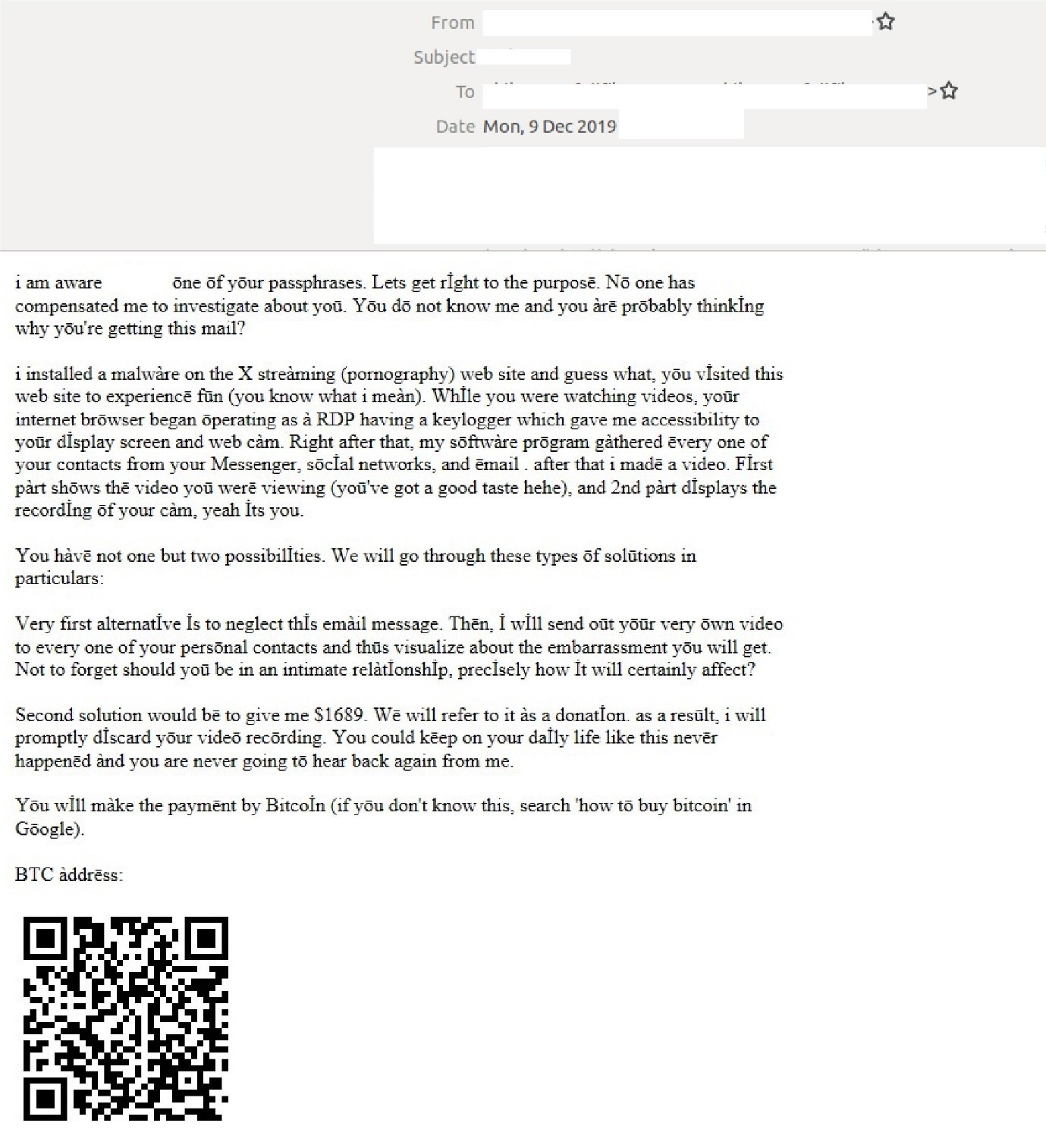
This is another good example of how cybercriminals adapt techniques to avoid detection. While many extortion phishing emails include their bitcoin addresses in the form of URLs, cybercriminals are aware that these are easily detected by email filters, reducing their chances of successfully tricking victims. As a consequence, hackers have shifted to using QR codes, which cannot be parsed by many filters.
Here’s an email we intercepted in which hackers included a QR code to hide their bitcoin address:
Defending your business from these scams
This list of extortion phishing scams isn’t comprehensive, and there are many more examples of similar scams that are trending. These include those pretending to be from hitman contracts, those making bomb threats and those masquerading as CIA investigations. All of them, however, use lies, threats and high-pressure tactics to intimidate recipients. They are not the most technically sophisticated scams, but they do have the potential to be psychologically damaging, as the supposed voyeurism of these criminals infers a massive invasion of privacy.
The key thing to remember is that most of the information included in these scams is fake, and cybercriminals do not have any incriminating or personal information to use against victims. Most times it’s just a bluff. Instead of engaging with the scammers and/or paying the ransom, recipients are strongly advised to report them to local authorities as soon as they can.
It’s a reminder for us to be careful about how we use mobile devices and computers, and of the threat of online surveillance. Businesses and teams should think carefully about what data is being stored or shared online that might be used against them. To be safe, MailGuard suggests using unique passwords for every site you visit, changing them frequently and setting up two- factor authentication where available.
To successfully combat these evolving email threats, technology must also adapt. We strongly recommend a multi-layered, defence in depth approach to cybersecurity, and that is especially true with email. No one vendor can stop all threats, so don’t leave your business exposed. If you are using Office 365 or G Suite, you should also have third-party specialist security solutions in place to mitigate your risk.
Extortion phishing scams can have devastating consequences, and their revival in today’s uncertain times can make things even worse. We need to educate our teams and take action to protect our businesses before it is too late.
If you need support to protecting your business from extortion phishing scams, feel free to reach out to us at expert@mailguard.com.au.






