Claire, an intern at a small legal firm, sits down at her desk after getting back from a hasty, late lunch. She gulps her coffee and flicks open her email inbox: 37 new messages. She rubs her temples and begins to work her way through the backlog that piled up during her 15-minute lunch break.
The lawyers Claire works for are prolific email writers who keep her busy 10 hours a day, and there’s always a constant stream of new tasks landing in her inbox. The first message in the queue states simply: “your office web-email account is over quota and prior messages must be deleted to save storage. Please verify your login credentials to keep your account active.”
Claire sits up straight and stabs at her mouse button, clicking on the “verify” link. The entire office runs on email messages so having her messages deleted would be a major headache.
The link in the message opens up a web page titled “Webmail login.” Claire punches in her email account name and password, clicks “send,” and completes the two step authentication process. A friendly looking message pops up advising her that her account has been verified and then her online inbox opens. All her messages are still there. She breathes a sigh of relief and ploughs on with the afternoon’s tasks. It’s going to be a long day, but at least she won’t have to explain to her boss that she blew up her email account.
Two weeks later the law firm’s entire computer system is compromised by hackers. The partners discover the data-breach when $500,000 goes missing from the firm’s bank accounts.
An IT specialist is called in to clean up the mess and traces the breach back to that innocuous email Claire received telling her that her account was over-quota.
The website Claire logged into was a phishing page set up by hackers that collected her password. Once the criminals behind the hack were able to get into Claire’s inbox, they found messages detailing the firm’s financial transactions, contact lists and banking credentials. A few days of covert surveillance of the company’s email traffic gave them everything they needed to divert a $150,000 payment that was supposed to go to a client into their own bank account, and the heist was complete.
Phishing attacks surging
The anecdote above is fictitious, but it exactly resembles cybercrime incidents that are occurring across the world with increasing regularity.
A new report published by APWG - the Anti-Phishing Working Group - surveying international cybercrime data from industry and government sources reveals that phishing attacks have surged 46% since 2017.
The total number of phishing attacks detected by survey respondents in Q1 2018 was 263,538; up from 180,577 in Q4 2017. APWG also found that there was a steep rise in the number of phishing sites detected across the early months of 2018.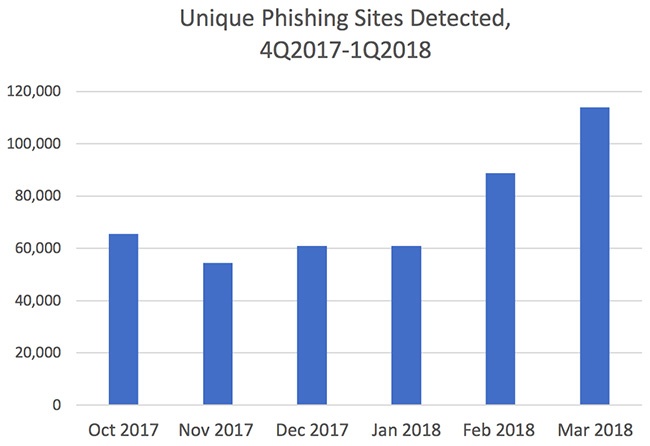
(Data source: APWG.)
The statistics relating to online fraud are deeply concerning. According to the FBI, this kind of attack has increased by 2,370% since 2015 and the global cost is now in the billions of dollars.
The MailGuard email filtering software screens out thousands of cyber-attack messages every day, and the volume of malicious email just keeps growing. The email fraud racket seems to be booming. Cybercriminals are sending out more phishing and malware attacks now than ever before, and every one of them has the potential to give cybercriminals access to companies’ systems and data.
The ASBFEO, Australia’s small business advocate, released survey figures in 2017 that illustrate the severe damage cyber-attack can do to SMBs. The ASBFEO reported that 43% of cybercrime attacks target smaller businesses, not large corporations and that 60% of small companies hit with a cyber-attack are so badly affected that they go out of business within six months.
How does phishing work?
 Phishing is the practice of tricking email recipients into revealing personal information that criminals can exploit for gain.
Phishing is the practice of tricking email recipients into revealing personal information that criminals can exploit for gain.
Phishing emails go to a wide group of random people; it’s like a fisherman casting a wide net to see what he can catch. The attackers know that not everyone will respond, but they know that if they send enough emails out somebody will probably take the bait.
A phishing attack message will typically include a link that will send the unwary victim to a fake login website. Once there, the user will be asked to enter username and password data which will be automatically captured by the phishing page.
Scammers use phishing pages to collect login credentials for email accounts, bank accounts, and a wide range of other online services. They use the information they gather to break into company computer systems and commit fraud or extortion attacks.
Learn more about protecting your business
The explosive growth of email-based fraud requires a multi-layered approach to security that includes virus scanning software, staff training and cloud-based email filtering. There’s never been a better time to take on the challenge of breach-proofing your company.
If you would like to learn more about the complex cybersecurity challenges facing companies, please download the e-book Surviving the Rise of Cybercrime. It’s a plain English, non-technical guide, explaining the most common threats and providing essential advice on managing risk.
“Cybercrime is a serious and growing business risk. Building an effective cybersecurity culture within an organisation requires directors and executives to lead by example. Surviving the Rise of Cybercrime is a must-read for directors and executives across business and in government and provides strong foundations for leaders determined to address cyber risk.” - Rob Sloan, Cybersecurity Research Director, Wall Street Journal.
You can download your copy of Surviving the Rise of Cybercrime for free, here.






