- Phishing
- Brandjacking
- CEO fraud
All these kinds of cybercrime are perpetrated using email as their primary vector.
Every business is constantly sending and receiving emails, it’s part of the background noise of everyday work, so it’s a powerful tool for criminals who want to slip under the wire and attack a company from the inside out.
The majority of people think of cybercrime and “hacking” as a technical process involving coding and cracking but actually, the reality is much simpler; cybercrime happens via email. Without layered email security, serious phishing and malware threats are landing daily in every company’s inboxes.
Report finds email is main threat
A key finding of the 2018 AusCERT Cyber Security Survey report was the dominance of email-based fraud amongst potential online security threats.
You can see in the graph below that organised crime is responsible for around 50% of cybersecurity incidents experienced by Australian companies.
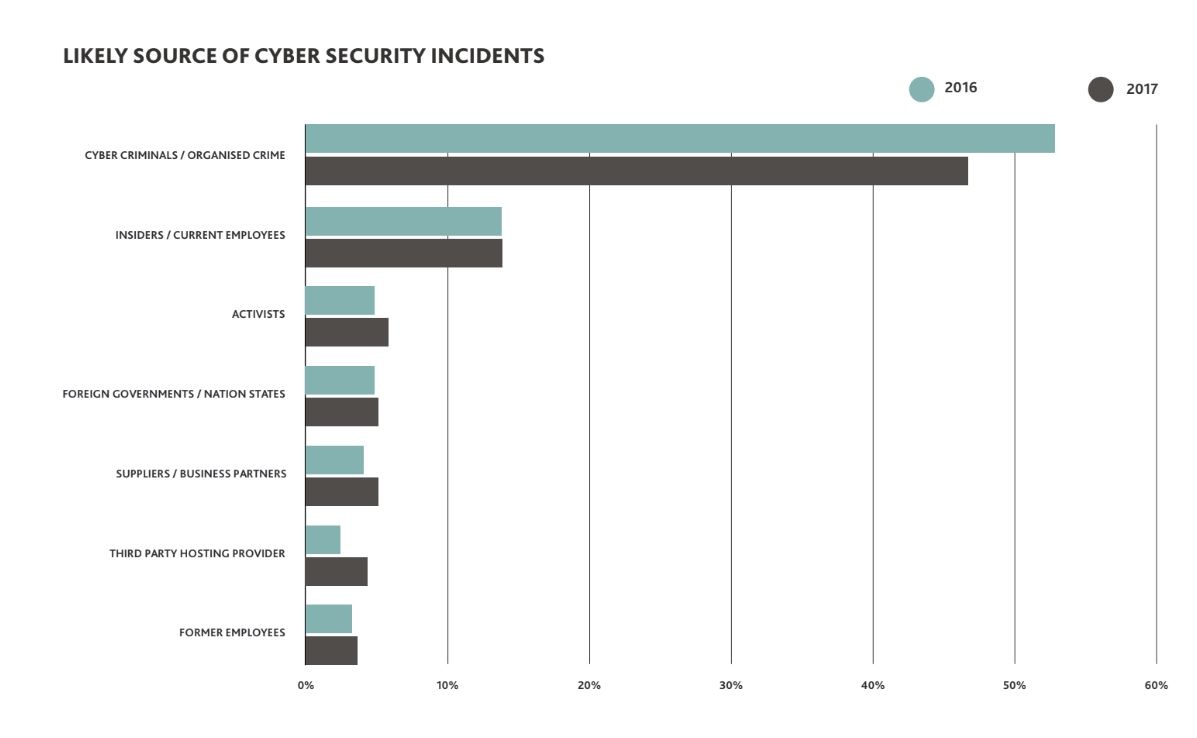
(Graph above: excerpt from the 2018 AusCERT Cyber Security Survey report.)
“Australian Businesses are targets and are generally underprepared,” concludes the AusCERT report. “Phishing and email attacks are still the most prevalent form of cyber security incidents affecting respondents, followed by ransomware and malware coming in a close second and third. Email is the primary online method used for communications and information sharing for private and business users... Phishing emails are the most widely used infection vector employed by 71% of all threat actor groups.”
How do email-based cyber-attacks work?
 How does a scammer get from a link in an email to breaking into a company’s accounts records or diverting their funds?
How does a scammer get from a link in an email to breaking into a company’s accounts records or diverting their funds?
If a crook can get a member of staff to click on a link or open an attachment in a malicious email message, they can quickly get access to the company’s data, including financial transactions, passwords and file storage systems.
In the next sections of this article, we’ll look at the most common email attack formats and the basic mechanics of how they work in real-life fraud cases.
But before we go any further I want to introduce you to one of the most fundamental techniques in the cybercriminals playbook.
Brandjacking
Essentially, brandjacking is a kind of forgery; scammers exploit the trademarks of well-known companies to deceive their victims and gain their trust. In a typical brandjacking scam, criminals create email templates that look like messages from big companies and send them out wholesale to millions of recipients. When the scam messages show up in victim’s inboxes they feel safe opening them, because they look like legitimate emails from familiar companies.
Some common brandjacking formats are fake invoice notifications or requests for account verification.
Phishing
Phishing is a tactic used by criminals to harvest the login credentials of their victims.
A phishing attack typically starts with a brandjacking email, as described above, which purports to be a notification from a well-known company like a bank or other service provider.
A phishing email will contain some sort of message that induces the recipient to click on a link to a fake login page set up by the criminals behind the fraud.
The login page will look and behave like a real online portal, but its sole purpose is to collect the victim’s username and password so that the criminals can exploit their account.
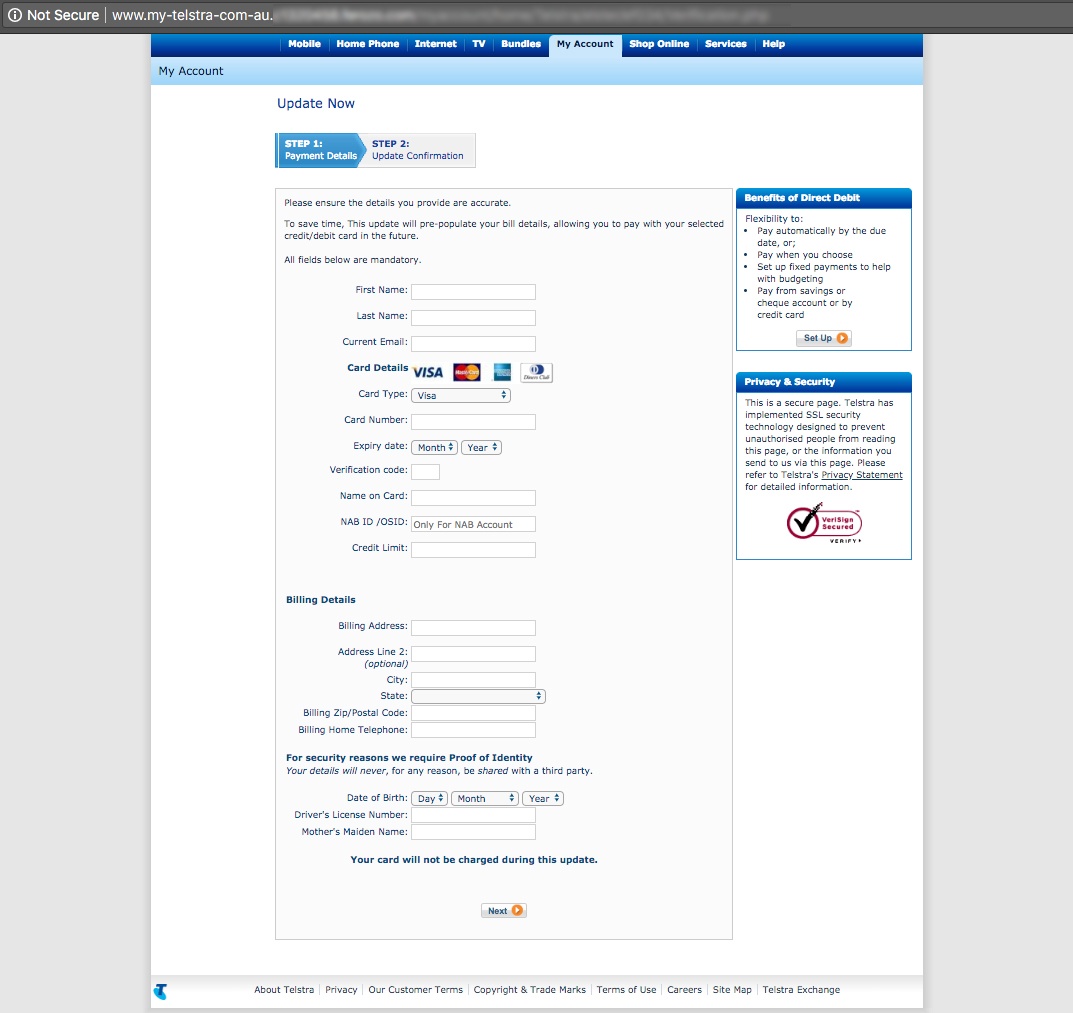
Some phishing scams involve a second page which will ask for the victim’s credit card details or other detailed data like address, phone number and bank account credentials.
With such detailed information about their intended victims, the cybercriminals who perpetrate phishing attacks are able to execute devastating BEC scams and CEO fraud attacks.
What does phishing look like?
Here’s an example of a brandjacking phishing attack recently detected by MailGuard:
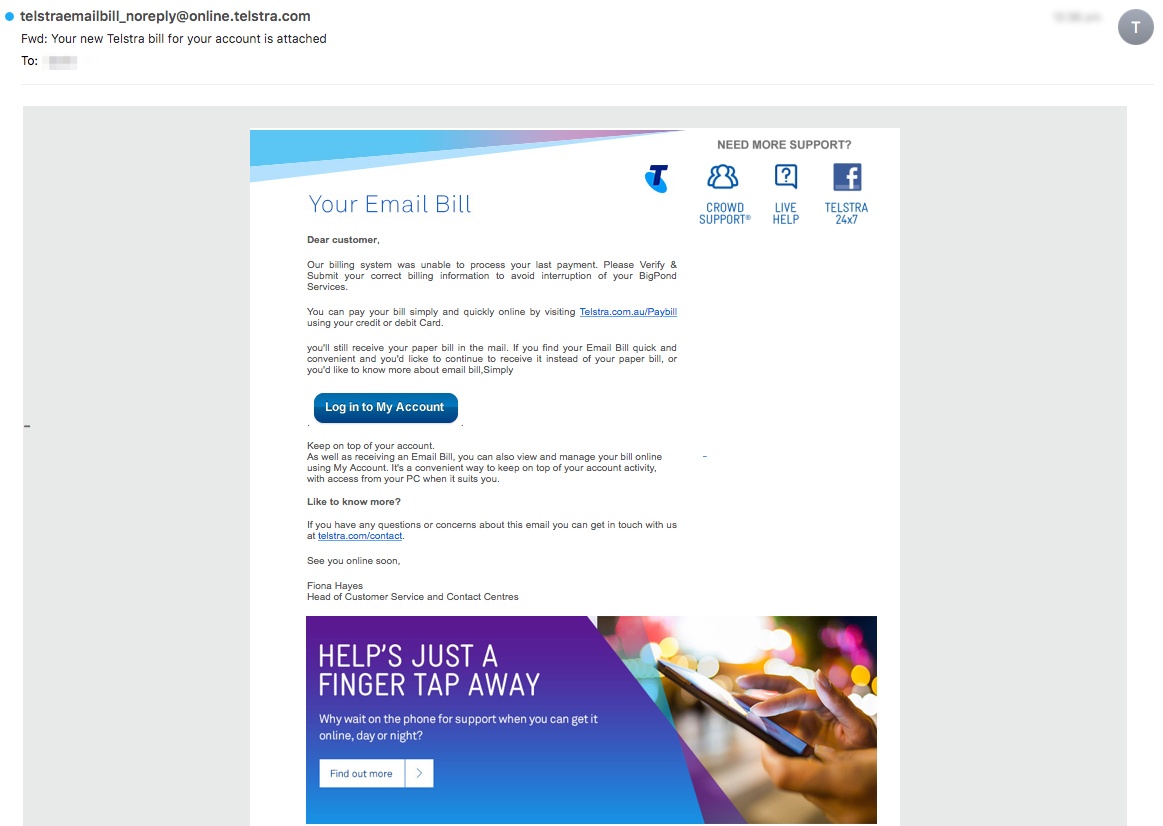
This phishing email is brandjacking Telstra, a major Australian telco.
This criminal intent email is one of the most sophisticated MailGuard has seen recently, using very convincing forgeries of a Telstra email notification and login portal that feature extensive graphical branding elements.
Note the sender display address on the email header which is also deceptively realistic; “telstraemailbill_noreply@online.telstra.com”
The phishing email linked to the login page shown in the screenshot below:
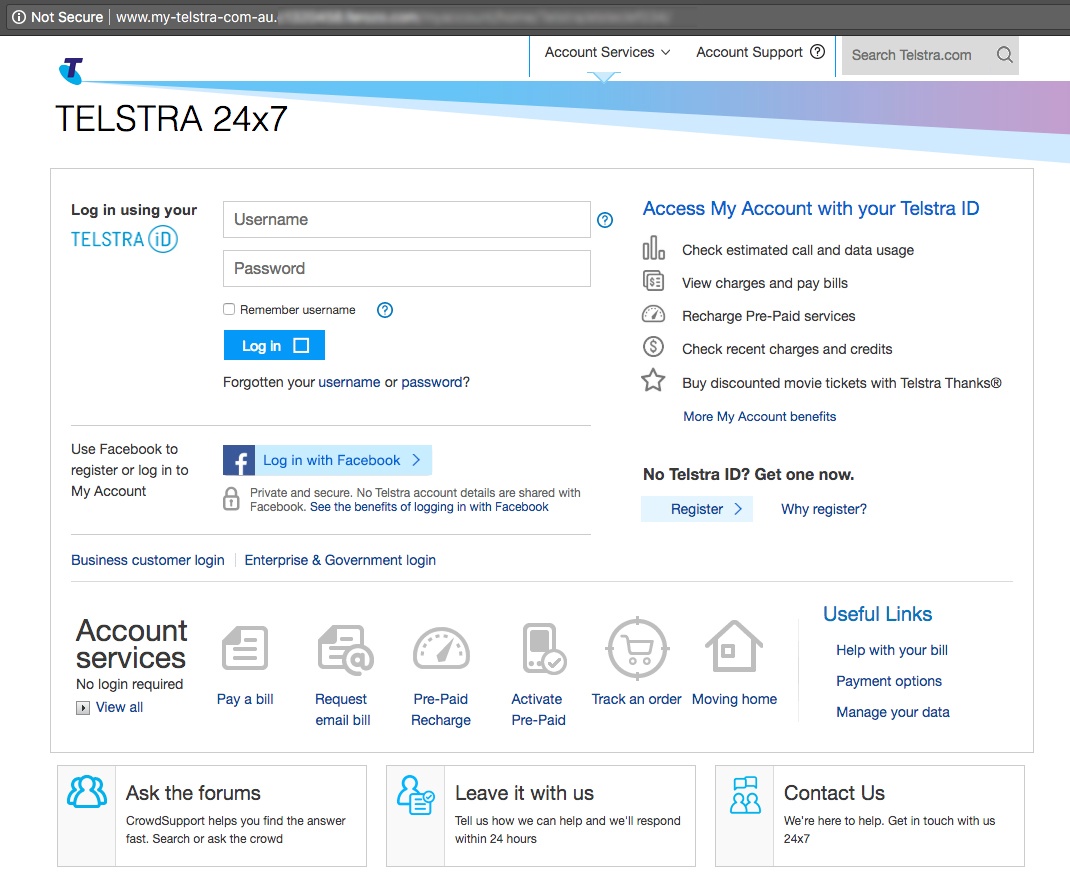
Well designed phishing attacks like this one can be very easy to fall for. In our busy lives, we're often hasty in reacting to emails and criminals take advantage of that.
The criminals who designed this fake login page went to considerable lengths to make it look legit. MailGuard’s analysts determined that the format of this page may have been directly copied from a genuine Telstra site. Even the domain URL used in this scam was carefully chosen to deceive victims - "www.my-telstra-com-au" - which although it is not genuine is close enough to the real website to pass a cursory inspection.
Once the intended victims of this scam submitted their Telstra credentials in the page shown above, they were forwarded to a second page that harvested their personal data and credit card details; enough information to allow cybercriminals to steal large sums of money with relative ease.
BEC and CEO Fraud
CEO fraud attacks use impersonation of high-ranking executives to extract money from companies.
The cybercriminals who perpetrate this kind of fraud collect information about CEOs or hack into their email accounts so they can assume their identity them. Once they have enough information to imitate a CEO, the fraudsters will leverage their authority to persuade another person in the company to send them money.
You might not think trickery like this could work, but the statistics on CEO fraud are alarming. According to the FBI, this kind of attack has increased by 2,370% since 2015 and the global cost is now in the billions of dollars.
People tend to think of cybercrime as being high-tech, but CEO fraud uses relatively simple tactics. Unlike ransom-attacks or spyware, CEO fraud doesn’t rely on clever software to be effective; it’s a kind of cybercrime known as ‘social engineering’ that uses psychological cues and deception to defraud victims.
In CEO fraud, instead of hacking code, the scammers hack social networks, relationships and company structures. One common technique is to use a phishing email to obtain a CEOs login details and then use their email account to manipulate the company from the inside. Using a CEOs email account, criminals can issue orders to the accounting department, authorise delinquent payments and gain access to sensitive data that may be of value on the black market.
When criminals are impersonating a CEO they usually try to create a sense of urgency with their fraudulent messages. Timing a message to arrive near close-of-business, and urging staff to act quickly are ways to discourage them from checking the authenticity of a message before acting on it.
Learn more about CEO fraud attacks and how to prevent them, here.
Important questions to consider
If your company is reviewing its cybersecurity status you may want to pose the following questions to your management team:
- What cybersecurity vulnerabilities is our company exposed to?
- Who is responsible for planning and implementing the company’s cybersecurity strategy?
- What cybercrime countermeasures does our company currently use?
- Should we be concerned about the security policies and vulnerabilities of our business partners?
- What regulatory concerns do we have around cybersecurity? Is GDPR compliance on our agenda?
- Does our company offer cybersecurity education to our team members?
First steps toward security
The explosive growth of email-based fraud requires a multi-layered approach to security that includes virus scanning software, staff training and cloud-based email filtering.
There’s never been a better time to take on the challenge of breach-proofing your company. The old saying goes ‘prevention is better than a cure’ and that’s certainly the case with cybersecurity.
If you would like to learn more about the complex cybersecurity challenges facing business today, please download my e-book Surviving the Rise of Cybercrime. It’s a plain English, non-technical guide, explaining the most common threats and providing essential advice on managing risk.
“Cybercrime is a serious and growing business risk. Building an effective cybersecurity culture within an organisation requires directors and executives to lead by example. Surviving the Rise of Cybercrime is a must-read for directors and executives across business and in government and provides strong foundations for leaders determined to address cyber risk.”
- Rob Sloan, Cybersecurity Research Director, Wall Street Journal.
 Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Follow me on social media to keep up with the latest developments in cybersecurity and Blockchain; I'm active on LinkedIn and Twitter.
I’d really value your input and comments so please join the conversation.






