The term “imitation game” comes from a paper Alan Turing wrote in 1960 called Computing Machinery and Intelligence. Turing posed the question "Are there imaginable digital computers which would do well in the imitation game?"
While machines are now beginning to answer Turing’s question in the affirmative, the most dangerous copycats in the cyber-world are still humans.
A massive new crime category has risen up as the world’s economy has gone digital: email fraud. The victims are companies, big and small, and the perpetrators are skilled con-artists who use fake emails and counterfeit websites to steal billions of dollars.
Imitation and fraud
Most of us get our ideas about cybercrime from television. It’s easy to imagine a high-tech game of code breaking and server hacking but the reality is very different.
Research on cyber-attacks consistently shows that most online fraud is perpetrated with very simple tactics. Reports released by The FBI, Deloitte and WEF all agree; cybercriminals directly target people through their email inboxes to get access to their employer’s data and ultimately, their money.
 Email-based fraud is so common it has spawned a slew of specific jargon; BEC fraud; phishing; whaling; all these terms are used in the cybersecurity industry to describe variations on a basic tactical format:
Email-based fraud is so common it has spawned a slew of specific jargon; BEC fraud; phishing; whaling; all these terms are used in the cybersecurity industry to describe variations on a basic tactical format:
- criminals send a counterfeit email to a person working in a company
- the email contains a link and urges the recipient to click on it
- the malicious link in the email message will go to a phishing page that harvests sensitive data or a malware file
- the phishing page or malware will allow the criminals to get the victim’s login credentials and thereby access the company’s computer system
Once inside an organisations email system cybercriminals have access to a plethora of valuable data.
- They can get hold of contact lists to extend their penetration of the company.
- Many organisations use email to send and receive purchase orders and invoices, so criminals can intercept those messages and divert the payments.
- With access to the email accounts of company staff, criminals can impersonate them in messages to their colleagues and manipulate them into revealing sensitive data or releasing funds.
 Recent revelations about the hacking of the 2016 Clinton Presidential campaign suggests that social engineering was the primary tactic used by the attackers. The accused Russian hackers sent phishing emails to key campaign staffers and stole their email login credentials to initiate the infiltration of the DNC.
Recent revelations about the hacking of the 2016 Clinton Presidential campaign suggests that social engineering was the primary tactic used by the attackers. The accused Russian hackers sent phishing emails to key campaign staffers and stole their email login credentials to initiate the infiltration of the DNC.
These tactics of imitation and manipulation are known as social engineering. It’s a kind of online fraud that is very similar to the tactics scammers and con-artists have been using for centuries. Social engineering exploits the trust people place in the familiar and uses it to trick them into letting criminals inside their company’s defences.
> I gave a detailed explanation of social engineering in an article I published in March; you can read it here.
Names and brands we trust
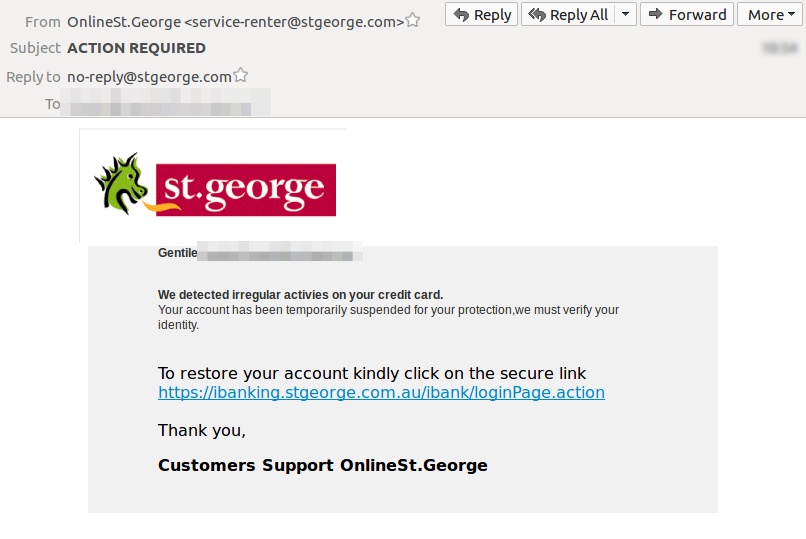
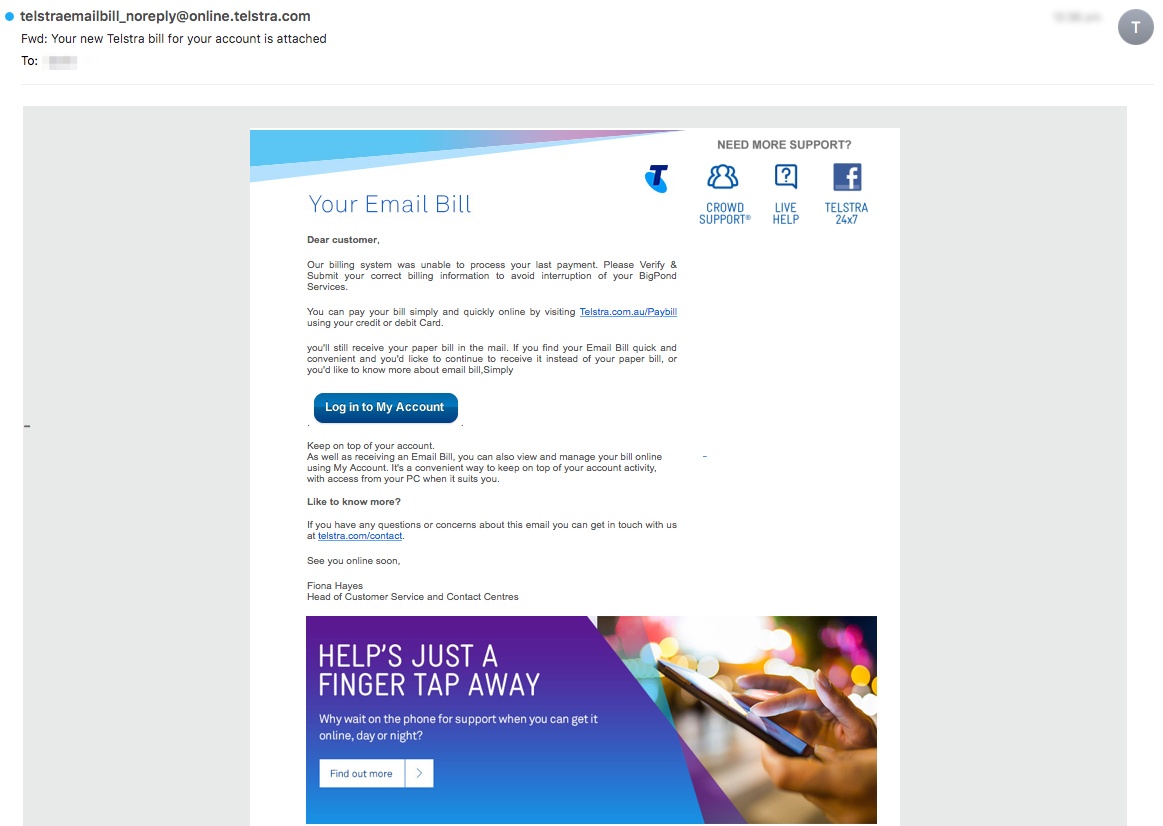
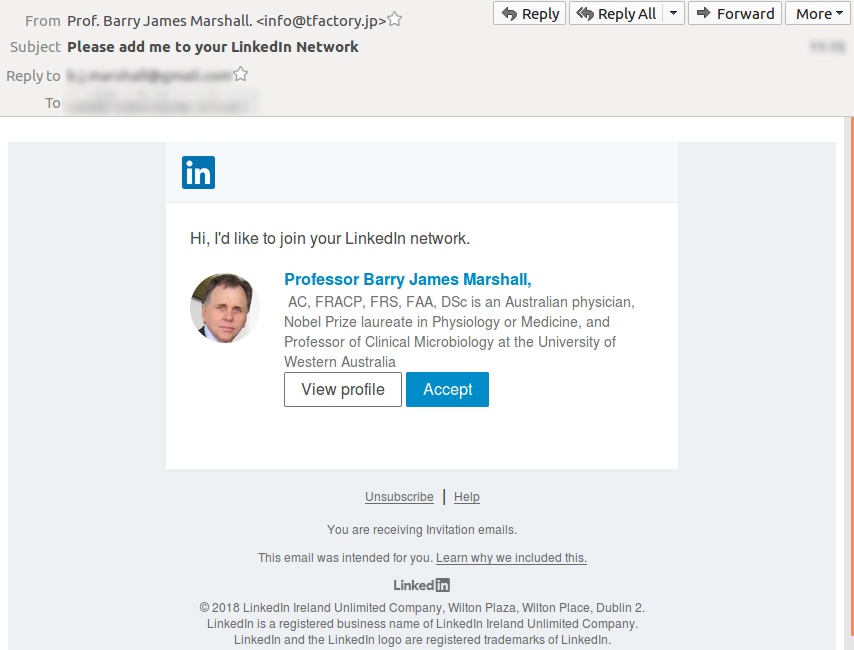
One of the core weapons in the cybercriminal arsenal is brandjacking. This is the malicious use of well-known company names and trademarks to fool people into thinking that they can trust malicious emails they find in their inboxes.
If you get an email that seems to be from your bank and asks you to click on a link to view your monthly statement, you probably won’t think twice. That’s the power of brand marketing. Companies spend billions of dollars creating an image of trustworthiness and reliability for their trademarks and cybercriminals exploit that image to trick their victims.
MailGuard is constantly intercepting new brandjacking emails that rip-off the trademarks of all kinds of companies: couriers; banks; retailers; utility companies; media organisations; and even government agencies.
Here are few examples of brandjacking emails MailGuard has detected; do you think you would recognise them as fakes if they showed up in your inbox?
Plenty of people are taken in by brandjacking emails like these, so the number and sophistication of these attacks keeps increasing every year.
Even if you think you could spot an email scam, are you confident that every other person in your company would be as vigilant as you?
It only takes one person in a company clicking on a malicious link to allow criminals to seize control.
Is it worth the risk of leaving it to chance?
Layered security is essential
Humans are very susceptible to fraud. To keep a business safe from email fraud requires a company-wide security strategy that starts with the boardroom and involves every member of the team.
- Endpoint virus scan;
- cloud-based email filtering;
- AI driven threat detection;
- thorough data management policies;
- staff education in cybersecurity best-practice;
These are all essential components of effective cybersecurity.
Defend your data
 If Alan Turing the great code breaker and defeater of the Nazi’s Enigma Machine could see the fraudulent use that computers were being put to nowadays he would probably be mightily unimpressed, but perhaps he wouldn’t be surprised. Every technology has the potential to be exploited for malicious purposes.
If Alan Turing the great code breaker and defeater of the Nazi’s Enigma Machine could see the fraudulent use that computers were being put to nowadays he would probably be mightily unimpressed, but perhaps he wouldn’t be surprised. Every technology has the potential to be exploited for malicious purposes.
Right now, with the explosive growth of online business platforms and stringent new regulatory regimes, the challenge of protecting data is getting more complex and also more critical.
There’s never been a better time to take on the challenge of breach-proofing your company. The old saying goes ‘prevention is better than a cure’ and that’s certainly the case with cybersecurity.
I’m on a mission to help business people understand cybercrime and protect their businesses from costly attacks.
If you would like to learn more about the complex cybersecurity challenges facing business today, please download my e-book Surviving the Rise of Cybercrime. It’s a plain English, non-technical guide, explaining the most common threats and providing essential advice on managing risk.
“Cybercrime is a serious and growing business risk. Building an effective cybersecurity culture within an organisation requires directors and executives to lead by example. Surviving the Rise of Cybercrime is a must-read for directors and executives across business and in government and provides strong foundations for leaders determined to address cyber risk.” - Rob Sloan, Cybersecurity Research Director, Wall Street Journal.
You can download the e-book for free, here.
 Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Follow me on social media to keep up with the latest developments in cybersecurity and Blockchain; I'm active on LinkedIn and Twitter.
I’d really value your input and comments so please join the conversation.