This year, ‘Scams Awareness Week’ is spotlighting impersonation scams, and the ACCC and ScamWatch are promoting the theme 'Who's really there?'.


Impersonation scams come in all shapes and sizes. They’re where scammers pose as the brands or people that are most familiar to us. Those trusted businesses that we know and love, or as friends, family, or work colleagues, aiming to steal money, personal information or sensitive credentials that might provide access to vital assets or data.
ScamWatch define impersonation scams as 'where scammers pretend to be trusted businesses, friends or family to steal your money or personal information. Impersonation scammers can reach you on all mediums such as text message, websites, social media, email and phone calls. Scammers often pretend to be government officials, well-known companies, charities, celebrities, law enforcement or even family and friends.'
They are essentially the good old-fashioned con-artist, but in today’s digital age they take advantage of all that technology offers to deceive you. It may be in the form of an SMS text message, as a fake website or eCommerce portal, on social media, as a phone call, or of course via email. Or it may even be a combination.
Scammers can even pretend to be government officials, charities, celebrities or law enforcement. Sadly, they have no moral barriers, and are willing to do whatever it takes to penetrate your defences.
Let’s look at some of the more common forms of impersonation employed in email scams.
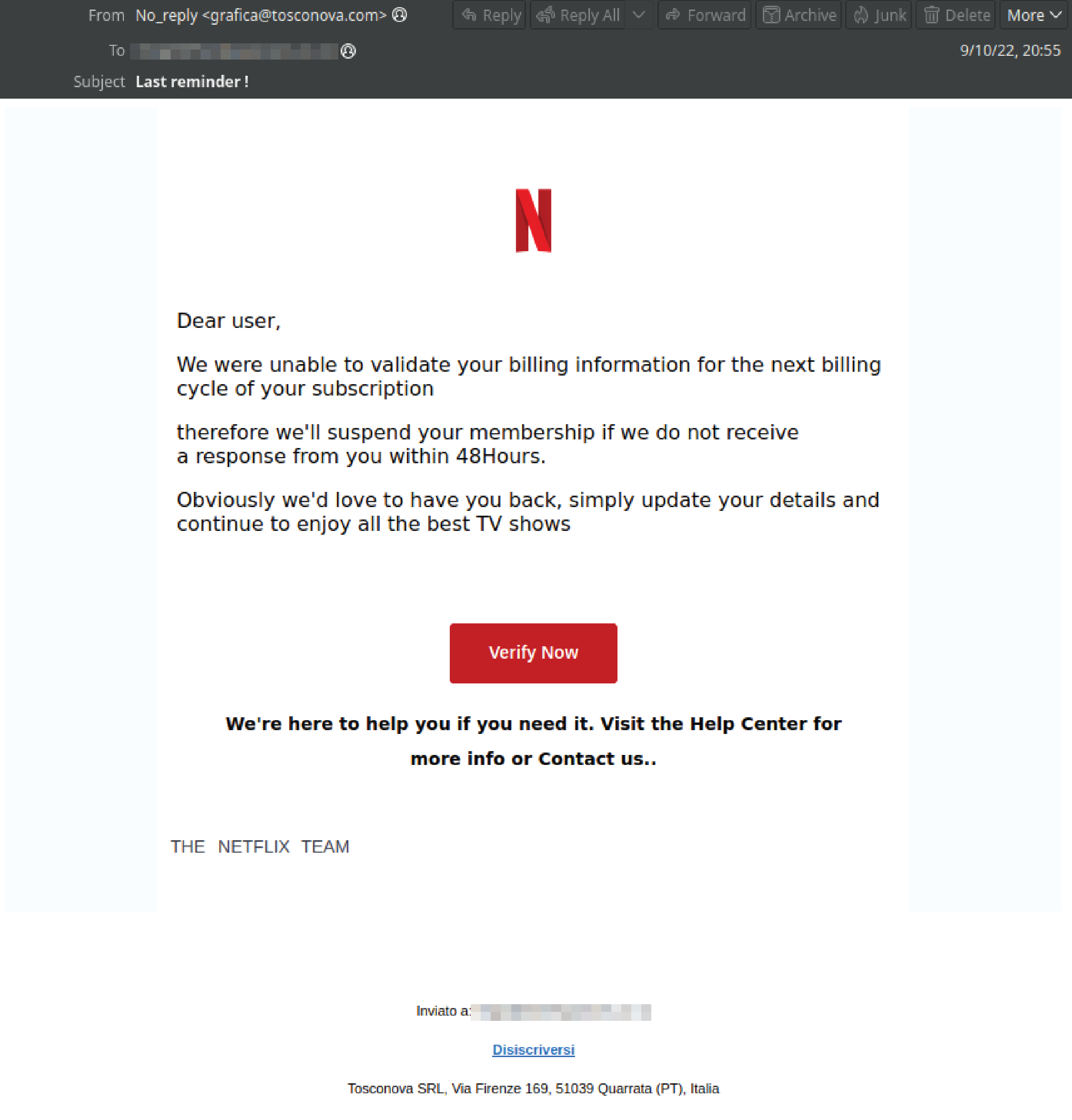
1. Phishing Attacks (Or vishing, smishing, quishing, and other variants)Phishing attacks are the ultimate form of impersonation, and probably the most prolific. They’re when someone sends you an email pretending to be someone else. Typically, they’re impersonating a well-known and trusted brand or service, like an energy company, a bank or finance company, a phone company, a parcel delivery service, a government agency or provider, or a streaming platform like Netflix. Try to think of something you can’t live without, and that company is likely to be spoofed in a phishing attack.
They generally come as an email, although there are a range if variants, forms of phishing like smishing which is phishing using SMS messages, or quishing, which is phishing with embedded QR codes. Bad guys will use whatever it takes to try and optimise their campaigns.
Tell-tale signs of a scam are grammatical errors, however the rise of AI services like ChatGPT means that those easy giveaways are occurring less frequently.
They will also normally include some kind of urgent call to action, like that your electricity is about to be cut off, or that your Netflix subscription is about to be cancelled. Or conversely, they may tout good news like a generous tax return or reimbursement. All just a click away.
Once you’ve taken the bait and clicked the link, they will direct you to a phishing site. It’s a landing page or website designed to look like the company that they’re spoofing, and those pages can be very convincing replicas.
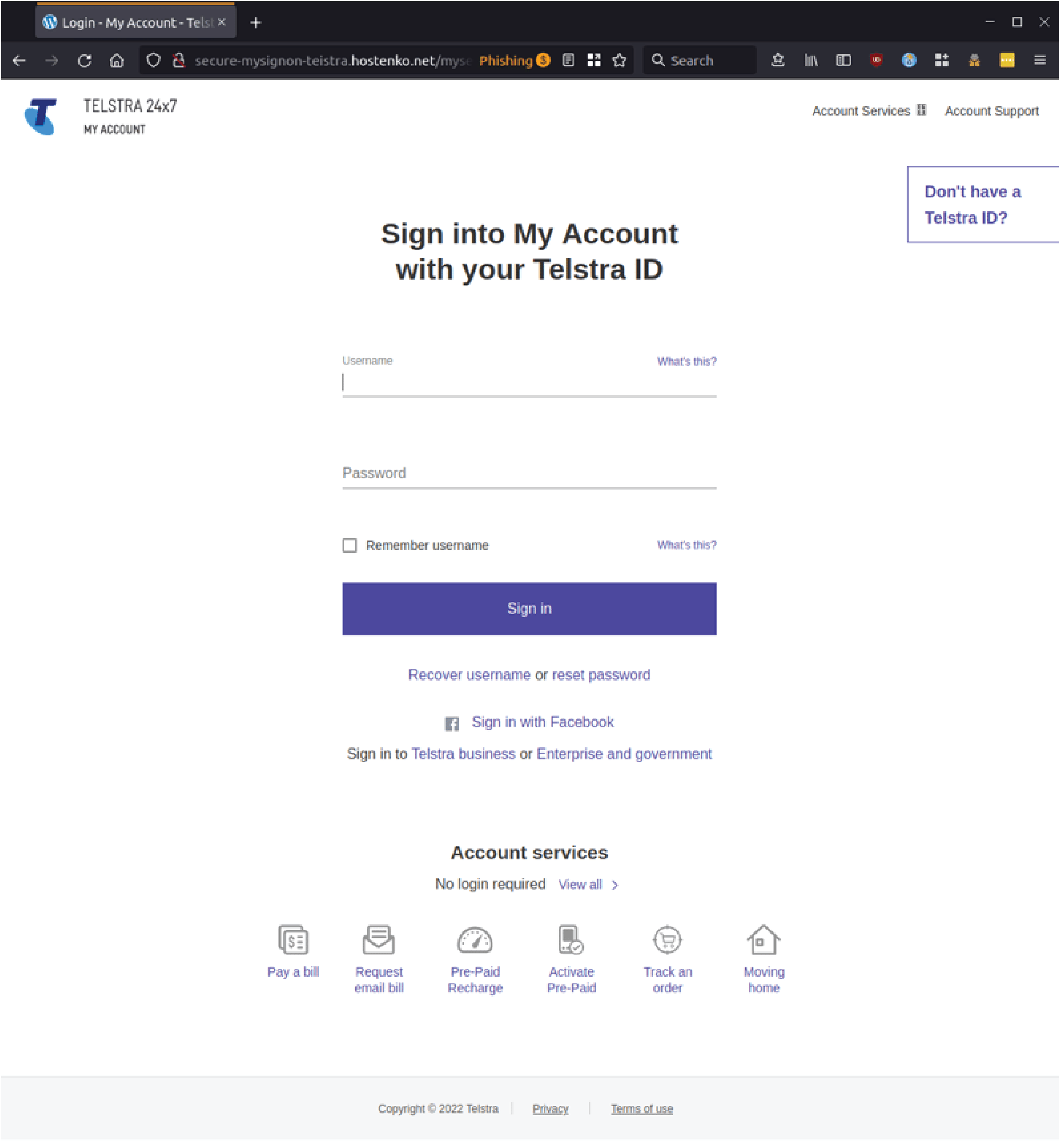
Phishing sites are designed to harvest your sensitive credentials, like credit card details, personal identity information like your name, address and date of birth, and/or your username and passwords. They may even send you a false verification link to capture the SMS verification number that you have received on your mobile from a legitimate service, so that they can complete transactions using the information that you have inadvertently disclosed.
Scammers will try to capture all of that information, or just part of it, then they may marry it up with a database that they have stolen elsewhere to launch follow on attacks that are even more sophisticated, to compromise your accounts, to process fraudulent card transactions, or they may simply sell your information on to the highest bidder on the dark web.
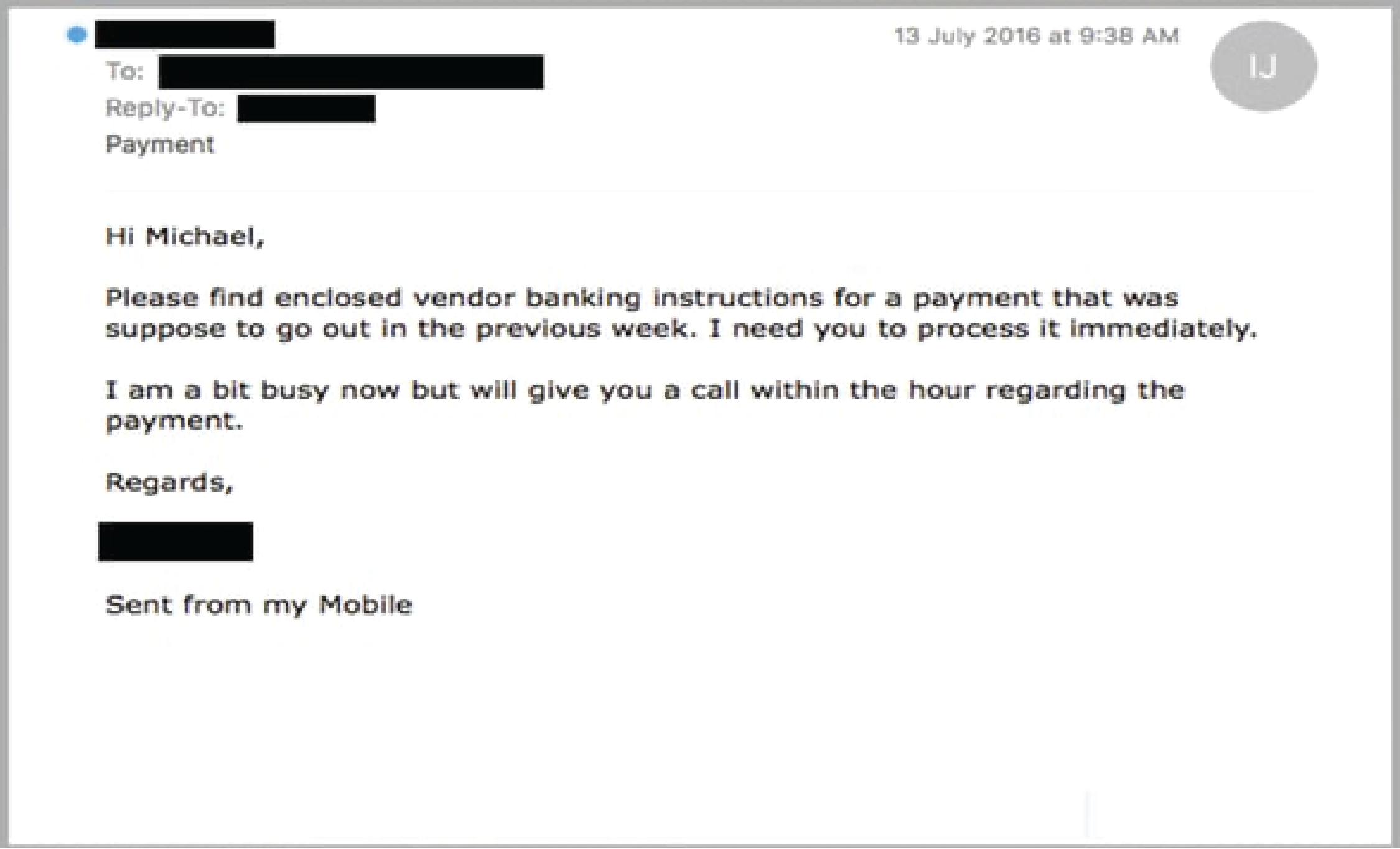
2. CEO Fraud or WhalingCEO Fraud, sometimes known as Whaling, are targeted email scams where the cybercriminals impersonate a high-ranking executive within your organisation in an attempt to exercise their authority and influence to trick and coerce employees. In that case, to be clear, the person that the scammers are spoofing could also be a CFO or Financial Controller, or a VP or other person of high status in your org.
These scams often entail a degree of social engineering, which means that the bad actors behind the scam have spent many hours researching the person that they’re impersonating online, checking company updates on LinkedIn and learning about connections within their professional networks, perhaps identifying times when they are likely to be out of the office or away attending a conference, all so that their colleagues will find it harder to confirm the voracity of the fraudulent request.
The emails are generally an attempt to authorise a payment or funds transfer, although they may also seek to change payroll details or account details for invoices so that funds are diverted to an unintended account.
You can download our free whitepaper, ‘CEO Fraud: What Every Executive Needs To Know’, to learn more.
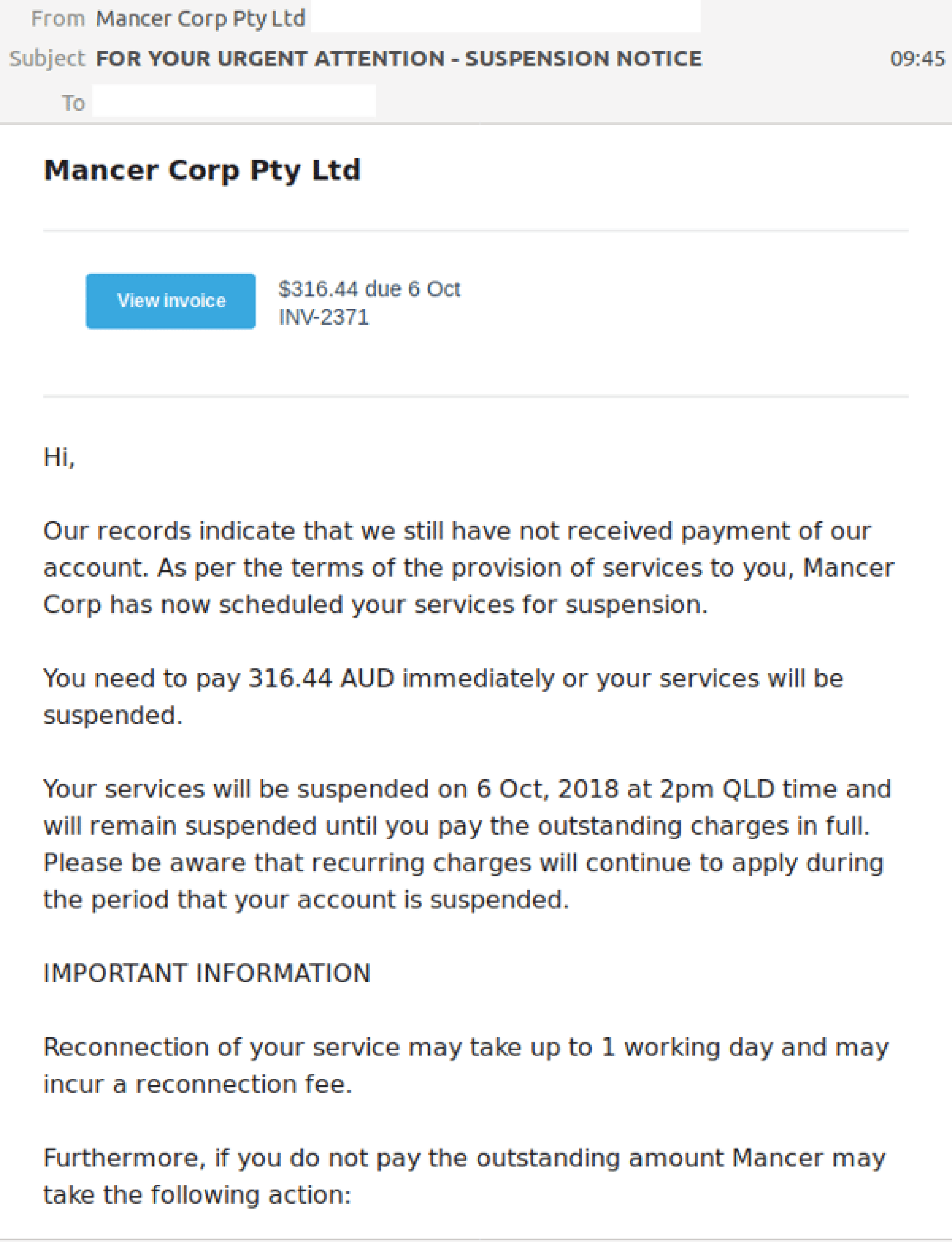
3. Business Email CompromiseSimilar to CEO Fraud or Whaling, Business Email Compromise or BEC, is where those perpetrating the scam are impersonating a particular individual. The NCSC define it as ‘where a criminal attempts to trick a senior executive (or budget holder) into transferring funds, or revealing sensitive information.
4. Identity TheftIdentity theft is when a criminal gains access to your personal information and uses it without permission for their benefit, financial or otherwise. So, it can impact a business, but can also impact individuals.
Often identities are stolen and used in illegal activities, such as creating fake identity documents with your name, applying for real IDs, or getting loans, credit cards, and mobile phone contracts.
These sorts of scams can have devastating financial and emotional impacts on the victim and may remain unresolved or cause problems for years. According to ScamWatch, from January to September of 2022, Identity Theft was the 4th most commonly reported scam type in Australia and cost its’ citizens almost $8 million.
Emerging technologies like voice and image generation AI’s, such as deepfakes, are making identity theft an even greater challenge. If you think you’re a victim of identity fraud, you can read our guide to find out what to do.
5. Account Takeover AttacksAn Account Takeover Attack is where a malicious cybercriminal gains unauthorized access to an account and uses it to propagate attacks on others. These scams are particularly troublesome because the emails are emanating from a legitimate account so in the early stages they are less likely to be intercepted by email filters and other security services.
Cloud services like MailChimp are common targets for such attacks, because the account owner is less likely to notice the activity, and the services will often contain a database or list of contacts that criminals can target, along with any other database of targets that they want to upload and include thenmselves.
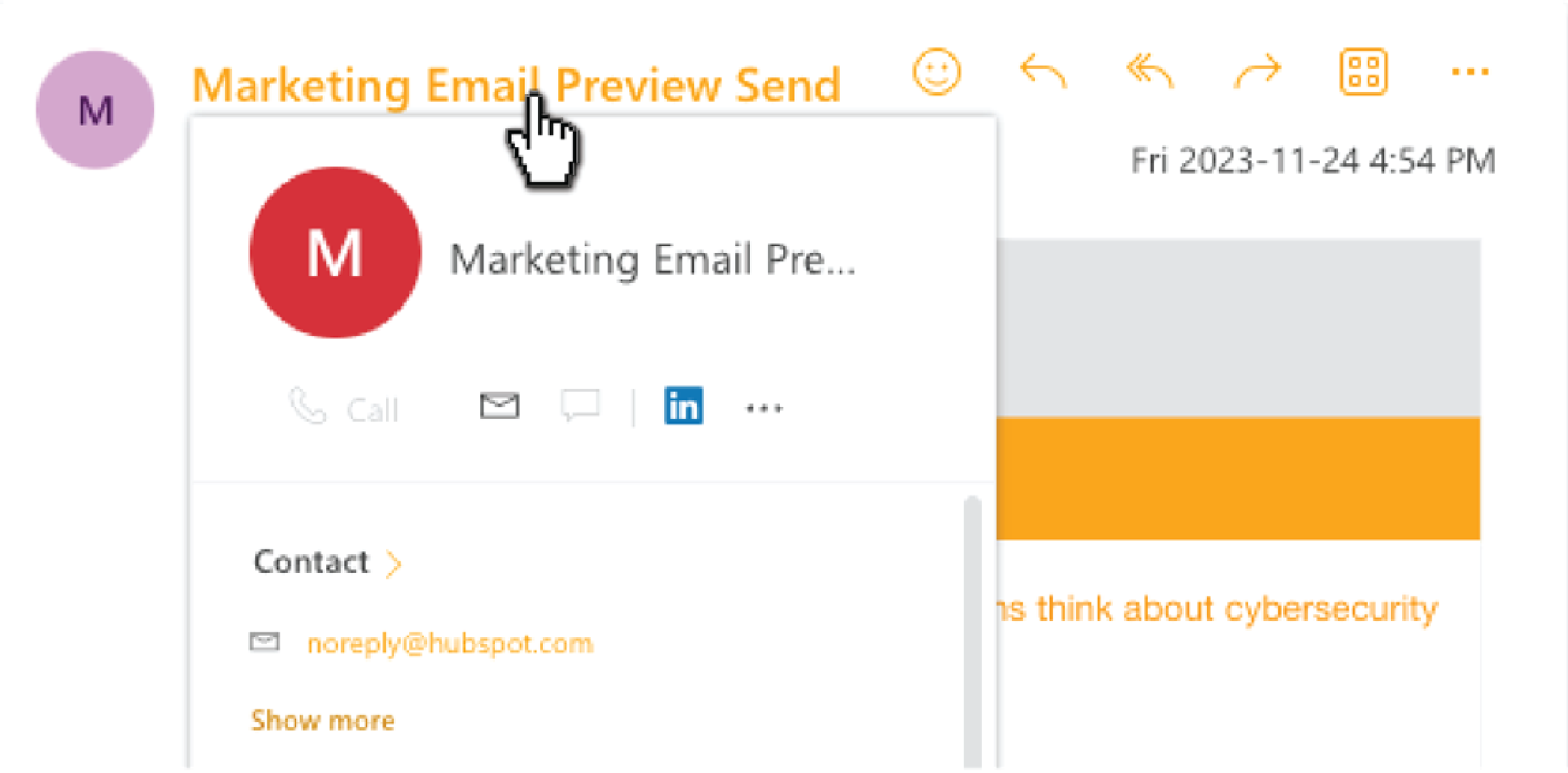
Here’s an example of an email that was intercepted by MailGuard that was sent from a compromised MailChimp account and impersonating the account owner. In this instance, recipients could be forgiven for believing that the email is legitimate given that it is coming from a sender email address that is frequently used by the company.
Supply Chain Attacks are very common. They occur when cybercriminals compromise one company, with the intention of using that compromise to gain access to other companies in their supply chain.
Blackbaud and Solar Winds are two of the largest scale and high-profile supply chain attacks in recent times.
SolarWinds, a software company with thousands of customers throughout the world, including government agencies and Fortune 500 companies, was hacked after attackers breached its networks and accessed the company’s proprietary IT software, Orion.
The attack involved inserting malware into legitimate updates for the Orion software, that allowed attackers remote access into the victim’s environments. Companies that applied the Orion updates, who were of course SolarWinds customers, also unwittingly installed the malware on their own systems. Reports state cybercriminals used the SolarWinds' hacked program to infiltrate at least 18,000 government and private networks.
In the case of Blackbaud, which provides services for many corporations, charitable foundations, education institutions and healthcare entities, it was hit by a ransomware attack.
After the company’s self-hosted environment was infected with malware, its cybersecurity team was able to stop the attackers from encrypting the entire network, however, the hackers did manage to steal a subset of data prior to deploying the ransomware payload, including data belonging to Blackbaud’s customers. The breach resulted in millions of sensitive student, patient, and donor data records being compromised.
There are many other examples, because supply chain attacks often impact a large network of companies, as with Blackbaud and SolarWinds. In other instances, they may only seek to breach a one particular target, often a smaller and less sophisticated supplier or contractor, with the objective of gaining access to a larger trading partner like a large corporate or government agency.
That was the case for mega-retailer, Target, which was breached with over 40 million debit and credit card accounts being exposed, after cybercriminals compromised a HVAC (heating, ventilation & air conditioning) contractor that possessed login credentials for the Target network. Speculation at the time was that the practice of providing network access to HVAC contractors by large retailers was not uncommon, so that they could monitor store temperatures and alarms, and to communicate with staff.
According to the US National Institute of Standards and Technology (NIST), cyber supply chain risks include:
- Insertion of counterfeits.
- Unauthorized production of components.
- Tampering with production parts and processes.
- Theft of components.
- Insertion of malicious hardware and software, and
- Poor manufacturing and development practices that compromise quality.
What’s the motto of the story?
Sadly, the motto of this story is that cybercriminals will do whatever it takes to trick someone into divulging sensitive credentials, or into making a payment or downloading malware. And the ramifications can be drastic.
As you would have noticed as we stepped through some of the more common types of email impersonation scams, there are lots of similarities between them.
The lessen to learn from it all is simply that you can’t judge a book by it’s cover. When it comes to online communications and emails, it is prudent to be cautious, with a healthy dose of suspicion. Take a few moments to think twice before clicking a link or sharing your details.
Aside from looking for the more obvious grammatical errors, use common sense to check if you are expecting a communication from the sender or company. If in doubt, don’t click. Pick up the phone and call to check or go directly to the company’s website to check your account status there.
And hover over the link of the sender email to check that it’s really from the person that it purports to be. Or on the landing page that you're directed to, check that the URL belongs to the company.
For Scams Awareness Week, the ACCC and ScamWatch offer the following advice:
'Key signs of impersonation scams
- You receive a message that asks you to click on a link that takes you to a webpage asking for your username, password, or personal information.
- You are asked to provide personal details or money urgently.
- An organisation that you think is real, tells you there has been an unauthorised transaction or asks you to confirm a payment that you didn’t make.
- A business asks you to use a different bank account and BSB from the last payment you made with them.
- You’re contacted by someone saying they are from a government department or law enforcement, and they threaten you with immediate arrest, deportation, or ask you to pay money.
- You’re asked to transfer money to an account to ‘keep it safe’ or for ‘further investigation’.
- A sale, investment or job offer looks too good to be true.
How to avoid Impersonation scams
- Don’t automatically assume the person you are dealing with is who they say they are.
- Slow down and ask yourself “who’s really there?”
- Don’t click on links in text messages.
- Immediately cut contact with anyone who tries to threaten or intimidate you.
- Don’t open or download any attachments or apps if instructed as these can install malicious software on to your computer or phone giving access to your personal information, data, and accounts.
- Consumers are urged to ‘Stop, think, protect’.
- Stop - Don’t give money or personal information to anyone if unsure.
- Think - Ask yourself could the message or call be fake?
- Protect - Act quickly if something feels wrong.
How to verify who you’re dealing with?
- Independently verify who you’re dealing with before you give money or personal information by either:
- Contacting the person or organisation directly using contact details you’ve found yourself on the organisation’s official website.
- Accessing the organisations’ secure, authenticated portal or app (never via a link).
- If someone you know sends a message to say they have a new phone number:
- Try to call them on the existing number you have for them.
- Message them on the new number with a question only they would know the answer to. That way you will know if they are who they say they are.
- Watch out for slight variations in Caller or Sender IDs and web addresses like dots, special characters, or numbers.
- Do online research of people and organisations who you’ve only dealt with online before paying any money. Search the name online together with the word ‘scam.’
- Check for the correct registration details of organisations through registers such as the Moneysmart financial advisors register and the Australian charity register for charities.
Victim support
- Contact your bank or card provider immediately to report the scam. Ask them to stop any transactions.
- IDCARE is Australia and New Zealand’s national identity and cyber support service. They can help you make a plan (for free) to limit the damage. Call them on 1800 595 160 or visit their website to find out more.
- If a scam is causing you problems with debt talk to a financial counsellor. Moneysmart provides a list of free and confidential services to help you get your finances back on track.
- Being scammed is a horrible experience and it can happen to anyone. If you need someone to talk to, reach out to family and friends or you can contact Lifeline (13 11 14) or Beyond Blue (1300 22 4636).
- Tell your friends and family of your experience to protect them from becoming a victim.
Reporting impersonation scams
- Once you have secured your details, you can help us try to stop the scam or to warn others by reporting the scam to the National Anti-Scam Centre via Scamwatch.gov.au.
- By reporting scams to Scamwatch you help protect others and assist us to disrupt and stop scammers – 30% of scams currently go unreported.
- The information you give us when you make a report helps the National Anti-Scam Centre to identify the scams that are causing the most harm to Australians.
- We use the information to understand how scammers work, who they harm and who we need to work with to disrupt and stop them.
- If you provide your consent, we also share information with law enforcement and other regulators here and overseas to help them investigate and prosecute scammers.
- You can make a report via Scamwatch anonymously or on behalf of another person.
- You can also make an official report to the police online.
- Report scams to the digital platform where they were encountered to assist with removal of the offending content.
The important role of business in scam prevention
- Impersonation scams can cause your business to suffer reputational damage or loss of revenue., not to mention the financial and emotional toll they can have on your customers.
- Business owners are not immune to being targeted by scammers. In fact, scammers impersonate well-known businesses and brands by creating fake websites, publishing fake ads, and sending fake communications that look just like the real thing.
- If your business has been the subject of impersonation by scammers, Scamwatch has published guidance to support you to deal with impersonation of your business online.'
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omits personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
Many businesses turn to MailGuard after an incident or a near miss, often as a result of an email similar to the one shown above. If unwanted emails are a problem for your business, don’t wait until it’s too late.
Reach out to our team for a confidential discussion by emailing expert@mailguard.com.au or calling 1300 30 44 30.
One email is all that it takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security. Talk to a solution consultant at MailGuard today about securing your company's inboxes.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







