MailGuard has detected a new phishing email attack brandjacking Telstra.
Phishing is one of the most common and harmful cybercrime types. The sophistication of these email scams varies a lot, from simple plain-text emails to very realistic forgeries that are hard to distinguish from genuine email notifications.
Unfortunately, Telstra is brandjacked in email scams on a regular basis, but this new attack is one of the most sophisticated phishing attacks MailGuard has seen recently.
The criminals behind this phishing email have created very convincing forgeries of a Telstra email notification and login portal that features extensive graphical branding elements.
The sender display address on the email header is also deceptively realistic, shown as; “telstraemailbill_noreply@online.telstra.com”
The phishing email (see image above) links to the login page shown in the screenshot below:
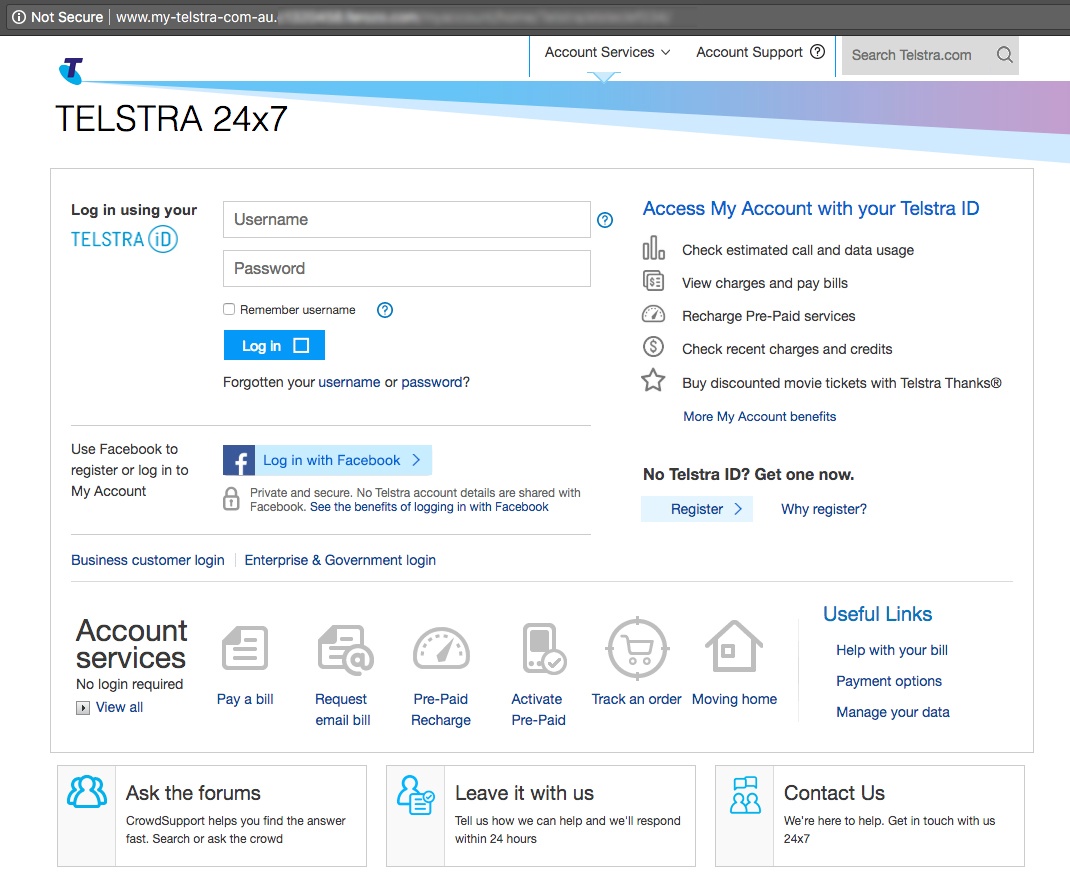
The criminals who designed this fake login page have gone to considerable lengths to make it look legitimate. MailGuard’s analysts have determined that the format of this page may have been directly copied from a genuine Telstra site.
The domain used in the scam is also cunningly deceptive; “www.my-telstra-com-au” is shown in the browser address bar at the top of the page. It should be noted that the browser displays the warning "not secure" beside the URL, which is a red-flag indicator of a criminal intent website.
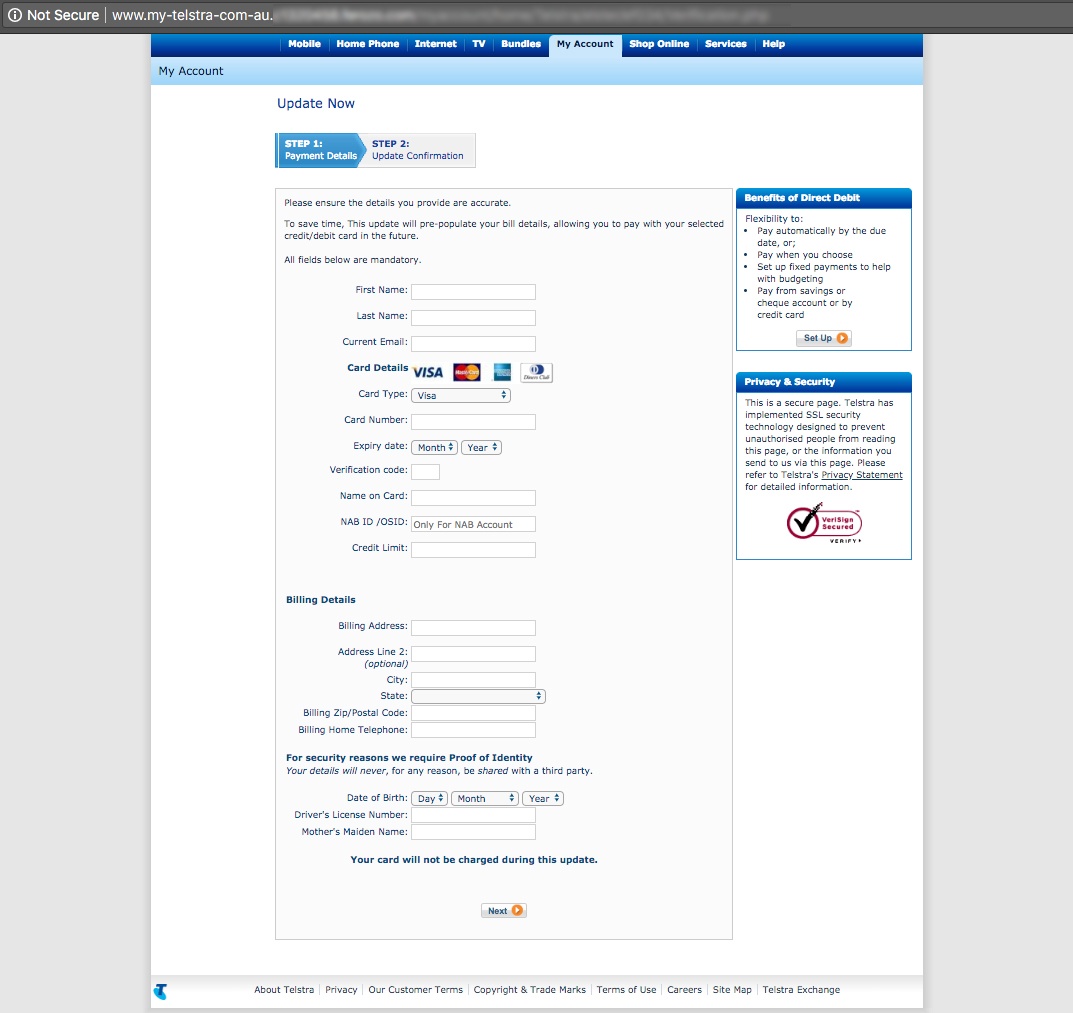
Once the intended victim has submitted their Telstra credentials in the page shown above, they are forwarded to a second page that harvests their personal data and credit card details:
Well designed phishing attacks like this one can be very hard to spot.
In our busy lives, we are often hasty in reacting to emails and criminals take advantage of that.
Please help us alert people to this phishing attack by sharing this blog post on your social media; click the buttons at the top of this post.
What is "phishing?"
Phishing is the practice of trying to trick email recipients into clicking on a link or revealing personal information that criminals can exploit for gain.
Phishing emails go to a wide group of random people; it’s like a fisherman casting a wide net to see what he can catch. The attackers know that not everyone will respond, but they know that if they send enough emails out somebody will probably take the bait.
A phishing attack message will typically include a link that will send the unwary victim to a fake login website. Once there, the user will be asked to enter username and password data which will be automatically captured by the phishing page.
Scammers use phishing pages to collect login credentials for email accounts, bank accounts, and a wide range of other online services.
What is "brandjacking?"
Brandjacking is basically a kind of forgery. Scammers use the trademarks of well-known companies in their emails to deceive their victims and gain their trust.
In a typical brandjacking scam, criminals create email templates that look like messages from big companies and send them out wholesale to millions of recipients. When the scam message shows up in a victim’s inbox they feel safe opening it because it looks like a legitimate message from a familiar company.
Some commonly used brandjacking formats are fake invoice notifications or requests for account verification.
Stay up-to-date with new posts on the MailGuard Blog by subscribing to free updates. Click on the button below:







