Cybersecurity, infosec, data-security; whatever you call it, this is an industry with enough jargon to make the average person’s head spin. Terms like phishing and ransomware are familiar to most of us, but what is a dropper? And what does a catfish do?
Sometimes it is necessary to be specific to make the message clear, and that’s where jargon becomes very useful.
On the MailGuard Blog we try to use language everyone can understand, but the broader IT media uses a huge lexicon of specialised terms that can be bewildering to non-tech people.
Cybercrime is growing very fast so it’s becoming increasingly important for businesspeople to be across the cybersecurity lingo.
With that in mind, the MailGuard Blog presents:
Cybersecurity Jargon for Businesspeople
Anti-Virus
Software designed to prevent infection by computer viruses; typically installed on an individual device.
Most antivirus programs include both automatic and manual scanning capabilities.
Botnet
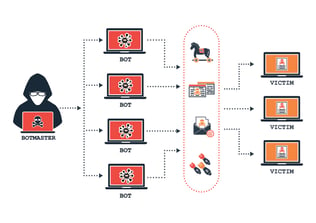
A network of compromised computers also called a ‘zombie network.’
In order to create a malicious botnet, a cybercriminal must first compromise several computers. They can then run automated programs or "bots" on all the systems at the same time.
A hacker may create a botnet for several different purposes, such as spreading viruses, sending e-mail spam, or crashing Web servers using a DoS attack (see below). Botnets can range from only a few computers to several thousand machines.
Brandjacking
A cybercrime technique where the criminals create a fake website or email message that looks like it belongs to a well-known company. Brandjacking has a high success rate because it exploits people’s confidence in popular brand-names. Victims of brandjacking scams are lulled into a false sense of security by recognisable logos and are deceived into providing login credentials or other valuable data.
Brand types that are regularly exploited by criminals include (but are not limited to); financial institutions; telco's; utilities; and media companies.
Read more about Brandjacking, here.
Catfish
Internet predators who create fake online identities to lure people into emotional or romantic relationships for personal or financial gain. Online seduction and blackmail are the stock-in-trade of the catfish.
Cloud-Based Security
Cloud-based security solutions provide a remote approach to detecting and mitigating security threats. Organisations deploy third-party cloud-based security software between remote users and their systems. The cloud-based security provider can examine network traffic for known attack patterns and pass only legitimate traffic through to users. This allows the solution to stop attacks in the cloud before they reach the target agency’s data centre or applications.
Cybercriminal
The reason we use this term at MailGuard is to distinguish between hackers and criminals.
A cybercriminal is anyone using the internet to commit crimes.
Hackers are often law-abiding people working in cybersecurity to prevent crime (hackers will be discussed more below).
Cybercriminals are not necessarily hackers, although many of them are. Hackers are IT experts with high-level skills. Many cybercriminals have no special IT knowledge and are just using ready-made software tools to commit crimes, or they are fraudsters, manipulating their victims through 'social engineering' (see below).
Dark Web
The dark web is made up of internet content that exists on ‘darknets,’ overlay networks which use the Internet but require specific software, configurations or authorization to access. The dark web forms a small part of the deep web, the part of the Web not indexed by web search engines, although sometimes the term deep web is mistakenly used to refer specifically to the dark web.
The darknets which constitute the dark web include small, friend-to-friend peer-to-peer networks, as well as large, popular networks like Tor, Freenet, and I2P, operated by public organizations and individuals.
The dark web is used for many kinds of criminal activity, including buying and selling malware and compromised data.
Data Breach
A data breach is a security incident in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an individual unauthorized to do so. Data breaches may involve many kinds of information including: financial records; credit card details; or corporate intellectual property.
DoS and DDoS Attacks
A denial-of-service attack (DoS attack) is a cyber-attack where the perpetrator seeks to make a resource unavailable to its intended users by flooding it with requests.
In a distributed-denial-of-service attack (DDoS attack) the incoming traffic flooding the victim originates from many different sources. This effectively makes it impossible to stop the attack simply by blocking a single source.
DDoS attacks are usually accomplished using ‘botnets’ (see above).
Drive-by-Download
A piece of software that is automatically downloaded to a victim’s computer without their consent. This strategy is often used in email scams to install malware or spyware via a ‘dropper.’
Dropper
A piece of code that has been designed to install some sort of malware, such as a virus, to a target system. The malware code can be contained within the dropper (single-stage) in such a way as to avoid detection by virus scanners or the dropper may download the malware to the target machine once activated (two stage).
Fullz
A slang term used by cybercriminals referring to full packages of identifying information; name; social security number; DOB; account numbers; etc. Fullz are typically sold to identity thieves who use them in credit fraud schemes.
GDPR
 In May 2018 the EU will introduce the ‘General Data Protection Rule,’ a regulatory system designed to penalise companies that allow data breaches to occur. Under the GDPR regime companies and organisations that are compromised may be subject to penalties up to 4% of their annual revenue.
In May 2018 the EU will introduce the ‘General Data Protection Rule,’ a regulatory system designed to penalise companies that allow data breaches to occur. Under the GDPR regime companies and organisations that are compromised may be subject to penalties up to 4% of their annual revenue.
Read more about the GDPR in this article on the MailGuard Blog.
Hackers: Black-Hat & White-Hat
A hacker is someone who has the skills to gain unauthorised access to a computer system. Hackers fall into two broad categories: black-hat and white-hat.
Black-hats are hackers with criminal intentions. Black-hat hackers find system vulnerabilities and use them to steal data, extort ransoms and seize control of computers.
White-hats are hackers who work to keep data safe from other hackers by finding system vulnerabilities that can be fixed. White hat’s work is not illegal because it is done with system owner's consent, and they are usually well paid for their expertise.
Keylogger (Keystroke Logger)
This is a kind of surveillance software that can record every keystroke made on a computer’s keyboard. A keylogger can record everything a user types including instant messages, email, usernames and passwords. The data captured by a keylogger will be sent to a specified receiver without the user’s knowledge.
Link-to-Payload Attack
A cybercrime technique that involves links to malware disguised as benign content. Link-to-payload attacks are commonly used in email scams to induce victims to unwittingly install malware that is hidden in .zip files. A link in the email message will say something like 'click here to view your statement,' but the link will go to an executable malware file.
Malware
Malware (or malicious-software) is any program or file that is harmful to a computer user. Malware includes viruses, worms, Trojan horses and spyware. These malicious programs can perform a variety of functions, including stealing, encrypting or deleting sensitive data, altering or hijacking core computing functions and monitoring users' computer activity without their permission.
NDB Scheme
As of February 2018, Australian companies that trade in personal information or collect customer data will be required to notify individuals if their personal information is compromised. These new rules are part of the Australian Government’s NDB (Notifiable Data Breach) Scheme. If credit card records or other sensitive data is accidentally exposed or stolen by cybercriminals, companies will be obligated under the Privacy Act to make it known to their customers. If a company fails to fulfil their new obligations as specified in the NDB scheme, there is provision for legal and financial penalties under the new legislation.
More info about the NDB Scheme, here.
Penetration Testing (Pen Testing)
Penetration testing (also called pen testing) is the practice of testing a computer system or network to find vulnerabilities that cybercriminals could exploit. The main objective of penetration testing is to determine security weaknesses. A pen test can also be used to test an organization's security policy compliance, its employees' security awareness and the organization's ability to identify and respond to security incidents.
Pharming
A technique used by cybercriminals to redirect victims to fake websites without their knowledge.
Websites use domain names - such as bank[dot]com - but their actual location is determined by an IP address. When a user types a domain name into their browser's address field and hits enter, the domain name is translated into the relevant IP address. The browser then connects to the server at the specified address and loads the website data it finds there. After a user visits a certain website, its IP address information is stored in the computer’s cache for future reference.
One way that pharming attacks are executed is that a cybercriminal may use a virus to ‘poison’ a user's cache. The pharming attack will corrupt the cache entry for a given website so that when the user types in bank[dot]com their browser will direct them to a scam website that looks like the real bank one. The URL in the browser will still look correct, but the IP address the user is sent to will be a fake one controlled by criminals.
Phishing
This is a similar kind of attack to pharming, but phishing is much more common.
Phishing utilises fraudulent email messages or websites that are used to gain access to victim’s personal information. Typically, a would-be victim of phishing will receive an email message pretending to be from a trusted source such as a financial institution or telco. The scam email will instruct the recipient to log into their bank account, credit card account, etc and the link provided will direct them to a fake website controlled by cybercriminals. When the victim enters their personal data it is captured by the criminals and then sold or exploited. Many phishing attacks are very expertly designed and victims are often none-the-wiser until it is too late.
Ransomware
 Malware which handicaps computer functionality - usually through browser hijacking or encrypting personal data - and offers to restore the functionality conditional on payment of a ransom.
Malware which handicaps computer functionality - usually through browser hijacking or encrypting personal data - and offers to restore the functionality conditional on payment of a ransom.
This is a very common form of cybercrime. Ransomware is often delivered via links in malicious email.
Read an article about ransomeware on the MailGuard Blog, here.
Social Engineering
Psychological manipulation techniques employed by cybercriminals. A wide variety of social engineering techniques are used in activities such as CEO fraud and phishing. Many social engineering scams are executed by gathering data about victims from social media. Social engineers harvest personal information about people that they can use to create spear-phishing attacks or send counterfeit messages.
Spear-Phishing
As described above, phishing is a fraud technique that uses fake email messages to gain access to victim’s personal information.
Spear-Phishing is an email driven fraud format that targets a specific organisation, or specific people within an organisation. Spear-phishing usually involves some form of social engineering (see above) to gain the confidence of intended victims. Unlike phishing, spear-phishing emails are addressed to deliberately chosen recipients rather than being sent out randomly.
Spyware
Spyware is software that is installed on a device without the end user's knowledge.
Spyware aims to steal personal or sensitive information by performing a set of operations covertly. General actions spyware can perform include: advertising; collection of personal information; and changing user configuration settings of victims computers.
SSL (Secure Socket Layer)
The most widely used security protocol on the internet for online banking and shopping sites. Website digital certificates are commonly implemented through SSL. Generally speaking, the presence of 'https://' as opposed to ‘http://’ in the browser address bar indicates that the connection between your computer and the website is SSL encrypted.
Trojan Horse
Malicious code that is hidden in a computer program or file that may appear to be useful, or at the very least harmless. When this computer program or file is run, the malicious code is also triggered covertly, resulting in the installation of malware.
Virus
Malicious software designed to install itself on a computer and replicate. In order for a virus to infect your computer, you have to run the infected program, which in turn causes the virus code to be executed. This means that a virus can remain dormant on a computer, without the user’s knowledge. Once a virus infects a computer it is designed to spread itself to other computers on the same network. Stealing passwords; key-logging; corrupting files; and spamming email contacts are some of the actions virus malware is typically designed to execute.
Whaling
 Whaling is a type of email fraud targeting high-level management of companies and corporate executives. Like spear-phishing (see above), whaling usually involves a social-engineering component. The objective of whaling is to swindle a senior executive into divulging confidential company information. Whaling fraud is usually instigated via a fake email that appears to be from a familiar business contact.
Whaling is a type of email fraud targeting high-level management of companies and corporate executives. Like spear-phishing (see above), whaling usually involves a social-engineering component. The objective of whaling is to swindle a senior executive into divulging confidential company information. Whaling fraud is usually instigated via a fake email that appears to be from a familiar business contact.
Read more about whaling, here.
Worm
Computer worms are self-replicating malware that duplicate themselves to spread to new computers. Worms often hijack parts of an operating system that are automatic and invisible to the user. It is common for worms to be noticed only when their uncontrolled replication consumes system resources, slowing or halting other tasks.
A worm is very similar to a virus, but unlike a virus it requires no interaction with the user to be triggered and can duplicate and spread autonomously.
Stop Cybercriminals
If your company is using an integrated productivity platform like Office 365, then you already know the benefits of cloud-based technology. Doing business online opens up opportunities for collaboration communication on an unprecedented level, but with that opportunity comes significant risk. Cybercriminals utilise sophisticated AI technology to monitor business and social networks and they exploit the data they collect to infiltrate organisations. All criminals need to break into your business is a cleverly worded email; if they can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's cloud-based email and web filtering security.
Talk to an expert at MailGuard today about making your company's network secure: click here.
Stay up-to-date with new posts on the MailGuard Blog by subscribing to free updates. Click on the button below:







