Commonwealth Bank customers are again being targeted by cybercriminals with a new phishing scam designed to steal customers’ credentials, including their name, date of birth, zip code, phone contact, credit card and client number and password details. As one of the most respected brands in corporate Australia, and an expansive customer base, Commonwealth Bank customers must remain vigilant when receiving emails about problems with their account.
The subject of the email is, ‘We noticed an attempt to sign into your account’, and the body of the email uses CBA branding to boost credibility, advising recipients that there seems to have been an unrecognised device attempting to access the users account, and that due to security reasons the account has now been disabled.
Here’s what the email looks like:
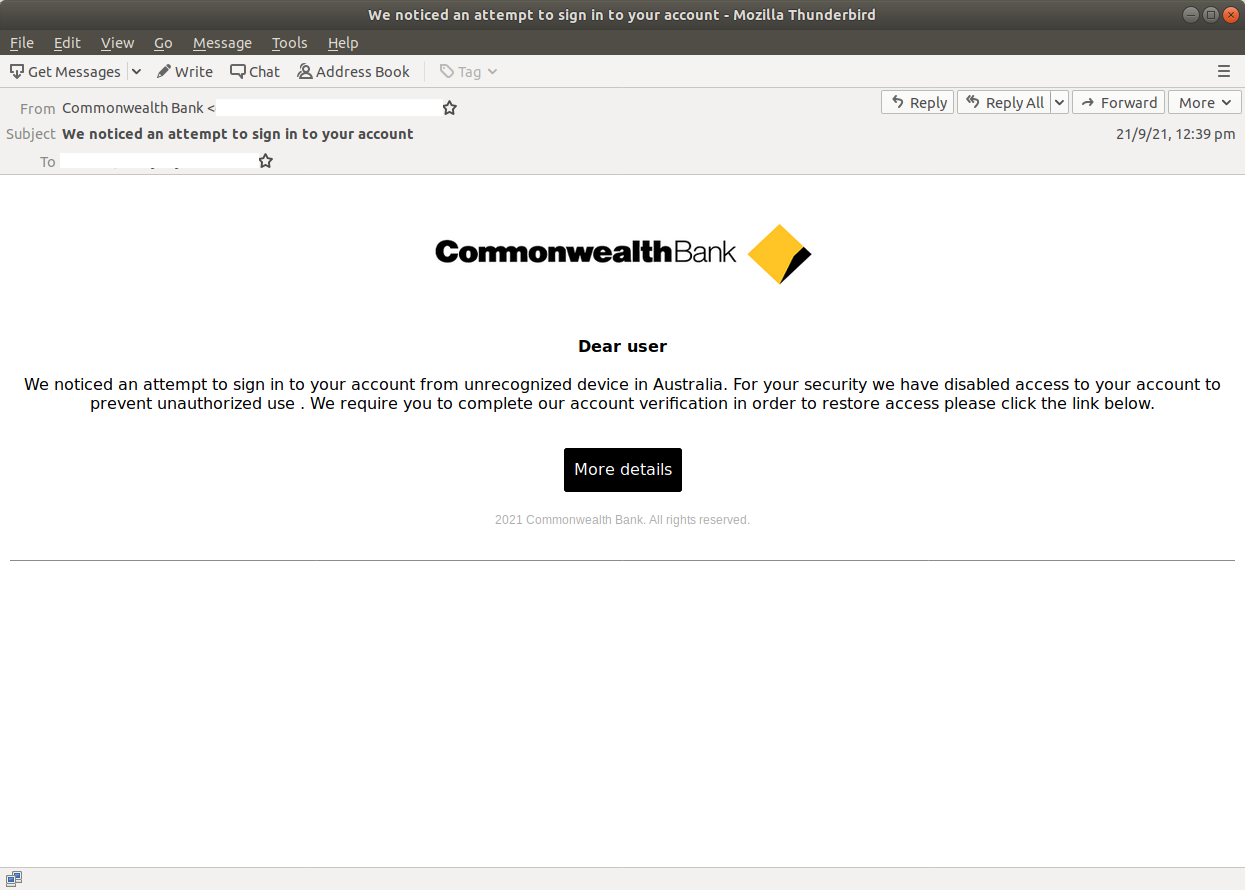
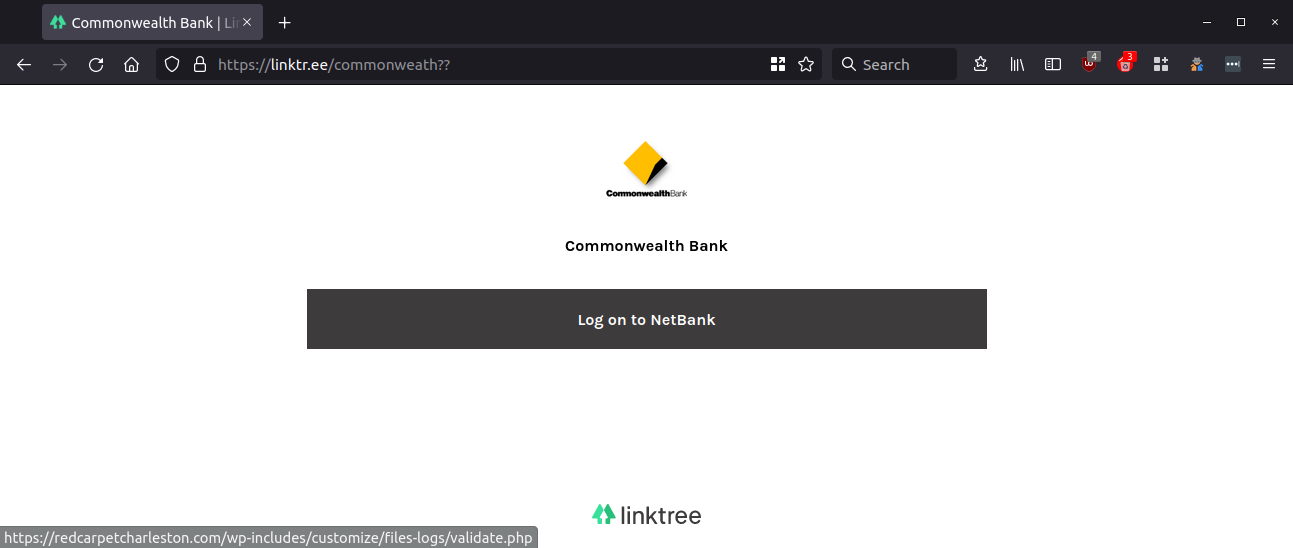
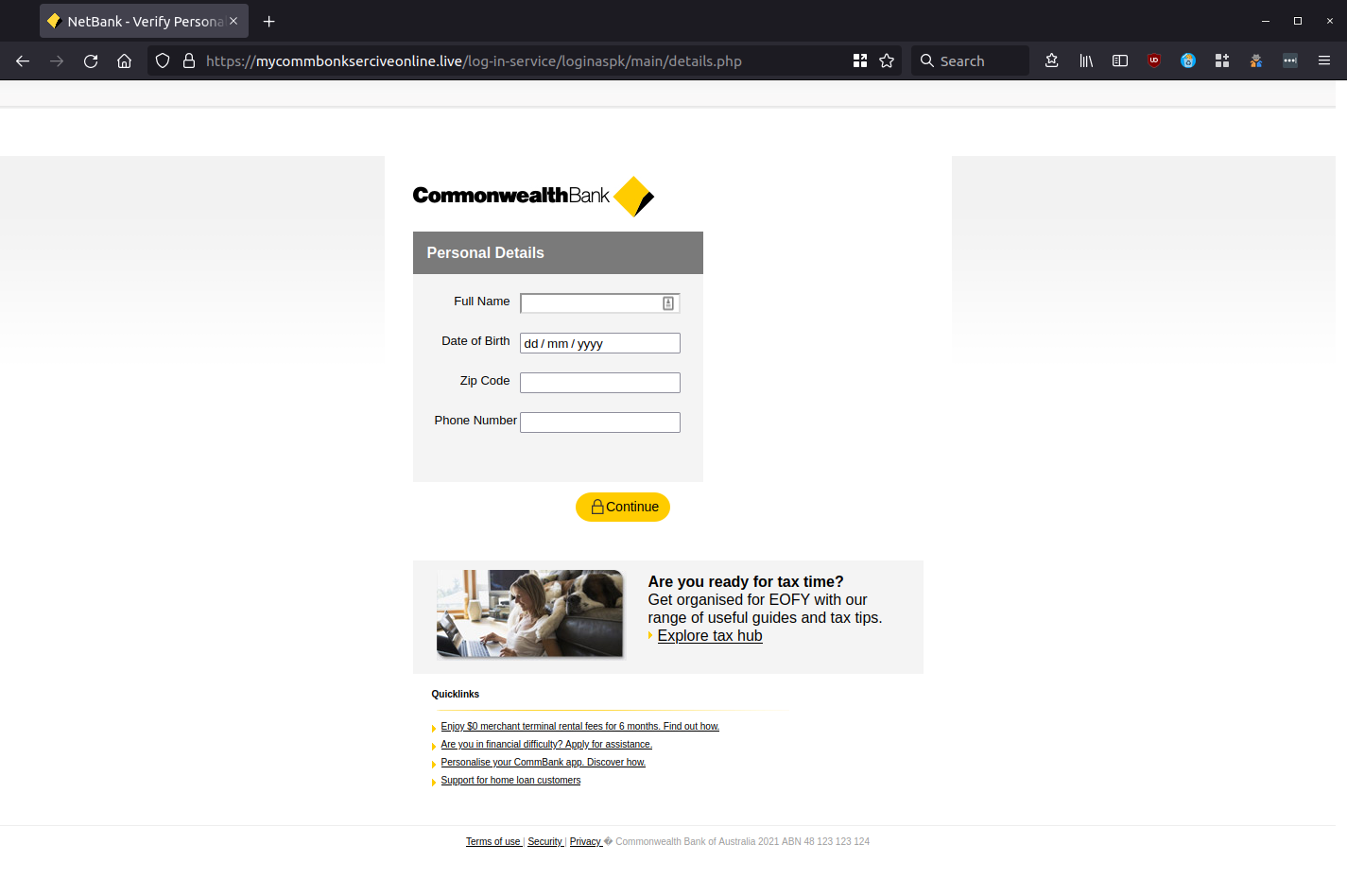
Recipients are asked to click on the ‘More Details’ button to complete an identity verification that the scammers advise will ‘restore access’ to their online account. The victim is taken to an intermediary page with ‘LinkTree’ and CBA branding. Clicking on the ‘Log on to NetBank’ button takes the user to the first phishing page requesting their client number and password.
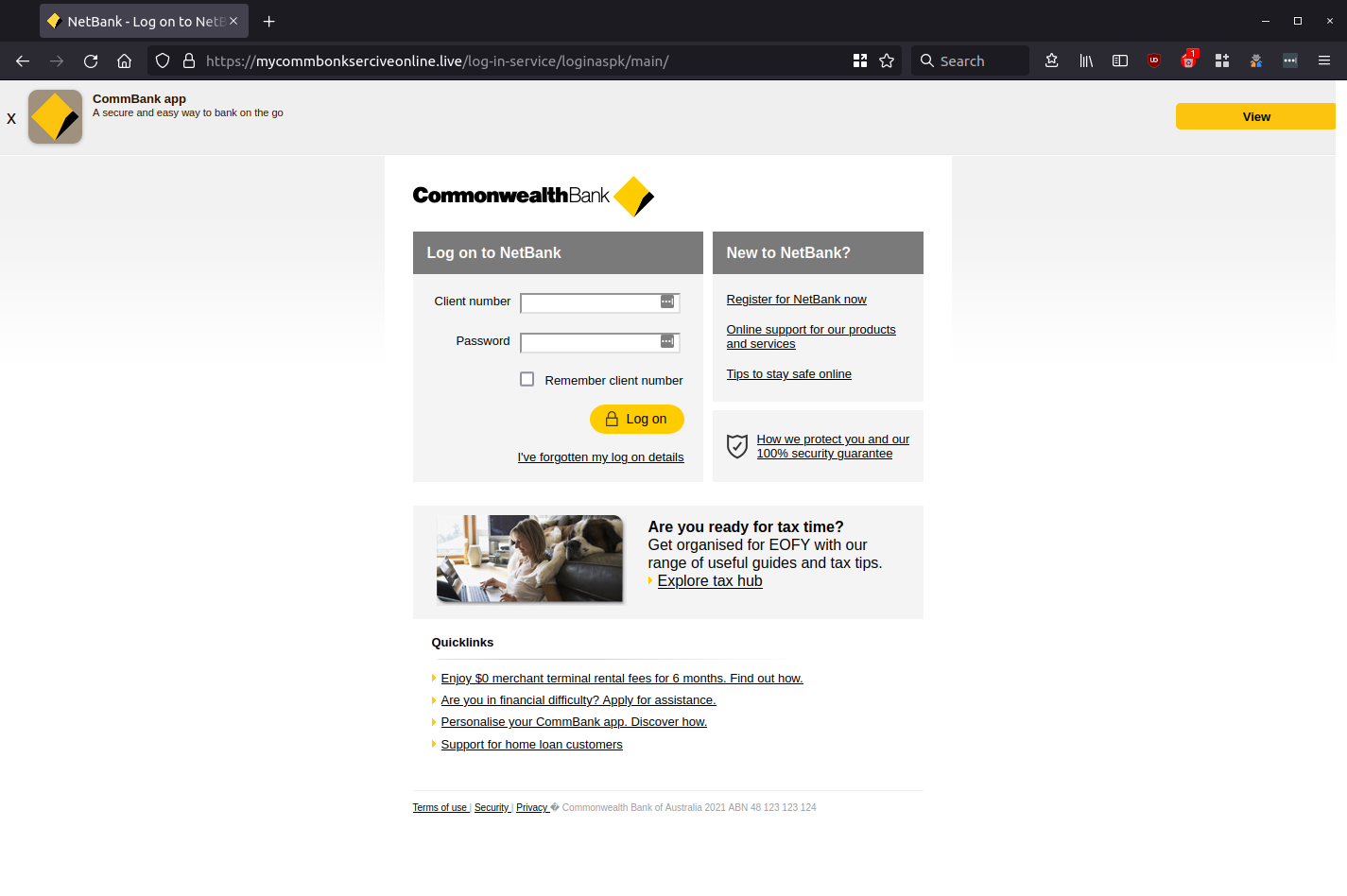
As you can see, the above screenshot is a replica of the actual Commonwealth Bank online banking page. By using extra details, such as an ‘App’ suggestion, ‘Quicklinks’ to other CBA services, and blog links with imagery similar to that used by the bank, unsuspecting users may easily be tricked into entering their details without a second take.
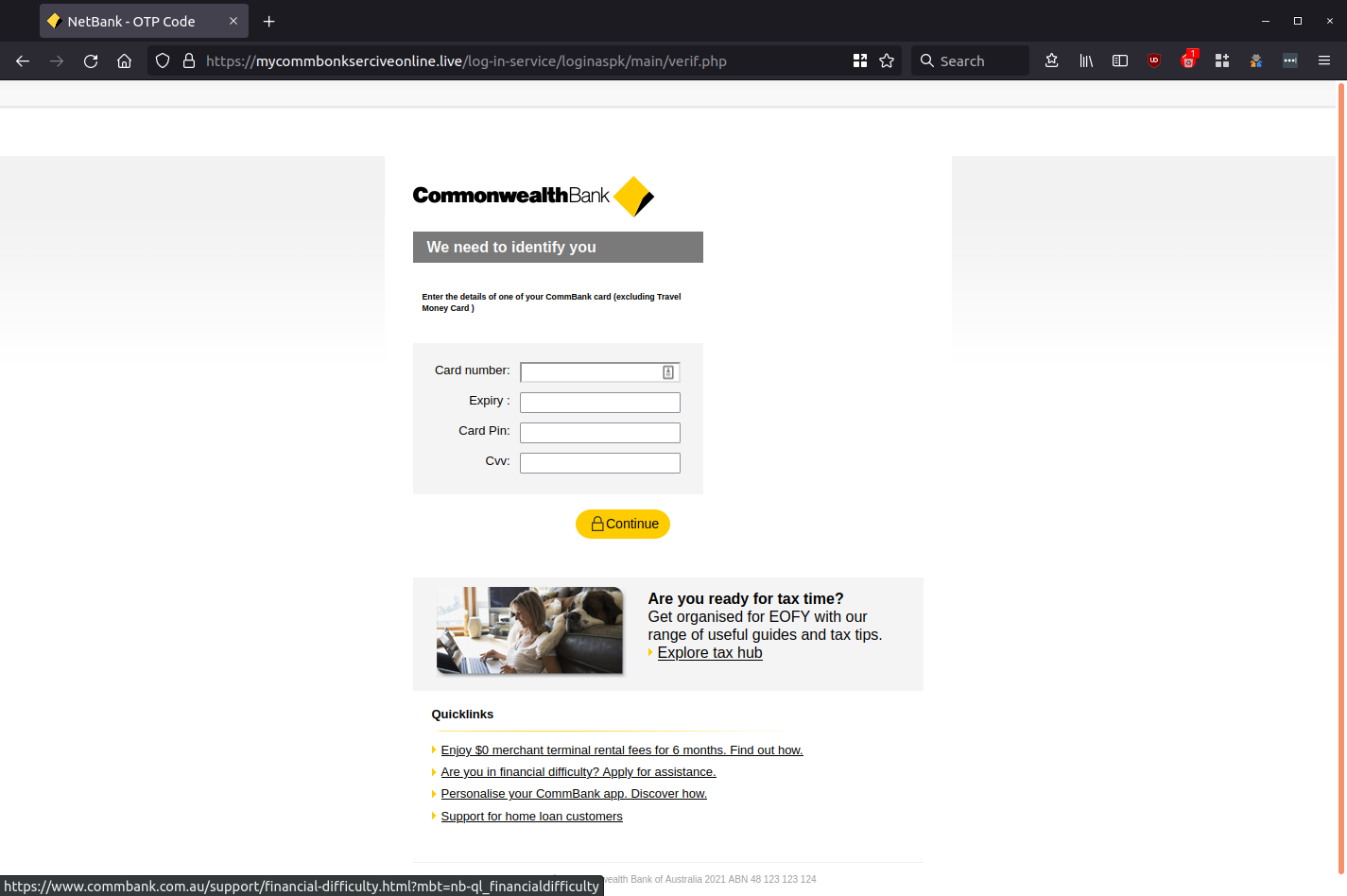
Once the user does ‘Log on’ to their account, providing the scammer with their client number and password, they are then taken to the next phishing page asking for their One-Time Password (OTP) sent to the user’s mobile phone number.
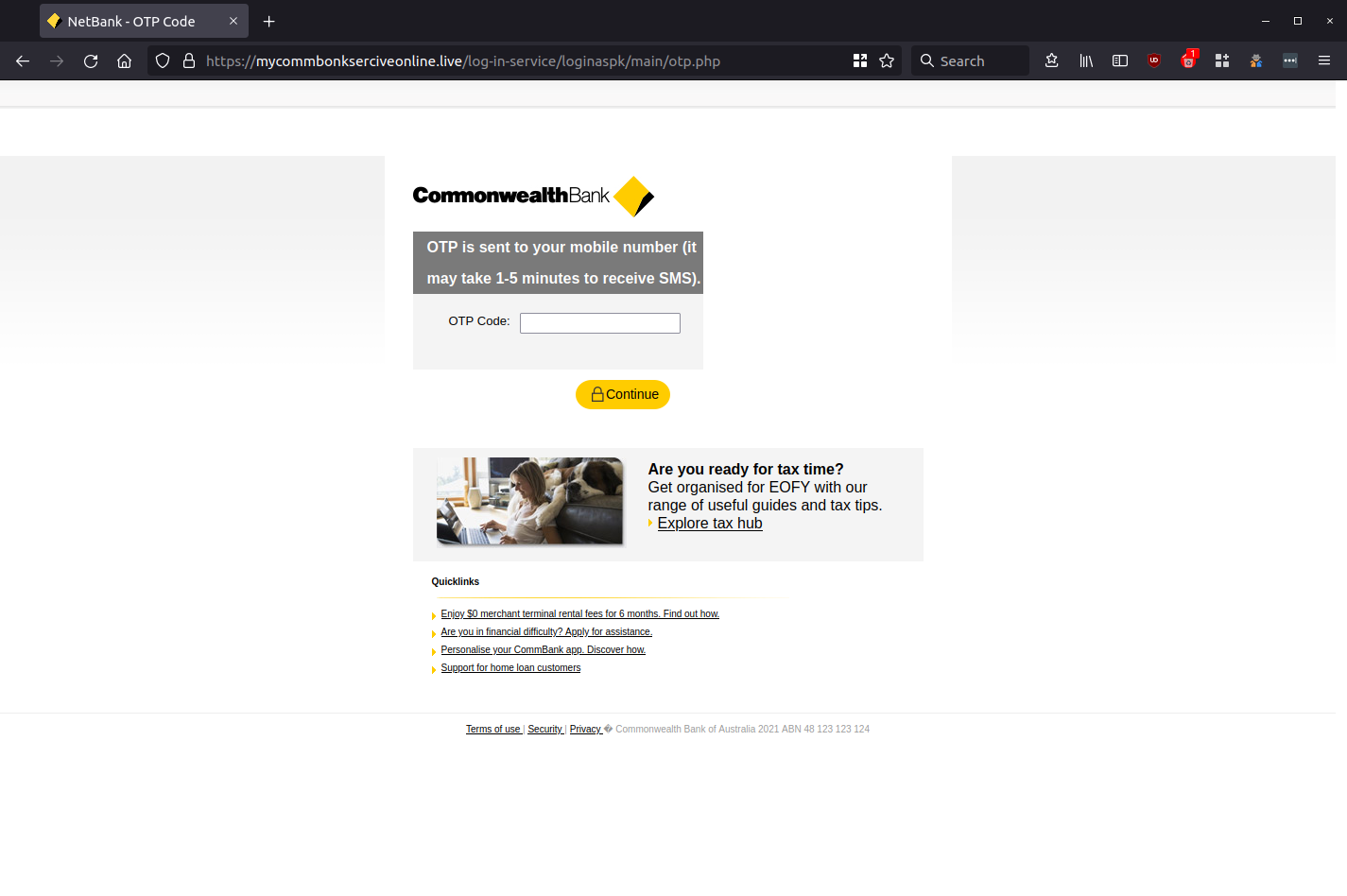
This stage of the phishing process is included to further trick the victim into believing that this is a legitimate communication, as many banks use OTP as a defence against financial fraud. After which, they are taken to the next two phishing pages below, the first asking for the users’ name, DOB, zip code and phone number and the second requesting the client’s credit card details.
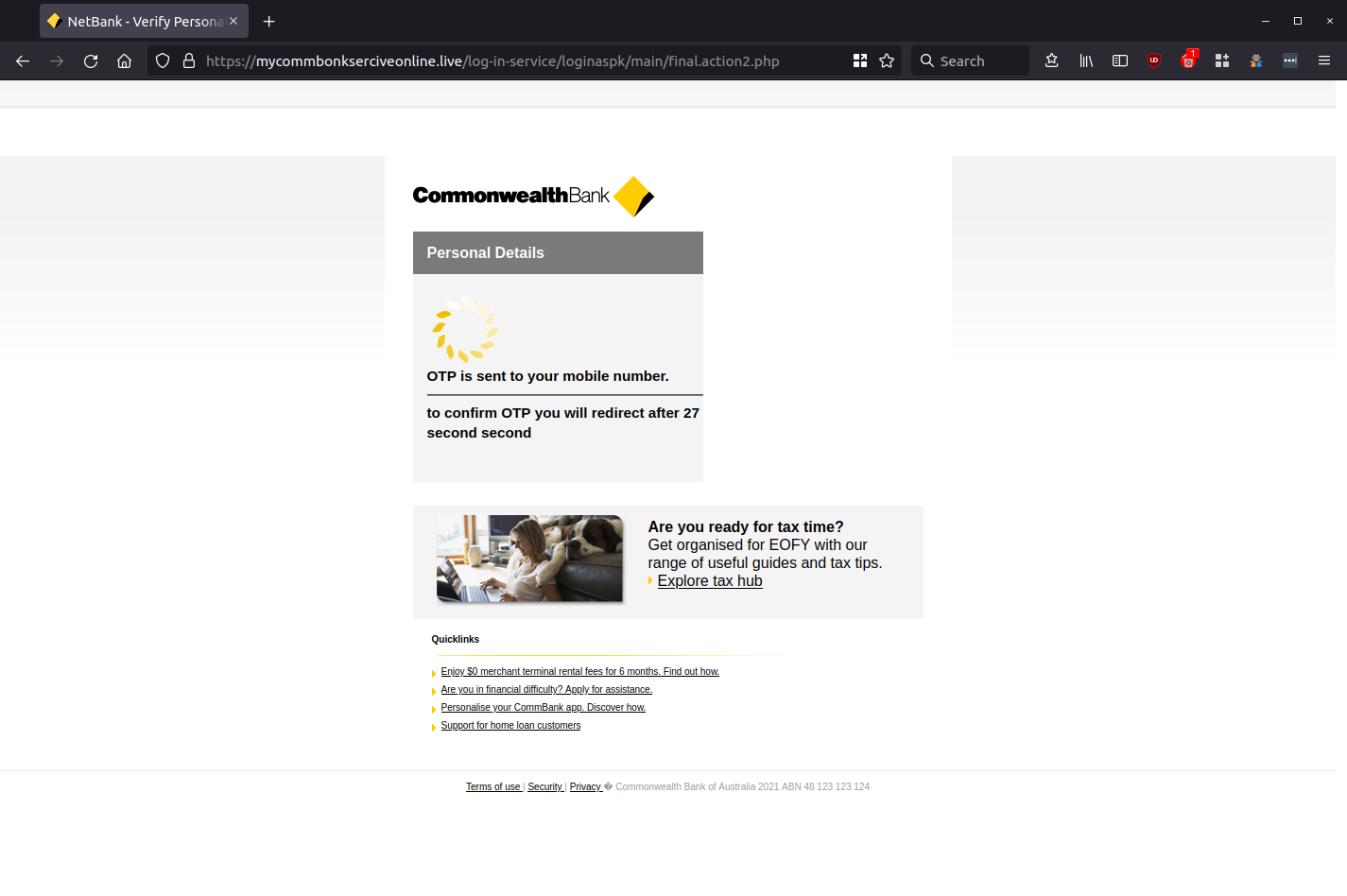
After the attacker has harvested these credentials, victims are provided with the following OTP verification message, before being redirected to a legitimate CommBank login page.
Although the scammer has gone to great lengths to imitate CBA’s email communications, upon closer inspection, grammatical errors present in the body of the email, as well as the domain address (e.g. ‘mycommbonkserviceonline(dot)live’) and the addition of a LinkTree hosted intermediary page are all red flags.
MailGuard urges all recipients of this email to delete it immediately without clicking on any links. Providing your personal details can result in your sensitive information being used for criminal activity and can have a severe impact on your financial well-being.
Commonwealth Bank (CBA) advises customers that have concerns about the safety of their accounts to call 13 2221 immediately, and provides the following advice on its website (https://www.commbank.com.au/support/security/sms-phishing-scams.html) for customers concerned about email and SMS scams:
- “Remember, we'll never ask you for your banking information by email or text message
- Stop before you click
- To be safe, always navigate directly to NetBank yourself and log on from the site you know to be genuine, rather than using any links in communications
- Report suspicious emails to hoax@cba.com.au then delete them straight after. Do not reply or engage with them
- Be aware that scams can also come via the telephone with people pretending to be from a reputable organisation who try and gain access to your computer, bank account and money. In this case the best thing you can do is hang up and call on an organisation’s officially listed phone number to verify the communication”
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security. Talk to a solution consultant at MailGuard today about securing your company's network.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







