Amazon Web Services (AWS) account holders need to be on the lookout for a phishing email purporting to be from the AWS-Support team, advising recipients that they need to consent to the processing of their personal data in accordance with EU Regulations. The shift to remote working means that cloud services are in demand, with cybercriminals taking the opportunity to capitalise on the increased use by businesses of services like AWS to steal credentials.
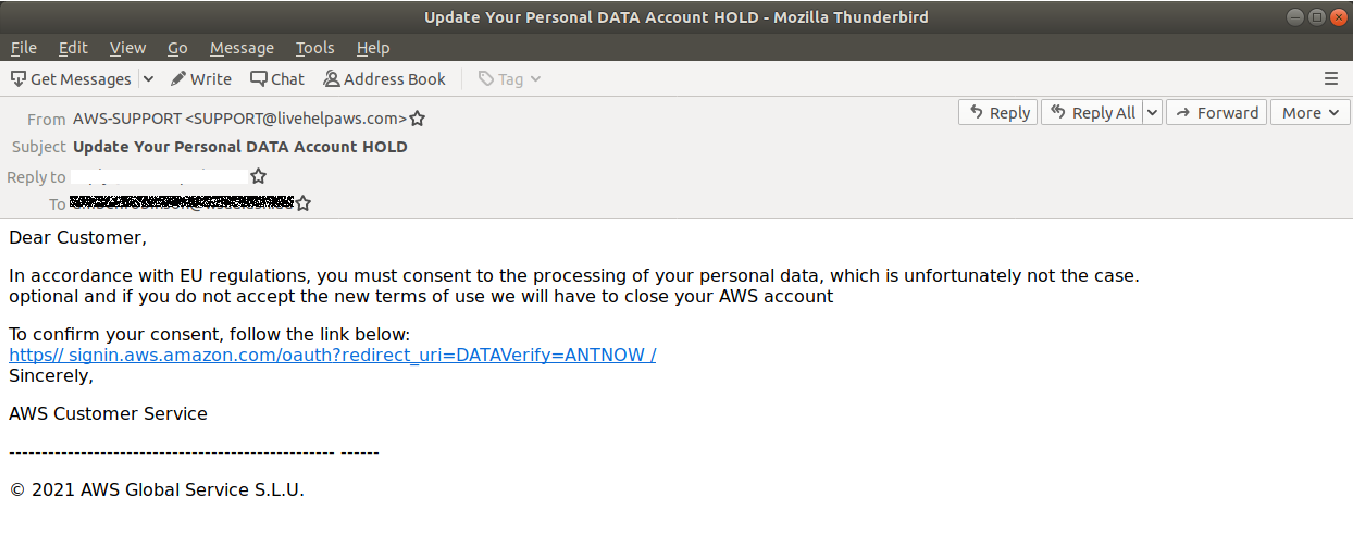
With the subject heading ‘Update Your Personal DATA Account HOLD’ purporting to be from ‘AWS-SUPPORT’, the body email informs the recipient that they have not consented to the use of their personal data, which is not in accordance with EU Regulations.
The email looks like this:
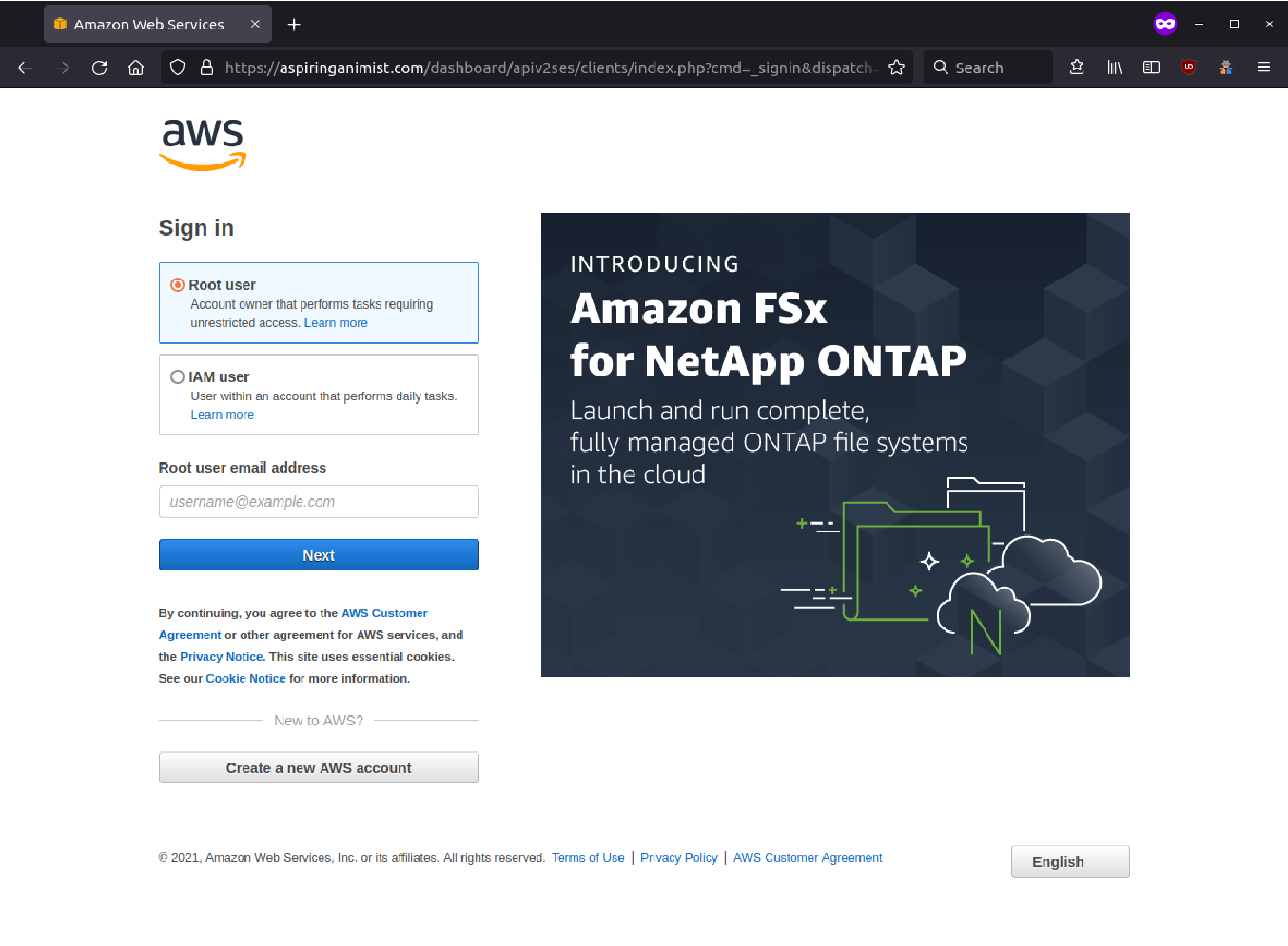
Clicking on the link provided in the email, sends the user to a phishing page as displayed below. This page asks for the ‘Root Account’ or ‘IAM User Account’ details. Here, the scammers have included the AWS logo and branding to make it seem more authentic.
Once the user has selected their preference to login as a ‘Root user’ or ‘IAM user’, they are taken to the page below which has pre-populated their email address and requests that the corresponding password be entered.
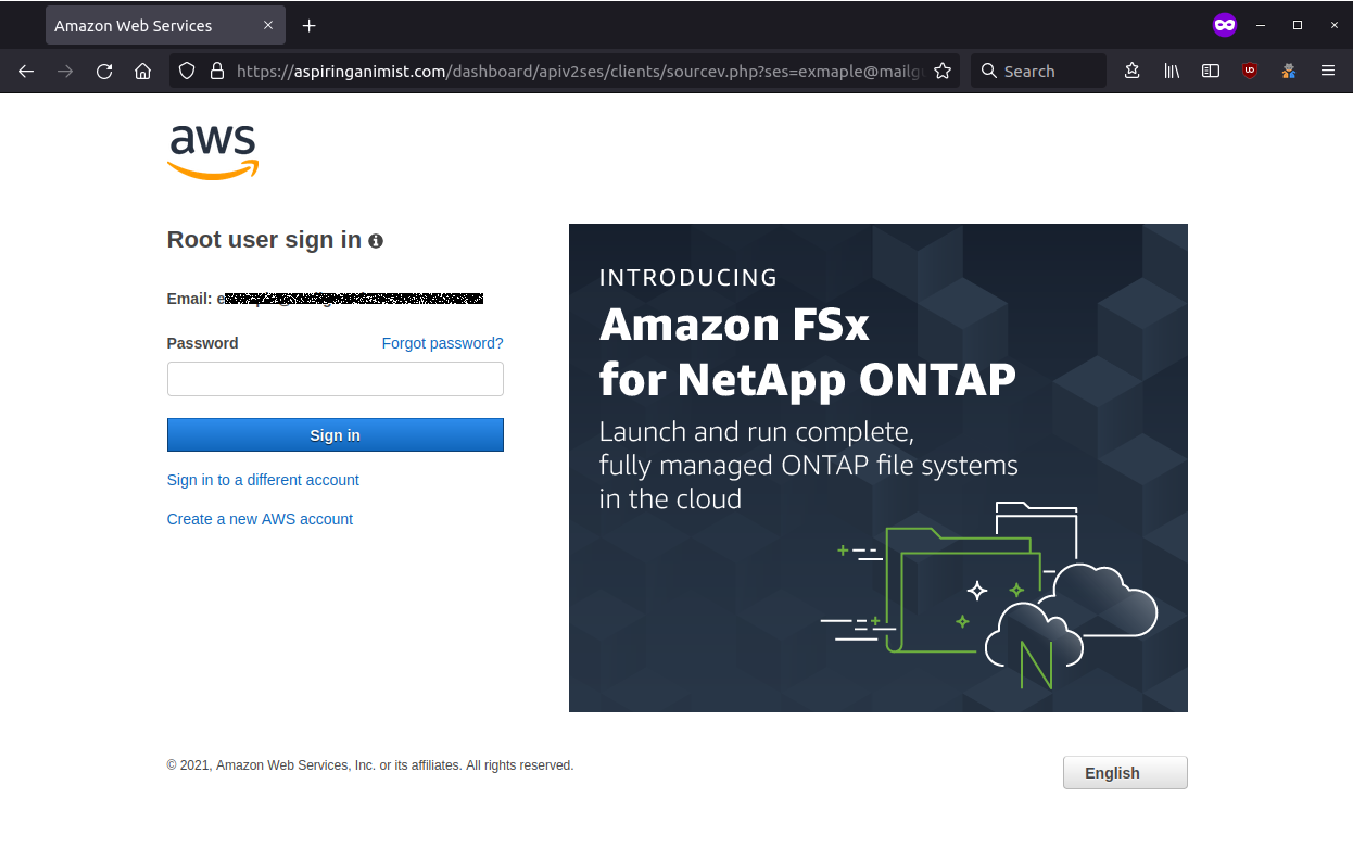
Once these credentials have been captured by the attackers, the victim is redirected to a legitimate AWS Help Blog Article, as an attempt to make the user believe that they have provided their details to a genuine AWS Support department.
AWS provide the following advice:
“If you receive an email that appears to be from Amazon, but you're not sure that it is, don't follow any links or open any attachments in the email.
Instead, sign in to your Amazon Web Services (AWS) account or Amazon.com account to take action or view notifications.
If you're still not sure, check the following:
- Does the subject of the email match the content of the email?
- Are the grammar and spelling of the email correct? Incorrect grammar or spelling often indicates suspicious sources.
- Does the email request the password or any other account-specific details of your Amazon account? Amazon and AWS never request sensitive information over email.
- Does the content of the email make sense in context? For example, if the email appears to be confirming a password reset, have you recently reset your password? If it appears to be requesting address information to complete an order, have you recently ordered anything from Amazon.com?
If you can answer "no" to one or more of the above questions, the email you received might be a spoofing email. For instructions about how to report potential email spoofing scams, see Report Suspicious Emails”
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes.
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security. Talk to a solution consultant at MailGuard today about securing your company's inboxes.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







