
The spectre of cybercrime continues to loom large over businesses globally. The Australian Cyber Security Centre (ACSC) released its Annual Cyber Threat Report in September, offering comprehensive, yet alarming, insights into the threat landscape facing Australian businesses. As a trusted advisor to your customers, it’s a must read for MailGuard partners. We share some highlights below, and a link to the full report.
The key threats identified in the report, centre around the exploitation of the pandemic environment, disruption of essential services and critical infrastructure, ransomware, exploitation of security vulnerabilities, supply chain risks and business email compromise (BEC).
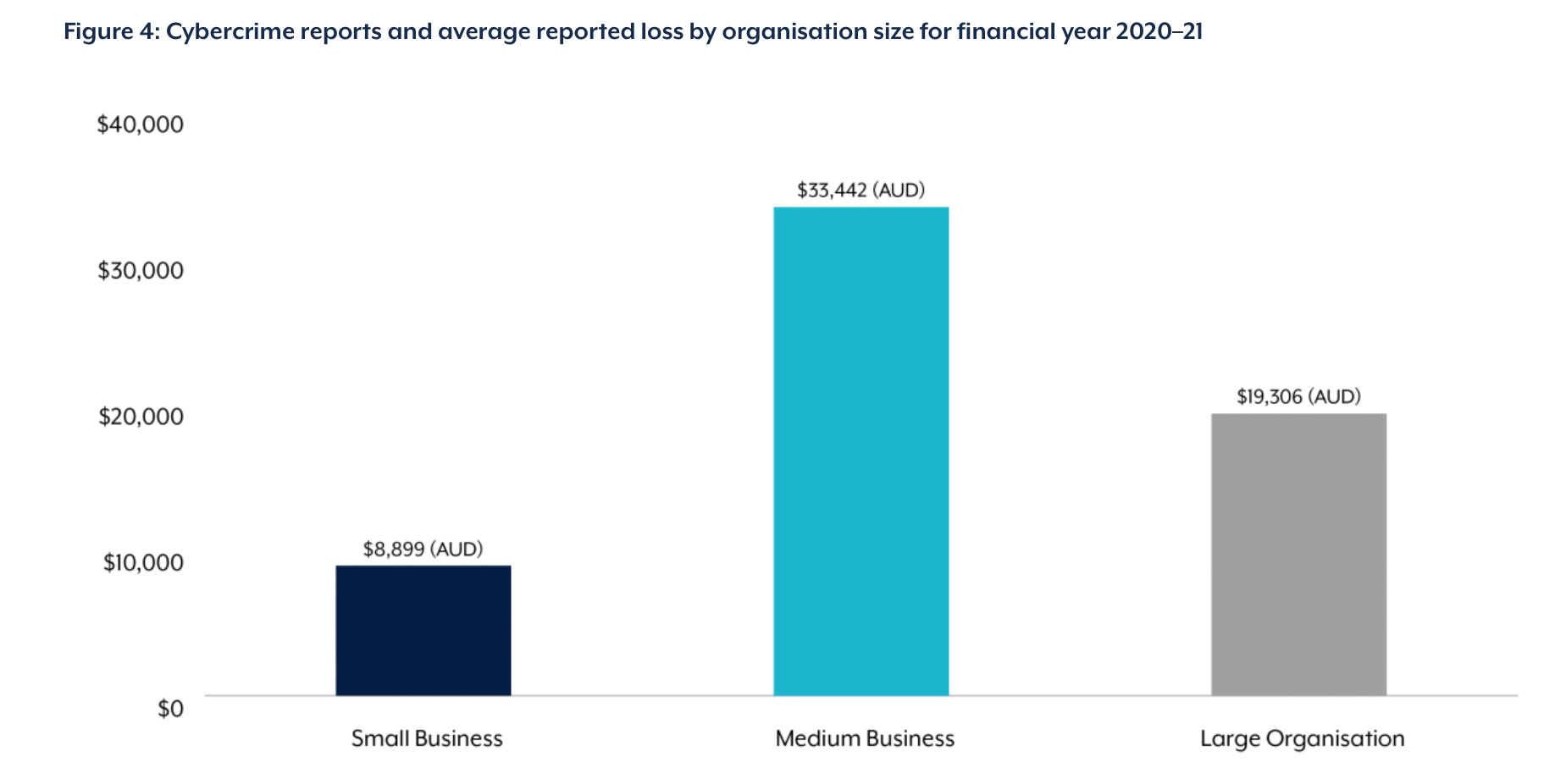
The report finds that medium sized businesses were hardest hit, with average losses of nearly $33.5K (AUD) from incidences that occurred in the last year.
The global pandemic and the shift to remote and hybrid working increased the attack surface for cybercriminals, highlighting the need to boost the cyber resilience of your customers:
"The coronavirus pandemic continued to expand the boundaries of Australia’s computer networks, pushing corporate systems into homes across the nation as a large percentage of the workforce shifted to remote working arrangements. The speed at which this occurred saw many organisations rapidly deploy new remote networking solutions, sometimes to the detriment of their cyber security. Various malicious cyber actors repeatedly took advantage of Australia’s heightened vulnerability during this time to conduct espionage, steal money and sensitive data, and disrupt the services on which Australians rely”.

Ransomware On the Rise
Ransomware threats have consistently been in the news headlines globally in recent times, so it’s no surprise that Australian businesses and organisations were not immune, with the ACSC receiving nearly 500 ransomware cybercrime reports – an increase of nearly 15% from the previous financial year.
It’s interesting to note, that the industry sectors that suffered ransomware attacks the most were the professional, scientific, technical and health sectors. Concerning, due to the critical services that each of these sectors provide, and the plethora of data that cybercriminals will be privy to in the event of a breach.
The report found that the most common vectors for deploying ransomware were phishing campaigns, targeted spear phishing, remote access through vulnerable machines and the use of publicly available exploits. In addition, the personal information found on professional and social networking platforms, such as LinkedIn, have been seen to provide threat actors with information for targeting certain individuals and organisations through spear phishing and other socially engineered online approaches.
If you have customers that are yet to implement MailGuard to enhance their email security, the ACSC report provides an excellent opportunity to revisit that position. You can also share the eBook, ‘Ransomware: The Worst Year Ever’. You can download a copy here: https://www.mailguard.com.au/the-worst-year-ever. Speak to your Account Manager about what more we can do to assist you reaching out to your customers.
In December 2020, the ACSC also launched the Act Now, Stay Secure campaign, to provide advice to Australians on protecting themselves from ransomware. It promoted a new technical ransomware guide, published by the ASD, including a prevention and protection guide, and emergency response guide and two step-by-step guides, that you can also share.
Business Email Compromise
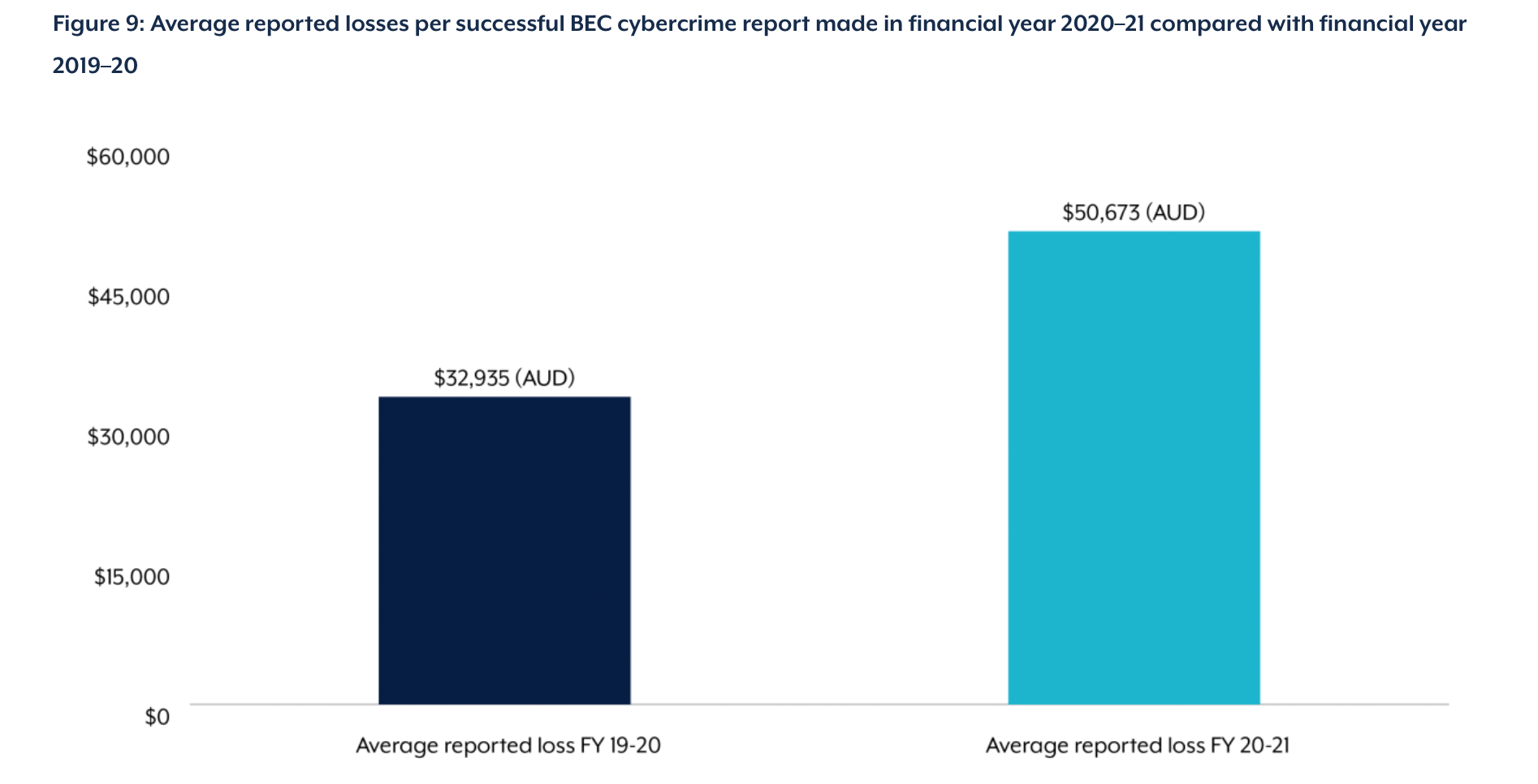
Business Email Compromise (BEC) continues to be a threat, with total losses at approximately $81.45 million (AUD) according to the report. That’s an increase of nearly 15% from the previous year. Staggering figures for Australian businesses, considering that the average loss per successful BEC attack has increased by 54% in the last year alone.
The report suggests that an increase in BEC attacks has been prevalent in organisations where employees are working remotely, with cybercriminals using BEC to target organisations with lures for purchases of personal protective equipment (PPE) and other supplies needed to combat coronavirus.
As we know all too well here at MailGuard, and supported by the ACSC report, BEC scams are becoming more and more sophisticated, with cybercriminals able to bypass cybersecurity protocols. That’s why we recommend a multi-layered approach to email security – no one solution can prevent every attack.
To put it into context, the following case study from the report outlines the impact of BEC on businesses, often resulting in financial loss, reputational damage and more:
“Case Study: Australian hedge fund subject to BEC and declared bankruptcy
In September 2020, an Australian hedge fund was subject to BEC and forced to declare bankruptcy as a result. The BEC involved false invoices with the company transferring $8.7 million (AUD) to bank accounts controlled by the offenders. While the business recovered the majority of its funds, it suffered significant reputational damage and its main client withdrew. This forced the hedge fund to go into receivership and resulted in its bankruptcy. This was likely Australia’s first bankruptcy case as a direct result of a cybercrime incident.”
In response to the growing threat of BEC, Operation Dolos was established by the Australian Defense Force, as a taskforce to help prevent and investigate BEC. In the 2020-21 financial year, Operation Dolos was able to prevent more than $8.45 million (AUD) being lost from the Australian community to BEC.
Protecting your business in a remote work environment
The ACSC provides the following helpful insights for business leaders and Infosec professionals to protect their organisations from cybersecurity threats in a remote and hybrid workforce:
- Be aware of scams – educate employees to recognise scams and social engineering and the risks associated with phishing, including opening malicious links and using social media networks. Raise awareness of good personal cyber security hygiene.
- Enable multi-factor authentication – have multi-factor authentication enabled by default on any corporate networks, devices or systems.
- Update devices and systems – update software and turn on automatic operating system updates.
- Use passphrases – these are most effective when they are long, complex, unpredictable and unique.
- Follow the ACSC’s COVID-19 specific guidance for: individuals working from home, small and medium businesses, large organisations (Operational Technology Environments), and government.
- Use a virtual private network (VPN) – these are an additional layer to securing web browsing and remote access over Wi-Fi. Note that this does not secure actual devices or online accounts, so it is important that these are also up to date.
Cyber resilience is a must for businesses
An overall analysis of the findings from the report reveal an indisputable truth: cyber resilience must be increased. The lack of which will result in more Australians affected by cyber threats, and ultimately catastrophic losses financially and with regards to critical data breaches.
“Despite the headlines, many of the compromises experienced by Australians will continue to be fuelled by a lack of adequate cyber hygiene. This delivers a significant advantage to adversaries and lowers the technical barrier to targeting victims in Australia, highlighting the need to uplift cyber security maturity across the Australian economy. Given the prevalence of malicious cyber actors targeting Australian networks – which is often under-reported to the ACSC – there is a strong need for greater resilience, and for Australian organisations and individuals to prepare to respond to and recover from any cyber-attack to their networks”.
To read the whole report: https://www.cyber.gov.au/acsc/view-all-content/reports-and-statistics/acsc-annual-cyber-threat-report-2020-21
Keeping businesses safe and secure
Share this overview of the ACSC report with customers and their teams as a reminder of the cyber threats that are facing businesses of all sizes, and to share recent statistics. Education is vital, with employees being the front line in a multi-layered defence against cybercrime.
Prevention is always better than a cure, and the best defence is to encourage businesses to proactively boost their company’s cyber resilience levels to avoid threats landing in inboxes in the first place. The fact that a staggering 94% of malware attacks are delivered by email, makes email an extremely important vector for businesses to fortify.
No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be an open dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282 2
UK partners call 0 800 404 8993
We’re on Facebook, Twitter and LinkedIn.






