
A PwC survey released at the end of 2020 highlighted fears of growing cyber-attacks targeting local critical infrastructure.
Australian business leaders said that they were expecting more cyber-attacks in the next 12 months than their global peers, including 56% of local executives who anticipated “attacks on the nation's critical infrastructure which could shut down vital services such as hospitals.”
Three months into 2021, and those fears appear to be well-founded. Cyber-attacks on local critical infrastructure like hospitals and universities are getting more prolific, with the potential for long-term and catastrophic consequences. CyberCX’s latest Annual Threat Assessment summarises the climate succinctly: "In critical infrastructure sectors, the cyber security challenge is acute, and the consequence of failure is debilitating. Malicious actors - whether nation-states or criminals - have demonstrated their willingness and capability to breach Australian critical infrastructure through cyber security vulnerabilities".
Here are three recent examples of cyber-attacks targeting local critical infrastructure that occurred this year:
1. Eastern Health
In a particularly insidious cyber-attack, one of Melbourne's largest metropolitan public health services was forced to postpone some elective surgery procedures after experiencing a "cyber incident". Eastern Health, which operates the Box Hill, Maroondah, Healesville and Angliss hospitals, as well as a number of health services, including Yarra Ranges Health and Wantirna Health, had to take a number of its IT systems offline as a precaution. While Eastern Health stressed that "patient safety has not been compromised", it stated that “category two and three elective surgery procedures” had to be postponed.
At the time of writing, the hospital was “still experiencing significant impacts related to the cyber incident”, with many systems still offline.
2. Western Australia’s parliamentary email network
Western Australia's parliamentary email network was hit by suspected state-sponsored hackers as part of a global cyber-attack involving Microsoft Exchange software. The impacted mail server was consequently taken down. The “online strike”, which was detected in the middle of the state election campaign, occurred after the Australian Cyber Security Centre (ACSC) published an alert on its website urging organisations using Microsoft Exchange to urgently patch a number of vulnerabilities. “Thousands of Australian servers are believed to have been affected by the hack” on Microsoft Exchange, with reports circulating many organisations are "yet to patch affected versions of Microsoft Exchange, leaving them exposed to potential compromise".
3. Australian National University (ANU)
Australian National University (ANU) was in the news after staff received a "standard phishing email" falsely claiming positive COVID-19 cases had been recorded on campus. The email used the subject line "New positive positive COVID-19 cases among staffs" and included a fraudulent link purporting to provide more details about these cases. Many employees at ANU reported receiving the email, with some reporting the cyber-attack as “disturbing”. Here’s a screenshot of the email:
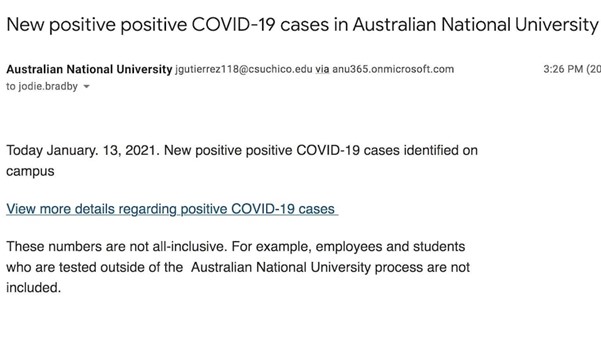
Source: ABC News
As you continue supporting your customers to help them remain cyber resilient, we encourage you to share these examples of cyber-attacks targeting local critical infrastructure. They remind us that cybercrime can strike anytime, anywhere, impacting critical systems that all of us rely on daily. In addition, they indicate the different and latest ways cybercriminals are attacking these networks and can help improve awareness of how to identify and avoid falling victim to them.
But more importantly, these examples act as a wake-up call for organisations across all industries to review and enhance their own existing cybersecurity strategies – especially because they flank a period in which the world endured not just a pandemic but some of the most aggressive and costly hacking episodes in modern history (e.g. SolarWinds). In addition, cyber-attacks on critical infrastructure have been making headlines not just in Australia, but across the world. For example, on the weekend of the Superbowl, a hacker infiltrated a computer used to control the water treatment system of Oldsmar, Florida, and briefly increased the levels of sodium hydroxide. Luckily, a supervisor working remotely noticed the changed concentration on his computer and reverted it to normal levels.
Essentially, risks to cyber systems have never been higher and organisations should urgently take proactive action to mitigate those risks. This includes focusing on the lessons learnt from these attacks, like patching any existing vulnerabilities within their Microsoft Exchange deployments, to avoid suffering a cyber-attack like Western Australia’s parliamentary network or fortifying email security to avoid being tricked by the phishing emails received by ANU staff.
Email-based cybercrime, in fact, continues to be an existential threat in Australia. Prime Minister Scott Morrison announced last year that Australian private & public sector companies were being targeted in “a massive cyber-attack” that included using phishing emails to trick users: "This activity is targeting Australian organisations across a range of sectors, including all levels of government, industry, political organisations, education, health, essential service providers and operators of other critical infrastructure," he said.
The attack was a reminder that email is the number one vector of cybercrime. Nine out of 10 cyber-attacks start with an email, even when most businesses have an email security solution in place. Precisely because email is a critical tool and arguably the most important means of communication among many businesses, it is imperative for businesses to consistently review their email security strategies to ensure they’re doing all that they can to stay safe. No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
Standing next to the PM during his announcement, Defence Minister Linda Reynolds reminded “all Australians that cybersecurity is a shared responsibility of us all", adding that it is "vital that all Australian organisations are alert to this threat and take steps to protect their own networks."
Let’s continue fulfilling our responsibility, as Australians, and as trusted cyber advisors, and use the lessons learnt from these recent attacks on local critical infrastructure to make our customers more cyber resilient than ever.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282![]() 2
2
UK partners call 0 800 404![]() 8993
8993
We’re on Facebook, Twitter and LinkedIn.






