Threat alert: two new email scams targeting Telstra customers are hitting inboxes. These well-designed email attacks both use fake Telstra bill notifications to trick victims into clicking on malicious links.
Scam #1: phishing page
The first scam variant directs the victim to a realistic looking fake Telstra login page that harvests their login credentials and credit card details.
This screenshot shows the fake notification message linking to the phishing site:
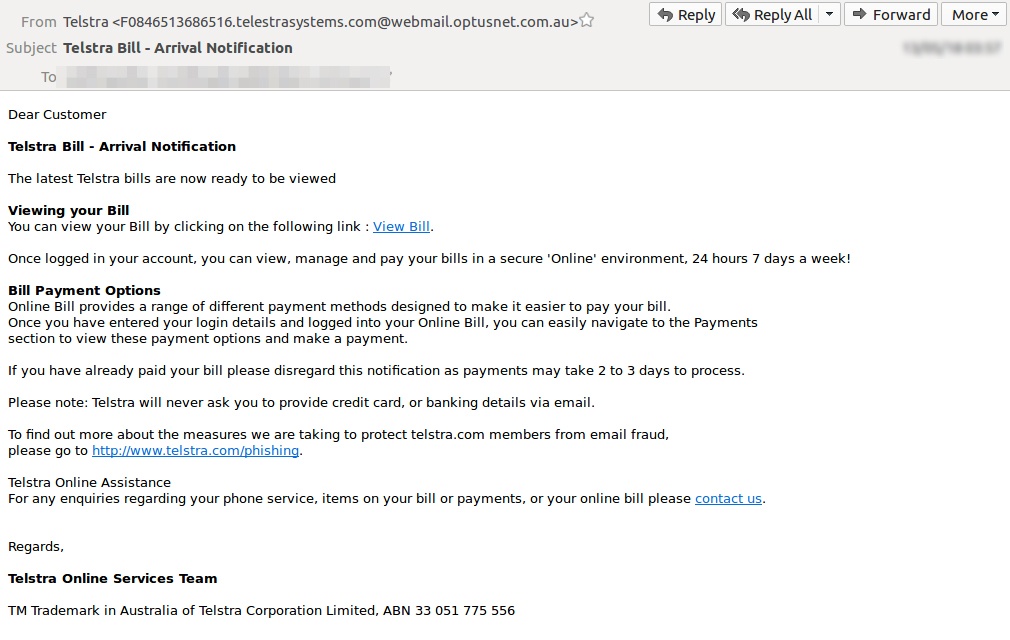
You can see that although the sender name is “Telstra” the actual sender email address is “f0846513686516.telestrasystems.com@webmail.optusnet.com.au”
This sort of mismatch between the stated sender and the email address is typical of an email scam and should be a red flag to recipients.
An unwary victim who clicks on the “View Bill” link in this message will be sent to a phishing page which is well designed and appears to be a genuine Telstra login portal. Once the victim has ‘logged in’ they will be shown the phishing page in the screenshot below:
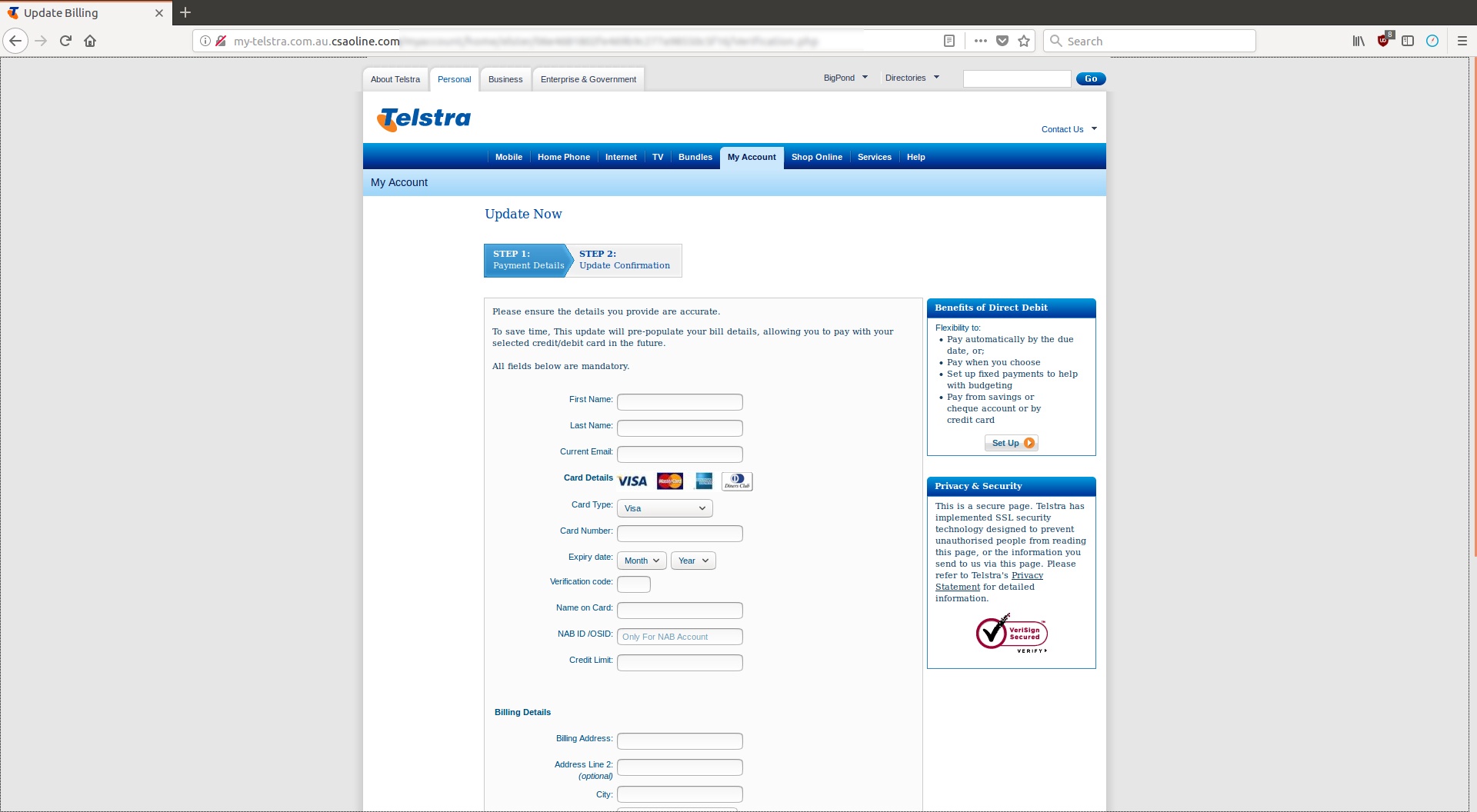
This phishing page collects the scam victim’s credit card details and personal data.
Once the criminals behind this scam have the information the victim submits to this page, they will be able to use their credit card in identity theft fraud.
Although this phishing page is well designed and exploits Telstra branding to look as convincing as possible, there are details that reveal this is a scam site:
- The first part of the site’s URL is “my-telstra.com.au” which looks legitimate, but that is followed by “csaoline.com,” which is the actual domain; csaoline.com is a new domain registered in America on May 12 and has no connection to the real Telstra website.
- Because this website was set up for the purposes of this scam and is not a secure domain, the padlock security icon in the browser address bar is disabled (see screenshot above).
Genuine credit card enabled websites operate only on secure domains, so this is a clear indication of a phishing scam.
Scam #2: malware
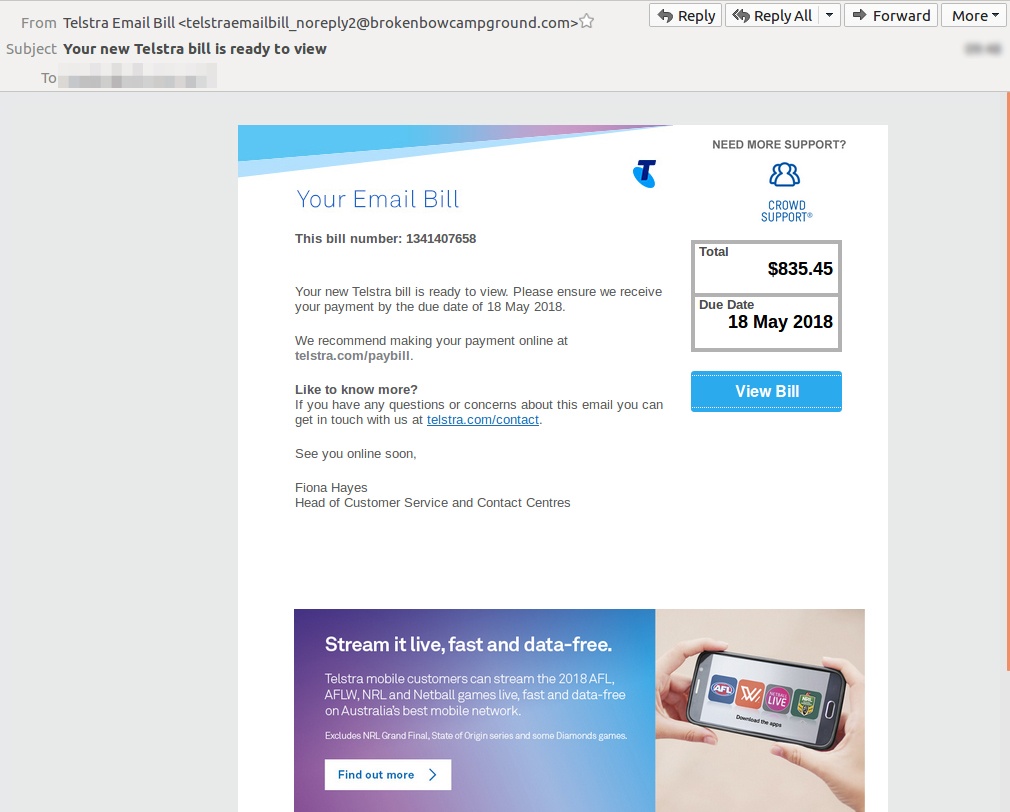
You can see in the screenshot above that this email scam is well designed and is quite a convincing fake Telstra bill notification.
A recipient who clicks on the “View Bill” button will be directed to a malicious website that will deliver malware to their computer. The malicious domain used in this malware attack is "telstrabroadband.com;" which has the appearance of a genuine Telstra URL. But actually, this domain is newly registered, having been created on May 13 via a registry in China.
Although the display name on this message is "Telstra Email Bill," this malware scam is being sent from a wide variety of delinquent email addresses, including:
- telstraemailbill_noreply1@360degreeshows.com
- telstraemailbill_noreply1@atticusfilm.com
- telstraemailbill_noreply1@butterflypassion.com
- telstraemailbill_noreply1@isaacmartinez.com
- telstraemailbill_noreply1@minocquasupperclub.com
- telstraemailbill_noreply1@pekingwillow.com
- telstraemailbill_noreply1@seminoleguardian.com
- telstraemailbill_noreply2@4webstudio.com
- telstraemailbill_noreply2@brokenbowcampground.com
- telstraemailbill_noreply2@cissyye.com
- telstraemailbill_noreply2@makenatapiceria.com
- telstraemailbill_noreply2@p2pwi.org
- telstraemailbill_noreply2@slammingsteel.com
- telstraemailbill_noreply2@stevenye.com
- telstraemailbill_noreply3@cyclocrossonline.net
Brandjacking
The fake Telstra email scams described above are typical brandjacking scams.
To steal our data, all cybercriminals need to do is get us to click on a link. Scammers are always looking for new ways to deceive us into falling for their tricks and one that has become extremely common in recent years is brandjacking. Criminals create email templates that look like messages from big companies and when they show up in victim’s inboxes they feel safe opening them because the logos and sender names look legitimate. Some common brandjacking scam formats are fake bill notifications from utility companies or requests for account verification from banks and credit cards.
If you would like to learn more about brandjacking scams, read MailGuard CEO Craig McDonald’s article; Brandjacking scams: data theft and malware hiding in plain sight.
Protect you business
If your company’s email accounts aren’t protected, brandjacking emails are almost certainly being received by your staff. Cybercriminals know we can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People aren't machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive email security.
Talk to an expert at MailGuard today about making your company's network secure: click here.
Stay up-to-date with new posts on the MailGuard Blog by subscribing to free updates. Click on the button below:







