Business email compromise (BEC) scams have been around for a while, but their continued success at bringing down organisations (both large & small) shows we’re dealing with an adversary that is constantly looking for ways to exploit our systems, our psychology & our trust.
Experts have warned that organisations in Australia continue to be plagued by BEC scams, urging proactive action in order to stay protected.
“Australian businesses reported over $14 million in losses to Scamwatch due to payment redirection scams last year, and average losses so far in 2021 are more than five times higher compared to average losses in the same period last year,” the Australian Consumer & Competition Commission (ACCC) stated in a special alert issued earlier this year.
“In a payment redirection scam, also known as business email compromise scams, scammers impersonate a business or its employees via email and request that money, which usually is owed to the legitimate business, is sent to a fraudulent account,” the ACCC stated.
The situation is worse in the U.S., with the FBI’s newly released 2020 Internet Crime Report stating Americans lost over $4.2 billion to cybercriminals and scammers in 2020. BEC scams were by far the biggest sources of reported losses, totaling $1.8 billion across 19,369 complaints.
Observing a similar trend, our team at MailGuard has continued to intercept sophisticated email threats this year, including BEC scams. Due to their highly targeted and personal nature, a lot of BEC attacks go unreported, so the actual number of BEC attacks and their resulting associated losses are likely to be far greater than the official published figures.
“Payment redirection scams impact businesses across many industries, including real estate, construction, law, recruitment, and universities,” ACCC Deputy Chair Delia Rickard said.
“An increasing number of reports are coming from sports and community clubs which reported more than $55,000 in losses to payment redirection scams last year. It is likely we will see similar figures this year, with $18,000 already reported lost so far in 2021… It can be difficult to recover money lost to a payment redirection scam, so prevention is really important,” she added.
It’s crucial that we don’t take these figures and warnings lightly and dismiss them as yet another update alerting us of a familiar cyber threat. Instead, these alerts serve as valuable opportunities for us to revisit conversations with our cybersecurity teams to ensure our business’ cyber defence strategies encompass all of the elements required to beat today’s evolving & sophisticated BEC scams.
As we continue fortifying our cybersecurity strategies, here are some of the latest BEC scams that made local headlines recently, along with a few valuable lessons and reminders that we can use for more well-informed and strategic discussions.
Invoice-related scams
Hacking into emails and altering invoices may be an old trick in a BEC scammer’s arsenal, but it is undoubtedly still effective.
Tesla was in the news this year after two local customers fell victim to BEC scams involving altered invoices and lost “thousands” of dollars. The first customer, Andrea Hammond, who was in the process of purchasing a Tesla 3 electric vehicle, was sent an email supposedly from the company. An attached invoice directed her to make her final payment of $74,647.62.
“That invoice was intercepted by hackers and the bank details changed…Andrea unknowingly paid the money to a fraudulent bank account instead of Tesla, sending her money straight into the hands of scammers,” stated an ABC News report.
Andrea Hammond transferred money into an account which was not associated with Tesla.
Source: ABC News
The second customer said the company emailed him on a Friday afternoon to inform him his Tesla 3 had arrived, with details of where to send the money.
"I should have checked the bank account details on the invoice by telephoning Tesla directly, but there was no phone number readily available to ring or to contact them. They wanted payment quickly because the vehicle had become available, so I paid the invoice," he said.
Again, the money didn’t end up going to Tesla.
Reminder: The devil is in the detail, stay vigilant.
This is a classic example of how cybercriminals hijack the trusted relationships that we all have with major brands like Tesla. Having realised the powerful influence and impact of brands on the minds of consumers, scammers often exploit the trademarks of well-known & trusted companies to deceive users. We have seen that scammers are investing more time and effort into producing communications that look authentic, just like those from the brands they are impersonating. In some instances, senior graphic designers and/or legal experts are employed by cybercriminals to design contracts and to use high quality design and branding elements within the emails.
In cases like these, it’s crucial to remind customers that vigilance is key whenever transferring funds online, especially when there are updates to banking details. When reviewing an invoice, even if it appears to be from a trusted brand, customers should keep a watch out for any red flags. These include checking for slightly altered email addresses, spelling and grammatical errors, and alterations on invoices, like mismatched fonts.
For businesses, the above scam is also a reminder to bolster their cyber defences to prevent hackers from infiltrating networks in the first place. Software should be kept up to date by regularly patching systems and running antivirus software.
Scams impersonating individuals
It’s common knowledge that many BEC scams involve exploiting the power and seniority in professional relationships. By mimicking a high-ranking executive for example, cybercriminals hope the recipient will be less likely to question a request or instruction. For example, it won’t be surprising for someone in a finance department to immediately reply to this email we intercepted below, sent supposedly from the CEO, requesting an unexpected bank transfer:
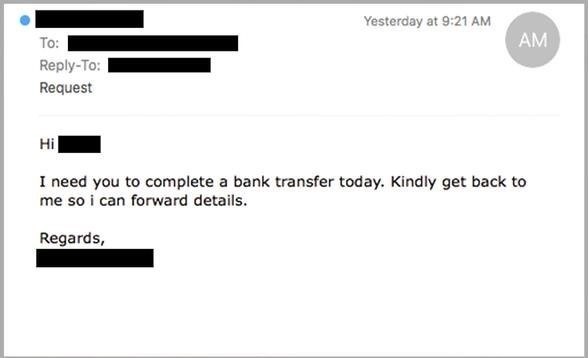
Explaining how such scams work, the ACCC said that often, “payment redirection is done by spoofing, when scammers impersonate CEOs or other senior managers using a registered email address that is very similar to that of the genuine email address. The scammer will then request that staff transfer funds to them or make a payment to a third party on behalf of the business”.
But it’s not always high-ranking, senior individuals who are impersonated. BEC scammers also pose as external parties and customers too, as with what happened with the Bank of Queensland (BOQ). A branch manager fell for a BEC scam after a customer’s email account was compromised and payment details for the final instalment of a loan were altered by a scammer. As a result, the bank lost $30,000 and the bank manager was dismissed.
BOQ’s customer had taken out an owner/builder construction loan and was seeking to make a final drawdown of $37,500 from it. Emails were the primary source of communication between the customers and the branch manager handling the case. Unfortunately, midway through, the customer’s email account was compromised, and a scammer started emailing instead. The emails implored the branch manager to pay out the remaining loan to a fraudulent CBA account.
Explaining why the branch manager was dismissed, the bank argued that she missed a series of red flags in emails sent from the hacked account of a BOQ customer and from email accounts used by the scammer.
However, “some of the flags were neither obvious nor out-of-character with the customer’s regular communications”, the Fair Work Commission (FWC) wrote in a judgment published earlier this year.
A staffer within BOQ’s financial crimes unit confirmed that “the first fraudulent email was actually sent from the customer’s email address, and ... there was nothing on the face of the first fraudulent email to indicate that it was being sent from an address other than the email address of the customer.”
Reminder: Verify, verify, verify
Before launching an attack, BEC scammers typically conduct thorough reconnaissance to research the companies and individuals involved, including the way they interact and the type of messages they exchange. This may have allowed hackers to manipulate the emails the branch manager received in a manner that didn’t raise any red flags. For instance, some red flags that the bank claimed the branch manager should have spotted included the language of the scam emails and the misspelling of CBA as “CommonWealth” on a scam invoice that was otherwise identical to the real thing. However, the FWC also noted the customer himself made typos in previous emails – making it difficult to differentiate between the fraudulent emails from the legitimate ones.
This scam is a good example of how BEC scammers use social engineering & mind games to exploit how people work and interact in business settings. Cybercrime isn’t only about hacking into technology, but getting inside the minds of users too. In cases like these, it’s crucial to remind our teams of the importance of verifying requests. They should contact the company/ person in question directly using a second, reliable mode of communication like a known phone number (known to them, not on the emails) to verify any request to transfer funds or for a change in bank details. While it can seem overly cautious to call the sender to verify what they’ve said, it can save a lot of pain in the long run.
Verifying requests includes contacting and questioning senior colleagues (like bosses or managers). Business owners should let their staff know it’s okay to ask questions, no matter how awkward they may be. For instance, if someone is purporting to be a senior executive and they’re asking for a transfer or transaction, businesses should pick up the phone and ask those people directly if they requested it. However uncomfortable it may be to ask that question, it’s better to have an awkward conversation today rather than to not have a job tomorrow.
Winning the war on the corporate email inbox
These are just a few examples of BEC scams that have struck organisations in recent times. There are many more, and they are irrefutable evidence that BEC scams continue to be an existential threat in Australia. It’s critical that we rise to the challenge and keep adapting our technologies and techniques in order to stay ahead.
Nine out of 10 cyber-attacks start with an email, even when most businesses have an email security solution in place. Precisely because email is a critical tool and arguably the most important means of communication among many businesses, it is imperative for businesses to consistently review their email security strategies to ensure they’re doing all that they can to stay safe from BEC scams. No one vendor can stop all threats, so don’t leave your business exposed. If you are using Microsoft 365 or G Suite, you should also have third-party solutions in place to mitigate your risk. For example, using a third-party cloud email solution like MailGuard to complement Microsoft 365. For more information about how MailGuard can help defend your inboxes, reach out to our team at expert@mailguard.com.au.
Along with the right technology, education is also key. Businesses should ensure all employees are aware of the formal transfer procedure in place and what to do if they ever receive unusual requests. They should also teach staff and employees what fraudulent emails look like. Show them real-life examples of BEC attacks that have occurred in the past and question them on how they would have responded to the scam emails. Executives should also learn to take special care when posting and sharing information related to work schedules on social media sites.
BEC and other social engineering-based attacks continue to be a widespread threat because they work. And what makes these attacks so unique — and difficult to stop — is that they leverage both technical compromise of trusted systems and people’s normal behaviours in order to infiltrate corporate inboxes. Let’s keep this in mind as we continue making our businesses more cyber resilient than ever.






