A new phishing email scam intercepted by MailGuard is a good reminder of the importance of thinking twice before clicking on links within an email – even if it appears to be sent from a legitimate sender.
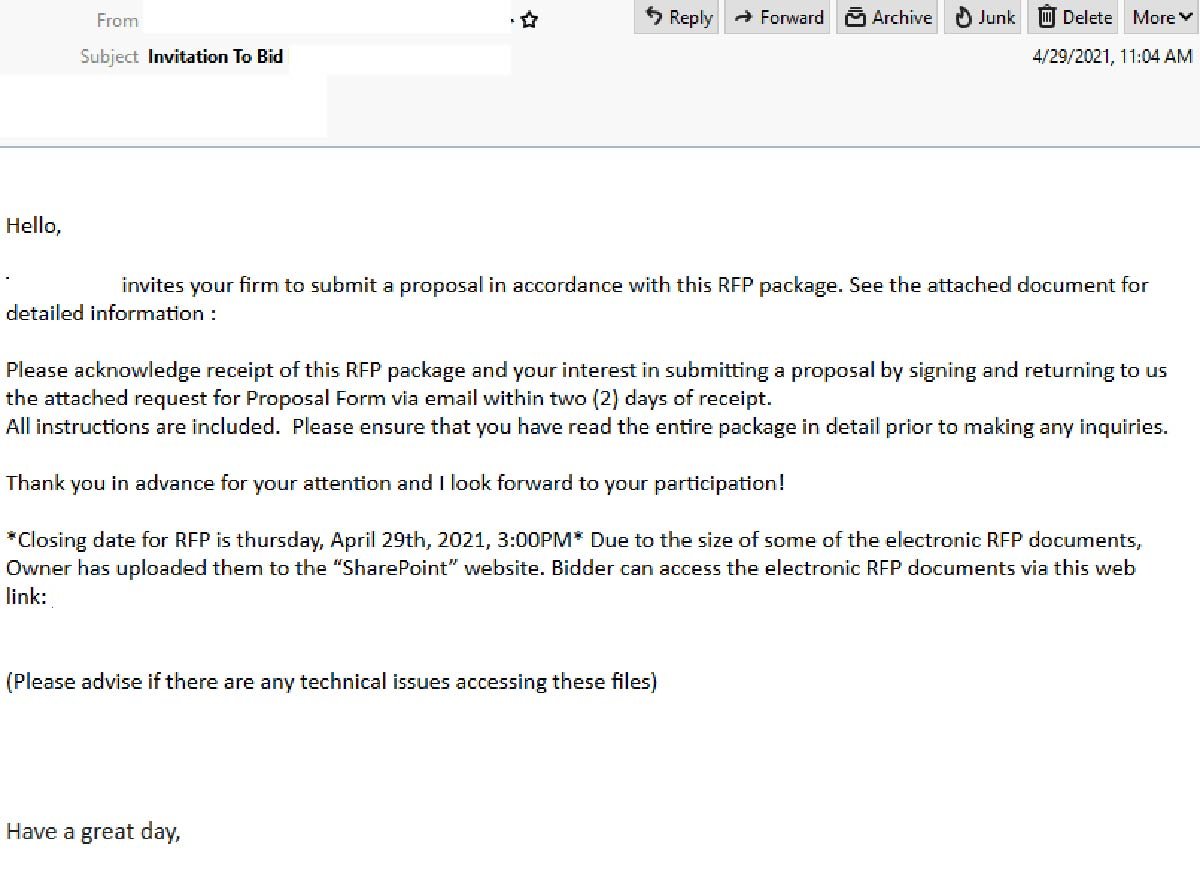
Titled ‘Invitation To Bid’, the email invites recipients ‘to submit a proposal in accordance’ with an 'RFP package'. The email explains that ‘due to the size of some of the electronic RFP documents’, they have been uploaded onto ‘SharePoint’ – a popular web-based collaborative platform by Microsoft that is commonly used by businesses. A link is provided for users to view the documents. Recipients are also instructed to acknowledge their interest in submitting a proposal by responding to the email ‘within two (2) days of receipt’. The email actually originates from a compromised email account.
Here is what the email looks like:
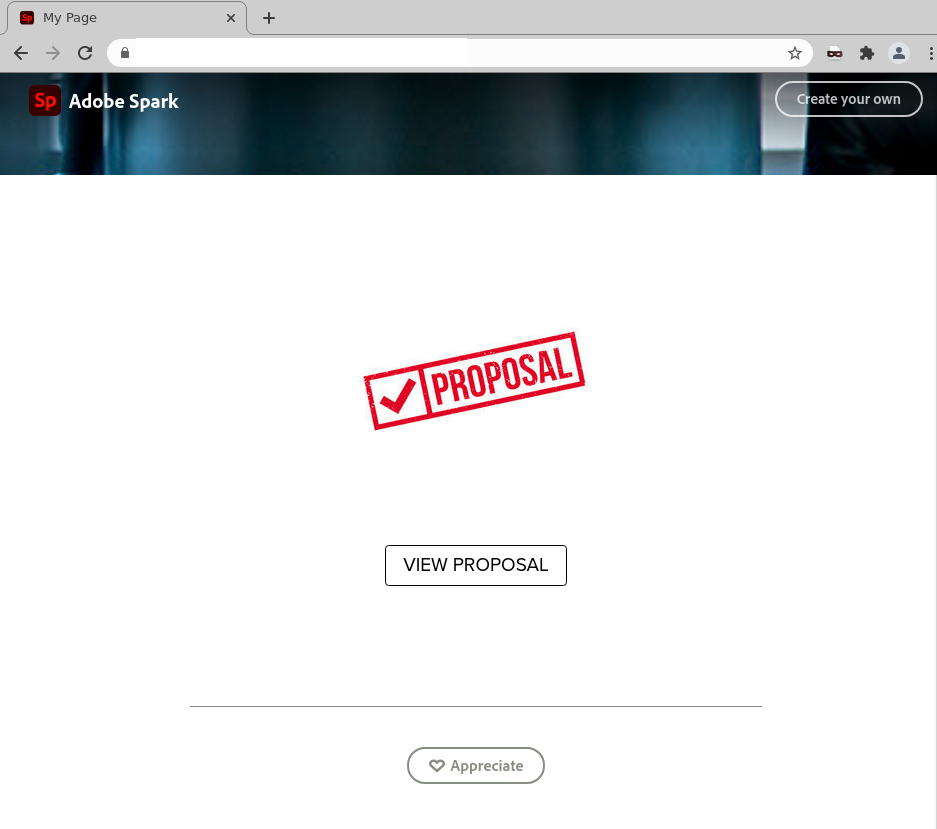
Unsuspecting recipients who click on the links to the view the documents are led to an intermediary page that asks them to click on another link in order to ‘view proposal’. This page includes Adobe Spark’s logo and branding. Here is what it looks like:
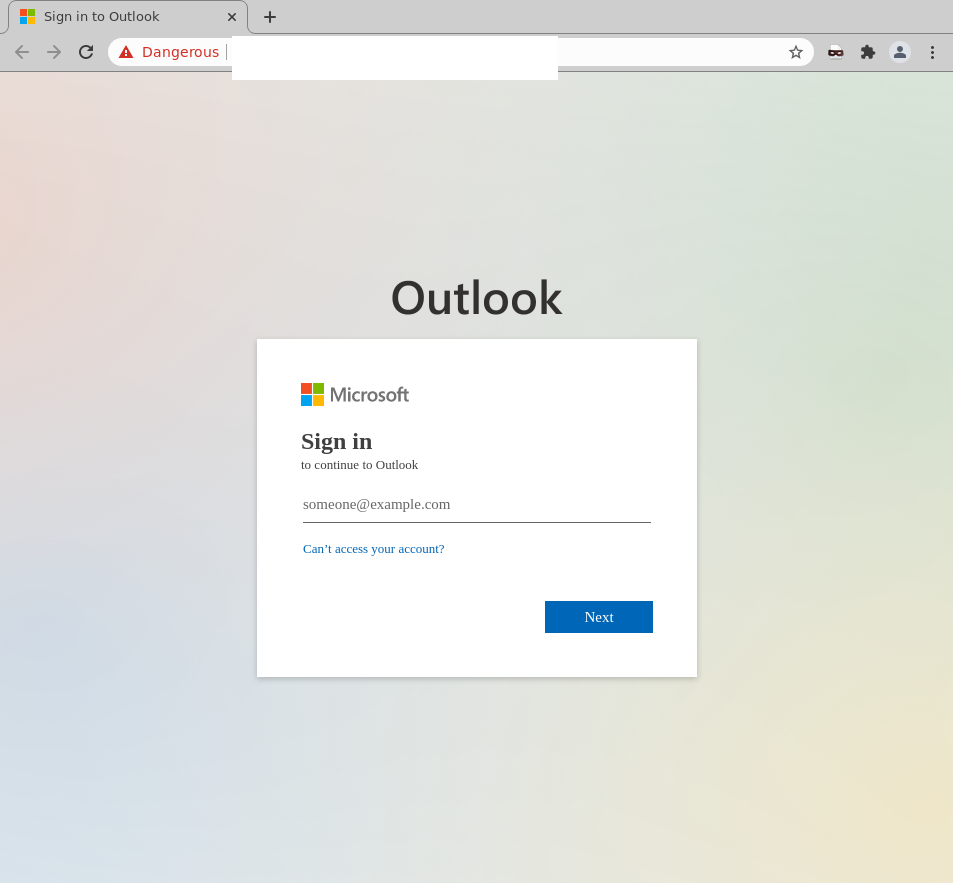
Upon clicking on the button to ‘View Proposal’, users are led to what appears to be a login page. While this page employs Microsoft’s logo and branding, the domain used in the URL of the page doesn’t belong to Microsoft – a red flag pointing to the page’s illegitimacy. This is actually a phishing page hosted on Cloudfare.
Here’s a screenshot of the page:
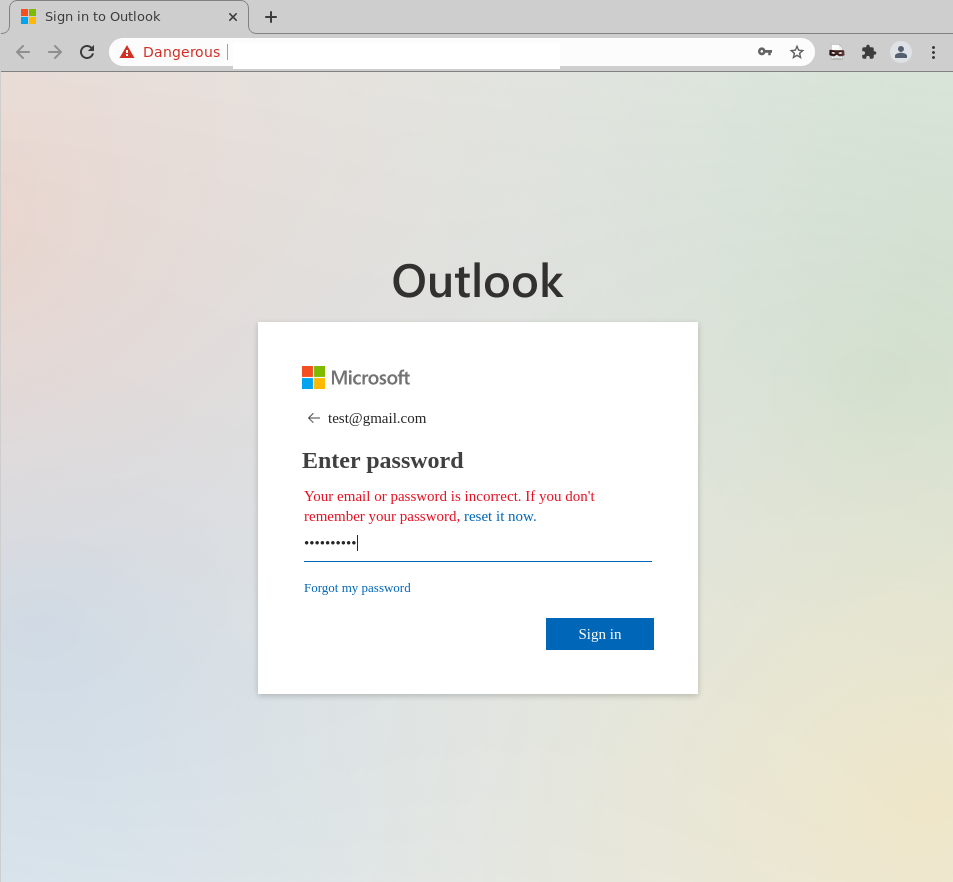
Upon ‘logging in’, users’ credentials are harvested by the cybercriminals behind the scam. Users are then shown a response stating the email or password they entered is incorrect, as per the below:
Whilst MailGuard is stopping this email scam from reaching Australian businesses, we encourage all users to exercise caution when opening messages, and to be extra vigilant against this kind of cyber-attack. If you are not expecting a file from the sender, do not open the email, download files or click through on the links. Check with the sender first, even if they are known to you.
By claiming to invite users to ‘submit a proposal in accordance with a RFP package’ that has been shared, this email scam aims to intrigue recipients. In addition, by including a deadline, i.e. the instruction to view the ‘attached document’ and reply to the sender ‘within two (2) days of receipt’, the email sparks urgency, further motivating users to click on the links to view the document as soon as possible.
Scams that are initiated from compromised accounts are particularly dangerous, for a number of reasons:
- The emails are sent from a legitimate account, so they are not likely to be blocked by email security services,
- The recipients are more receptive to the emails because they are from a legitimate service, and especially where the sender is known to them, and
- Because they may deliver a malicious payload, or simply a link to a file like these examples, directing users to external phishing pages to harvest credentials.
It's also interesting to note the inclusion of 'SharePoint' in the email, and the presence of Adobe Spark and Microsoft branding in the scam. Cybercriminals frequently impersonate global companies like Microsoft and Adobe, because their good reputation lulls victims into a false sense of security. Because of the large number of users globally, they are regular victims of these scams. In this case, by assuring recipients that the shared documents are hosted on a safe platform like SharePoint, the email boosts its credibility, further encouraging users to click onto the links present in the email. In addition, using a file-sharing notification to trick users is another trick employed by cybercriminals to avoid detection. Since the COVID-19 pandemic, it’s become increasingly more common for employees working remotely to share confidential business documents with one another via email, so notifications like this one aren’t likely to raise too much suspicion.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







