Earlier this year, I wrote about the need for Australian businesses to step up their efforts in defending themselves from Business Email Compromise (BEC) attacks.
The Australian Competition & Consumer Commission (ACCC)’s Targeting Scams report had found that businesses in Australia lost $132 million to BEC scams in 2019. This was, in fact, the highest loss accrued across all scam types last year.
Fast forward to now, things are worse, with a storm of BEC scams (also known as whaling or CEO Fraud) targeting Australian firms, resulting in devastating financial losses & reputational hits – consequences that are more keenly felt amid a pandemic-ridden year of business disruptions and economic uncertainty.
In October, the Australian Cyber Security Centre (ACSC) warned of a “significant increase” in BEC scams targeting local organisations. There were 4,255 reported incidents of email compromise scams in the 2019-20 financial year, costing over $142 million Observing a similar trend, my team at MailGuard also continued to intercept sophisticated email threats, including BEC scams.
I’m a firm advocate for sharing stories, knowledge and learning from past misfortunes in order to adapt & enhance our strategies for the future. It's key to remember that where we’re seeing a rise in cyber-attacks, we’re also being presented with learnings & opportunities to thwart them.
Below, I list three different examples of BEC scams that were reported in the news last month. These scams targeted businesses and professionals in different industries and in different ways, but they point to one common reminder – that BEC scams are successful because they leverage the technical weaknesses of our cybersecurity defences, but they also rely heavily on human error, psychology & in particular, trust.
For cybercrime to succeed, attackers need to convince users to trust them, and often use traditional techniques online to hoodwink unsuspecting users. The below examples summarise some of these measures, specifically, the trust we place in the processes we have at hand, the trust we place in the brands we work with, and in the relationships we hold with our colleagues. Businesses must remind teams to be smart about the security choices they make everyday. Share the below examples as mini case studies about the different ways BEC scammers exploit our trust.
1) Trust in processes: "This is one example of the manifest failure of (security) checks and balances with dramatic consequences for our business.”
A scam that began with a fake Zoom invite brought Levitas Capital, a Sydney hedge fund, to its knees after hackers sent $8.7 million worth of invoices from the fund manager’s email account. The fake Zoom invitation was opened by either Michael Brookes or Michael Fagan (the hedge fund’s co-founders), which triggered a malicious software program to be planted on the company's network. This allowed the cyber criminals to take control of its email system and send off the bogus invoices.
What was particularly interesting in this case was how the payment from these invoices was approved and transferred from the company’s trustee, AET Corporate Trust, and administrator, Apex, despite the usual verification procedures reportedly being followed.
“Issues that weren't picked up included the attached invoice being addressed to Levitas, not the trustee as was required. It also claimed to be a "capital call", something the fund had never previously requested. Unique Star (the fraudulent company the money was transferred to) also had no links or previous relationship with the fund and was not on its supplier list. The fund administrator, Apex, did call Mr Fagan to verify the transaction, but he was at the gym and said he would call back before approving any payments. When he returned to the office, he emailed Apex but received no reply or call back. The $1.2 million was transferred to Unique Star's ANZ bank account that day – September 16. In the background, the fund later learned, the hackers had sent another email to the fund administrator Apex authorising the transaction, as they had taken control of the hedge fund's email system,” stated a report from the Australian Financial Review.
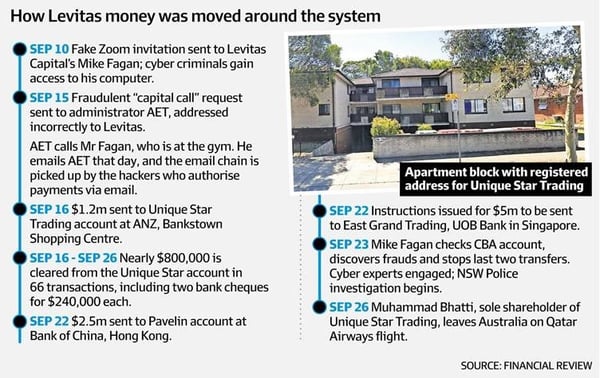 Source: Australian Financial Review
Source: Australian Financial Review
The fact that Levitas Capital collapsed as a result of one fraudulent email is a reminder of the need to continuously enhance email security measures and to have airtight, multi-layered processes in place for verifying and paying accounts.
"The entire funds management industry relies on a range of important checks and balances to ensure the integrity of the system – in particular the role trustees and administrators are supposed to play. This is one example of the manifest failure of these checks and balances with dramatic consequences for our business. It makes you wonder where else in the system this could happen?” said Fagan.
Cybercriminals often exploit the fact that we are busy, distracted professionals, who in our rush to clear emails and tasks, often assume and trust that all security measures and processes are in place and throw caution to the wind. Unfortunately, cybercriminals know most of the security processes we rely on too, and they use this familiarity to trick us, anticipating our thinking and next moves. Even intelligent, cyber-savvy CEOs and leaders are not safe, when targeted with a cleverly worded, socially engineered email.
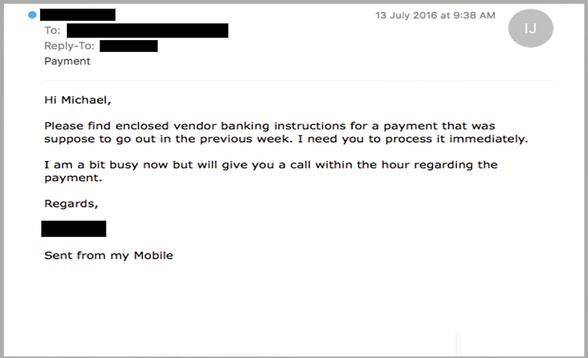
We often see in BEC scams that cybercriminals make urgent requests in emails too – to motivate recipients to bypass security processes & procedures in the interest of time. Here’s an example of a BEC scam employing this technique that my team intercepted in the past:
Key reminders & lessons:
- If you have received an unexpected email, check who it was sent by. Examine the sender or reply-to address and check that it hasn’t been sent from a similar, but recently registered domain such as example.com instead of example.com.au. Be alert for strange sentence structure, or phrasing uncommon to the apparent sender.
- Ensure a formal payment or transfer process is well communicated throughout the entire business. If employees are transferring funds, especially large or unusual ones, remind them to ring the apparent sender on a known number to verify the transfer. If they’re not available, wait until they are. It’s not advisable to seek confirmation by email, because users may inadvertently end up communicating directly with the criminal, as in the Levitas Capital case.
- Implement scam-proof approvals processes for financial transfers such as two-factor authentication, and require two employees to sign off on wire transfers.
2) Trust in people & relationships: "We hadn't used Simon for six months so I thought he'd possibly changed it (his banking details) over that period of time"
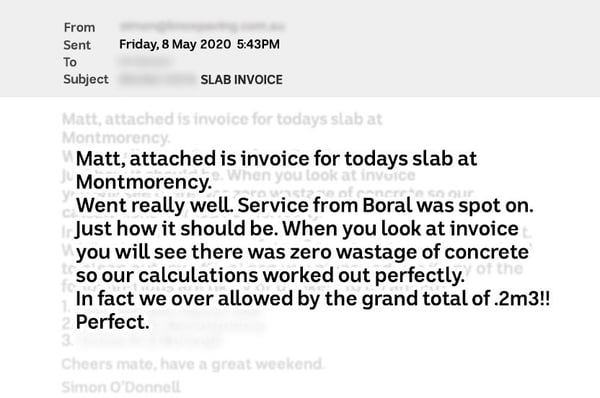
An Australian SMB lost $51,000 after the building business owner, Jane Fleming, transferred the funds into a scammer's bank account, thinking she was paying a legitimate subcontractor, a concreter whom she has been working with for years. Jane had received an email, containing details of a recent job, along with a request for payment to be made to unexpectedly new banking details.
"We hadn't used Simon (the concreter) for six months, so I thought he'd possibly changed it over that period of time," Fleming said.
The email itself showed clear details of the job that'd been completed.
Source: ABC.net
Fleming only realised she had been scammed when the concreter called her husband asking where his money was, a couple of days after she had transferred the funds.
According to reports, hackers had gained access to either Fleming's email account, or the concreter’s account, to modify the invoice, and was waiting for an opportunity like this. Before launching an attack, BEC scammers typically conduct thorough reconnaissance to research the companies involved, including the way they interact and the type of messages they exchange. This may have allowed hackers to manipulate the email Fleming received in a manner that didn’t raise any red flags.
This is a classic example of how cybercriminals use social engineering & mind games to exploit how people work and interact in business settings. Cybercrime isn’t only about hacking into technology, but getting inside the minds of users too. In this case, cybercriminals are leveraging the long & trusted relationship between Fleming & her concreter, knowing that she would be likely to trust that the information provided in the email she received from him was legitimate.
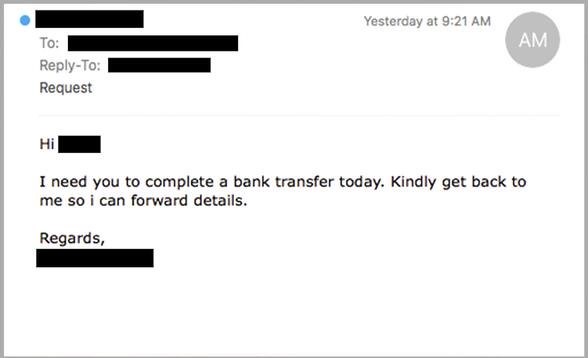
Cybercriminals also exploit power and seniority in professional relationships. By mimicking a high-ranking executive for example, cybercriminals hope the recipient will be less likely to question a request or instruction. For example, it won’t be surprising for someone in a finance department to immediately reply to this email we intercepted below, sent supposedly from the CEO, requesting an unexpected bank transfer:
Key reminders & lessons:
- Using strong & unique passwords and updating them frequently can go a long way to protecting business email accounts from being hacked or compromised.
- Contact the company/ person in question directly using a second, reliable mode of communication like a known phone number (known to you, not on the emails) to verify any request to transfer funds or change in bank details. While it can seem overly cautious to call the sender to verify what they’ve said (especially when you’ve had a trusting relationship with them for years), it can save a lot of pain in the long run.
- Verifying requests includes contacting and questioning senior colleagues (like bosses or managers). Business owners should let their staff know it’s okay to ask questions, no matter how awkward they may be. For instance, if someone is purporting to be a senior executive and they’re asking for a transfer or transaction, pick up the phone and ask those people directly if they requested it. However uncomfortable it may be to ask that question, it’s better to have an awkward conversation today rather than to not have a job tomorrow.
- Manipulating an email containing in-depth information about the job that only a credible source would have access to (i.e. the concreter himself) is a technique employed by cybercriminals to boost the email’s legitimacy, further convincing the recipient that the updated changes to the banking details are also legitimate.
- The email is also sent near the end of the financial year – a period notorious for invoice-related scams like these. Cybercriminals love this period because they know that being cyber-savvy is probably pretty low on staff’s list of priorities, as teams are distracted by settling overdue invoices, balancing numbers and filing tax returns amid stringent deadlines.
3) Trust in brands: "It was identical to the usual message we receive and didn't ring any alarm bells."
Brandjacking is a term I use when cybercrime groups hijack the trusted relationships that we all have with major brands and companies. Essentially, brandjacking is a kind of forgery. Having realised the powerful influence and impact of brands on the minds of consumers, scammers often exploit the trademarks of well-known & trusted companies to deceive users.
And that’s what happened to a farming couple in Queensland who were recently scammed of $90,000 after falling for a fraudulent email supposedly from Arrow Energy, reminding them to make their quarterly payment for land they lease from the company. The email mentioned that due to “company restructuring”, a new bank account had been created and all payments should be transferred there.
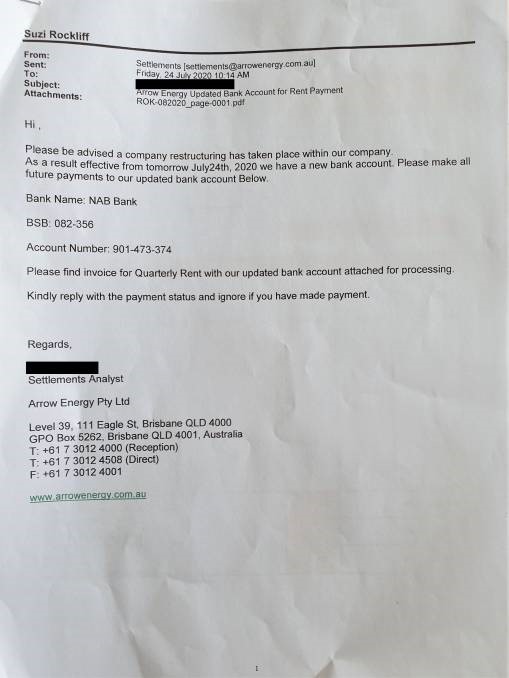
Source: Queensland Country Life
"We receive similar messages regularly from other businesses and didn't think to check," Noel Rockliff, the Dalby farmer, said. "It was identical to the usual message we receive and didn't ring any alarm bells."
Interestingly, the fraudulent invoice attached to the email was almost identical to the real one, as per the screenshot below:
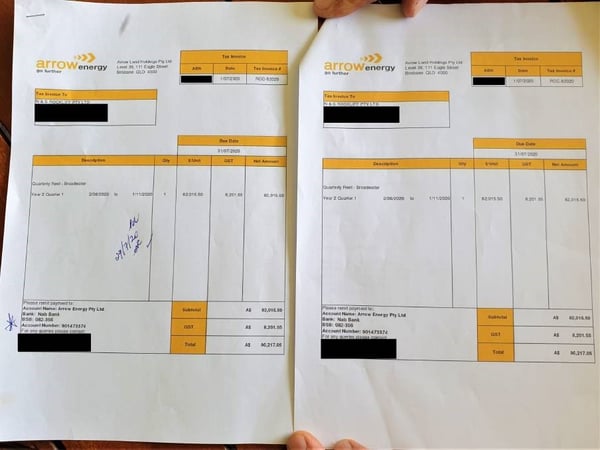
The real invoice received by the Rockliffs is almost identical to the fake one on the right. Source: Queensland Country Life
The farmers only realised they'd been duped when they were contacted by Arrow a week later asking why they hadn't made their payment.
Playing on the fact that we’re all time-poor, with full inboxes, cybercriminals are hoping we won’t think twice about clicking emails from the brands we know and trust. At MailGuard, my company regularly intercepts fraudulent emails impersonating popular local & international brands like Netflix, PayPal, NAB, Australia Post, and others. Here’s our hit list of brands that are frequently mimicked by cybercriminals.
Key reminders & lessons:
- Scammers are investing more time and effort into producing communications that look authentic, just like those from the brands they are impersonating. In some instances, senior graphic designers and/or legal experts are being employed by cybercriminals to design contracts and to use high quality design and branding elements within the emails.
- Vigilance is key whenever transferring funds online, especially in cases where there are updates to banking details. When reviewing an invoice, even if it appears to be from a trusted brand, make sure you keep a watch out for any red flags. These include checking for slightly altered email addresses, spelling and grammatical errors, and alterations on invoices, like low quality graphics or mismatched fonts.
- Prevent your IT systems from being compromised. Keep your software up-to-date by regularly patching your systems and running antivirus software, and have a good firewall to protect your data.
These are just a handful of examples of BEC scams that have struck organisations in recent times. There are many more, and they are irrefutable evidence that email-borne cybercrime is an existential threat in Australia. As a new year beckons, let’s continue to share our experiences with our networks, so we can collectively build out our resilience and develop the capabilities required to combat incoming cyber risks.
With 9 out of 10 cyber-attacks delivered by email, I strongly advise ensuring your business email security is up to scratch by adopting a strategic, multi-layered approach. It’s sometimes referred to as ‘defence in depth’, designed to defend a system against attacks using several different methods and solutions, in the event that if one fails, the others will stop the threat – an approach that’s become even more critical in this era of amplified cyber risk.
You may already have native security from your email hosting provider, like Google or Microsoft, but it’s key to remember that no one vendor can stop all attacks. If you are using Microsoft 365 or G Suite, you should also have third-party solutions in place to mitigate your risk - especially as email threats continue to grow in sophistication. For example, using a specialist third-party cloud email solution like MailGuard to complement Microsoft 365. If you need more support to protect your business from email threats, including BEC scams, reach out to my team at expert@mailguard.com.au.
BEC scams have been around for a while, but their continued success at bringing down organisations (both large & small) shows we’re dealing with an adversary that is constantly looking for new ways to exploit our systems, our psychology & our trust. Let’s rise to the challenge and adapt our technologies and techniques in order to stay ahead.
What are you doing to protect your business from BEC scams? Comment below.






