Once again, an elaborate phishing scam is the weapon of choice for cybercriminals aiming to take advantage of the weakest link in the security landscape – human beings. A recent attack has taken inspiration from history by using ‘Project Zebra’, the name given to the top-secret mission between Stalin and Roosevelt (with the aim of flying a state-of-the-art amphibious warplane) as the subject of a malicious email impersonating an employee at international engineering, design and advisory firm ‘Aurecon’. The email currently intercepted by MailGuard uses a direct interaction phishing tactic designed to entice the victim into submitting a job proposal by creating a highly personalised email from an unsuspecting Aurecon employee. It is possible that these details have either been found publicly or from a leaked database.
Notable characteristics of the phishing attack include the following:
- Polished Microsoft 356 branding which has been used as the trusted name in this scenario in order to retrieve information for criminal use.
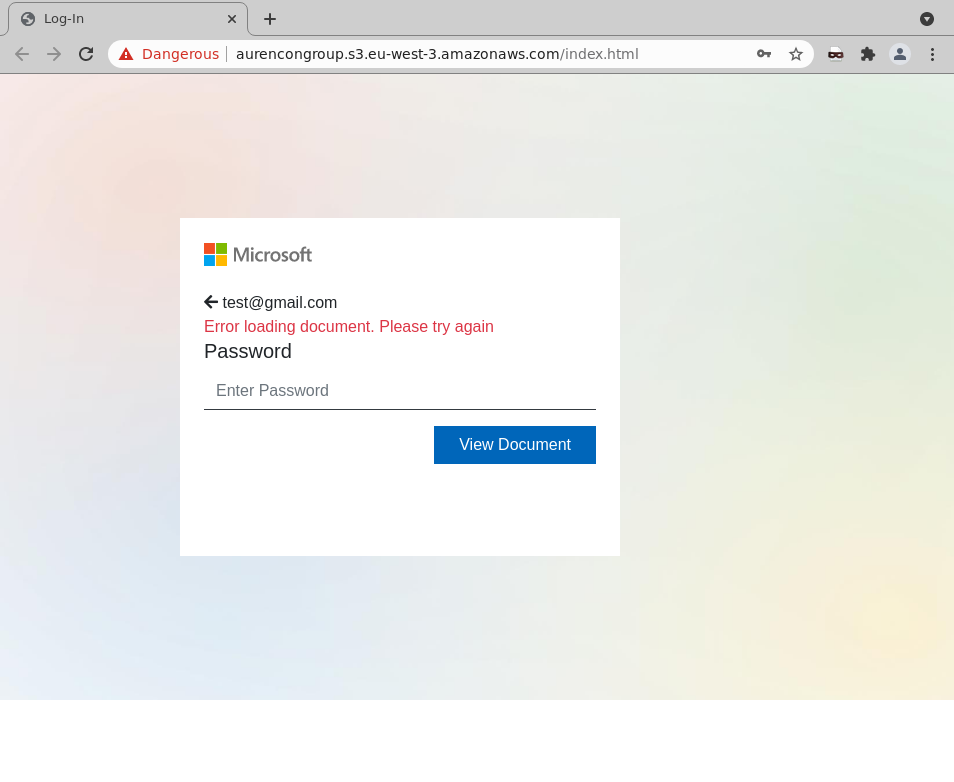
- The criminal website for the phishing page is disguised by using AWS (another trusted and commonly known brand) as the hosting name.
- Attention to detail with regards to use of trusted names, near accurate branding imitations and use of familiar and well-known iconography.
Perhaps the most alarming part of this attack is the use of accurate credentials (name, role and contact details) from an existing employee at Aurecon, indicating that the account of the staff member has indeed been compromised.
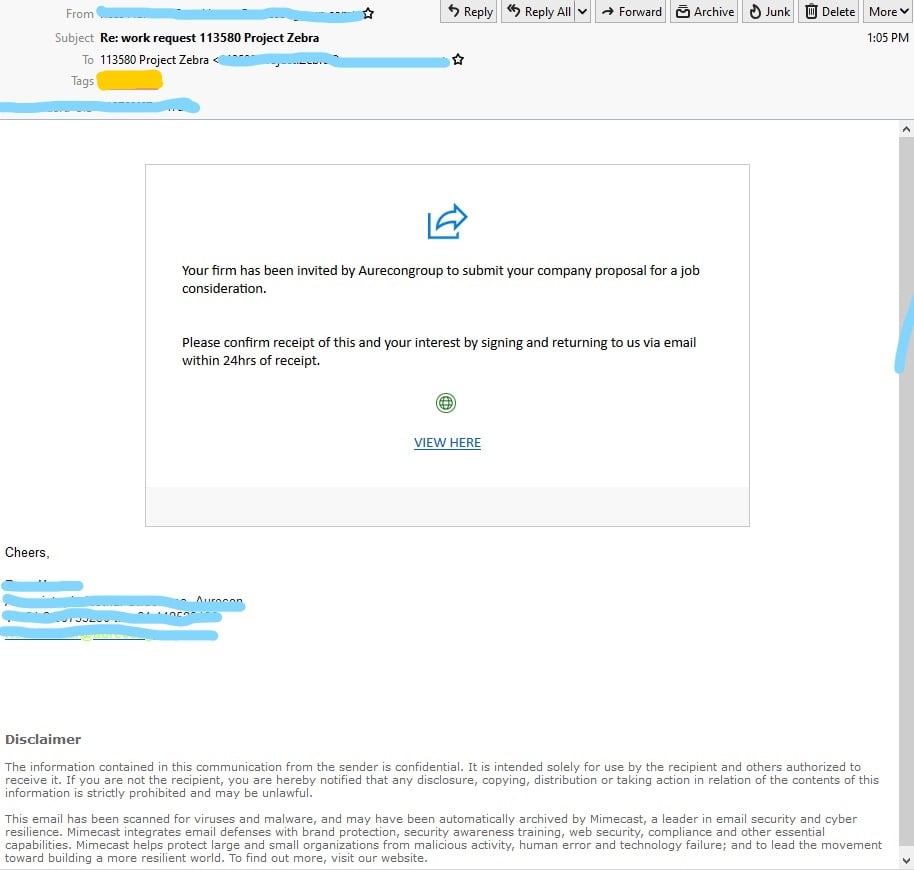
As seen below, the professional email invites the user to participate in submitting a proposal to the Aurecon Group, by providing a link asking you to view a form to be signed as acceptance. Notice the Disclaimer note added to the end of the email, purporting the legitimacy of the email.
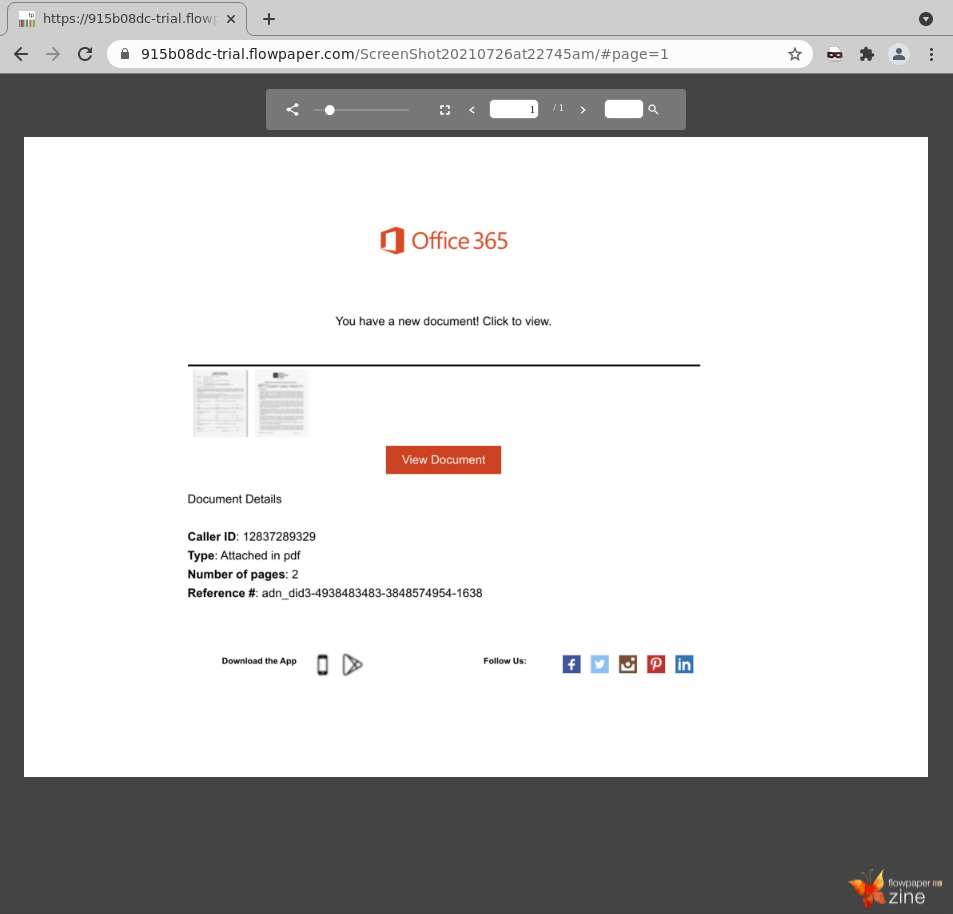
Once the victim clicks on the link provided, they are taken to an intermediary page hosted by FlowPaper which contains Office 365 branding and what appears to be PDF documents that need to be downloaded and signed. The scammers have also included popular Social Media icons (Facebook, Twitter, Instagram, Pinterest and LinkedIn) on the page.
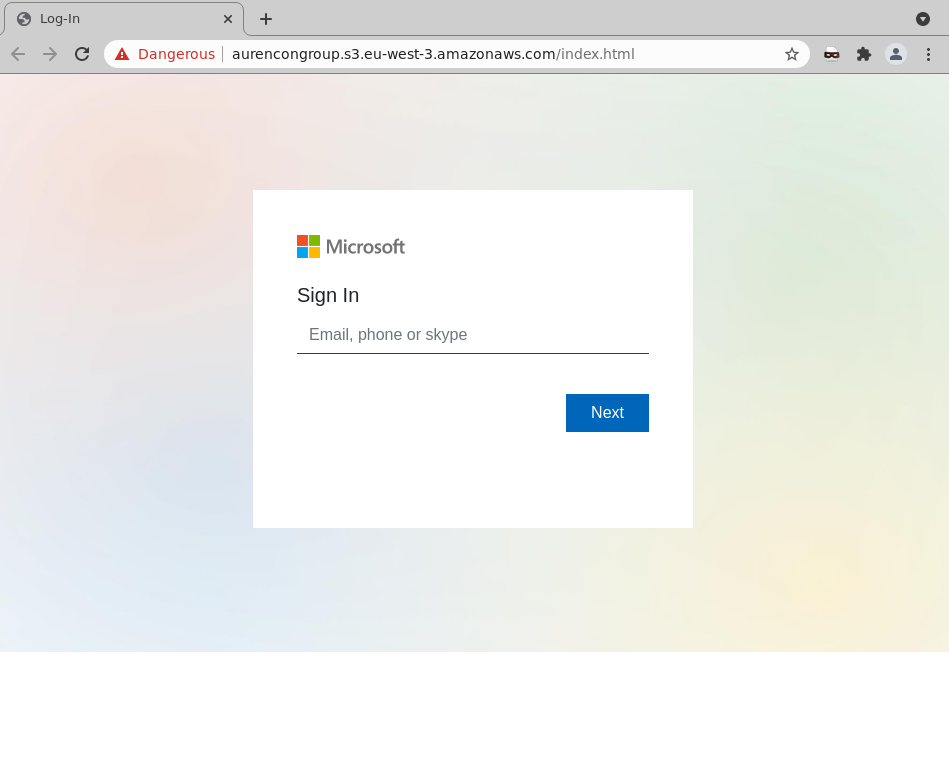
If the recipient is enticed to click on the ‘View Document’ button, they are taken to the phishing site hosted by AWS, asking them for their credentials via a Microsoft branded page that is a copy of the sign-in page you may see when logging into your Microsoft or Outlook Account.
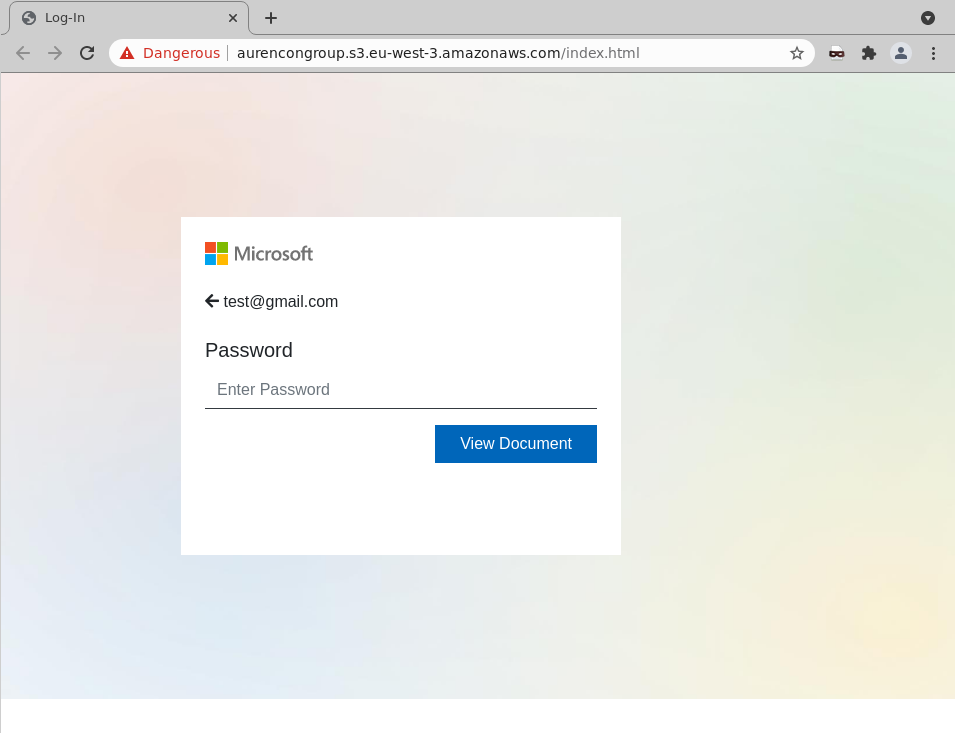 Once the credentials are entered and submitted, the attacker harvests them for later criminal use. The user is met with the following message: “Error loading document. Please try again” to further confirm the details being given to the attacker.
Once the credentials are entered and submitted, the attacker harvests them for later criminal use. The user is met with the following message: “Error loading document. Please try again” to further confirm the details being given to the attacker.
MailGuard urges all recipients of this email to delete it immediately without clicking on any links. Providing your personal details can result in grave consequences for you and your organisation’s security.
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security. Talk to a solution consultant at MailGuard today about securing your company's network.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







