MailGuard has intercepted an email attack that uses multiple trusted brand names to fool victims into providing their sensitive information for credential harvesting. DocuSign, with hundreds of millions of users worldwide, is a household name with businesses and organizations using the tool for electronic signatures and agreements. Purporting to be from a prominent healthcare provider a DocuSign link is sent to recipients, in an attempt to capture email and login addresses and to potentially download malware. Other trusted names such as Adobe, Microsoft and IBM have been spoofed using accurately depicted branding and logos to catch victims off guard.
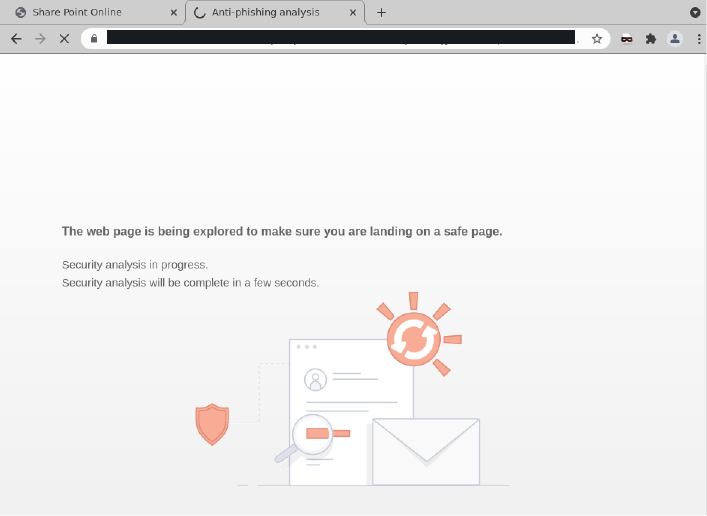
Interestingly, scammers have used an intermediary phishing page that pretends to be hosted by a well-known anti-phishing service in a bid to add credibility.
The email is below:
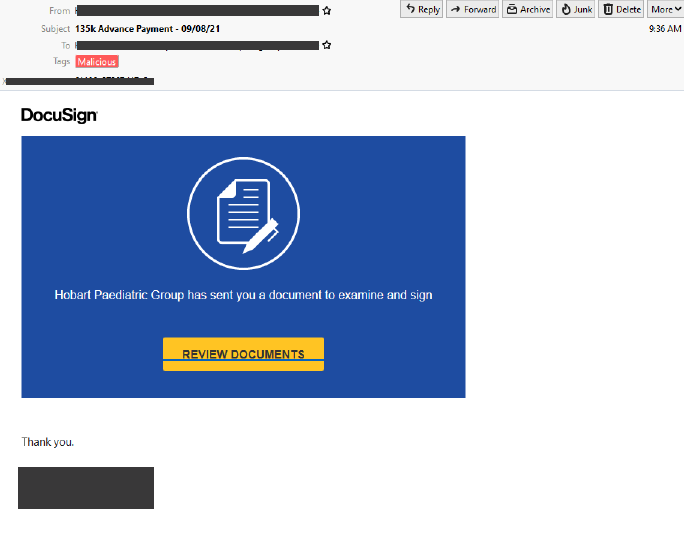
Note the mention of the large sum of money (137K Advance Payment) in the subject line, as well as the slight discrepancy in the DocuSign branding in the initial email, warning signals of foul play.
Once the victim clicks on the yellow ‘Review Documents’ link in the email, they are taken to the intermediary phishing page below, purporting to be hosted by an anti-phishing company. This page cleverly assures the victim that a security analysis is being done in order to ensure that the documents being accessed are trustworthy.
After the mock security analysis has been completed, the victim is taken to an Adobe branded login page requesting that the user select the Microsoft email login applicable to them (Outlook, Office 365 or ‘Other’) in order to view the phony document. The message to the victim mentions the word ‘valid’ in order to gain trust to confirm credentials. Once an email address and password are entered and submitted, the attacker harvests this information for later use and the victim is met with an error message saying “Please Try Again Later” as per below.
.png?width=952&name=MicrosoftTeams-image%20(5).png)
.png?width=952&name=MicrosoftTeams-image%20(6).png)
-1.png?width=954&name=MicrosoftTeams-image%20(7)-1.png)
DocuSign provides the following helpful advice regarding phishing scams using their name, which can be found on their website: https://www.docusign.com/trust/security/incident-reporting
“Fake links
- Avoid fake links by accessing your documents directly from https://www.docusign.com using the unique security code found at the bottom of the DocuSign notification email.
- Always check where a link goes before you click on it by hovering your mouse over the link to look at the URL in your browser or email status bar (they should be hosted on docusign.com or docusign.net). A fraudulent link is dangerous and can:
- Direct you to a fake website that tries to collect your personal data
- Install spyware on your system (spyware is an application that can enable a hacker to monitor your actions and steal any login IDs, passwords, or credit card numbers you type)
- Cause you to download a virus that could disable your computer
Fake sender email address
- Fake emails may include a forged email address in the "From" field, which is easily altered. If you don’t recognize the sender of a DocuSign envelope, contact the sender to verify the authenticity of the email.
Attachments
- DocuSign emails that request you to sign a document never contain attachments of any kind. Don’t open or click on attachments within an email requesting your signature. DocuSign emails only contain PDF attachments of completed documents after all parties have signed the document. Even then, pay close attention to the attachment to ensure it’s a valid PDF file. DocuSign never attaches zip files or executables.
Generic greetings
- Many fake emails begin with a generic greeting like “Dear DocuSign Customer.” If you don’t see your name in the salutation, be suspicious and don’t click on any links or attachments.
False sense of urgency
- Many fake emails try to deceive you with the threat that your account is in jeopardy if you don’t provide immediate updates. They may also state that unauthorized transactions have occurred on your account or that DocuSign needs to update your account information immediately.
Emails that appear to be websites
- Some fake emails are made to look like a website to get you to enter personal information. DocuSign never asks you for personal information, including login, ID, or password, via an email.
Deceptive URLs
- Check the Web address. Just because the address looks OK, don't assume you're on a legitimate site. Look in your browser's URL bar for signs that you may be on a phishing site:
- Often the Web address of a phishing site looks correct but actually contains a common misspelling of the company name or a character or symbol before or after the company name, such as docusing.com instead of docusign.com
- Look for tricks like substituting the number "1" for the letter "l" in a Web address or transposing consecutive letters of the brand, such as rea1estate.docusign.com instead of realestate.docusign.com
- Your browser has ways of detecting certain types of malicious sites—always heed these browser warnings, especially when they notify you that the site or certificate can’t be trusted
Misspellings and bad grammar
- While no one is perfect, fake emails often contain misspellings, incorrect grammar, missing words, and gaps in logic. Mistakes like this help fraudsters avoid spam filters.
Unsafe sites
- The term "https" should always precede any website address where you enter personal information. The "s" stands for secure. If you don't see "https," you're not in a secure Web session, and you shouldn’t enter any personal data. A legitimate DocuSign sign-in page address always starts with “https://” not “http://.”
Pop-up boxes
- DocuSign never uses a pop-up box in an email, because pop-ups aren’t secure.
- DocuSign-themed fraudulent emails and websites: if you think that you’ve received a fraudulent email purporting to come from DocuSign, forward the entire email as an attachment to spam@docusign.com and delete it immediately.
DocuSign-themed fraudulent emails and websites: if you think that you’ve received a fraudulent email purporting to come from DocuSign, forward the entire email as an attachment to spam@docusign.com and delete it immediately.”
MailGuard urges all recipients of this email to delete it immediately without clicking on any links. Providing your personal details can result in your sensitive information being used for criminal activity.
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security. Talk to a solution consultant at MailGuard today about securing your company's network.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







