When hackers set about breaking into a company’s computers, they start with phishing emails. Their objective is to get one person inside their target company to click a link to a fake website they’ve set up and enter their email password.
Deceiving people into clicking a link in a phishing message is a malicious artform. Cybercriminals use forged graphics like company trademarks to trick their victims and make their messages look as much like genuine emails as possible.
One way to distinguish a real email message from a fake one can be to check the sender’s email address, or the URLs that the links in the message point to.
To deceive more wary victims, hackers use a tactic called “domain spoofing” to disguise their intentions.
What is domain spoofing?
Phishing emails are more likely to deceive recipients if they seem to come from real company’s URLs.
The email below, detected by MailGuard in March this year, appears to come from a company called Corral Photography. It even shows ronald@corralphotography.com.au as the sender, which makes it look more legitimate.
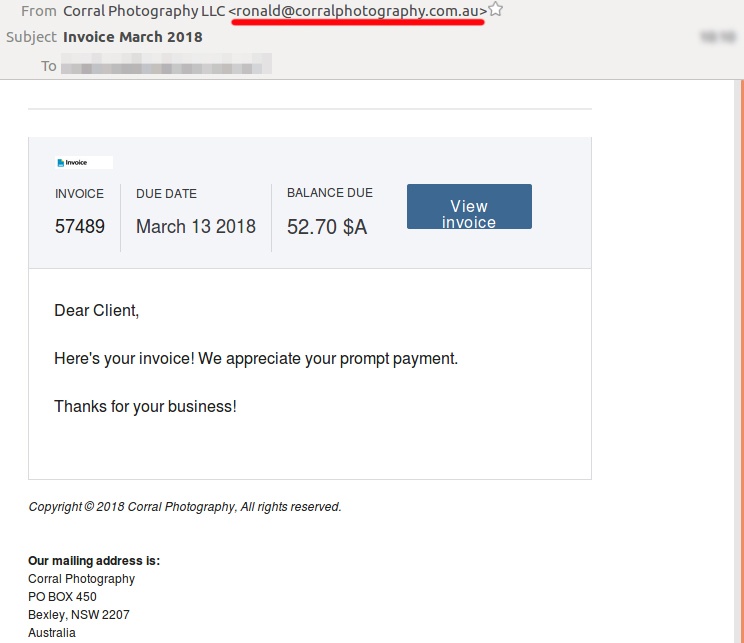
In fact, Corral Photography was hacked right before this email was sent and the criminals used the email account of the company’s owner to send their malicious messages. The message carried a malware payload designed to infect the victim’s computers with a virus.
A single click can mean big losses

“A massive new crime category has risen up as the world’s economy has gone digital: email fraud. The victims are companies, big and small, and the perpetrators are skilled con-artists who use fake emails and counterfeit websites to steal billions of dollars. Reports released by The FBI, Deloitte and WEF all agree; cybercriminals directly target people through their email inboxes to get access to their employer’s data and ultimately, their money.” - Craig McDonald, CEO, MailGuard
Cybercriminals build their hacking attacks in multiple stages. They will use phishing scams to crack the email accounts of individual people inside a company, then use the information they glean from that person’s inbox to break into more accounts in the company.
Hackers gaining control of a company’s website and data storage can start with just one well-designed phishing message. All it takes is one person clicking unwisely on a forged message like the ones shown above.
Protect your business online
Phishing scams and website hijacking can make millions of dollars for criminals. The big rewards for cybercrime have driven explosive growth in phishing in recent years, but many businesses are still poorly prepared to counter such attacks.
If you would like to learn more about cybersecurity and how to protect your business, please download the e-book Surviving the Rise of Cybercrime. It’s a plain English guide explaining the most common threats and providing essential advice on managing risk.
“Cybercrime is a serious and growing business risk. Building an effective cybersecurity culture within an organisation requires directors and executives to lead by example. Surviving the Rise of Cybercrime is a must-read for directors and executives across business and in government and provides strong foundations for leaders determined to address cyber risk.” - Rob Sloan, Cybersecurity Research Director, Wall Street Journal.
You can download your copy of Surviving the Rise of Cybercrime for free, here.






