MailGuard has identified and blocked a new phishing campaign impersonating shipment and logistics notifications, designed to trick recipients into paying fraudulent “customs clearance” fees.
This attack exploits a familiar business scenario, package delivery and shipment tracking, to create urgency and prompt immediate action.
How the scam works
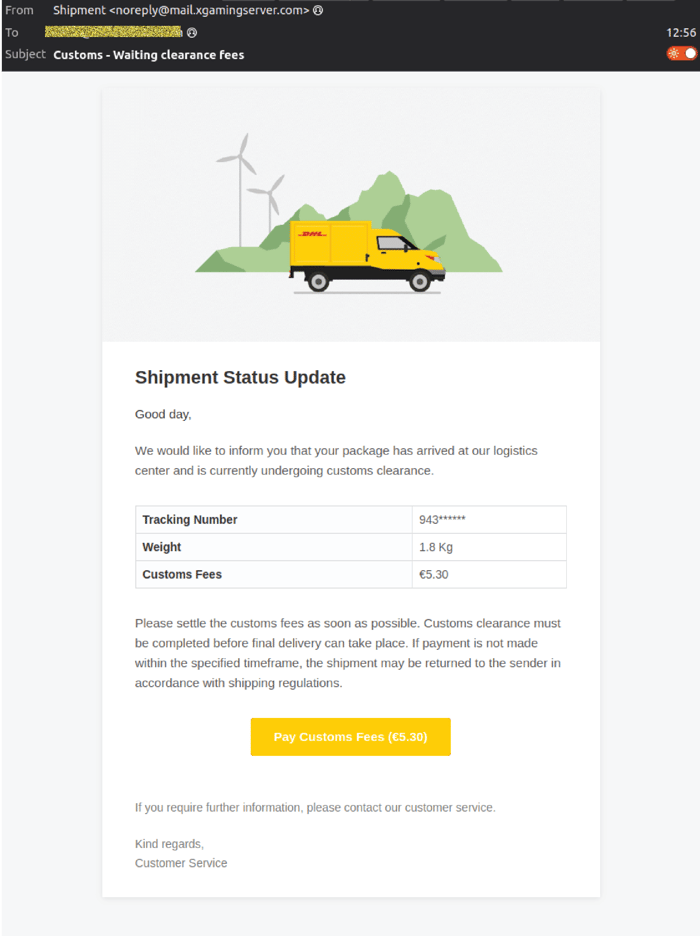
The email arrives with the subject line referencing shipment delays or customs clearance, typically framed as: “Customs – Waiting clearance fees”
It claims that a package is being held and requires a small payment to proceed. The message appears routine, well formatted, and aligned with legitimate logistics communications. Recipients are prompted to click a link to resolve the issue.
What happens when you click
The attack unfolds across multiple steps, after clicking the yellow ‘Pay Customs Fees’ button:
Landing page (information page)
The first page presents shipment details such as tracking number, weight, and customs fees, reinforcing legitimacy.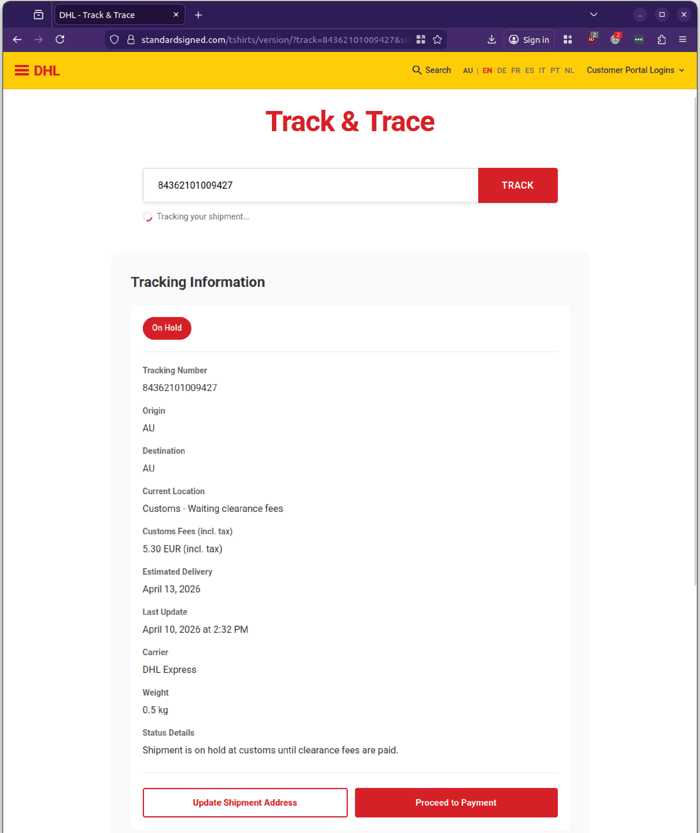
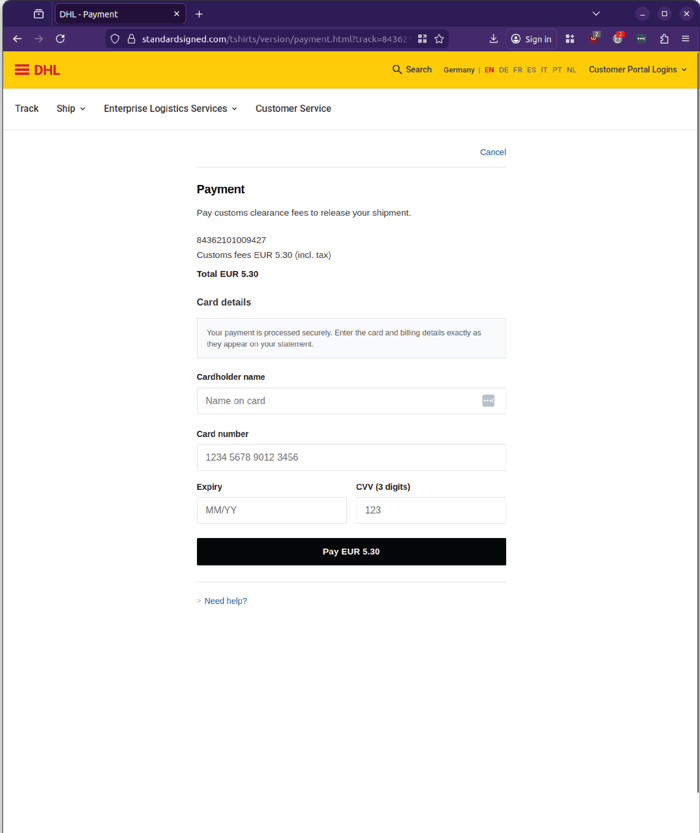
Payment page (data capture)
Users are asked to enter credit card details to pay a small fee, typically only a few dollars or euros, lowering suspicion.
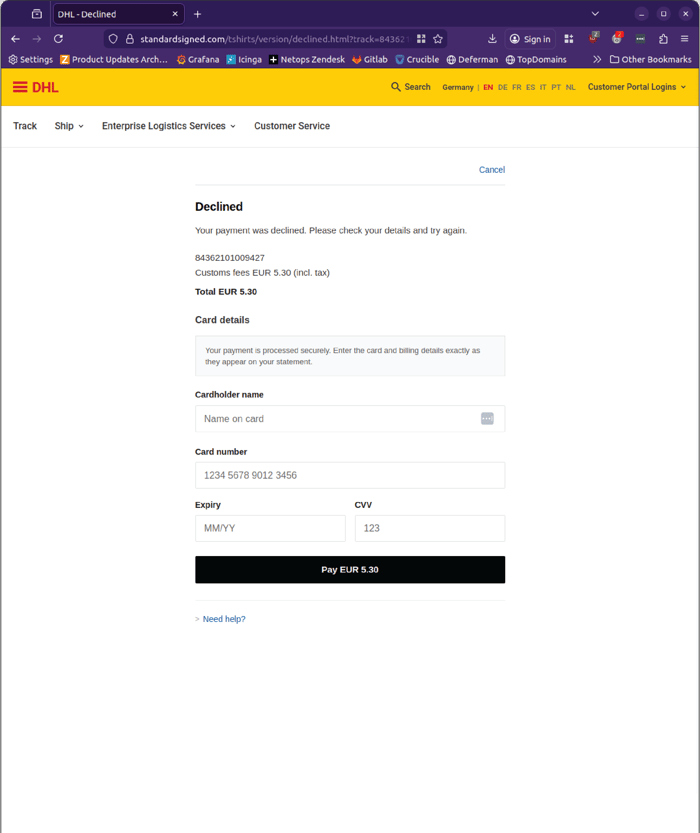
Processing page (false confirmation loop)
The site simulates payment processing, then returns an error, prompting users to re-enter their details.
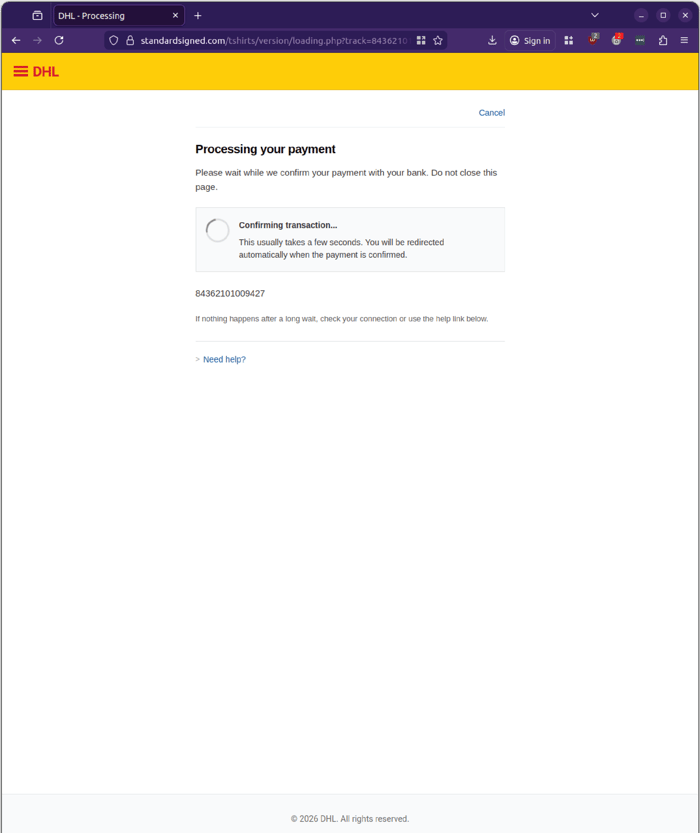
This increases the likelihood of successful data capture. This is a classic credential and payment harvesting technique, using repetition and friction to extract sensitive information.
Why this attack is effective
This campaign is simple, but highly effective.
- It uses familiar business processes such as deliveries and customs clearance
- It introduces urgency, suggesting delays or failed delivery
- It requests low-value payments, reducing hesitation
- It mimics legitimate branding and workflows, making detection difficult
Importantly, the email does not rely on sophisticated malware or attachments. Instead, it relies on user action, aligning with everyday business behavior.
Sender details and infrastructure
The email purports to come from a generic “Shipment” sender, using rotating and inconsistent email infrastructure.
Display addresses include:- Hello(at)parkedin(dot)com.au
- Noreply(at)mail(dot)xgamingserver.com
-
mail21.suw111(dot)mcdlv.net
-
mail.xgamingserver(dot)com
This variability helps attackers evade traditional filtering and detection mechanisms.
What to look out for
This scam contains several indicators:
- Generic sender name such as “Shipment”
- Unexpected delivery or customs fee notifications
- Requests for small, immediate payments
- Links that redirect to non-legitimate domains
- Payment pages that loop or fail after submission
Even when the amounts are small, the consequences can be significant if payment details are compromised.
Why this matters for your business
Attacks like this highlight a broader shift in cybercrime. Threat actors are no longer relying on technical exploits alone. They are designing attacks that fit seamlessly into everyday workflows. A simple message, aligned with routine business activity, can be enough to trigger action. And once that action occurs, whether entering payment details or credentials, the damage is already underway.
Stay Safe, Know the SignsMailGuard advises all recipients of these emails to delete them immediately without clicking on any links. Responding or providing personal details can lead to identity theft, data breaches, and financial losses.
Avoid emails that:
- Aren’t addressed to you personally.
- Are unexpected and urge immediate action.
- Contain poor grammar or miss crucial identifying details.
- Direct you to a suspicious URL that isn’t associated with the genuine company.
Many businesses turn to MailGuard after a near miss or incident. Don't wait until it's too late. Reach out to our team for a confidential discussion by emailing expert@mailguard.com.au or calling 1300 30 44 30.
One Email Is All That It Takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's specialist AI-powered, zero-day email security. Special Ops for when speed matters! Our real-time zero-day, email threat detection amplifies our client’s intelligence, knowledge, security and defence. Talk to a solution consultant at MailGuard today about securing your company's inboxes.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







