The image many businesspeople have of cybercrime is a teenager with a grubby hoody hunched over a laptop hammering code into a flickering screen that’s like something out of The Matrix. The imaginary teen finds a backdoor into a bank’s server admin page, and typing like fury beats the computer in a showdown of quick-draw typing. He seizes control of the mainframe and then chuckles to himself and rubs his hands together with glee as a glowing green progress bar indicates millions of dollars draining into his account...
That television inspired idea is about as far from reality as it could be. Although cybercriminals may be young in some instances, and may occasionally wear hooded jumpers (like just about everyone) the techniques they use are more about psychology and deception than computer hacking.
A realistic cybercrime scenario:
A typical cybercrime attack is all about social engineering; that’s a jargon term to describe con-artistry or fraud, basically. Criminals look for promising target companies, often financial services, medical practices or professional sectors like lawyers and accountants. They check social media like LinkedIn and websites to find some email addresses for people in the company.
The next step is to send a phishing email to those inboxes. It’s a scattershot approach, but sooner or later one of those phishing emails is going to trick a victim into clicking on a link and logging into a dodgy website, and that’s all it takes.
Once the criminals have their victim’s email login credentials, they can find out all kinds of useful stuff about the business; the contact details of their employees, financial documents, sensitive data of every type. That kind of information is valuable in itself, but it also makes it possible for crim’s to hijack large sums of money by manipulating the company’s hierarchy from the inside. They can send an email from the CEOs account instructing the accounts department to write a cheque, or create bogus purchase orders for phoney goods. Companies can lose millions to attacks like this, and they’re very hard to detect once the criminal has got inside the system.
Phishing is huge
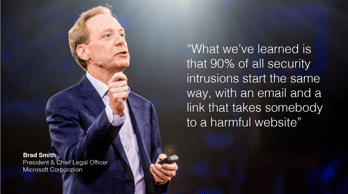 Phishing attacks of the type I just described represent the vast majority of damaging cyber-attacks.
Phishing attacks of the type I just described represent the vast majority of damaging cyber-attacks.
Even recent high profile incidents like the Democratic campaign hacks of 2016 and the attempts to take down the US power grid in 2017 were instigated with phishing emails.
The phishing problem is getting so severe that the US DHS (Dept. of Homeland Security) recently launched a special division to deal exclusively with cyber-threats. The DHS secretary described cyber-attacks as being a “bigger threat to national security than physical threats.”
Rethinking security spending
Knowing all these things about email-based cybercrime, businesspeople and CEOs need to be asking themselves some tough questions about the way they tackle cybersecurity.
- Is spending on cybersecurity initiated by the IT department or at senior management level?
- Does your company allocate cybersecurity funds for the education of team members in spotting phishing emails?
- Do you conduct security assessments, such as penetration tests?
- How confident are you of your ability to demonstrate compliance under data regulations like the GDPR?
- Email attacks represent 90% of threats; what percentage of your cybersecurity budget is spent on email protection?
Get the facts
 I wrote an article recently talking about some common phishing attack formats and the mechanism of social engineering attacks. If you’d like to learn more about this growing threat category check out my article, here.
I wrote an article recently talking about some common phishing attack formats and the mechanism of social engineering attacks. If you’d like to learn more about this growing threat category check out my article, here.
There seems to be a bit of a disconnect amongst many C-suite’s about the sources of cyber-threat.
Companies are spending more on cybersecurity now than ever before but those funds aren't always targeting the most significant dangers.
Studies consistently show that more than 90% of cyber-attacks are perpetrated via email, yet email security is rarely the biggest item in cybersecurity budgets.
If we’re going to win the battle with cybercrime we have to get real about the nature of the threat.
I’m on a mission to help business people understand cybercrime and protect their businesses from costly attacks. If you would like to learn more about the complex cybersecurity challenges facing business today, please download my e-book Surviving the Rise of Cybercrime. It’s a plain English, non-technical guide, explaining the most common threats and providing essential advice on managing risk.
“Cybercrime is a serious and growing business risk. Building an effective cybersecurity culture within an organisation requires directors and executives to lead by example. Surviving the Rise of Cybercrime is a must-read for directors and executives across business and in government and provides strong foundations for leaders determined to address cyber risk.” - Rob Sloan, Cybersecurity Research Director, Wall Street Journal.
You can download the e-book for free, here.
... ... ...
 Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Hi, I’m Craig McDonald; MailGuard CEO and cybersecurity author.
Follow me on social media to keep up with the latest developments in cybersecurity and Blockchain; I'm active on LinkedIn and Twitter.
I’d really value your input and comments so please join the conversation.






