The verdict is in, most industry experts and business leaders agree that Government contractors should be legally accountable for not meeting cybersecurity standards. A somewhat harsh stance perhaps, or simply being cruel to be kind? For partners, the approach could have serious ramifications.
The verdict is in, most industry experts and business leaders agree that Government contractors should be legally accountable for not meeting cybersecurity standards. A somewhat harsh stance perhaps, or simply being cruel to be kind? For partners, the approach could have serious ramifications.
Cybersecurity attacks are destructive, and the rise of threats, expedited by the global pandemic, has drastically impacted both the public and private spheres, with anyone from large company’s through to government agencies exposed to threat actors, and the truth is, it’s only getting worse. In fact, in 2021 alone, it’s been reported that a ransomware attack will occur every 11 seconds, and this is already amidst a backdrop of high-profile attacks such as SolarWinds and Colonial Pipeline that have coerced governments and entities everywhere to ramp up their responses to the cyberwar that we’re facing. With cybercriminals increasingly focussed on critical infrastructure, and a further rise in supply chain attacks, it’s not surprising lawmakers are taking matters into their own hands.
“Supply chain attacks rose by 42% in the first quarter of 2021 in the U.S., impacting up to seven million people, according to research. Analysis of publicly reported data breached in quarter one by the Identity Theft Resource Centre (ITRC) found 137 organisations reported being hit by supply chain cyber-attacks at 27 different third-party vendors”.
Cue, an initiative from the U.S. Department of Justice, which aims to strengthen defences and minimize the risk of intrusion on government networks due to poor cybersecurity practices from external partners. “The initiative will hold accountable entities or individuals that put U.S. information or systems at risk by knowingly providing deficient cybersecurity products or services, knowingly misrepresenting their cybersecurity practices or protocols, or knowingly violating obligations to monitor and report cybersecurity incidents and breaches”. In effect, this initiative gives the Department of Justice the leverage to fight cyber threats stemming from contractors of federal agencies who fail to follow cybersecurity standards.
Taking this into account, I was curious to know the thoughts of my network of industry experts and company leaders as to their response to this legislation.
I posed the following question:
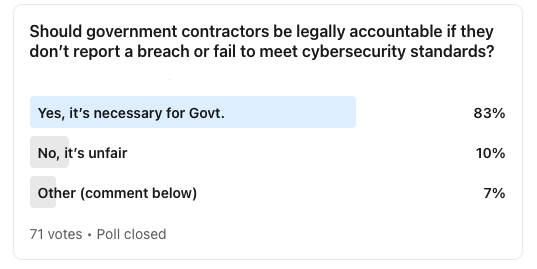
As you can see, the results are definitive.
- An overwhelming majority (83%) voted that it is indeed necessary for Government contractors to be legally accountable if they don’t report a breach or fail to meet cybersecurity standards.
- 10% voted, ‘No, it’s unfair’ .
- 7% voted that it was not a clear-cut ‘yes’ or ‘no’ answer.
The feedback and comments touched on some interesting and valuable points:
- “My immediate response is yes. Though I would say with three caveats: (1) Government standards need to be better and clearer, they aren’t homogenous across levels of government, (2) If you’re integrated with government and the breach occurs because of lax internal government security and you’re a contagion, should you be liable? (3) Reporting methods of breaches need to be improved so that stigma goes away, and crisis teams and planning occur instead. A national reporting register without consequence and indemnity from immediate bogus lawsuits would go a long way”.
- “Having a no-fault declaration period, I think is suitable, so any changes to the risk profile can be managed (before a breach). The last outcome we would want is third parties covering up unmanaged risk or compliance for fear of immediate legal action”.
- “It’s important, but governments should also be held to the same standard”.
- “I would also add said vendors that make massive claims and don’t deliver”
- “This would be the same as locking up police because they couldn’t stop your house from getting robbed, it’s hard to legally define knowingly”.
- “Given that security issues often arise within an organisation, including by contractors, the efficacy of a cybersecurity system relies on the ability to identify those gaps before breaches are realised”.
- “But if it is really about cybersecurity then the Government entity will need to allow for flexibility of budget and methods in response to new threats. If they choose not to, they hold accountability”.
- “Such an important topic, and scarily, can easily have less than necessary due diligence applied to it. Speaking from someone who has done short-term contracts in the past”
- “A great perspective on potential gaps of accountability. Just because you’re a contractor doesn’t mean you don’t owe a duty of care to your current employer – whether it be 6 months, 12 months or longer (or shorter)”.
- “I think this type of legislation is inevitable. The burden of proof for negligence and/or false representation will be tested by the courts. The clauses will likely find their way into supply contracts as well”.
- “Great poll! Standards are so important and ensuring that they are assessed regularly not only protects the data, but it protects so much more”.
- “Every company should have a standard procedure/protocol on cybersecurity”
Enhancing the Partnership
As partners working with businesses and government agencies to build their cyber resilience, we can agree that in any good partnership, both parties need to work together to establish the ground rules of accountability and to build trust. The same applies to the public and private spheres, working together to achieve cyber-resilience. It’s a complex playing field though, and there’s no one simple solution.
For partners, the implications could be even more significant, if you and your teams are supporting a government agency. There are a lot of grey areas, and plenty of room for interpretation, as evidenced by the comments in response to the poll.
I empathise with business leaders, partners and other experts who feel that lawmakers and government departments need to ensure they are incorporating best practise cyber resilience internally and across departments, in addition to, or before issuing any legislative demands. It’s only fair. No one is immune from a cyber threat, and this shift could lead to unhealthy blame-shifting.
The initiative has also considered legitimate business fears, for instance, the stigma associated with reporting breaches. The Department of Justice has responded to this by incorporating a whistle-blower provision in the overriding Act, allowing parties to identify and pursue fraudulent conduct confidently and anonymously.
As partners, I would love to know your thoughts.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282 2
UK partners call 0 800 404 8993
We’re on Facebook, Twitter and LinkedIn.