
It’s one of the most contentious topics facing businesses and cybersecurity professionals at the moment: Should ransomware payments be illegal?
Just as with our previous discussion on ‘To pay or not to pay’, it is not an easy question to answer. It is already a complex space, with a growing number of cyber threats, and the rapid rise of ransomware attacks threatening every business, from multi-national conglomerates to critical infrastructure and businesses of every shape and size worldwide.
A ransomware attack occurs every 11 seconds according to recent statistics. Globally, we see the Australian Federal Police, Europol, the U.S., and UK Governments forming task forces and sting operations to combat the ransomware threat. And there is a long line of high-profile victims, such as Nine Entertainment, JBS Meats, Kaseya, Uniting Care, Colonial Pipeline, Acer, and the HSE, Ireland’s public health service, adding to a growing list. Ransomware gangs like Black Matter, REvil, and Clop continue to wreak havoc, inflicting severe financial losses, stealing data, and leaving reputations in ruins.
A ransomware attack can have a devastating impact on a business. Every incident is different, and every company has its own unique set of challenges and priorities to consider. Balancing the advice of regulators and experts against the interests of employees, customers and shareholders is a difficult task. With the burden falling on businesses to pay a ransom (or not), the question arises as to whether ransom payments should in fact be illegal. Assistant Director of the FBI’s cyber-division, Bryan Vorndran, said, “banning ransom payments could inadvertently create opportunities for further extortion by ransomware gangs”. On the other hand, The Ransomware Action Plan takes a decisive stance - the Australian Government does not condone ransom payments being made to cybercriminals. “Any ransom payment, small or large, fuels the ransomware business model, putting other Australians at risk," Minister for Home Affairs Karen Andrews said. Some also believe that businesses are providing cybercriminals with a significant revenue stream to continue attacks.
I was curious about what my LinkedIn network of industry professionals and business leaders thought, so I posed the following question. The result and comments make for interesting reading and reflection, adding to the conflicted emotions of any business leader contemplating a payment.
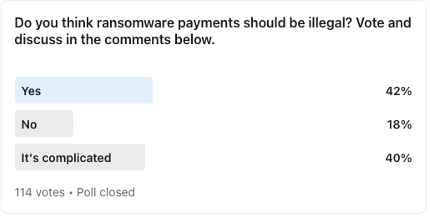
Here are the results:
- 42% say ransomware payments should be illegal.
- 18% say no, ransomware payments should not be illegal, and
- 40% say there’s more to consider and could not provide a clear-cut answer.
Here are some of the views that were expressed in the comments:
- “A clear ‘NO’. By making ransomware payments illegal will put more pressure on the victims. It will be like victimising someone who is already a victim. The Australian government made a great initiative by introducing a bill where a ransomware payment must be reported. A good start to understanding the scope and size of the problem. We need to strengthen the ransomware awareness domain. A huge number of organisations still believe that phishing training is enough for protecting against ransomware. This myth must be busted. We need to raise awareness on attack vectors of ransomware, which is much larger than phishing emails. And the most important step for any organisation is to develop a ransomware strategy and ransomware playbooks. A ransomware strategy will help organisations to identify critical assets and VAR (value at risk) which will help them develop their resilience strategy (to pay or not to pay). And ransomware playbooks will help them to smoothly transit through the attack if it happens. Ransomware is the hard reality of cyber-space, and it is out there ready to take anyone. And most organisations believe that this will not happen to them. A good cyber resilience strategy, awareness, security good practices will be helpful”.
- “It is far from clear that promoting and funding cybercrime capability, along with workforce expansion is a cogent option. Let alone the long-term impacts of extortion and cybercrime, being supported as a profitable career option. If the deficiencies in cyber hygiene, along with the absence of resilient data protection, results in a winning argument for paying ransoms, perhaps that money would be better spent on the enhancement of cyber hygiene, security capability, and data resilience. “Something” was wrong in the pre-attack state, which remains after the initial ransom is paid”.
- “Paying vast sums for extortion is a very slippery slope, leaving the need to enhance cyber security capability and data resilience overhanging, to lower the risk of subsequent similar attacks. Yes, it can be complicated, but is “what’s right” really that hard to define? Perhaps payment of a ransom not made “illegal” or criminal, but somehow strongly and economically discouraged”
- “No – consider it a market-driven fine to the business for not doing real cyber security”.
Business Continuity versus Ethics?
As a business leader in the cybersecurity industry for over two decades, I see both sides of the argument. I empathise with those victims that are in a desperate situation when struck by a ransomware attack. It’s difficult to take an idealistic view that may serve a greater public good when your business operations have ceased, networks have been hacked, jobs have been lost and your reputation is at risk of being tarnished. Business continuity is your primary concern and your duty to shareholders and employees alike.
On the other hand, although a ransomware payment might be the most expedient way out of the situation, cybercriminals are not to be trusted.
“Disruption of criminal activity does not eliminate the problem, but it raises the cost of committing the crime. Arrests and prosecution in cybercrime can be difficult, disrupting the infrastructure that is used by cybercriminals in ransomware attacks is, therefore, a key part of deterrence. In the case of ransomware, there are opportunities for both the public and private sector to focus on making the crime more difficult to commit (infrastructure disruption) and opportunities to focus on making the crime less profitable (payment disruption). The hope is that by shifting this balance, criminal actors will abandon this crime”. (Kemba Walden, Assistant General Counsel, Microsoft Digital Crimes Unit)
Arriving at a fit for all policy outcomes in relation to ransomware requires a deep analysis of the obstacles to increased cyber resilience facing businesses, and how they can be alleviated. As one very astute view pointed out in the poll comments, “Something” was wrong in the pre-attack state, which remains after the initial ransom is paid”. Businesses must invest in cybersecurity with a ‘prevention is better than cure’ mindset rather than as an after-thought. No one is immune from a cyber attack, let alone a ransomware attack, and the problem is only growing. Although it’s encouraging to see global initiatives taking place to combat this threat, it will be interesting to watch how governments continue to respond and support businesses in the coming years, and how the public and private spheres work together to increase cyber resilience against ransomware attacks.
As partners who are working so closely with customers to keep them safe, I would love to know your thoughts – should ransomware payments be made illegal?
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282 2
UK partners call 0 800 404 8993
We’re on Facebook, Twitter and LinkedIn.
Keep Informed with Weekly Updates






