 Ransomware attacks are impacting businesses every 11 seconds. That’s a staggering statistic for a threat that is all too real and wreaking havoc on companies' longevity, operations, and reputation. In Australia, the ACSC observed a 15% increase in ransomware attacks in the last year alone, whilst globally, losses from ransomware are projected to reach $US20 billion. This unfortunate global trend has called for urgent action from both the public and private sectors as we work together to combat this ominous threat.
Ransomware attacks are impacting businesses every 11 seconds. That’s a staggering statistic for a threat that is all too real and wreaking havoc on companies' longevity, operations, and reputation. In Australia, the ACSC observed a 15% increase in ransomware attacks in the last year alone, whilst globally, losses from ransomware are projected to reach $US20 billion. This unfortunate global trend has called for urgent action from both the public and private sectors as we work together to combat this ominous threat.
The past month, however, has brought some welcomed developments for businesses when it comes to ransomware, with key initiatives put in place to help fight ransomware and protect businesses from suffering from the dire consequences of an attack. We hope that these updates will have a significant positive impact and provide protection for businesses. Below are some key highlights that may be of interest to partners and customers, as we head into, what is hopefully, a more cyber resilient 2022.
International Summit on Ransomware
Sparked by the increased frequency of ransomware attacks and losses suffered by victims, the U.S. government convened a summit, bringing together 30 nations, to discuss strategies to combat ransomware as it becomes one of the most devastating threats facing us.
In a joint statement from the summit, "Governments recognize the need for urgent action, common priorities, and complementary efforts to reduce the risk of ransomware. Efforts will include improving network resilience to prevent incidents when possible and to respond effectively when incidents do occur; addressing the abuse of financial mechanisms to launder ransom payments or conduct other activities that make ransomware profitable; and disrupting the ransomware ecosystem via law enforcement collaboration to investigate and prosecute ransomware actors, addressing safe havens for ransomware criminals, and continued diplomatic engagement."
We will keep you updated on the outcomes of the summit as it progresses.
BlackMatter Ransomware
The BlackMatter ransomware-as-a-service group has been causing major havoc for businesses everywhere, targeting high-profile companies such as Olympus, New Cooperative, and Marketron, as well as many others. Claimed to be the successor of REvil and Darkside ransomware, the latter known for its attack on Colonial Pipeline earlier this year, BlackMatter has been making headlines with its increased activity – specifically targeting health care and other critical infrastructure, including two U.S. based food and agriculture entities.
As a response to this, a joint advisory has been developed by CISA, the FBI, and NSA to provide information on BlackMatter ransomware and offer technical advice with regards to mitigating cyber-attacks from the group. “This advisory provides information on cyber actor tactics, techniques, and procedures (TTPs) obtained from a sample of BlackMatter ransomware analyzed in a sandbox environment as well from trusted third-party reporting. Using embedded, previously compromised credentials, BlackMatter leverages the Lightweight Directory Access Protocol (LDAP) and Server Message Block (SMB) protocol to access the Active Directory (AD) to discover all hosts on the network. BlackMatter then remotely encrypts the hosts and shared drives as they are found”.
Read the whole advisory here: https://us-cert.cisa.gov/ncas/alerts/aa21-291a
Australian Government: Ransomware Action Plan
The Australian Government released a Ransomware Action Plan this month, to further add to the global reckoning to combat Ransomware, spurred on by attacks on Australia’s critical infrastructure, businesses, and the community at large. An example of this, cited in the Action Plan, was the ransomware campaigns targeting Australia's healthcare and aged care sectors at the height of the pandemic. The ‘Maze’ ransomware caused significant harm, by encrypting valuable information, such as sensitive personal and medical information, threatening the operation of health facilities, and causing major health and safety risks for the community.
“We are continuing to observe cybercriminals successfully use ransomware to disrupt services and steal from Australians. Whether it is conducting attacks on critical infrastructure, taking from small businesses, or targeting the most vulnerable members of our community, cybercriminals use ransomware to do Australians real and long-lasting harm. In response, the Australian Government is taking concrete action to protect Australians, including working with our international and business partners to combat this global threat” (Minister for Home Affairs, Karen Andrews).
The Ransomware Action Plan is based on three initiatives: (1) Prepare and Prevent: Building Australia’s resilience to ransomware attacks (2) Respond and Recover: Strengthening responses to ransomware attacks by ensuring that support is available to victims (3) Disrupt and Deter: Disrupting cybercriminals through deterrence and offensive action by strengthening Australia’s criminal law regime and increasing the risk of ransomware gangs being caught.
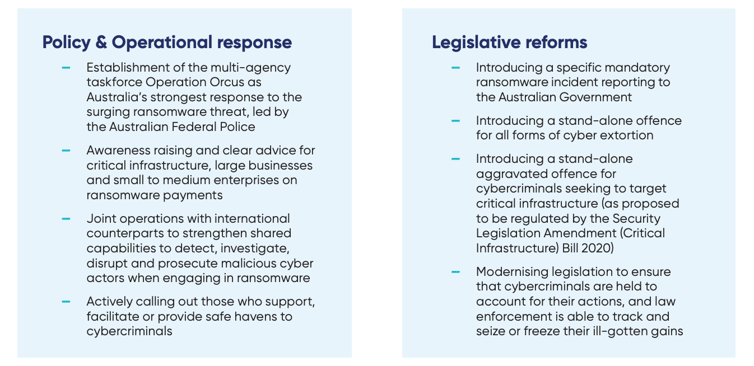
Here are some key highlights from the Ransomware Action Plan that may be of interest to our partners and customers:
- Increased investment in cybersecurity. The plan states that the Government will invest $1.67 billion over 10 years to build new cybersecurity and law enforcement capabilities to assist businesses to build their cyber resilience, protect essential services and raise cybersecurity awareness.
- Progressed Legislation. Cyber laws will be extended to help uplift the security and resilience of critical infrastructure, build a collective understanding of the threat landscape, and ensure that Governments can assist businesses in responding to threats that are too complex to be dealt with alone. Particularly those that cause substantial disruption to business operations.
- Protecting Businesses. The Action Plan states that businesses will be provided with technical cyber security advice from the Australian Cyber Security Centre on how to prepare for and respond to ransomware attacks. A free cyber security assessment tool will also be provided to small and medium businesses to help improve cyber resilience.
- Working Collaboratively. Ransomware attacks are a global threat, and the Government has promised to work with international partners to address ransomware. Australia was one of the countries invited to join the International Summit on Ransomware aforementioned. Furthermore, in 2021, the government will be launching the International Cyber and Critical Technology Engagement Strategy, investing $20.5 million to strengthen cyber and critical technology resilience in South-East Asia and $17 million to boost capability in fighting cybercrime in the Pacific.
Source: https://www.homeaffairs.gov.au/cyber-security-subsite/files/ransomware-action-plan.pdf
An interesting insight from the Ransomware Action Plan is the Australian Government’s stance on ransomware payments: “The Australian Government does not condone the payment of ransoms to cybercriminals. Australia is, and must continue to remain, a hard target for ransomware gangs. Payment of a ransom does not guarantee the victim access to its system or data and puts other Australians at greater risk”.
Read more on this heavily debated topic here: ‘Ransomware: To Pay or Not to Pay? 5 Factors to Consider'.
It is heartening to see the significant progress being made in this area, with governments and industry professionals taking substantial steps towards combatting this very real threat. The impact of ransomware is disastrous for businesses. No business, large or small, is immune from a ransomware attack, and with one of the key deliveries of the threat being email, we must keep updating customers on recent developments, that can help them to plan for a more cyber resilient 2022.
If you have customers that are yet to implement MailGuard to enhance their email security, the above updates provide a great opportunity to do so. You can also share the eBook, ‘Ransomware: The Worst Year Ever’ by downloading a copy here: https://www.mailguard.com.au/the-worst-year-ever. Speak to your Account Manager about what more we can do to assist you in reaching out to your customers.
No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be an open dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282 2
UK partners call 0 800 404 8993
We’re on Facebook, Twitter and LinkedIn.






