MailGuard has intercepted a series of malicious emails that attempt to manipulate users suffering from financial turmoil and difficulties triggered by the COVID-19 pandemic.
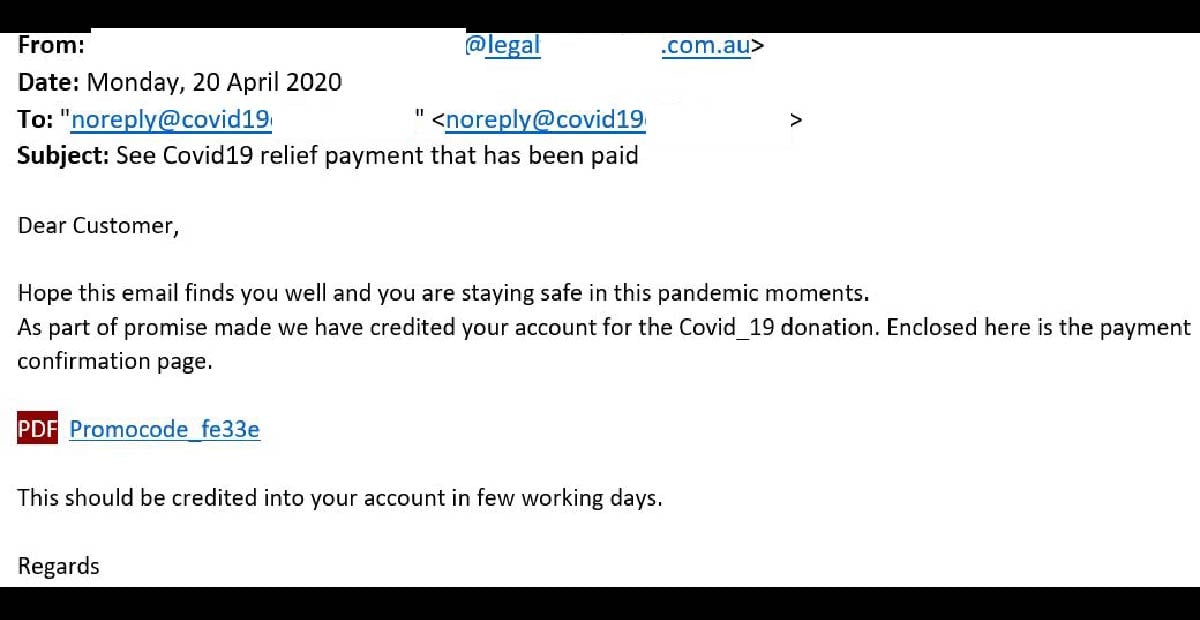
The emails have similar titles such as “See Covid19 relief payment that has been paid” or “BLOCKCHAIN: See Payment Approval for Covid19 Donation.” The sender addresses are likely to be from compromised email accounts. The example below contains a domain that appears to be from a legal firm, and other examples are from similarly trustworthy sources such as a Christian school (...@Holyfamilyschool...).
The “To:” field is an email address beginning with “noreply” and the example below uses the domain “@covid19”. The email informs the recipient that their account has been credited “for the Covid_19 donation” and that the payment confirmation page is attached. A link to this page is provided, titled “Promocode_fe33e”, along with a “PDF” image. Here is a screenshot of the email:
Unsuspecting recipients who click on the link to view the page are led, not to a PDF file, but an HTML page hosted on “getcloudapp.com” with its background blurred. A message appears at the front of this page, titled “Account Payable Shared A File With You”. A file labelled ‘Remittance Advice” is included, along with a link to download the file, as per the below screenshots:
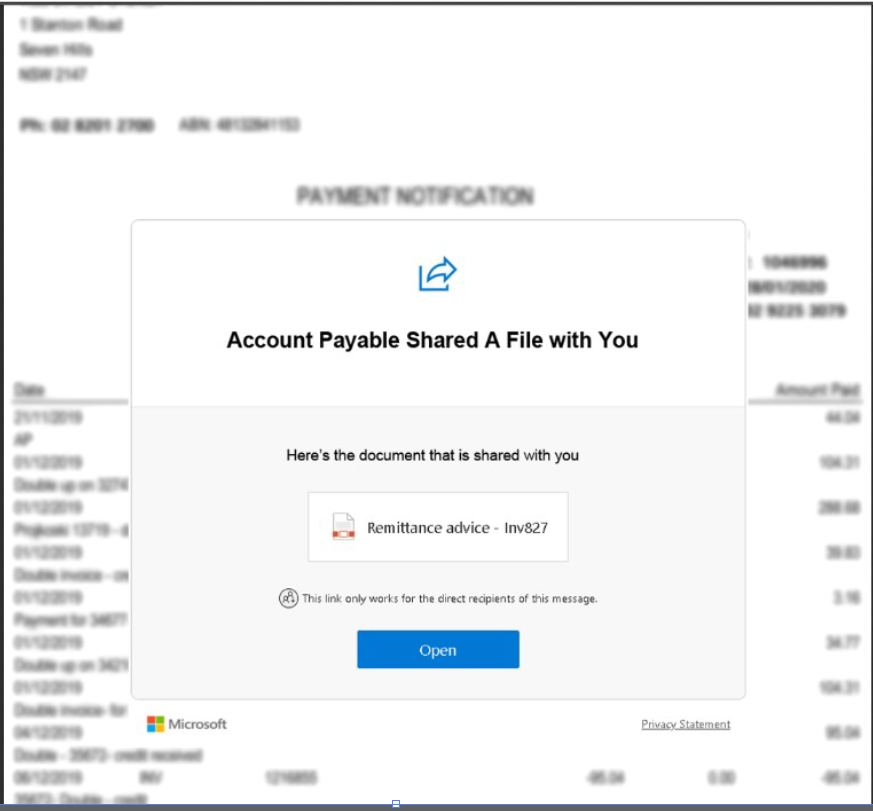
Clicking on the button titled “Open” currently leads to an error page.
This is a particularly sinister scam as cybercriminals are attempting to exploit users who may be suffering from financial difficulties as a result of the economic uncertainty caused by the COVID-19. Scammers are well-aware that many individuals and businesses are currently in desperate need of economic assistance. Cruelly, these attackers are capitalising on this hardship to steal even more from those who are already suffering.
Here are some ways this email scam has attempted to exploit users:
- The use of a subject line like “See COVID19 relief payment that has been paid”. This creates intrigue among recipients, or even excitement among those who are actually expecting financial assistance. This may motivate them to click on the link without pausing to check for the email’s legitimacy.
- The sender address implies the email is from a legal firm, Christian school or similar respected institutions. This isn’t unexpected and is plausible that a notice of this nature may be sent with a COVID-19 relief notification, thereby not raising any alarm bells.
Despite these techniques, eagle-eyed recipients of this email would be able to spot several red flags that point to the email being a fraud. These include the fact that the email doesn’t address the recipient directly, and that the link included in the email doesn’t actually open a PDF, as implied. Several grammatical errors like ‘in few working days’ and spelling errors (“Covid_19”) are also red flags that this email is, in fact, not legitimate.
The practice of launching cyberattacks that are centred around ongoing trends isn’t anything new. Cybercriminals have long employed these tactics to take advantage of any disruptions and vulnerabilities in the hope that users’ uncertainties and fear around new changes will get better of them and they will not pause to check for the legitimacy of these emails.
Coronavirus-themed cyberattacks are designed to play with human psychology and emotions, like this one we intercepted a few weeks ago. As such, we strongly advise being extra vigilant when you receive emails such as these and lookout for any tell-tale signs that might be suspicious.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







