MailGuard has intercepted a phishing email masquerading as a fraudulent invoice notification that is designed to harvest your Adobe Cloud credentials.
Titled ‘Outstanding Invoice’, the email was sent from a single compromised email address using the domain ‘@plan-international.org’. It uses a display name of ‘Mubanga, Chama’, as per the below screenshot:
Interestingly, a DocuSign-branded header included within the email body claims that a sales agent with another name, ‘Malyangu, Eric’ has ‘sent you a document to review and sign’. A link is provided to review the document.
As you can see from the screenshot below, the email body in itself is very short, with a ‘Thank You’ note included, along with a mention that the email has been ‘powered by DocuSign’.
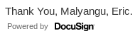
This note is followed by a banner titled ‘Covid-19 Pandemic’, that is designed to look like an advertisement by Plan International, a development and humanitarian organisation that advances children's rights and equality for girls. The company’s logo is included, along with a link to ‘find out more’.

Here is a screenshot of the email in its entirety:
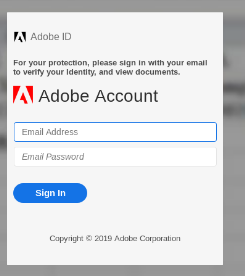
Unsuspecting recipients who click on the email to review are redirected to what looks like an Excel spreadsheet that is actually a phishing page. However, the page appears blurred, and instead a message appears at the front of the page. It asks recipients for their Adobe account details, including their email address and passwords. The message includes Adobe’s branding and logo, as per the below screenshot:
Here is what the page looks like in its entirety, including the background:
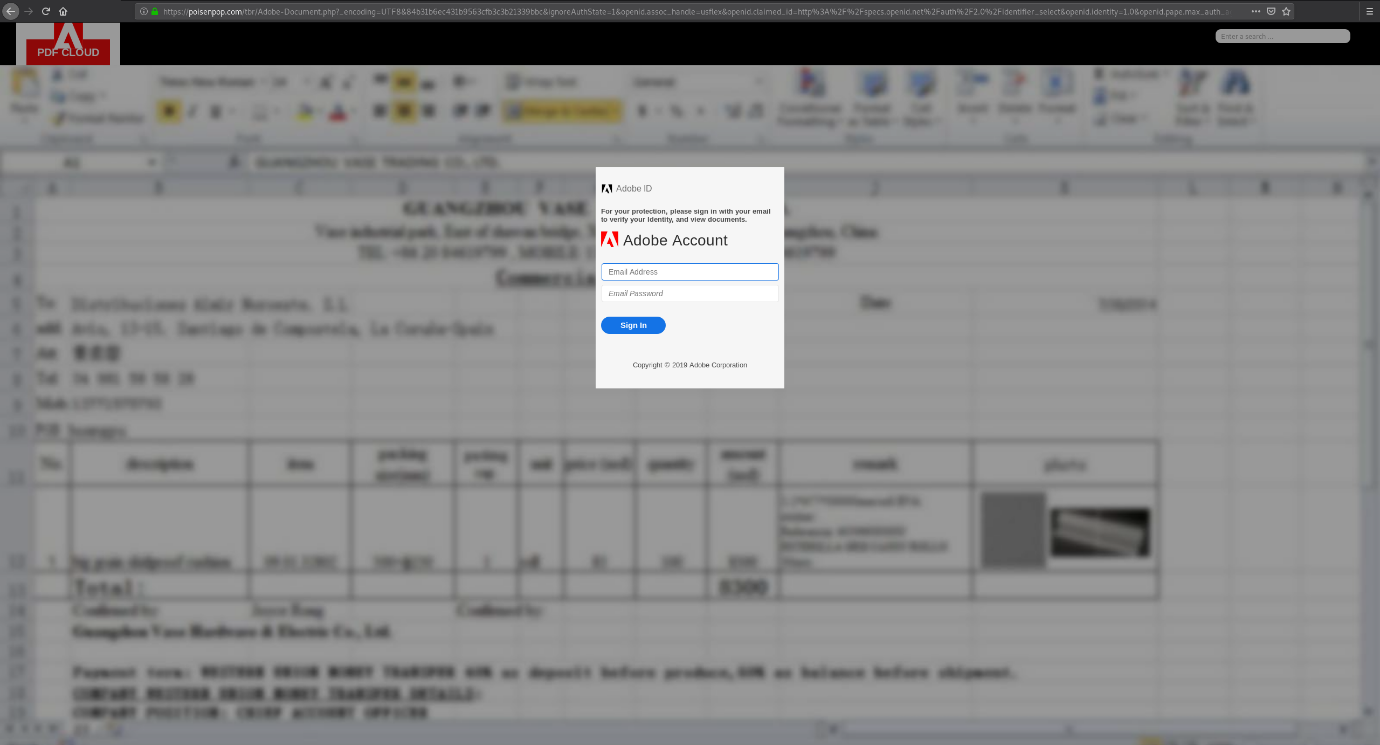
Upon ‘signing in’, recipients are redirected to the actual Adobe website.
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
As you can see from the screenshots above, cybercriminals have employed multiple elements to trick recipients. Here are some of them:
- The use of a subject like ‘Outstanding Invoice’. This creates alarm and intrigue among recipients, who may click on the link without pausing to check for the email’s legitimacy.
- The email header uses a typical DocuSign style email format, including its logo, that users may recognise. DocuSign is a popular file-sharing service that is commonly used in business correspondence. This makes them an attractive target, and since their service requires users to click a link to download files, they are a convenient trojan horse for malicious attacks like this one and may not raise any alarm bells.
- The actual phishing page uses Adobe’s branding and logo, as mentioned above. Again, this is done to convince users that the page is actually an Adobe file.
- The inclusion of the banner that contains details surrounding COVID-19 and what the company is doing in light of the pandemic. This mention of an ongoing worldwide global health emergency draws attention towards the email and may deter intrigued users from immediately dismissing it.
Despite these techniques, eagle-eyed recipients of this email would be able to spot several red flags that point to the email’s in-authenticity. These include the fact that the email doesn’t address the recipient directly, and that domain in the email link does not belong to DocuSign. The fact that the supposed DocuSign link surprisingly leads to an Adobe branded page that isn’t hosted on an Adobe domain is another big red flag that this email is, in fact, not legitimate.
This email scam is a good example of the need to be extra vigilant when you receive emails such as these and lookout for any tell-tale signs that might be suspicious.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







