MailGuard has intercepted a phishing email scam purporting to be sent from Qantas titled “Your Coronavirus Relief Bonus is about to expire”.
The email actually originates from several email addresses that belong to different domains. Multiple display names are also used in this scam, but each of these always contain the word “Qantas”.
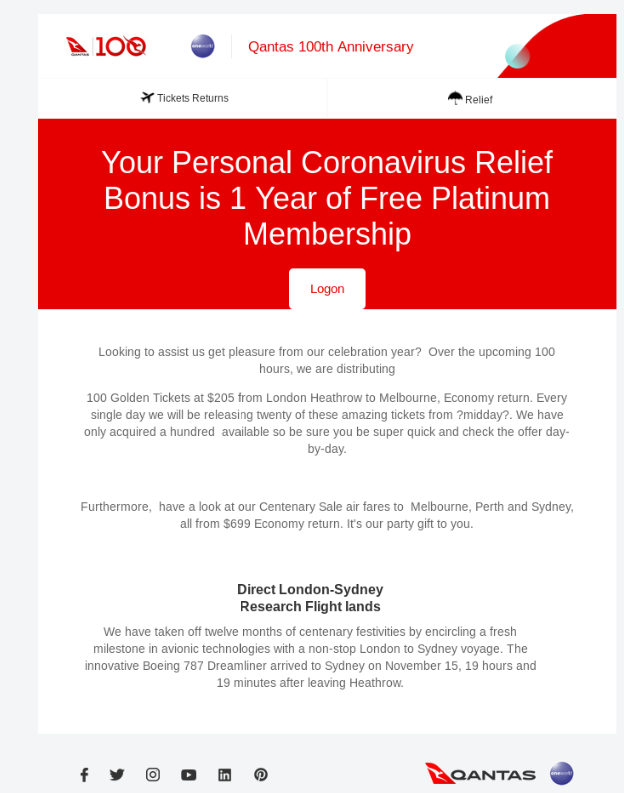
The body of the email contains the Qantas logo and branding and is titled “Your Personal Coronavirus Relief Bonus is 1 Year of Free Platinum Membership”. Recipients are provided with a button to login and claim the bonus.
Here is what the email looks like:
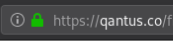
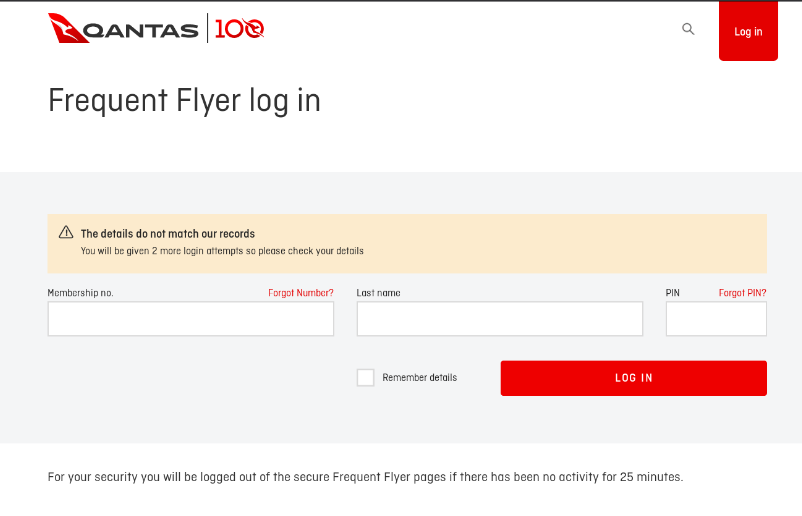
Upon clicking the button, victims are redirected to what appears to be a Qantas Frequent Flyer login page. This is actually a phishing page. Victims are asked to insert membership number, last name, and security PIN. Interestingly, this page is hosted on a domain called Qantus.co that appears almost similar to the one legitimate Qantas pages are hosted on, i.e. Qantas.com.
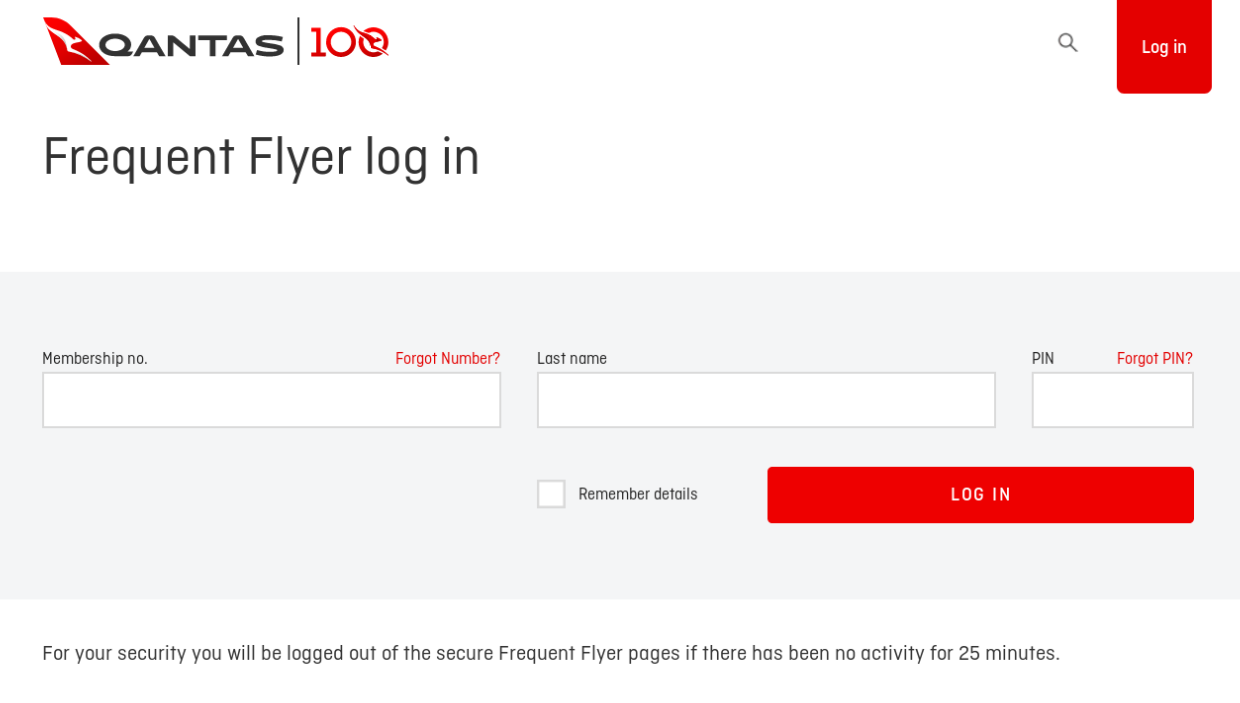
Users who insert all the above fields are then taken to another page containing the message "The details do not match our records". If they re-insert their login credentials, the same error message is displayed again.
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Cybercriminals are well-aware that the COVID-19 crisis has triggered the introduction of many new economic stimulus packages and relief measures around the world. As such, they know that an email offering a relief package in the form of a valuable Qantas platinum membership isn’t likely to raise any red flags among recipients. Here are some techniques that cybercriminals behind this scam have employed to trick users:
- use of a display name like “Qantas Support” suggests the email is sent from an official source belonging to Qantas, boosting its credibility. Qantas is a well loved and established brand, with an immensely large customer base, widening scammers’ victim pool.
- use of a subject line like “Your Coronavirus Relief Bonus is about to expire”. The threat of expiry motivates users to take immediate action, or risk losing their free membership. Cybercriminals behind this scam hope in their urgency to take action, recipients don’t pause to check for the legitimacy of the email.
- incorporating Qantas’ logo and branding elements in the email and in the phishing pages. This helps to convince users that those pages actually belong to Qantas.
- the inclusion of a domain (“Qantus.co”) that is highly similar to the actual Qantas domain (“Qantas.com”). Scammers know that the absence of official domains is a red flag that many users look out for, and by including a domain that highly resembles the actual Qantas domain, they are attempting to trick those users.
Despite these techniques, eagle-eyed recipients of this email would be able to spot several red flags that point to the email’s in-authenticity. These include the fact that the email doesn’t address the recipient directly, that the email address used in the “from” field doesn’t use a familiar domain, and that its body contains several grammatical and spelling mistakes that aren’t likely to be present in an official notification from Qantas (e.g. “we will be releasing twenty of these amazing tickets from ?midday?”). It’s also interesting to note that the actual message body suspiciously contains no mention of COVID-19 or Coronavirus, or even any details about its offer on a free Platinum membership, as mentioned in its subject line and email body header.
This practice of launching cyberattacks that are centered around ongoing disruptions like COVID-19 isn’t anything new. Cybercriminals have long employed these tactics to take advantage of any disruptions and vulnerabilities in the hope that users’ uncertainties and fear around new changes will get better of them and they will not pause to check for the legitimacy of these emails.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







