What do crooks need to get into the cybercrime racket?
It’s a lot less complicated than you think these days. Wannabe online crims can just sign up for a $50 / month subscription to an online service like ‘Rubella Macro Builder’ and start churning out malware scams at the rate of dozens a week like they’re sending out Facebook memes.
According to estimates from the White House Council of Economic Advisers, the cost of cybercrime could be more than US$100 billion p/a in the United States alone. Realistic figures on worldwide cyber-attacks are hard to establish, but trusted sources like the Financial Times say that the overall trend is rapid growth.
Part of the reason that cybercrime is booming right now is that it is easier than ever for new players to enter the arena. In the early days of the internet, malware was created and deployed by hackers; software specialists who usually worked inside the IT industry, but that is no longer the case because DIY tools like Rubella Macro Builder have lowered the knowledge bar for entry. In the same way that Amazon Kindle brought e-book publishing within reach for everybody, DIY malware kits have made cybercrime highly accessible. There’s even a name for this new criminal industry sector: MaaS; Malware as a Service.
The latest DIY malware
Rubella is suspected to be the work of a Russian cybercrime syndicate. It is the latest MaaS kit to hit the blogosphere headlines and it’s gained notoriety because of the type of cyber-attack it generates. Rubella is a tool for making .doc and .xls files with hidden macro code; tiny software fragments that are harmless in themselves but have the ability to download and install secondary malware files.
Hidden macros are a common component of email-borne malware attacks. They’re a favourite attack vector with scammers because they install malware through the simple act of opening an email attachment.
Scammers send out a message to random recipients with some bogus message inviting them to look at an attached document and when the victim clicks on the attachment, the macro code installs malware onto their computer.
Rubella, and other MaaS kits like it, make creating malware infected attachments a simple drag-and-drop process; no coding or design work required.
How malware attacks work
MailGuard detects macro malware messages regularly and they usually take the form of brandjacking scams; email-based attacks that are designed to look like legitimate communications from trusted companies.
A typical macro malware email might look like an invoice notification message with a ‘view your invoice’ link in it; the victim clicks the link and opens the attached document, unwittingly activating a malware download that will install spyware or ransomware on their device.
Here’s a screenshot of a macro malware scam email that MailGuard detected in February this year:
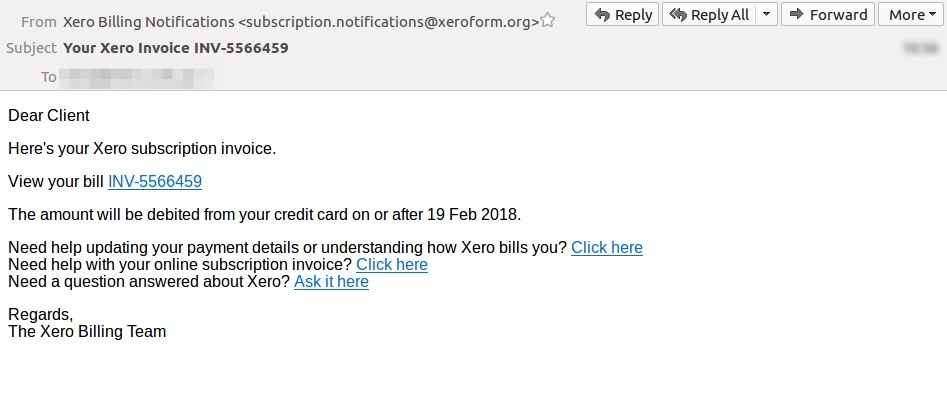
This innocuous looking message cunningly name-drops Xero’s trademark - one of the world’s best known online accounting services - and invites recipients to click on a link and ‘view your bill.’
The link opens a .doc file containing macro malware that will quietly infect the victim’s computer in the background without them even knowing.
The potential rewards of cybercrime are huge. It’s possible for criminals to score millions of dollars with a single attack, so paying $50 a month for a MaaS scam subscription like Rubella must seem like a great investment for a lot of would-be crooks.
Protect against hidden threats
Every organisation should take email-borne threats seriously. Most businesses rely on email as an integral part of their day-to-day operations, and statistics consistently show that 90% of cyber-attacks are perpetrated via email.
Innocent email attachments can carry malware capable of infecting a company’s entire computer system, and tools like Rubella make generating that sort of malware a simple process.
The proliferation of user-friendly crime services like Rubella underlines the need for companies to use a multi-layered security strategy, one that includes endpoint software protection, staff education and email filtering.
People aren’t machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive email security.
Talk to an expert at MailGuard today about making your company's network secure: click here.






