Users are advised to be wary of this phishing email that aims to manipulate users into handing over their confidential data.
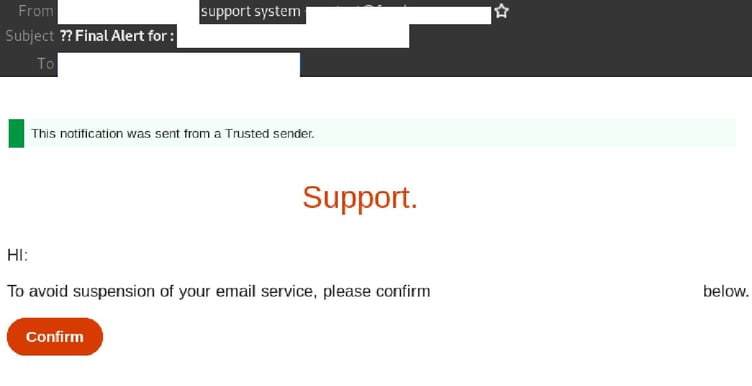
The email’s display name uses the recipient’s email domain, followed by the words “support system”. The email is titled “?? Final Alert for:”, along with the recipient’s email address. This phishing email actually originates from multiple randomly generated email addresses.
The body of the message contains a header informing the recipient that “this notification was sent form a Trusted sender”, and includes the recipient’s email domain as a title, along with the word “Support”. It informs recipients that “to avoid suspension” of their email service, they need to “confirm” their email address. A button is provided to do so.
Here is what the email looks like:
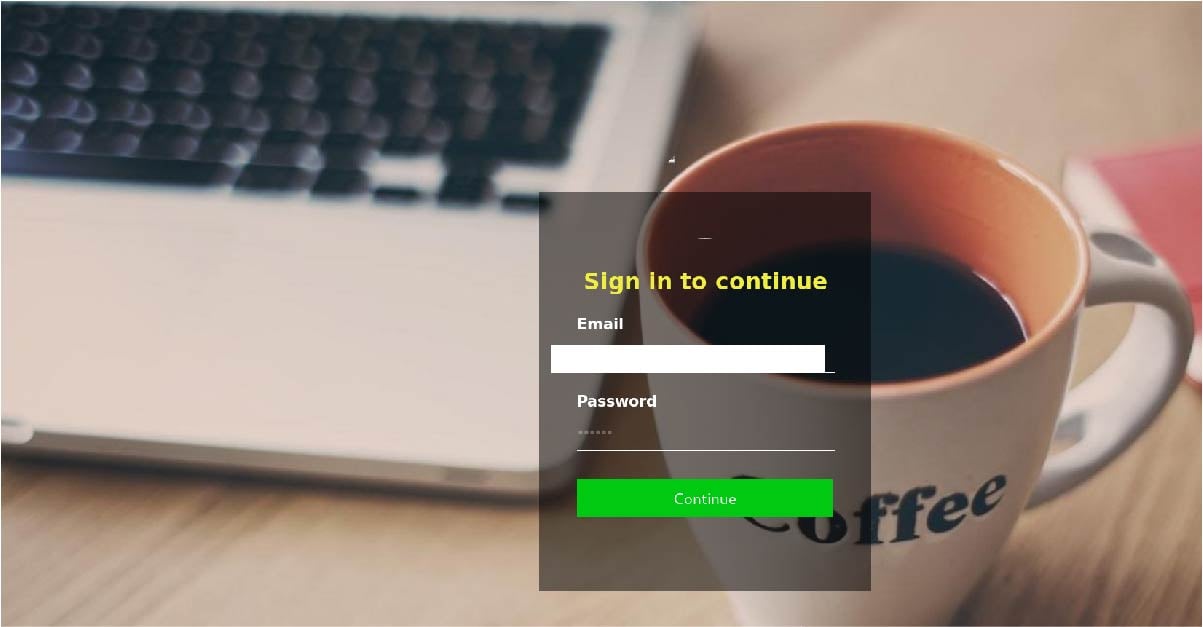
Unsuspecting recipients who click on the button are led to a login page asking them to “sign in” to their email, as per the below screenshot. This is actually a phishing page:
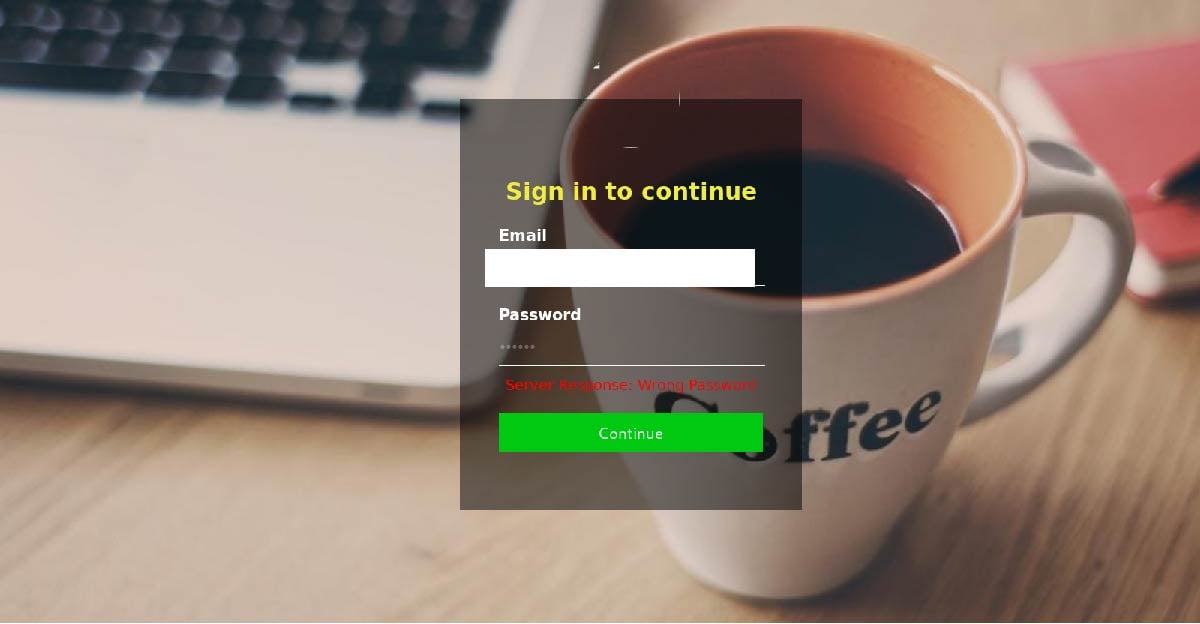
Upon “signing in”, a message appears, informing users that they have inserted a wrong password:
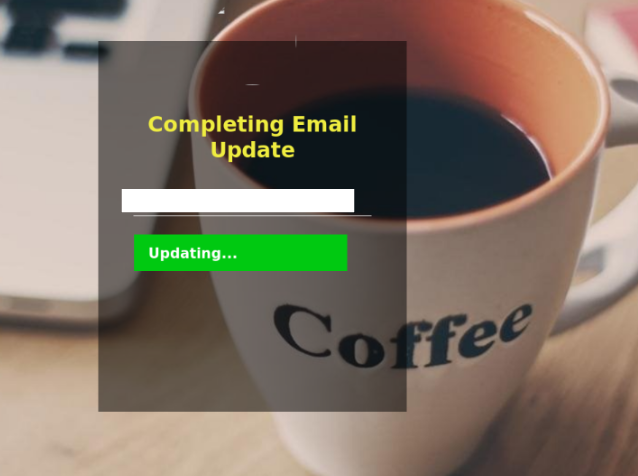
After inserting the password a second time, users are led to a page informing them that their email is being updated, as per the below:
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
The phishing email contains several typical elements that attempt to trick recipients into falling for the scam:
- presence of customised greetings, subject lines and display names that use and/or refer to the recipient’s email address. These indicate the email isn’t a generic notification but one directed specifically to the recipient,
- the inclusion of a header in the email body that ironically states this message is from a trusted sender. Headers such as these are commonly used to convince recipients that the email in question has been verified by email security filters and deemed safe.
- and attempt to alarm; using a subject line like “Final Alert’’ creates a sense of alarm and urgency, motivating the recipient to click on the malicious link.
Despite these elements, the email in itself contains several tell-tale signs that commonly belong to fraudulent emails and should help eagle-eyed recipients point to its illegitimacy. These include the fact that the ‘from’ field doesn’t use a familiar domain, as well as spacing and formatting errors within the email and in its subject line (e.g. “?? Final Alert”).
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
Don't get scammed
If your company’s email accounts aren’t protected, emails like the one above are almost certainly being received by your staff. Cybercriminals know people can be tricked; that’s why they send out millions of scam messages and put so much effort into making them look convincing.
People are not machines; we're all capable of making bad judgement calls. Without email filtering protecting your business, it’s just a matter of time before someone in your organisation has a momentary lapse of judgement and clicks on the wrong thing.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







