International shipping company DHL is once again the subject of a phishing email scam intercepted by MailGuard.
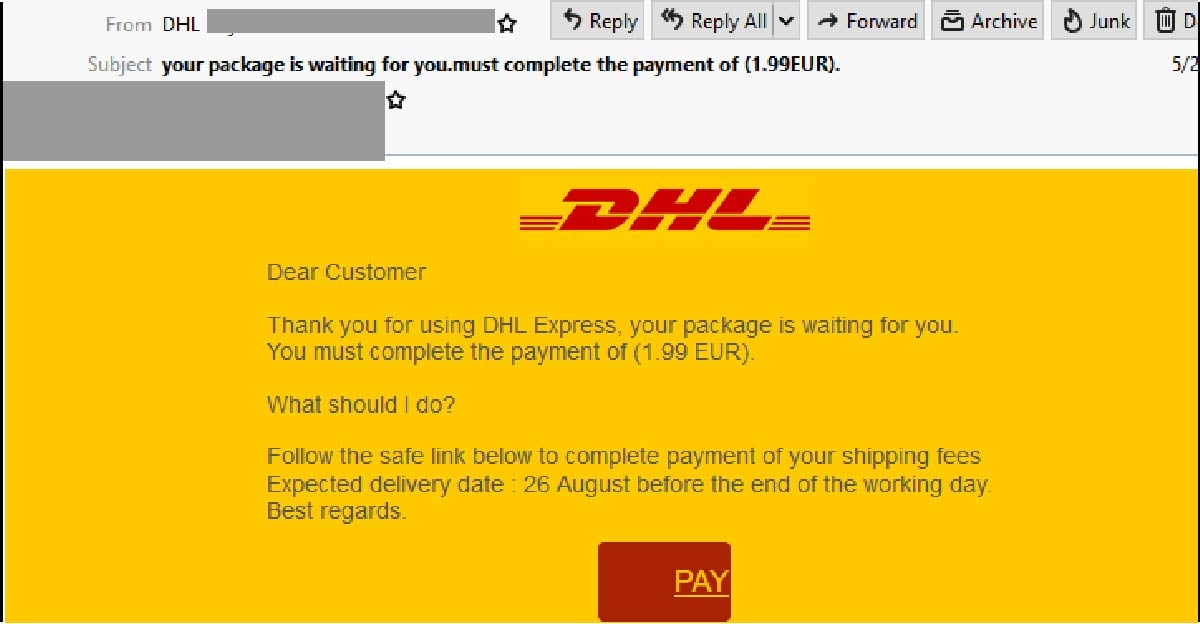
The email uses a display name of “DHL” and includes the company’s branding & logo. However, the sender address included in the email’s “From:” field doesn’t use a domain belong to DHL – a red flag pointing to its illegitimacy. The email actually originates from a SendGrid account that is most likely compromised.
The email body informs users to complete payment of their shipping fee in order to receive a package. A link is provided for them to do so, along with a tracking code and an “expected delivery date” of the package.
Here is what the email looks like:
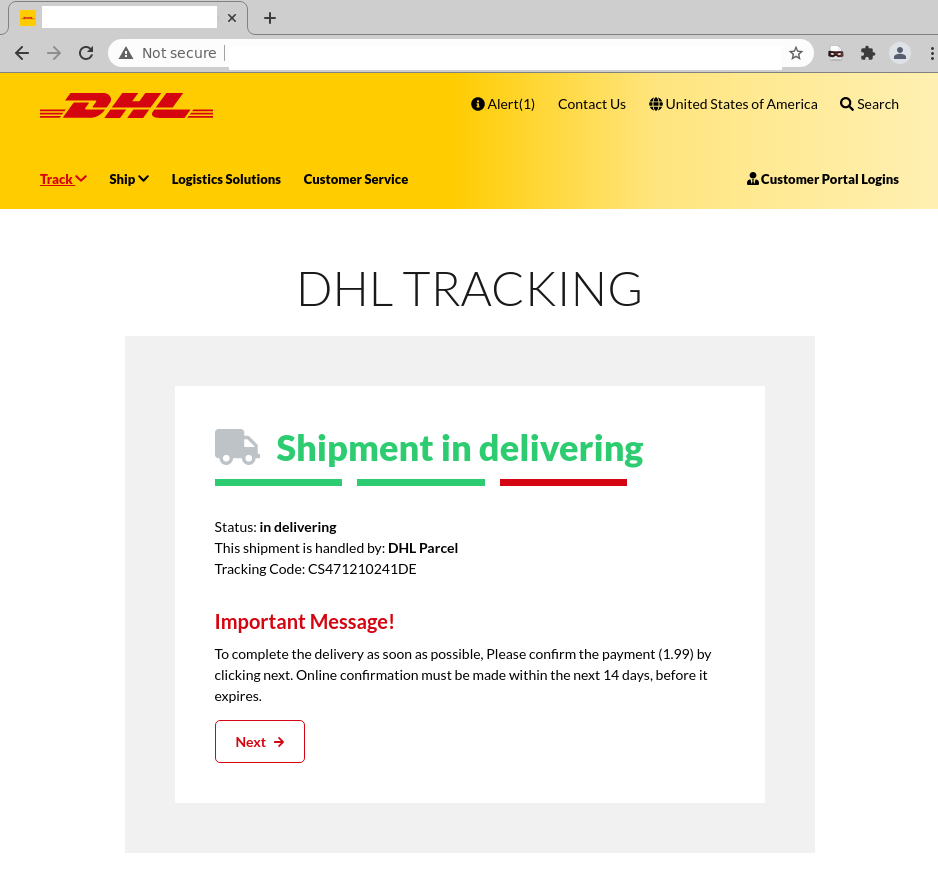
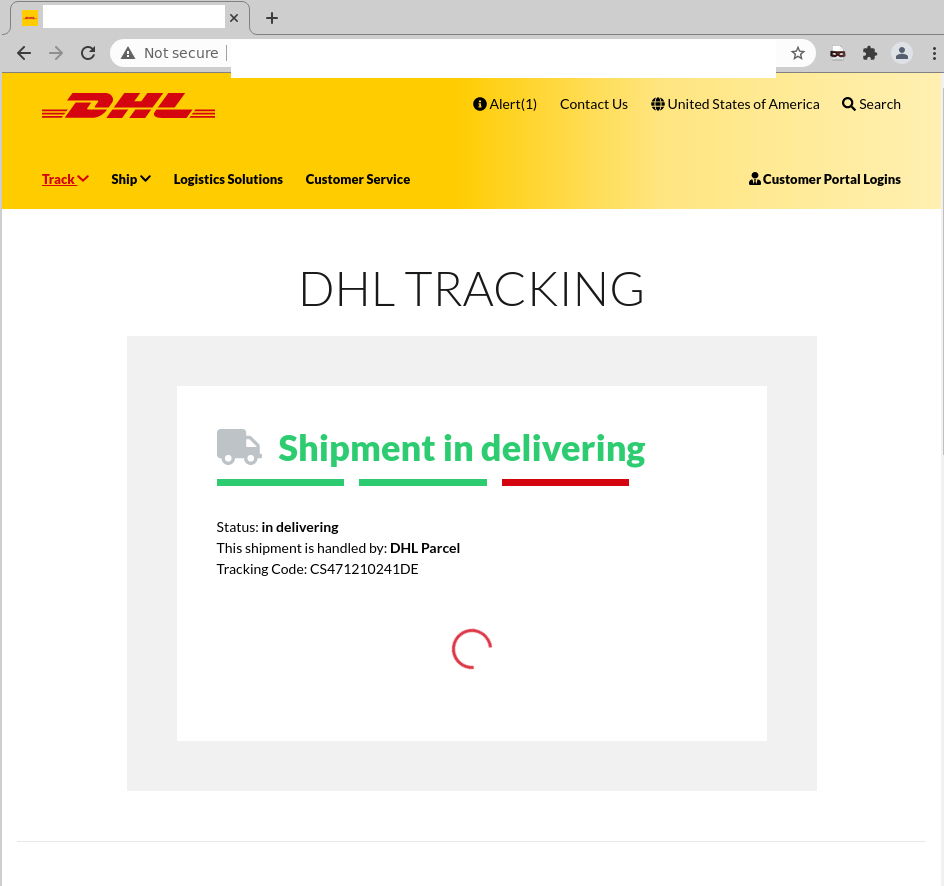
Unsuspecting recipients who click on the link to “Pay” are led to a page titled ‘DHL Tracking’. Employing DHL’s logo and branding, this page informs users that to complete the delivery of their package, they need to confirm payment "within the next 14 days" by clicking a button titled "Next". Here is what the page looks like:
After users click "next", they are led to a similar page which includes a web form. Users are asked to insert various details in the web form, including their credit card information, names, addresses and finally, a verification code as per the below:
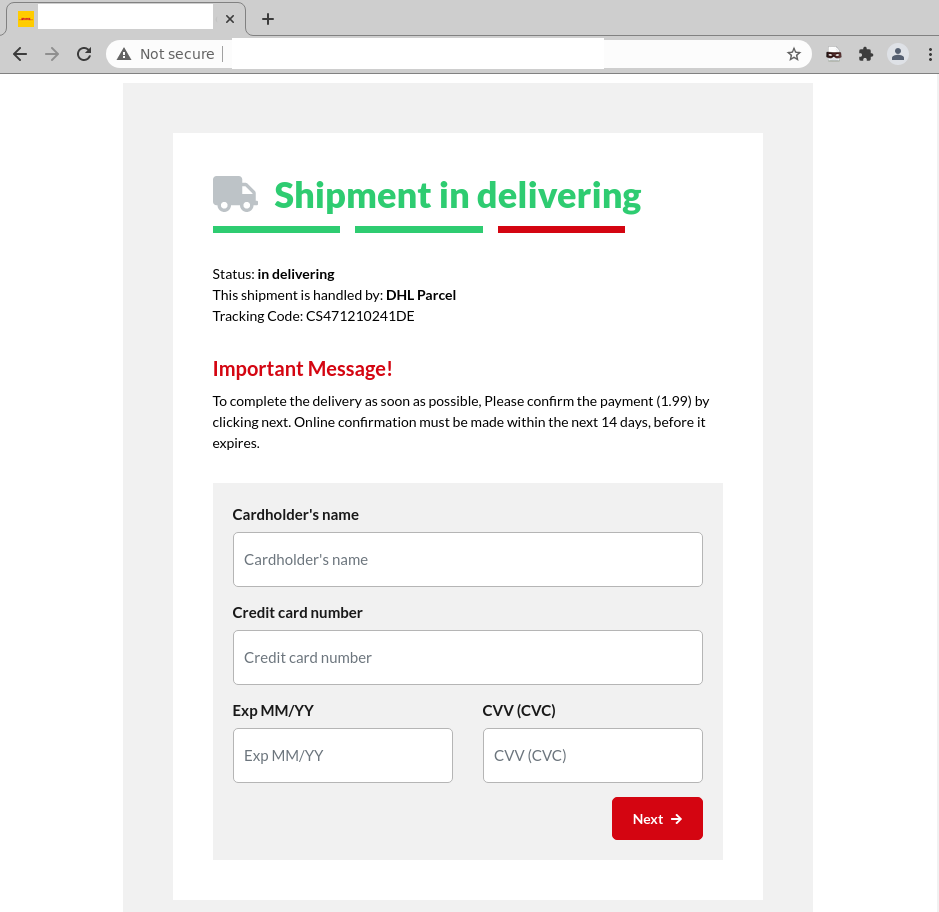
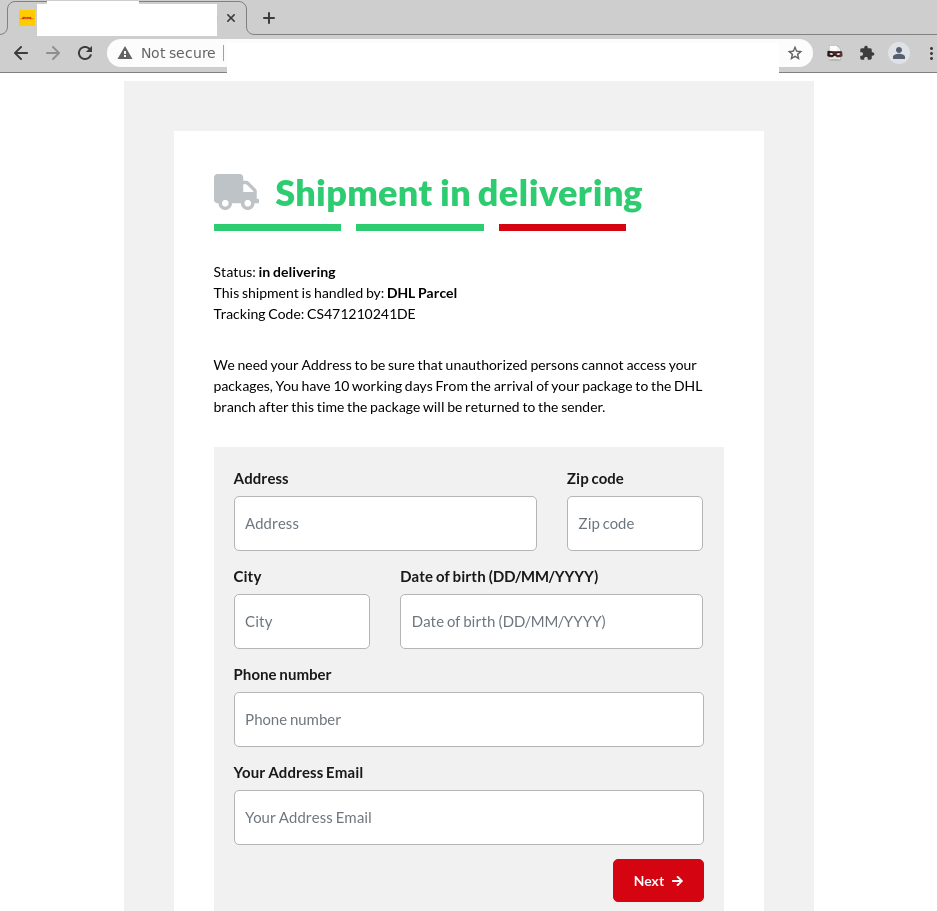
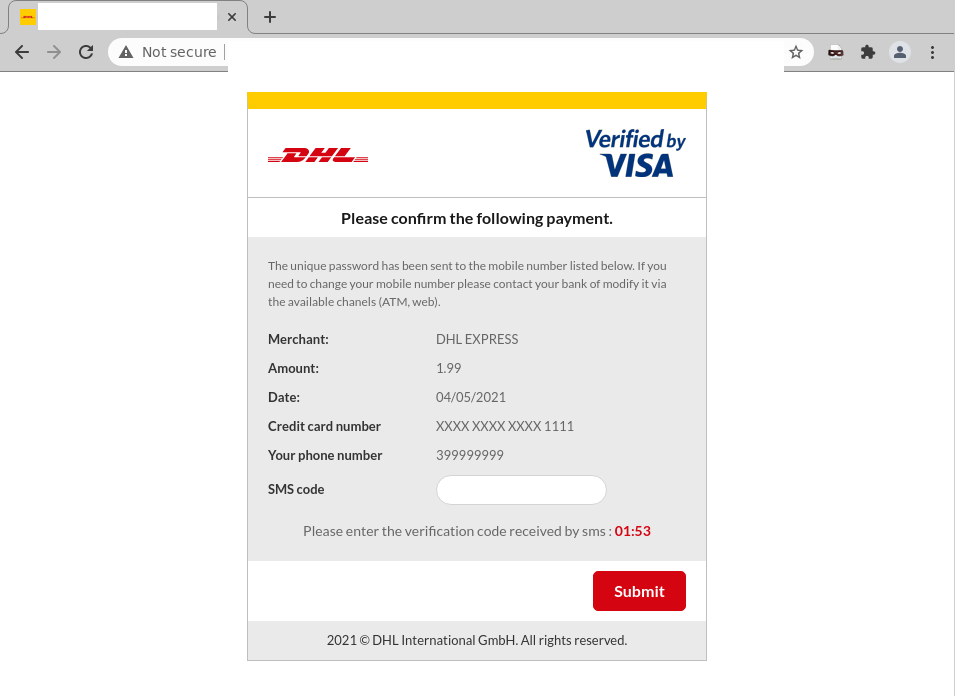
As you can see, this page also employs branding elements belonging to DHL. However, the domain used in the URL of this page, however, does not belong to the shipping company. It's actually a phishing page hosted on a third-party platform and is designed to harvest the above-mentioned credentials of users.
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Well-known companies such as Australia Post, FedEx and DHL are popular targets for scammers to impersonate because they are trusted names with large customer bases. Most recently, MailGuard reported a similar DHL-themed email scam in January this year.
The timing of this scam is particularly opportunistic. With the End of Financial Year (EOFY) approaching, many users will be shopping online to take advantage of lucrative deals & sales. This is one of the busiest parts of the year for shopping & parcel delivery. Scammers know that receiving notifications related to parcel delivery isn't likely to be unusual in this period, and hence use lures like these to trick users. We’re all eager to get our shopping on time, so we might not think twice before clicking a link in parcel-delivery notifications.
In this particular case, cybercriminals are preying on the curiosity of DHL customers who may think a ‘package’ is actually on its way. This motivates them to enter their personal details without hesitating. Here are some techniques that cybercriminals behind this scam have employed to trick users:
- The inclusion of specific details, like expected package delivery date and a tracking code, suggests the email is sent from an official source belonging to DHL, boosting its credibility,
- The use of a subject like “Your package is waiting” and an “important message” in the phishing pages informing them that the link to confirm payment will expire in 14 days. This intrigues and motivates users to take immediate action if they wish to receive their package. Cybercriminals behind this scam hope in their excitement to retrieve their package, recipients don’t pause to check for the legitimacy of the email and,
- The presence of security features like a verification code, to confirm payment. These features are commonly present in notifications from well-established companies like DHL, further convincing users that those pages actually belong to DHL.
Despite these techniques, several red flags are present in the email that should alert users of its illegitimacy. These include the fact that the recipient isn't addressed directly in the email, and that it contains spacing & grammatical errors, including within the email’s subject line.
We all love getting something (aside from a bill) in the mail, and with online shopping more popular than ever (especially since the COVID-19 pandemic), it’s sometimes hard to keep track of what parcels we’re expecting. Cybercriminals know this, and often prey on people’s busy lives and curiosity trick them.
DHL advises users to report any suspicious emails or activity to its dedicated Anti-Abuse Mailbox at phishing-dpdhl@dhl.com. More details can be found here.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







