PayPal users should be watchful before opening or responding to any generic emails advising of a ‘limit’ being placed on their account, as it is most likely a devious attempt by scammers to get a hold of account and credit card information. Many of us rely on PayPal, (approximately 392 million, in fact) as a trusted way to make and receive payments, with 29 million active merchants using the service to run their online businesses, particularly in the current pandemic influenced times. This is not the first time that MailGuard has intercepted a scam spoofing the popular global payment provider, with the rise of online shopping and ease of use from various, perhaps, unsecured devices, providing a vantage point for criminals.
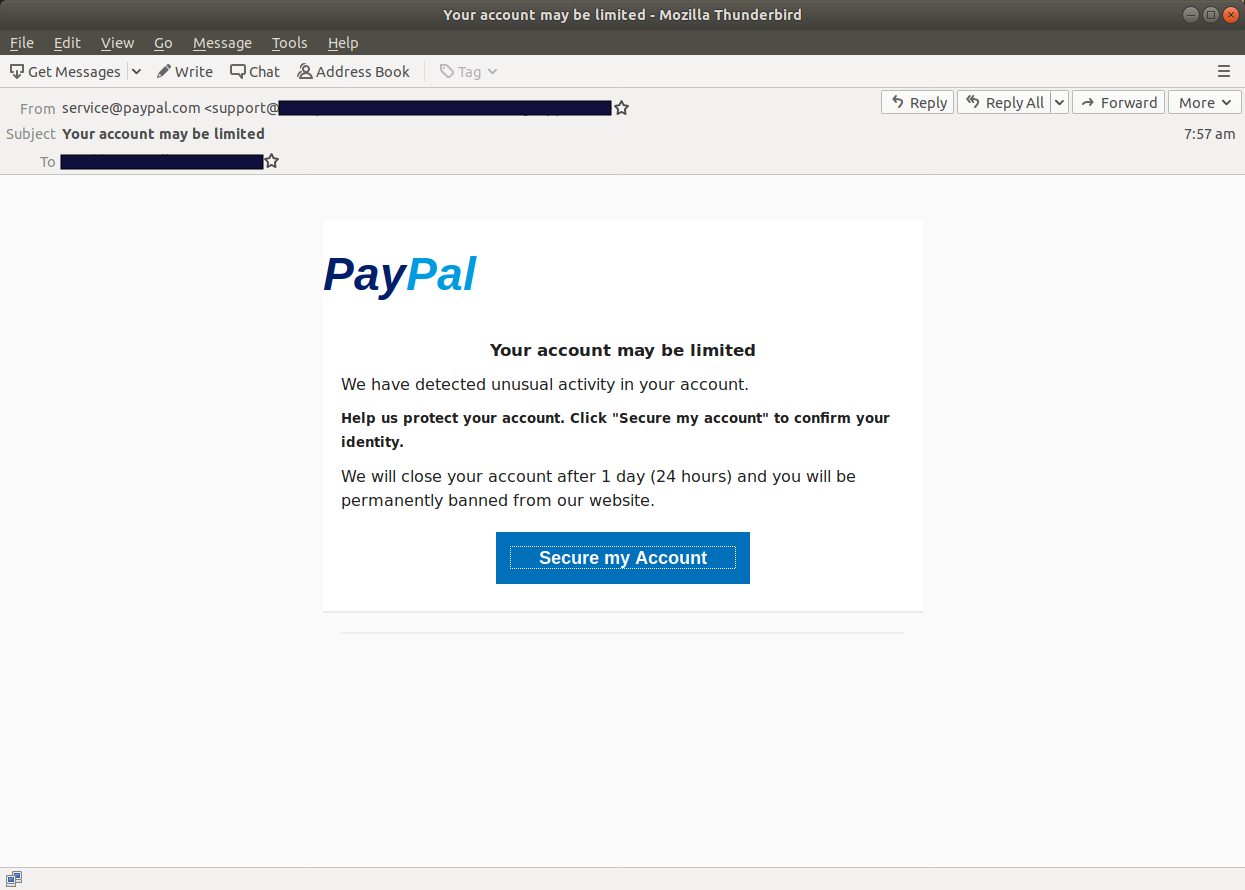
The email carries the subject line, ‘Your account may be limited’ with the sender’s name purporting to be from PayPal and displaying a legitimate domain in the email address used (i.e., service@paypal.com). The actual email however originates from a WordPress site. The legitimate domain displayed in the sender’s name has been added to distract the user from noticing the discrepancy. PayPal’s branding is incorporated into the body of the email, particularly playing on the brand colours, which could easily mislead users into believing that it is a legitimate communication. The email advises the user that there has been ‘unusual activity detected in their account’, along with a warning that their account will be ‘closed within 24 hours’, and that they will be ‘permanently banned’ from the website. A disturbing message for merchants and users alike, who may use PayPal as their primary means of transacting. Usually, a message like this would spur immediate action for the unsuspecting user. A ‘Secure my Account’ button in blue is then provided to victims to lure them into allowing continuation of their account.
Here’s what the email looks like:
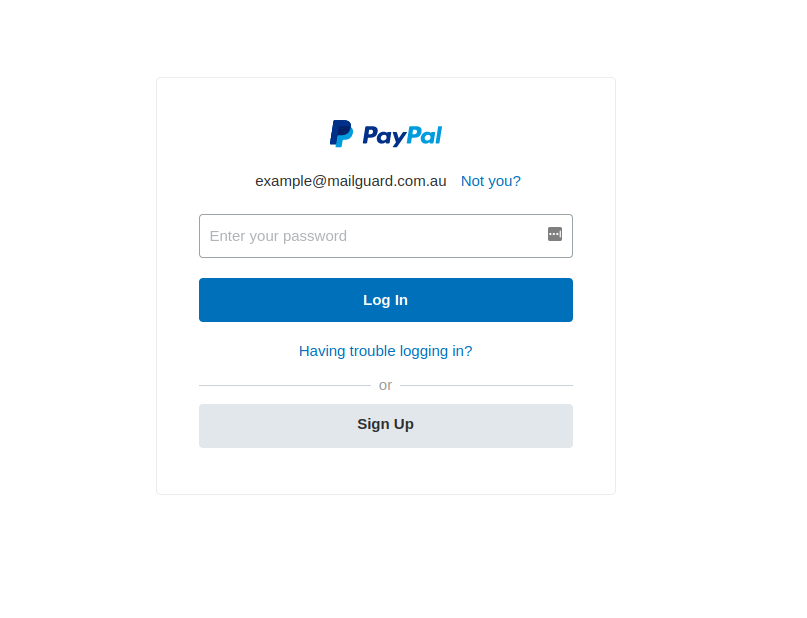
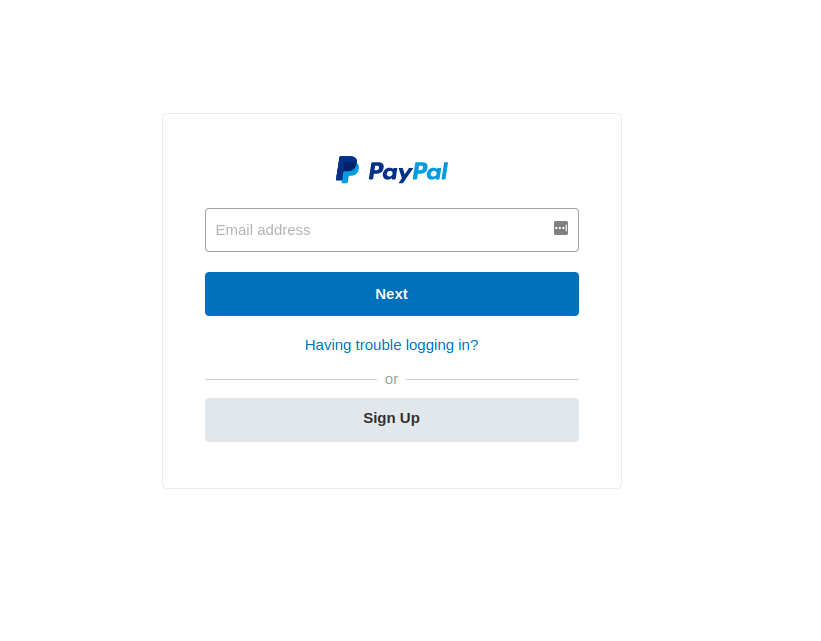
After clicking on the ‘Secure my Account’ link, users are then taken to the following two phishing pages, requiring the victim to enter the email address and password associated with their PayPal account. Each page is a close replica of the actual login pages used by PayPal.
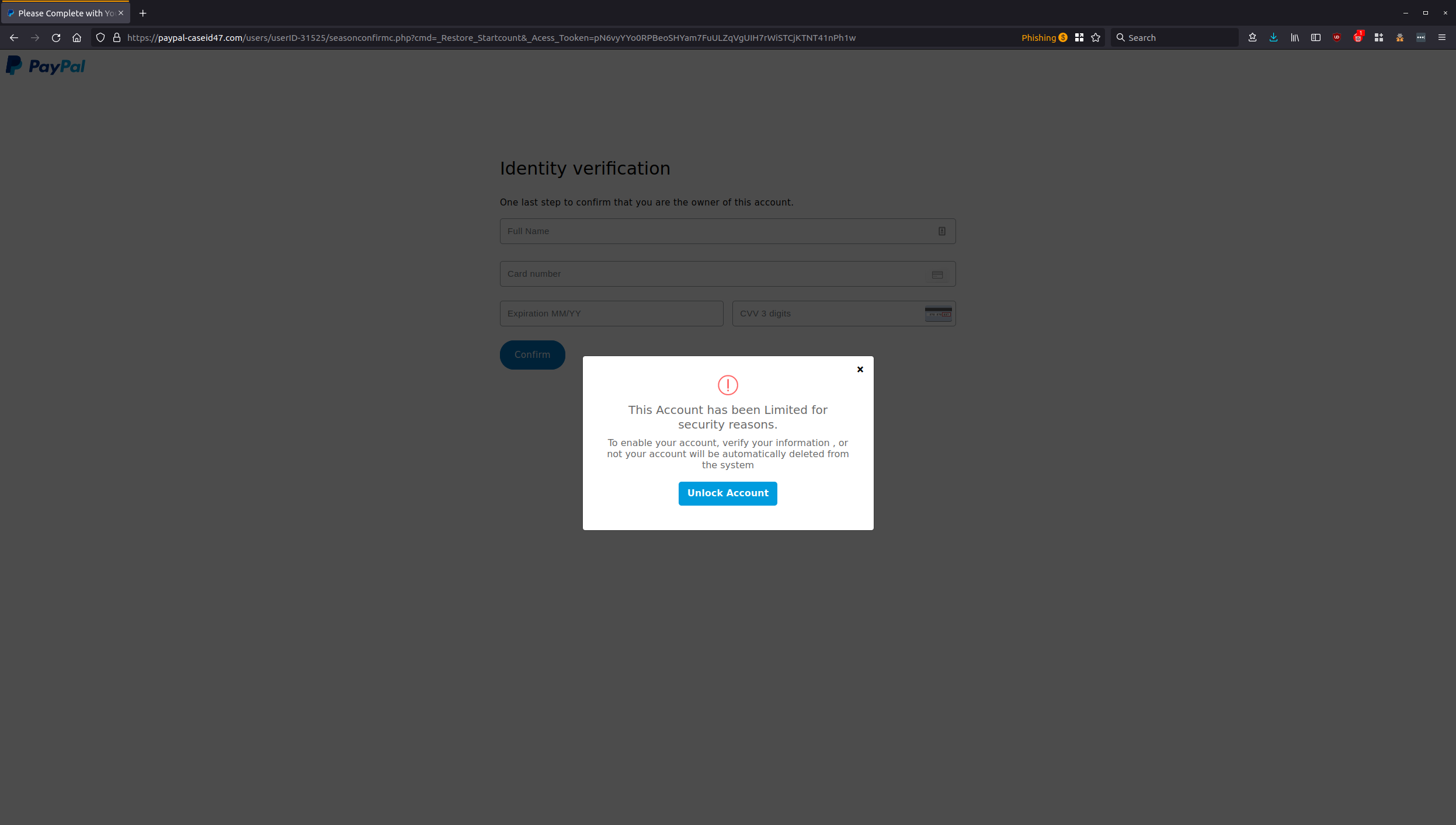
Once these details are harvested, the user is then taken to the next page, asking them to further verify their identity by entering in their credit card details. Under the guise of identity verification, a lightbox appears as an overlay to the page, advising the user that if these details are not provided, their account will be ‘automatically deleted from the system’ – deceiving unsuspecting victims into clicking on the ‘Unlock Account’ button to enter in their credit card information.
The last phishing page below asks for an SMS verification:
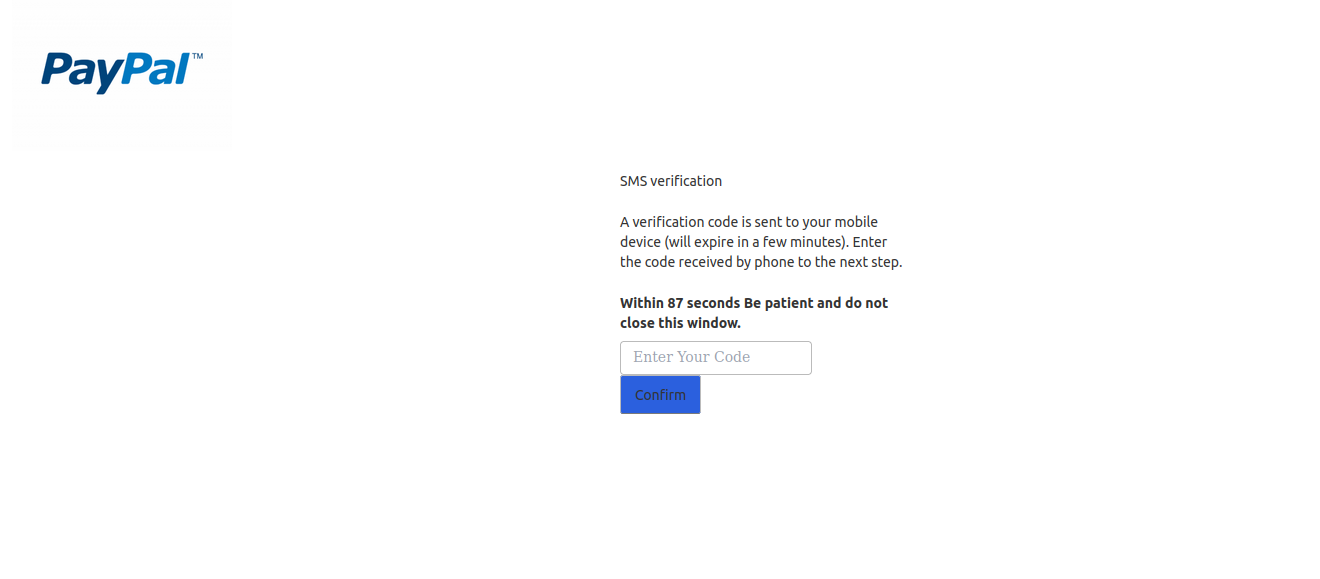
Upon closer inspection, eagle-eyed users will be able to see the red flags present in the phishing scam, particularly with regards to the grammatical errors present in the body of the email, the credit card verification page, and the SMS page. However, the close imitation of the company’s online branding, coupled with the urgency of ensuring that a PayPal account is functional, can very easily trap victims into providing cybercriminals with sensitive account details, ultimately leading to the risk of criminal activity such as identity fraud and financial theft.
"PayPal provides the following advice about how to ensure you are receiving a legitimate email from them:
An email from PayPal will:
- Come from paypal.com. Scammers can easily fake the “friendly name,” but it’s more difficult to fake the full name. A sender like “PayPal Service (zxk1942R3@gmail.com)" is not a message from PayPal. But sophisticated scammers can sometimes fake the full name, so look for other clues.
- Address you by your first and last names, or your business name.
An email from PayPal won't:
- Ask you for sensitive information like your password, or credit card number.
- Contain any attachments or ask you to download or install any software
Think you’ve received a phishing email? Forward it to phishing@paypal.com.au
For more information: https://www.paypal.com/dm/webapps/mpp/security/common-scams"
Recipients of this email should delete it immediately without clicking on any links. Providing your personal details can result in your sensitive information being used for criminal activity and may have a severe negative impact on your financial well-being.
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security. Talk to a solution consultant at MailGuard today about securing your company's network.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







