Global online payments system PayPal has once again been embroiled in a phishing email scam designed to harvest confidential data of users.
Purporting to be from PayPal, the malicious email is titled “Reminder: Take action on your PayPal account” and employs the company’s logo in its body. The sender email address in the “From:” field however, doesn’t use a domain belonging to PayPal – a red flag pointing towards its illegitimacy. The email actually originates from a compromised email account. It informs users that “some unusual activity” on their PayPal account has been detected, and that PayPal is “concerned about potential unauthorized access”.
The email informs users that for their safety, their PayPal accounts have been “temporarily limited”, until users “complete the steps required to secure” their account. A button is included to do so, and the email ends with a sign off from “PayPal”. Hovering over the link in the button reveals the presence of a URL shortener, likely included to mask its true destination (the malicious phishing page).
Here’s what the email looks like: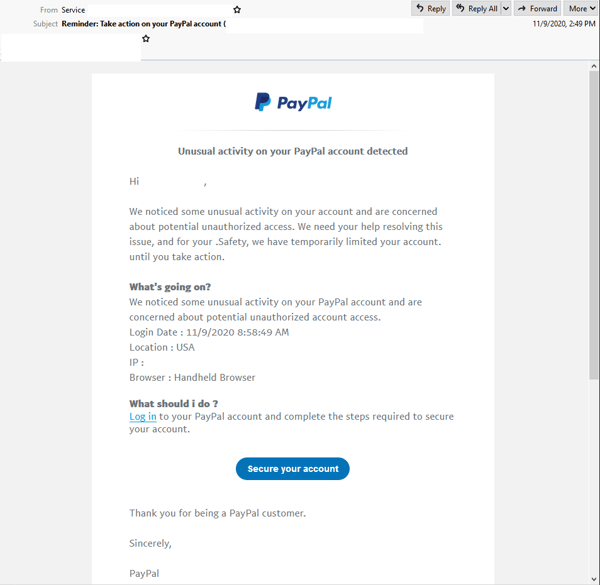
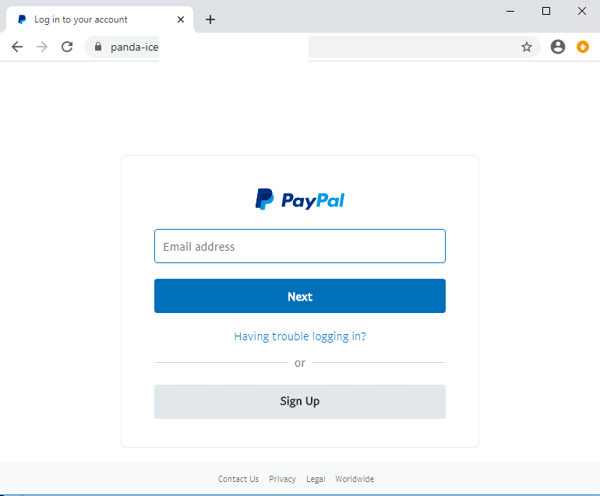
Unsuspecting recipients who click on the link are led to a page that instantly redirects them to a fake login page asking for the victim’s PayPal credentials. This page employs PayPal’s logo & branding elements, complete with support links that are typically present in genuine pages belonging to PayPal. However, the domain used in the page’s URL doesn’t belong to the e-commerce company. The page is actually hosted on a compromised website.
Once users “log in” to their PayPal account, the scam leads them to several different phishing pages that ask for various personal details, including:
- Credit card details
- Address details
- Various banking details and identifiers
- Email credentials, and
- Pictures of various documents used to verify identity, including Passport, National ID and Driver’s license
Here are some screenshots of these pages:
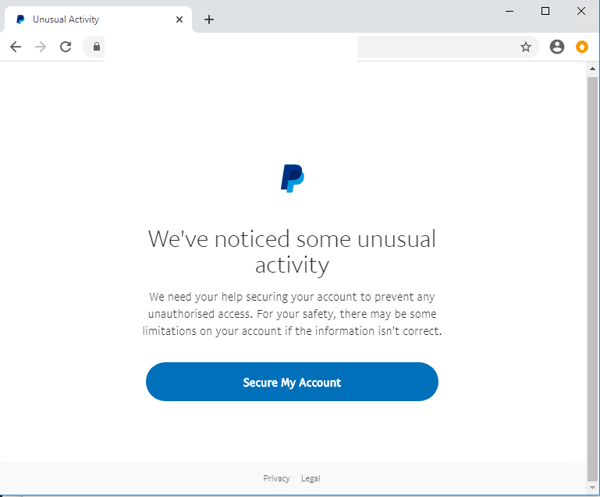
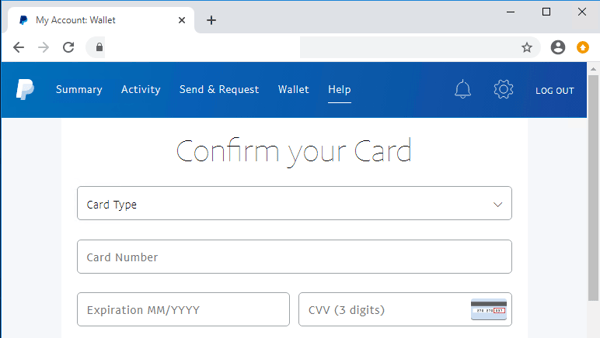
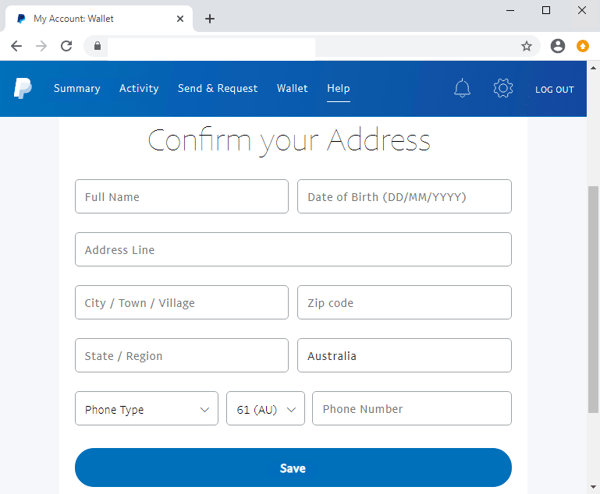
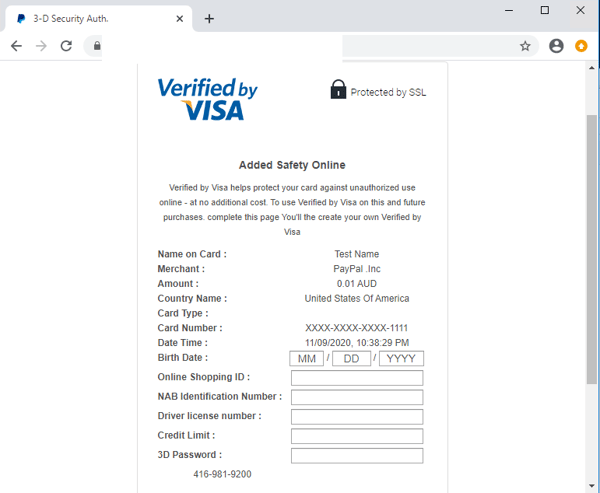
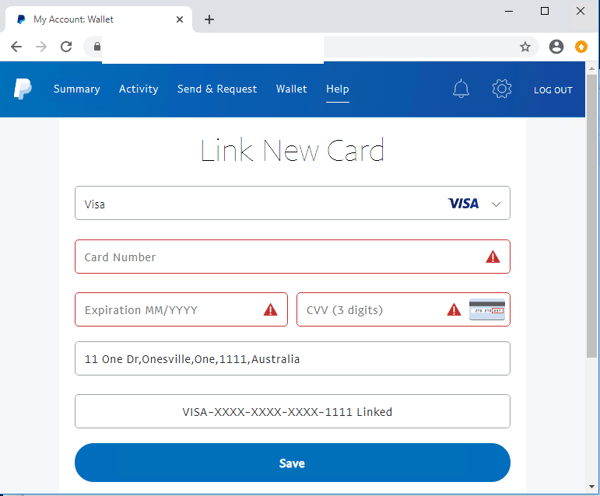
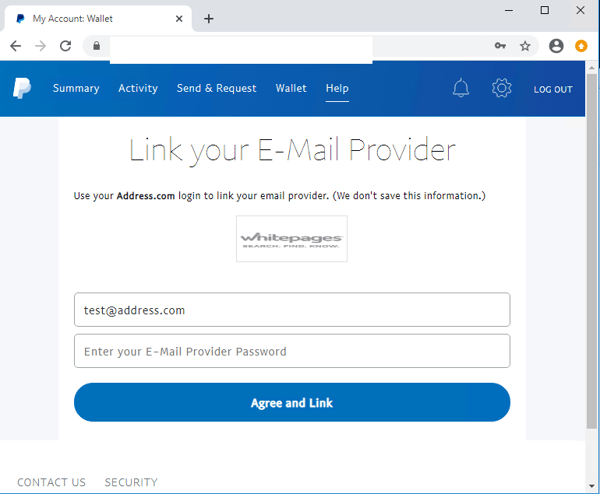
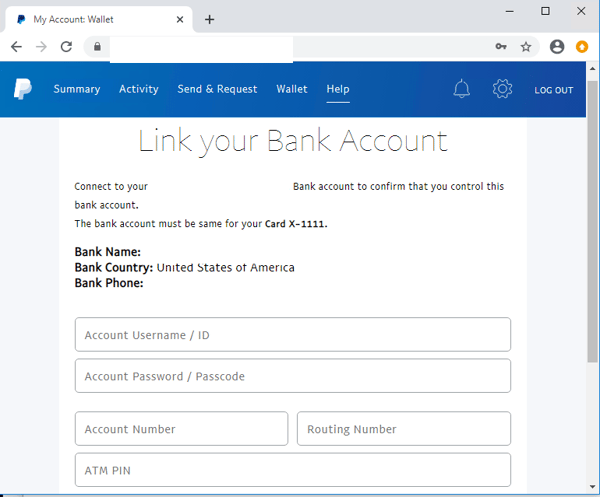
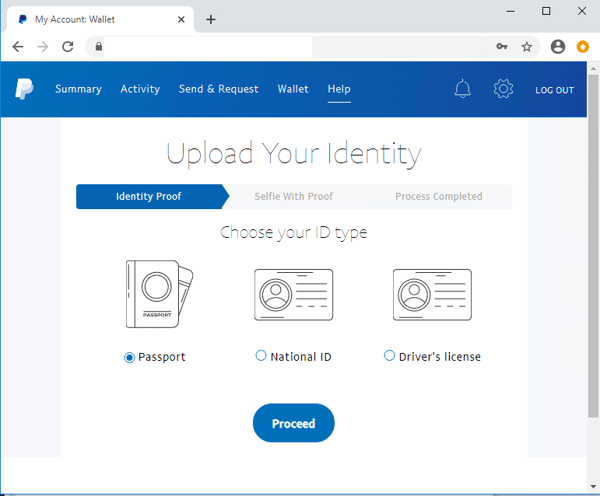
As you can see from the screenshots above, most of these pages are designed to appear as legitimate pages belonging to PayPal, employing high-quality branding and styling elements. They are crafted to steal a wide variety of personal information from users and could lead to grave consequences. If any user did fall victim to this scam, they are vulnerable to having their PayPal account hijacked, their credit card credentials used to make fraudulent purchases and their identity stolen. In addition, scams that are initiated from compromised accounts (like in this case) are particularly dangerous because the emails are sent from a legitimate account, so they are not likely to be blocked by email security services. Cybercriminals often exploit these rules to trick users.
We’ve intercepted several phishing email scams spoofing PayPal in the past. Some of these informed recipients of ‘unusual activity’ in their accounts (like this one), while others took a different approach, like confirming new activity (the addition of another address) or claiming to offer a refund.
Being a widely used and trusted online payments service supporting a plethora of online stores, PayPal is a popular target for cybercriminals, especially as more users shop online due to the closure of many physical stores during the COVID-19 pandemic. Many of us rely on PayPal as a trusted means of making and receiving payments securely, so naturally, when we receive an email supposedly from PayPal regarding an action required for our account, we would take action.
Cybercriminals behind this particular scam have incorporated multiple elements to boost this email’s credibility. These include:
- The use of an alarming subject line and body; informing recipients to take action following the detection of “unusual activity” on their PayPal account creates a sense of urgency and anxiety, motivating users to take action immediately without checking on the email’s authenticity,
- The inclusion of multiple steps & pages to “secure” users’ accounts, complete with high-quality branding elements like PayPal’s logo & branding that are typically present in legitimate pages from the company, and
- the presence of multiple details related to the “unusual activity” in the email, like login date, location, IP and type of browser used; likely included to convince recipients that their accounts have actually been accessed by an “unauthorized” source; further motivating users to take action immediately.
Despite these techniques, eagle-eyed recipients should be able to spot several red flags that point to the email’s illegitimacy. For instance, the user isn’t addressed directly in the email and it contains spacing & spelling errors (e.g. “for your .Safety”).
If you are unsure whether a notification you’ve received from PayPal email is legitimate, simply contact the company directly.
Whilst MailGuard is stopping this email scam from reaching Australian businesses, we encourage all users to be extra vigilant against this kind of email and whatever happens, do not open or click them.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







