Cybercriminals have targeted unsuspecting victims with a phishing email purporting to be from the Human Resources Department of their respective employer. The scam uses multiple methods of redirection to the phishing site, with the use of highly accurate Microsoft branding, including Microsoft Word, Microsoft Teams and SharePoint. With over 190 million people across the globe using SharePoint alone, users need to remain extremely vigilant and think twice before downloading any unfamiliar files or clicking on suspicious links, as this could allow threat actors to steal your credentials and potentially install malware, leading to a myriad of other criminal activity.
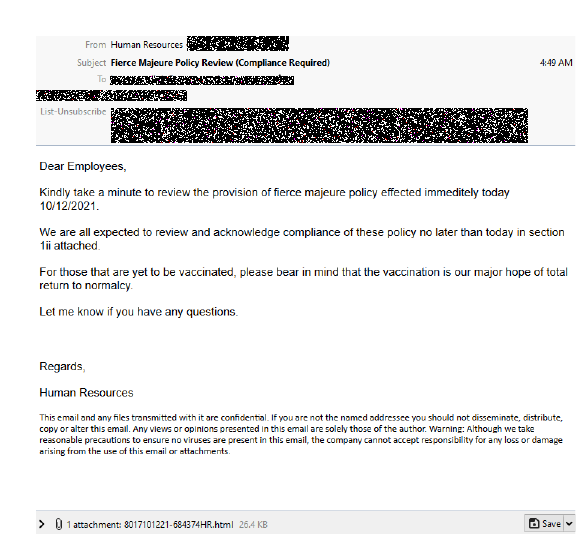
The email purports to come from the ‘HR Department’ when in actuality the email has been sent by an external fraudulent sender using a newly registered domain. The body of the email urges ‘Employees’ to ‘review the provision of fierce majeure policy’ (attached as a document) and acknowledge compliance of the policy no later than the date that the email has been received. For those who are familiar, it seems that the cybercriminals have mistaken ‘Fierce majeure’ for ‘Force majeure’ – the latter being a common clause in contracts and is most likely what the scammers had in mind to trick users into believing this is a legitimate communication. An emotive note, encouraging readers to get vaccinated, is added before the sign-off from HR, ‘Please bear in mind that the vaccination is our major hope of total return to normalcy’.
Here’s the email:
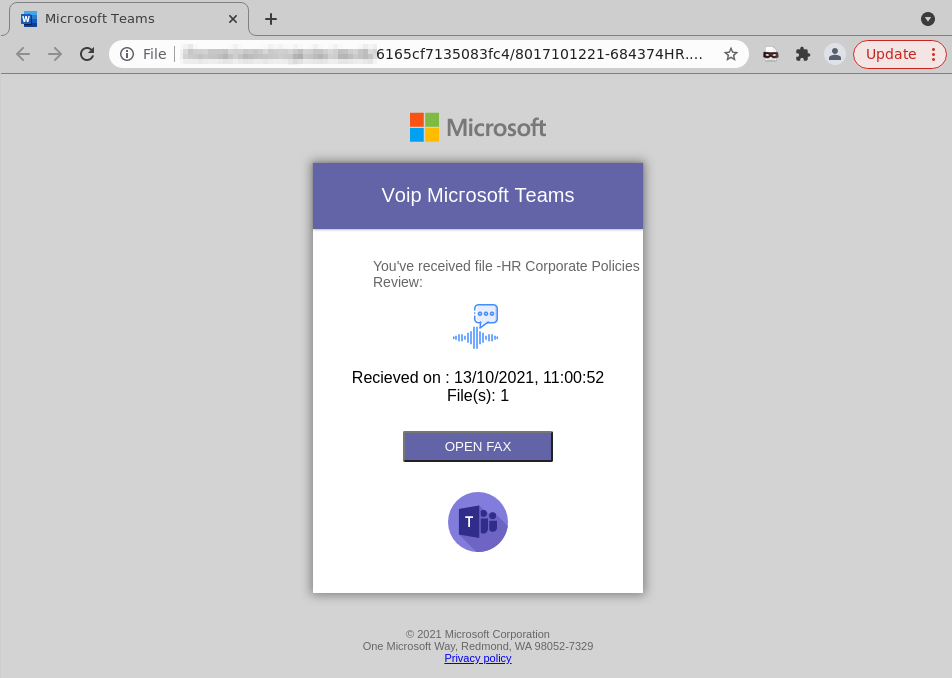
When the victim opens the attached document, they are taken to the following Microsoft Teams Voice Plan (VoIP) page, advising them of the file received from HR. It’s important to note here that Teams Voice Plan does not support Fax functionality, contrary to the screenshot below, which asks users to click on the ‘Open Fax’ button.
Users are then taken to the following Microsoft Word Document, which is a compromised SharePoint page, setting out the ‘Fierce Majeure’ policy. Cybercriminals have been especially sly in this instance by taking advantage of the vulnerabilities, including employee financial support and well-being, faced by many during this difficult global pandemic period.
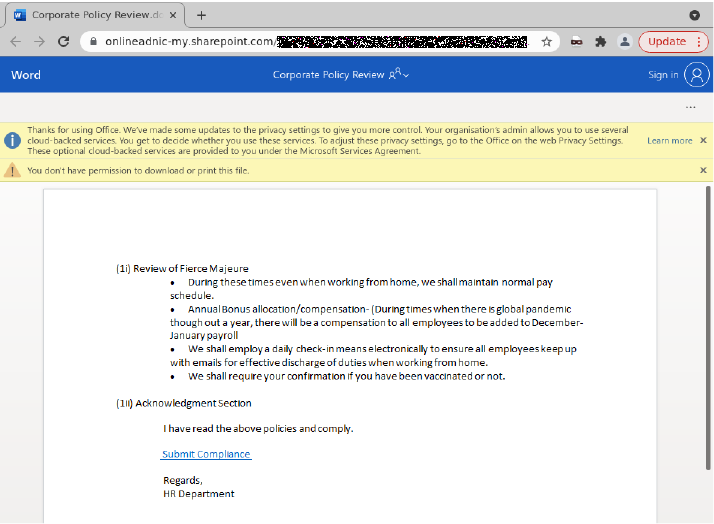
When users ‘Submit Compliance’ via the blue link in the document above, they are then taken to the following Microsoft login pages, asking for their email address and password. These pages are highly accurate imitations of the actual sign-in pages from Microsoft.
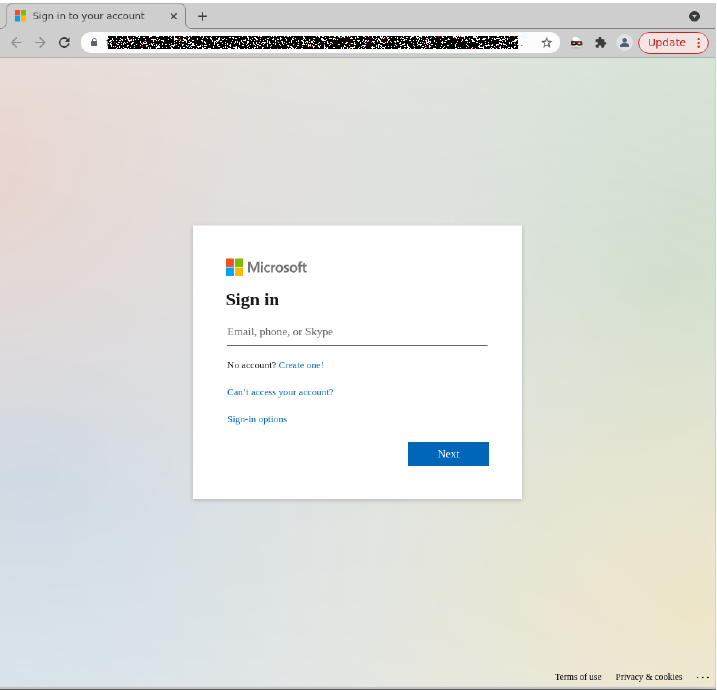
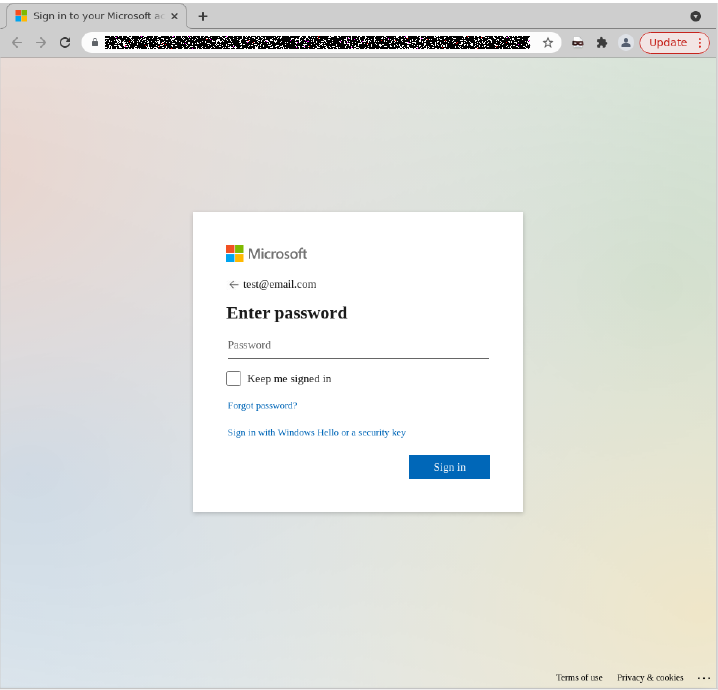
Once these credentials are entered and submitted, the attacker harvests them for later criminal activity and the user is met with an error saying ‘Invalid password or connection timed out please try again’ as highlighted in red font below. Again, Microsoft branding has been imitated with great detail.
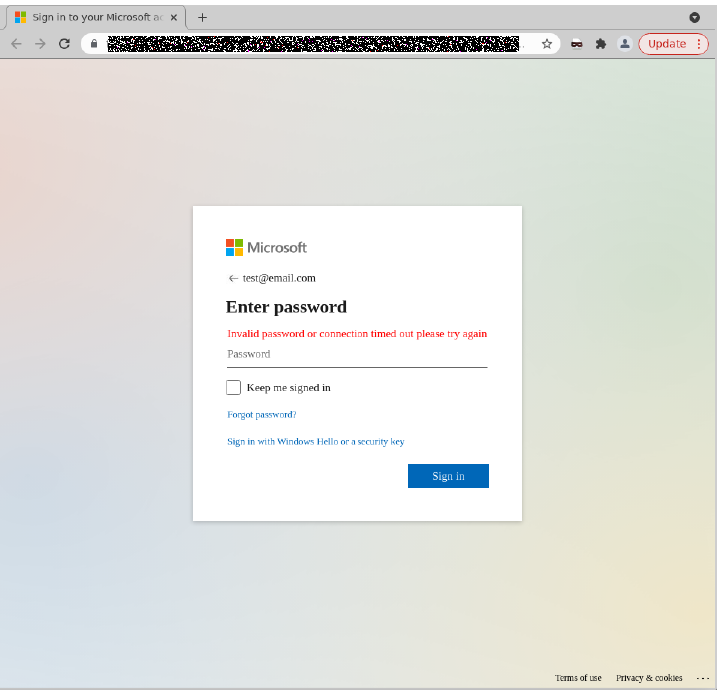
Scammers purposefully use tactics present in this phishing scam, such as copying the logos of Microsoft and SharePoint, and including SharePoint in the URL, to increase their chances of harvesting credentials that can be used to access sensitive information for further criminal activity.
In such cases, users are reminded of the importance of not downloading or clicking links for documents from unknown senders, despite the organisation they purport to be from. All attachments and/or links should only be accessed when users are certain about the credibility of the sender.
MailGuard urges all recipients of this email to delete it immediately without clicking on any links. Providing your personal details can result in your sensitive information being used for criminal activity.
MailGuard urges users not to click links or open attachments within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and/or
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to devastate your business is a cleverly worded email message that can steal sensitive user credentials or disrupt your business operations. If scammers can trick one person in your company into clicking on a malicious link or attachment, they can gain access to your data or inflict damage on your business.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's inboxes.
Stay up-to-date with MailGuard's latest blog posts by subscribing to free updates. Subscribe to weekly updates by clicking on the button below.







