Warning: International cyber criminals are targeting Australians again by recycling their fake ‘Australian Federal Police (AFP) infringement scam’ campaign.
Cyber criminals are holding victims’ data to ransom by tricking email recipients into downloading ransomware.
This campaign is almost identical to their previous attempts, in terms of the execution method.
Here is a sample of the email scam purporting to be from the AFP:
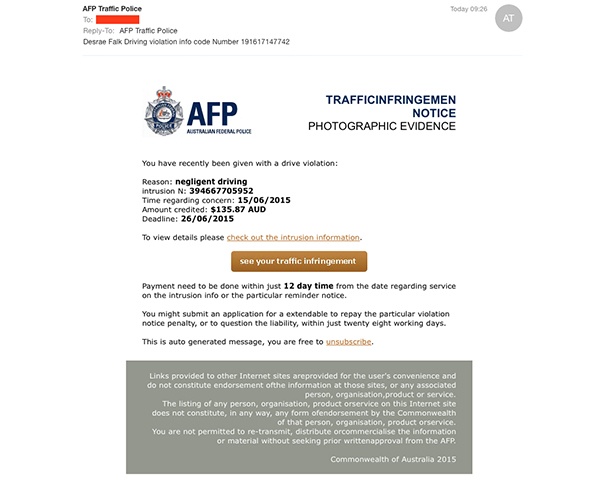
A huge warning sign for email recipients is the poor language used, such as:
‘You have recently been given with a drive violation’
‘…check out the intrusion information’
‘payment need to be done within just 12 days…’
It's the usual 'click here to view your traffic infringement' email, which then directs recipients to a fake AFP landing page. The website appears to be almost identical to the legitimate AFP site.
See images below showing the actions required in order to ‘download’ the supposed infringement notice. By following through, recipients are actually downloading a .zip file containing the now common Cryptolocker ransomware.
Criminals will follow through by locking down the victim’s files and demanding a ransom in order to decrypt the data.
Please warn all email users to be aware of this recent run of fake AFP Infringement emails, and be sure to educate team members on the typical warning signs:
1. The Australian Federal Police never send out traffic infringement notices via email
2. Always check the URL of the landing page you have been directed to, and you will notice (even in this example) it is not the correct domain of the purported organisation
3. Poor language in emails should be a warning to recipients that the email could be a scam
4. Never click links within an email that seems suspicious, and if in doubt check with your IT support team
5. If you are expecting an email from a legitimate company such as a bank or government organisation, go directly to the website through your browser and never click links from within an email.
MailGuard is at the forefront of finding and successfully blocking these types of fastbreak email scams containing malware or links to download malware. You can read more, as reported by the Australian Reseller News (ARN):
MailGuard Discovers Zero-Day Cryptor Variant Vulnerability
New Cryptolocker Variant Discovered Targeting Australians







