Watch out for this phishing email masquerading as a notification related to a new order.
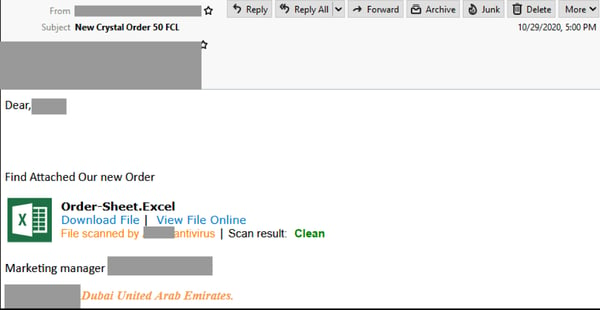
Sent from a compromised SendGrid account, the email is titled “new Crystal order 50 FCL”. It informs recipients that a new order is attached, and contains a link to what appears to be a Microsoft Excel file that has been scanned by an anti-virus service. The inclusion of the file’s scan result is likely an attempt to boost the email’s credibility and convince the recipient that it is safe to click on the link included in the email. The email ends with a sign off from a “marketing manager”.
Here’s what the email looks like:
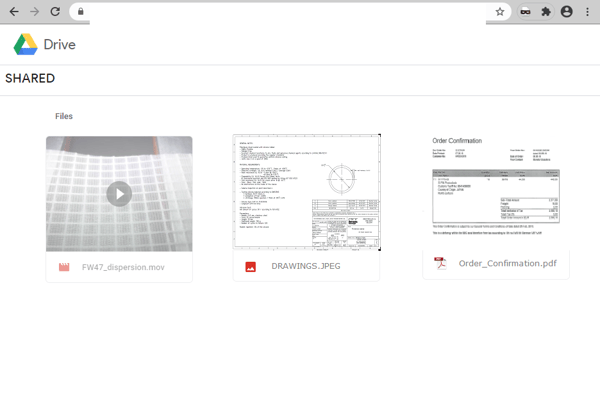
Unsuspecting recipients who click on the link are led to a page employing Google Drive branding. It includes images and links of multiple files in different formats (i.e. .PDF, .JPEG etc.). However, the domain used in the page’s URL doesn’t belong to either Google or Microsoft. This is actually a phishing page hosted on a compromised website that advertises real estate rental overseas.
Once any of these files are clicked, users are led to a login page that asks for their email address and password, as per the below:
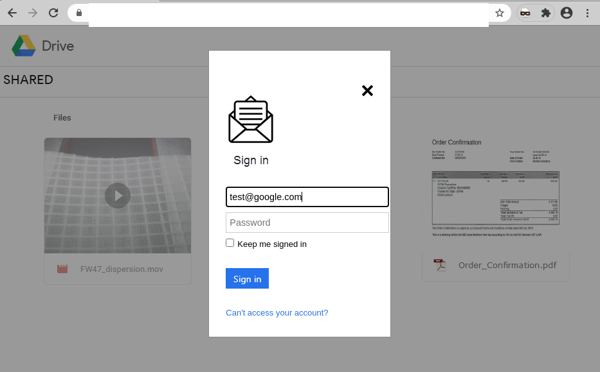
Once these credentials are entered and submitted, the attacker harvests them for later use, and the user is met with an error saying that password is invalid.
We advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Enquiries or notifications related to customer orders have long been used by cybercriminals to scam users. These are common business documents, frequently exchanged by professionals and habitually found in inboxes. Cybercriminals know this, and hope that in their urgency to respond to and act upon such notifications, users don’t pause to check for their legitimacy. In addition, scams that are initiated from compromised accounts (like in this case) are particularly dangerous because the emails are sent from a legitimate account, so they are not likely to be blocked by email security services. Cybercriminals often exploit these rules to trick users.
Several red flags are, however, present in this email scam that should alert users. These include the fact that the email contains several grammatical & formatting errors, and that the domain used in the URL of the phishing page belongs to a third party.
In such cases, users are reminded of the importance of not accepting/clicking on documents from unknown senders, despite the organisation they purport to be from. All attachments/links should only be accessed when users are certain about the credibility of their owners.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







