Machinery Trader, a website used to advertise new and used construction equipment, is the subject of a phishing email scam blocked by MailGuard.
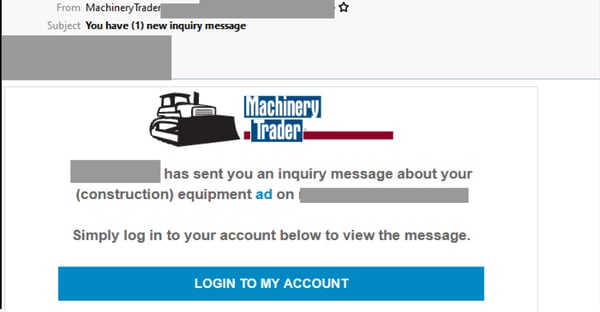
Titled “You have (1) new inquiry message”, the email purports to be a message alert for Machinery Trader and includes the company’s logo and branding. It informs recipients that they have received an “inquiry message” about their “(construction) equipment ad” and directs them to log into their account to view the message. A button is included for them to login to their account. The email actually originates from a compromised account for a small business based overseas.
Here’s what the email looks like:
Unsuspecting recipients who click on the link are led to a link shortening service, before being presented with a login page employing Machinery Trader’s logo, along with those of a couple of financing and insurance companies, as per below:
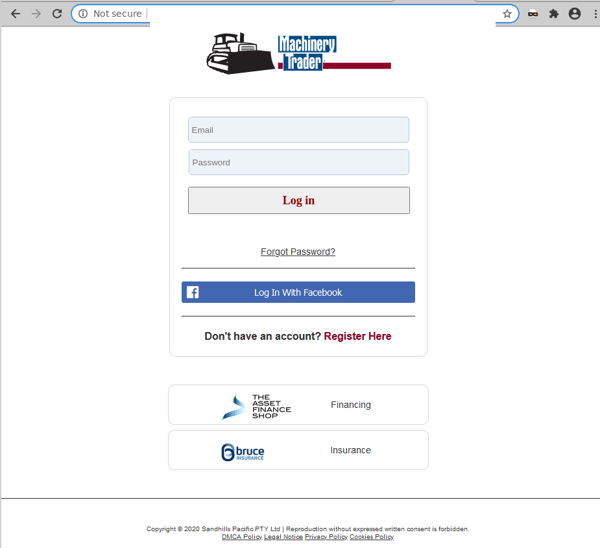
This is actually a phishing page that is hosted using an American small budget server hosting service. The phishing page and email are both utilizing free hosting services (Google and Imgur) to host branding pictures. In addition, rather than replicating the style of an actual login page from Machinery Trader, the majority of the page's background is actually an image, as seen below:
Once users “log into” their accounts by entering their email address and password, the attacker harvests the credentials for later use, and the user is met with an error saying that password is invalid.
We advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Machinery Trader is a platform designed specifically for buyers and sellers in the construction equipment market. Since this phishing email scam impersonates a relatively niche service, it is possible that this may be a phishing attack targeting a specific industry or group of similar industries.
Enquiries or auto-generated messages claiming to deliver new messages have long been used by cybercriminals to scam users. Cybercriminals know this, and hope that in their curiosity and urgency to respond to and act upon such notifications, users don’t pause to check for their legitimacy. In addition, scams that are initiated from compromised accounts (like in this case) are particularly dangerous because the emails are sent from a legitimate account, so they are not likely to be blocked by email security services. Cybercriminals often exploit these rules to trick users.
Several red flags are, however, present in this email scam that should alert users. These include the fact that the email doesn’t address the recipient directly, and that the domain used in the URL of the phishing page belongs to a third party.
In such cases, users are reminded of the importance of not accepting/clicking on messages from unknown senders, despite the organisation they purport to be from. All attachments/links should only be accessed when users are certain about the credibility of their owners.
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







