
To pay or not to pay? On the surface it may appear to be a relatively straightforward question, however, in reality, the answer is not so simple (particularly if we dig a little deeper). Amidst the plethora of information and advice offered by Governments, cybersecurity professionals and industry experts around the world, there is one thing that we seem to all agree upon: the answer to this critical question is not one-dimensional, whatever your viewpoint may be. Every incident is different because every company has its own unique set of challenges and priorities to consider.
In May we shared a post with our partners about ‘5 factors to consider’ when contemplating the question of whether to pay a ransom.
I empathise with any executive, IT or infosec professional that finds themselves in this predicament, balancing the advice of experts, regulators, and governments, against the interests of their employees, customers and shareholders. The needs and interests of the two groups may be diametrically opposed, and then add to the equation your own personal views about what you believe is morally and ethically correct, and you are left with a need for deep reflection (and plenty of paracetamol!). It is certainly not a clear cut or easy decision.
As partners, you know better than I, the breadth of factors that must be considered as the trusted experts charged with protecting your customers’ data and people.
I was keen to test the temperature of the room, with a poll that I posted to my network on LinkedIn. It posed the following question:
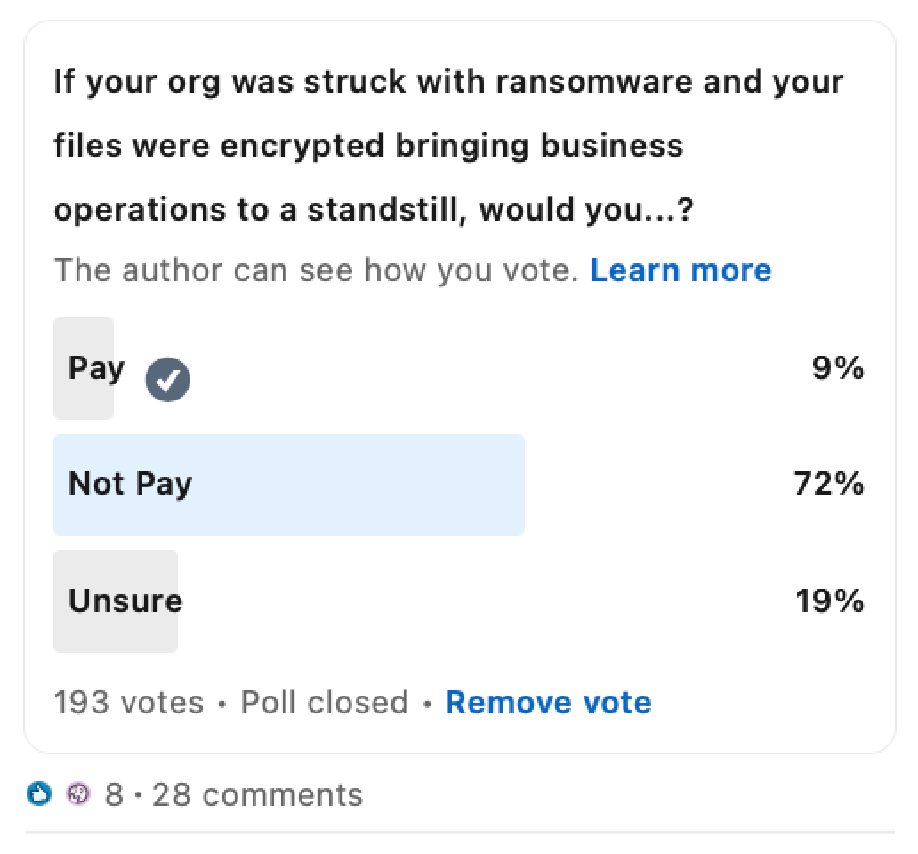
Firstly, I would like to thank everyone for contributing to the poll, and for their feedback. Almost 200 people responded, providing a divided yet articulate debate in the comments. Ransomware is clearly a major concern within the business community and the diversity of responses have illuminated the fact that it is a complex and challenging dilemma.
Here are some quick highlights
- 1 in 3 or ~30% would ‘Pay’ or were ‘Unsure’. Senior Executives and Business Leaders tended to be more highly represented in this group, and I can only infer that they were considering the direct business stresses that a ransomware disruption would place on their business, as the basis for their answer.
- Technology and IT/InfoSec Professionals were otherwise more highly represented in the other group, and more inclined to vote ‘Don’t Pay’ (72%). This of course is aligned with the best practice advice of regulators, professional and industry bodies.
- The comments were illuminating, and most security professionals were pointing to the importance of a reliable back up, and business continuity plans, to mitigate any disruptions.
- Other factors to consider were the reliability or trust that you place in those that are holding the encryption key. Do you trust the criminals behind the attack to give you access to your data intact once payment is made? Has the data been compromised or exfiltrated already? How can you be certain? How do you know that there aren’t backdoors?
- Some pointed the finger at cyber insurance, arguing that insurers have a role to play in demanding that companies have better processes in place to mitigate the risk of compromise and data loss.
- And yet others took a contrary and more pragmatic view, suggesting that the decision is a rational one like any other business problem. Assess the time and cost impacts or paying versus not paying, and then act in the best interest of the company and your shareholders.
- Finally, there were those that called out the legal and reputational risks that a company is confronted with if they do in fact choose to pay.
A diverse array of opinions
I thoroughly enjoyed reading the comments, of which there were many in all the varied shades of grey:
“Hard question, I would initially say don't pay as it gives them more incentive to move on and do it again...”
“Treat it like every other decision at work. Do the math, how much the ransom is versus how much it will cost in lost business...”
“Missed a few related to post payment, (like) the reputational damage of paying, the potential legal fights depending on where you operate and the laws for funding certain groups...”
“Of, course your risk assessment needs to account for the fact that the ransomer has no need to help you once they get their bitcoins. What are the chances they act 'honourably', really?”
“If your DR (Disaster recovery) & BC (Business continuity) plans, and your technology, get you up and running within a few hours or less, then I certainly would not pay...”
“That’s what DR (disaster recovery) and business continuity plans, provisions and actions are for. Ransomware should never impact a business that it brings to a standstill. If all the above is in place and working makes this question mute.”
And others were certainly more unequivocal:
“If you need to pay, then you’ve failed...”
“Not pay, definitely not. No way!”
The right answer?
While the majority view is certainly “Don’t pay”, and that is absolutely the advice of regulators, I cannot help thinking that it just isn’t quite that simple. Many of the biggest and most sophisticated companies in the world have been impacted by cyber incidents including ransomware attacks, so to dismiss the question as irrelevant based on whether the company has taken the necessary steps and precautions is ignoring the fact that those same companies are armed with large cybersecurity budgets and armies of IT & security professionals. They would almost certainly have their own DR & BC plans in place. I would even hazard a guess that prior to being impacted, those inside may have held the same emphatic views about not paying. But when the clock is ticking and you’re under pressure to get the business back online, to resume services to customers and to reassure shareholders that revenues have been restored, then the picture must look very different. It’s easy for the debate to rage on social media, but the reality is much harsher. None of us want to find ourselves or our customers in that position.
Regardless, we can all agree that ransomware is something we do not wish to experience. I commend governments around the world for being more proactive in the fight against the groups responsible. We heard earlier this year that the U.S. Department of Justice had formed a taskforce to tackle ransomware, and under the ‘Rewards for Justice’ program that monetary rewards are now being offered for information leading to the prosecution of those responsible for attacks on critical infrastructure. And in Australia, the AFP are now leading Operation Orcus, with a similar focus to stamp down on ransomware. But it is safe to say that this is a problem that is not going away any time soon, and one that is of grave concern from a political and organisational standpoint.
Keeping businesses protected
Prevention is always better than a cure, and the best defence is to encourage businesses to proactively boost their company’s cyber resilience levels to avoid being hit by ransomware in the first place. The fact that a staggering 94% of malware attacks are delivered by email, makes email an extremely important vector for businesses to fortify.
No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
Being hit by a ransomware attack can cause businesses significant financial losses and a hit to their reputation, especially following a tough pandemic-ridden year which resulted in many businesses struggling to keep the lights on. By taking time to assess the situation and exploring all recovery options at hand, your customers can make the right decisions and successfully navigate the ransomware payout dilemma.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282 2
UK partners call 0 800 404 8993
We’re on Facebook, Twitter and LinkedIn.






