What would you do if you received an email claiming to boost your “immunity so you’re less likely to catch the Coronavirus”?
You’ll probably click on it, especially if the email looked legitimate enough. The worldwide pandemic of coronavirus (officially known as COVID-19) has gripped all of us. It’s trending everywhere – from news publications to social channels (the hashtag #COVID19 is currently trending on Twitter with 387,000 tweets & counting). Global fears about the spread of the virus, combined with a lack of clarity about how to prevent it have made the topic irresistible – and cybercriminals have noticed too.
Real examples of cyberattacks exploiting fears around coronavirus
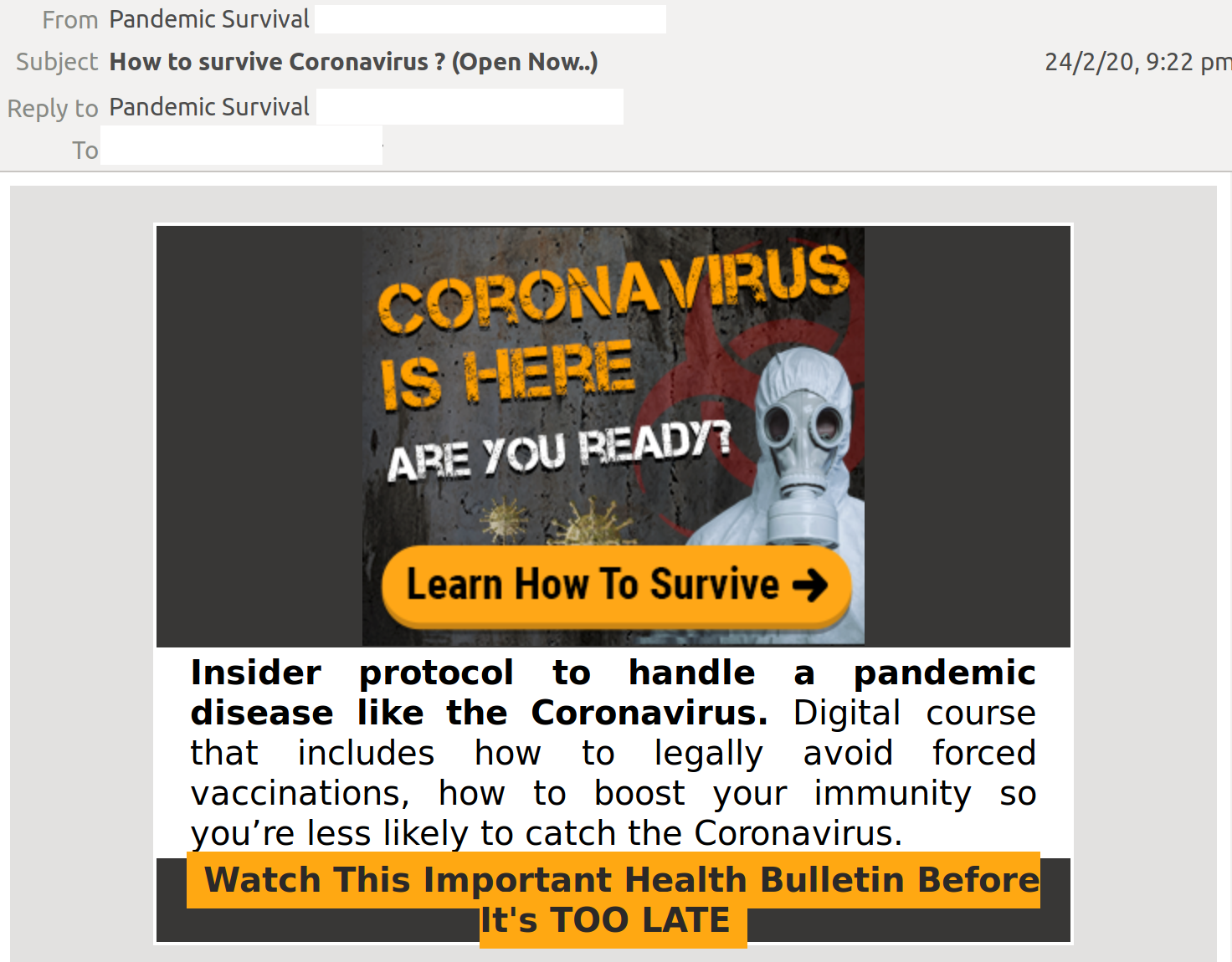
At MailGuard, we have intercepted several email scams centered around coronavirus, including the email about boosting your “immunity” cited above:
Here’s another one around the sale of “unlimited” face masks:
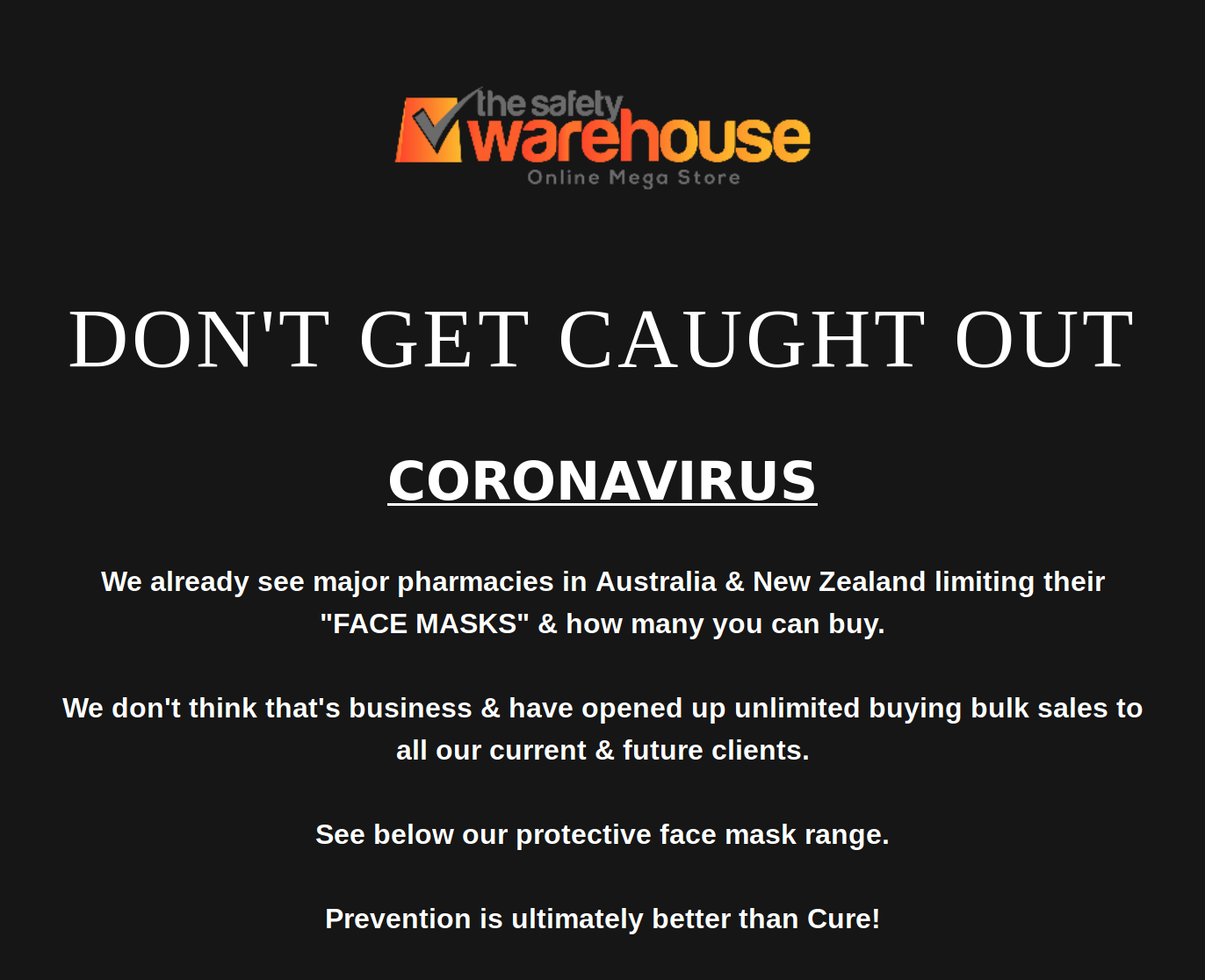
The techniques these coronavirus-themed scams are employing to trick users are similar to any other type of email scams. In one scam that we intercepted, the email claimed to contain a list of ‘pictures, countries, names and companies affected’ by coronavirus. This list was actually a malicious payload designed to infect the system of any unsuspecting recipient who opened it. The email was supposedly sent from a medical practitioner called “Dr. Li Wei”. This is a classic trick employed by cybercriminals – impersonating senior professionals is likely to inspire false trust and suggests the email is sent from a credible authority.
But cybercriminals aren’t just stopping at impersonating random individuals. They’re also increasingly spoofing worldwide organisations that are directly involved with the virus. Kaspersky Labs and Sophos have found phishing emails claiming to be from the Centre for Disease Control and Prevention and the World Health Organization that attempt to steal email credentials and other information. Additionally, researchers with IBM X-Force reported that cybercriminals are spreading the Emotet trojan via emails purporting to be from a disability welfare service provider in Japan.
As IT consultants & strategic advisors, the responsibility we hold in guiding our clients to help them defend their people, data and assets is crucial in critical times like these. These scams are pervasive, leveraging normal human psychology and emotions. Any company, even one with the most experienced cybersecurity team and the best tech defences can fall victim to these scams. All it takes is one of their employees to get tricked.
Share the below information & tips with your clients and use these to begin a conversation around improving cyber resilience in light of these coronavirus-themed cyberattacks.
Why businesses need to rethink their defence strategies
Most coronavirus-themed email scams are using a form of psychological manipulation, using fear to warp minds and as a consequence, cripple systems. And fear is a very powerful emotion, especially one that is centered around a rapidly spreading, fatal and somewhat unknown global health emergency that might affect users and/or their loved ones. Cybercriminals can easily tap into users’ fear and/or paranoia and distract them from checking the legitimacy of the emails they’re receiving.
Furthermore, the ripple effect from a coronavirus-themed attack gives cybercriminals multiple opportunities to trick businesses. One example is the disruption posed to supply chains of businesses around the world. China is “the workshop of the world” and the disruption caused by the widespread presence of the virus in the country is likely to disrupt business operations worldwide. It won’t be surprising for a company in Australia, for example, to receive an email about a delayed FedEx shipment from China – an email that could easily be a malicious one. Cybercriminals are well aware of these disruptions, and likely won’t hesitate to launch cyberattacks that exploit them.
How we can protect businesses from these attacks
Luckily, this practice of launching cyberattacks that involve natural disasters or other critical events that grab national or International headlines isn’t anything new. Cybercriminals have long employed these tactics to take advantage of users’ desire to keep up to date with new information, or to manipulate their emotions. Sometimes cybercriminals even use positive events, like Greta Thunberg's climate change movement, to spread malware.
We’ve seen that in these situations, a strong cybersecurity culture, and awareness & education around being able to spot email scams become your best bet. Here are a few important tips:
As a precaution, avoid clicking links in emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include. Most of the coronavirus-themed emails we have intercepted (including examples mentioned above) didn’t address the recipient directly;
- Are from businesses you’re not expecting to hear from;
- Ask you to download any files and,
- Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from.
We expect that scams centred around coronavirus will continue and trigger several malicious types of cyberattacks that use the deadly virus as bait – making it more important for businesses to be proactive in training employees how to spot these attacks. It also helps to be on the lookout for directives from credible organisations, like the World Health Organization that has listed specific tips on how to spot malicious coronavirus-themed emails that purport to be from the organization.
Ongoing education is the key to enlightening your staff on the ground. This may be in the form of workshops, meetings, guest speakers, cross-functional teams, tests, and plenty of resources available on your intranet, including weekly cybersecurity updates. You can refer to external resources as well. MailGuard’s blog, for example, is regularly updated with the latest email threats that we see popping up, along with thought leadership articles on the current cyber landscape and how to navigate it.
Take a multi-layered approach
Just keeping your antivirus software up to date is not going to cut it, and likewise, giving your employees comprehensive knowledge on being cyber-savvy without having strong technological defences in place won’t work either.
Experts recommend that companies take a strategic, multi-layered approach when it comes to cybersecurity – especially when defending against targeted or ‘themed’ cyberattacks. It’s sometimes referred to as a ‘defence in depth’ approach, designed to defend a system against attacks using several different methods and tactics, in the event that if one fails, the others will stop the threat.
Putting this in the context of email security, you may already have native security from your email hosting provider, like Google or Microsoft, but it’s key to remember that no one vendor can stop all attacks. It’s also prudent to employ an additional layer of cloud email security with an email security specialist like MailGuard.
Other methods you can implement include multi-factor authentication (MFA), limited access to systems including regular account maintenance, a strong firewall, website blocking, and encryption of critical data.
What strategies are you implementing to defend your business from coronavirus-themed cyberattacks? Share your thoughts and recommendations with us at the details below.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us what your customers need so we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 2822
UK partners call 0 800 404 8993
We’re on Facebook, Twitter and LinkedIn.






