
In the final weeks of 2020, news of the SolarWinds hack broke – a cyber-attack that has been dubbed as “the Pearl Harbor of American IT”.
To recap, SolarWinds, a software company with thousands of customers throughout the world, including government agencies and Fortune 500 companies, was hacked after attackers breached its networks and accessed the company’s proprietary IT software, Orion. This involved inserting malware into legitimate updates for the Orion software, that allowed attackers remote access into the victim’s environments. Companies that applied these Orion updates also unwittingly installed the malware on their own systems. Reports state cybercriminals used the SolarWinds' hacked program to infiltrate at least 18,000 government and private networks.
The hack brought a dangerous attack vector to the fore - supply chain attacks, AKA attacks wherein threat actors exploit vulnerabilities in an organisation in the supply chain of others, in order to breach the upstream target(s). These attacks shine a spotlight on the risks organisations face as they accelerate their digital transformation, increase their reliance on cloud technologies, and become more interconnected with networks in their ecosystem (including those of their consumers, partners, vendors and suppliers).
Explaining how supply chain attacks work, Microsoft’s Joram Borenstein, General Manager, Cybersecurity Solutions Group, and Cristin Goodwin, Assistant General Counsel at Microsoft, say that “throughout the supply chain, hackers look for weaknesses that they can exploit. Hardware, software, people, processes, vendors—all of it is fair game. At its core, attackers are looking to break trust mechanisms, including the trust that businesses naturally have for their suppliers. Hackers hide their bad intentions behind the shield of trust a supplier has built with their customers over time and look for the weakest, most vulnerable place to gain entry, so they can do their worst.”
According to the US National Institute of Standards and Technology (NIST), cyber supply chain risks include:
- Insertion of counterfeits.
- Unauthorised production of components.
- Tampering with production parts and processes.
- Theft of components.
- Insertion of malicious hardware and software, and
- Poor manufacturing and development practices that compromise quality.
While Microsoft President Brad Smith has called it the "largest and most sophisticated attack the world has ever seen", the SolarWinds hack isn’t the first supply chain attack in recent times. Just a few months earlier, cloud software provider Blackbaud, which provides services for many corporations, charitable foundations, education institutions and healthcare entities, was hit by a ransomware attack. After the company’s self-hosted environment was infected with malware, its cybersecurity team was able to stop the attackers from encrypting the entire network. However, the hackers did manage to steal a subset of data prior to deploying the ransomware payload, including data belonging to Blackbaud’s customers, resulting in millions of sensitive student, patient, and donor data records being compromised.
There are, of course, many other examples of notable supply chain attacks (including NotPetya in 2017), but I highlight these two examples not simply because they are among the biggest cyber-attacks that occurred as recently as last year, but because they act as painful reminders of the breadth of supply chain vulnerability and of the catastrophic and far-ranging consequences supply chain attacks can cause. The fact that even well-established entities like U.S. federal agencies and Fortune 500 organisations were disrupted is a wake-up call that these attacks can impact any organisation, at any time.
Why are supply chain attacks a major concern in 2021?
With remote working continuing to be a key business trend in 2021, these attacks are continuing to amplify, making it integral for us to remind our customers of the dangers posed by these attacks and the need to take quick action in order to stay protected.
The reason is simple. COVID-19 has jolted organisations around the world to embrace fast-tracked cloud migrations and digital transformations that can enable their workforces to work remotely. This transition seemingly occurred overnight, and it has amplified vulnerabilities, like the use of unsecured networks and devices. Plus, as many supply chains sub-contract, company data is being handled by secondary, tertiary, and even fourth-degree entities. It’s easier to exploit disparate—yet interconnected—networks – and cybercriminals know this.
Research conducted recently found that organisations have an average of 1,013 vendors in their supplier ecosystem – and that 82% of organisations have suffered a data breach in the past 12 months due to cybersecurity weakness in the supply chain.
To make things worse, a third of organisations surveyed in the study said that they have little to no indication when hackers hack into their supply chain, meaning that they often do not find out that they've been the victim of an incident until it's too late.
The World Economic Forum (WEF) succinctly summarised why the current climate is a catalyst for supply chain attacks, citing them as one of the five main cybersecurity challenges that global leaders should consider and tackle in 2021:
“Organisations operate in an ecosystem that is likely more extensive and less certain than many may recognise. Connected devices are expected to reach 27 billion by 2021 globally, driven by trends such as the rise of 5G, the internet of things and smart systems. In addition, the boom in remote work that began with the pandemic is expected to continue for many. The concentration of a few technology providers globally provides many entry points for cyber criminals throughout the digital supply chain.”
But it’s not just the fact that it’s now easier for cybercriminals to launch successful supply chain attacks that is concerning. What’s more worrying is that these attacks are exploiting vulnerabilities in the supply chain at a time when businesses are more dependent than ever on the interconnected relationships within their intricate ecosystem of consumers, partners, vendors, and suppliers.
A case that comes to mind is when IBM uncovered a global email phishing campaign targeting organisations associated with a COVID-19 cold chain. The cold chain is a component of the vaccine supply chain that ensures the safe preservation of vaccines in temperature-controlled environments during their storage and transportation. The fraudulent emails impersonated a business executive at a credible cold-chain supply company. Disguised as this employee, the threat actor sent phishing emails to organisations believed to be providers of material support to meet transportation needs within the COVID-19 cold chain. Here’s a screenshot of the email:
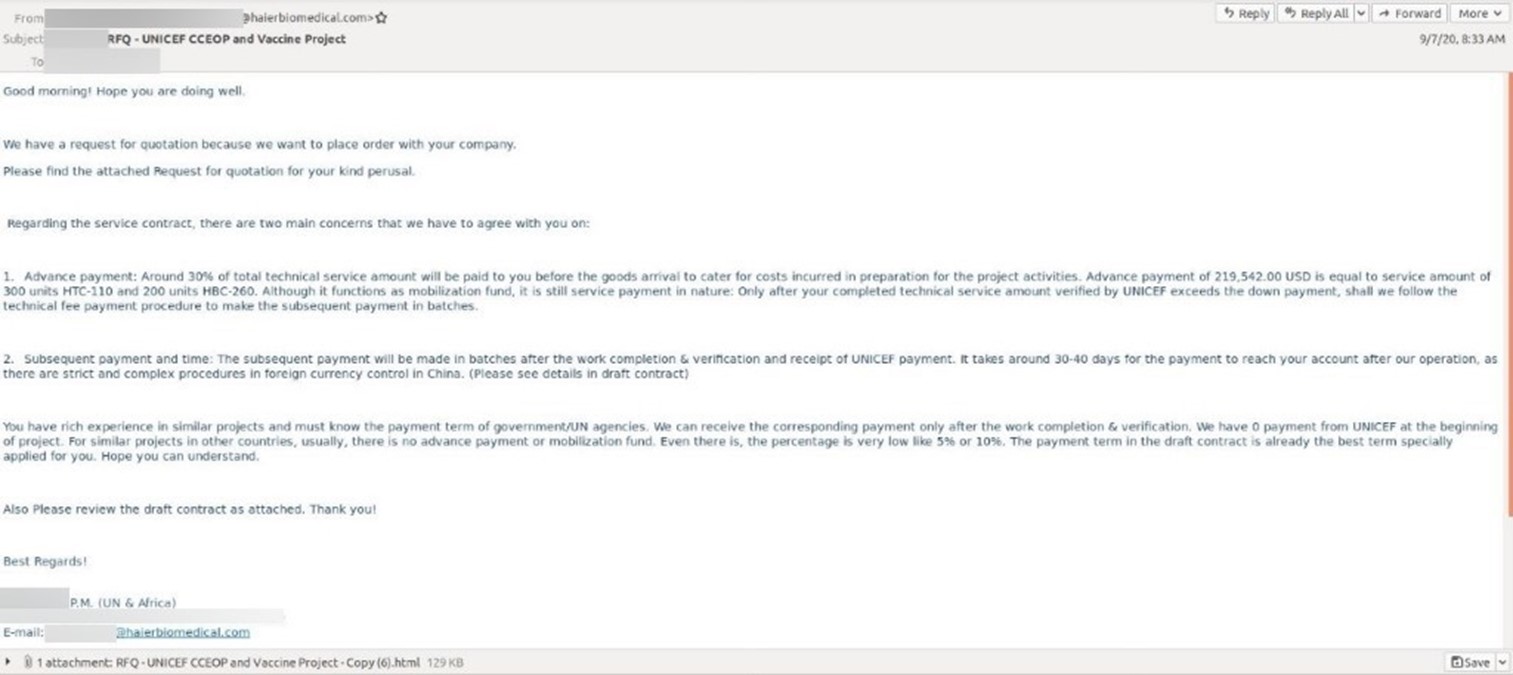
Source Image: IBM
“We assess that the purpose of this campaign may have been to harvest credentials to gain future unauthorised access,” IBM researchers wrote in a report. “From there, the adversary could gain insight into internal communications, as well as the process, methods and plans to distribute a COVID-19 vaccine.
The attack reveals how malicious emails are being used to fraudulently access data related to the development of a COVID-19 vaccine – data that is understandably of vital importance in a world ravaged by an ongoing pandemic. In compromising the safety of such key information, cybercriminals are capitalising on the interconnected network of entities involved in the development and distribution of the vaccine, cruelly attempting to exploit any security vulnerabilities in that network – unfortunately at a time when a successful roll-out of a vaccine is needed the most.
As you know, malicious emails remain one of the most prolific ways fraudsters infiltrate networks in a supply chain. My team regularly intercepts fraudulent emails impersonating vital businesses involved in the supply chain, including parcel delivery, financial and banking services. These organisations are custodians of sensitive data, ranging from customer information through to confidential passwords, systems access, and valuable financial information - exactly what cybercriminals exploit to gain access to more lucrative companies.
Staying protected
Supply chain attacks exploit trust mechanisms within networks. The threat is all too real, and the stakes are too high. Since we’re all part of an interdependent and fragile ecosystem, what negatively impacts one company is likely to have detrimental consequences on other businesses too, a ripple effect if you will. If our customers are not prepared to deal with such cyber-attacks (either directly or indirectly), the consequences will be catastrophic.
Nine out of 10 cyber-attacks start with an email, even when most businesses have an email security solution in place. No one vendor can stop all threats, so it’s crucial to remind customers that if they are using Microsoft 365 or G Suite, they should also have a third-party email security specialist in place to mitigate their risk. For example, using a third-party cloud email solution like MailGuard.
As we continue solidifying our customers’ cybersecurity strategies this year, let’s recognise the recent hacks on SolarWinds and Blackbaud as reminders of the dangers posed by supply chain attacks, and use them in conversations with decision makers to help their businesses stay protected in this period of amplified risk.
What are you doing to help your clients mitigate the risks of supply chain attacks? Write your comments below.
Talk to us
MailGuard's partner blog is a forum to share information and we want it to be a dialogue. Reach out to us and tell us how we can serve you better. You can connect with us on social media or call us and speak to one of our consultants.
Australian partners, please call us on 1300 30 65 10
US partners call 1888 848 282![]() 2
2
UK partners call 0 800 404![]() 8993
8993
We’re on Facebook, Twitter and LinkedIn.






