MailGuard have recently identified and successfully blocked a new JavaScript malware email scam.
Unlike previous variations we have identified, this email scam is broad and does not target users of any particular service or company. It preys on human curiosity, exploiting the greatest security weakness many businesses have – people.
Here are screenshots of two variations to be aware of:
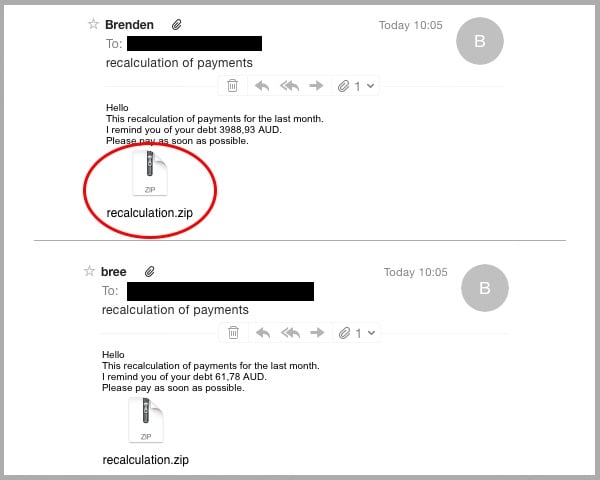
As you can see in the example emails above, the subject is ‘Recalculation of Payments’ whilst the purported sender is randomly generated.
The content of the email is consistent, besides the alleged ‘debt’ dollar-figure which is dynamic. This is a technique commonly used to bypass email content scanners and distribute thousands of unique variations.
The sender encourages the target to download the ‘recalculation.zip’ attachment to view more details of their debt.
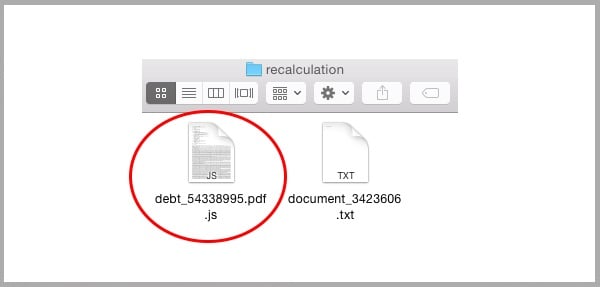
Upon extracting the ZIP file, the user is exposed to a .txt and ‘.pdf.js’ file. The .txt is non-malicious.
The ‘.pdf.js’, however, is a heavily obfuscated, Base64 encoded JavaScript file, comparable to the ‘.doc.js’ variation we previously identified.
Similar to the previous variation, unless the user has elected to show known file type extensions, this file will appear as a PDF file type and further convince the user that it is legitimate.
Here’s where things get interesting…
At the time of report, MailGuard can confirm none of the top antivirus vendors were blocking this attachment.
The original JavaScript file appears legitimate to antivirus security engines considering the code is scrambled and dynamic.
Upon being executed by Windows Script Host, this file is designed to build a number of .js scripts, further confusing antivirus defences with each unique variation it generates.
Finally, a Trojan virus is downloaded from a remote location.
Trojan malware is installed locally, and can be employed to:
- Use the machine as part of a botnet.
- Steal login credentials and other sensitive data like trade secrets and payment information.
- Install ransomware like CryptoLocker. This encrypts your files with a private key that cannot be reverse engineered. The victim is forced to pay the ransom to receive the decryption key and regain access to the files.
Warning signs to help identify this email as a scam:
- The informal, impersonal greeting.
- Grammatical errors within the body, “I remind you of your debt”.
- The victim is asked to download an attachment that they were not expecting to receive from an unknown sender.
If you receive one of these emails, or one of the many variations that are currently circulating, do not open any attachments.
Remember, educating staff and employing cloud-based email and web filtering is your first and best line of defence. Compliment this multilayered defence with updated on premise antivirus, anti-malware and anti-spyware solutions. This will go a long way to mitigating the risk from a wide range of email scams.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







