MailGuard have recently identified and blocked a large scale run of email spam containing Word files infected by macro malware.
We can confirm at the time of report, no major antivirus vendors were detecting these documents as containing a macro virus. Whilst macro malware scams have existed for years, we have identified a large increase in their distribution recently.
Here are screenshots of some of the unique email variations we have observed:
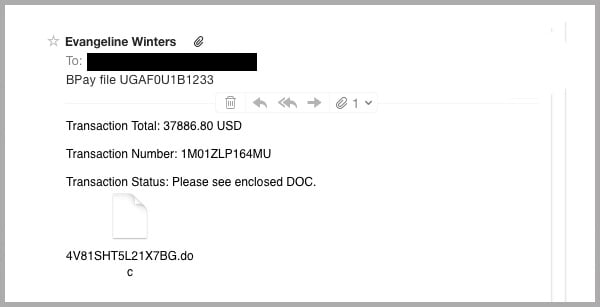
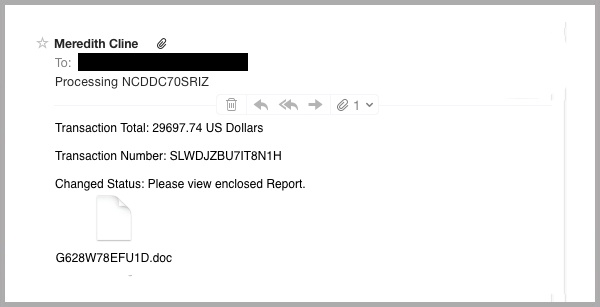
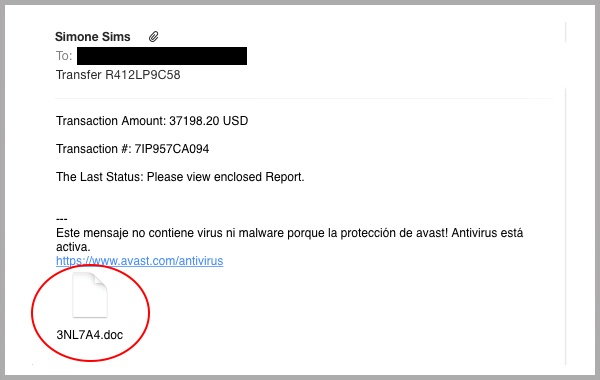
As you can see in the examples above, the sender has used a common email template to craft this mass spam attack.
This template uses a syntax content spinner to dynamically generate content and distribute thousands of unique variations; bypassing content scanners.
The email encourages the recipient to view the attached Word ‘.doc’ file.
The macro embedded in the Word document contains a malicious Visual Basic macro - we’ve highlighted this to show you the hidden code in the image below. The string is obfuscated and encoded using Base64 – when decoded, it creates a Trojan dropper.
Antivirus layers are often bypassed by macro code within Word documents; it is more difficult to detect a virus within VBA script than a malicious attachment.
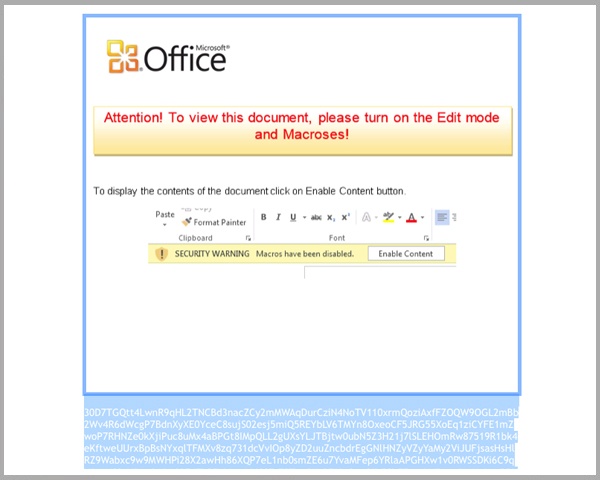
The victim is encouraged to ‘enable content’ to activate the macro.
The dropper is then executed to download malware from a remote location, without their knowledge.
The .DOC is a common file type – for many recipients it isn’t uncommon to open dozens of .doc attachments daily, nor does it raise any alarms.
Recipients in certain professions, such as accountants, analysts and auditors, as well as software engineers frequently receive attachments containing word macros. These departments use macro process commands to perform repetitive tasks – they can be streamlined to be completed more quickly and accurately with automation.
They can also be used maliciously – we recently reported on a scam in which Human Resources was the target of macro malware scam orchestrated by cybercriminals using fake job applications as a means to fool recipients.
As a default in recent versions of Microsoft Word, macros are disabled to limit the security threat. This campaign employs social engineering to coerce the victim into enabling the macro; activating the Trojan downloader.
What’s the damage? What does the dropper download?
Once the obfuscated code is unscrambled, the dropper downloads ‘.exe’ malware from a remote location. At this point, it really is the luck of the draw. Cybercriminals can program these exploits to download virtually anything, including:
- Trojans that steal login credentials,
- Crypto ransomware - This encrypts your files with a private key that cannot be reverse engineered. The victim is forced to pay the ransom to receive the decryption key and regain access to the files. Ransomware is growing rapidly, even the FBI suggests it’s easier to “just pay” the ransom. In reality, unless you can restore from a backup or don’t value the encrypted files, your only solution to ransomware removal is to pay up; without a guarantee of actually receiving the key!
Warn your network about the Word Macro Malware virus (Click to Tweet!)
Here’s how you can defend yourself against the macro malware virus:
- As mentioned above, Microsoft Word has disabled VBA macros by default in newer editions. Don’t fall for the attempt to convince you into enabling macros for an unexpected attachment.
- Exercise vigilance and always be suspicious of emails from unknown/unexpected sources.
If you receive one of these emails, or one of the many variations that are currently circulating, do not open any attachments or links within the email.
Educating staff and employing cloud-based email and web filtering is your first and best line of defence. Compliment this multilayered defence with updated on premise antivirus, anti-malware and anti-spyware solutions. This will go a long way to mitigating the risk from a wide range of email scams.
Microsoft is a registered trademark or trademark of Microsoft Corporation in the United States and/or other countries.
Keep up to date with email scams affecting your business by subscribing to MailGuard’s weekly update.







