A recent email phishing run purporting to be from PayPal is targeting PayPal users with an identity theft scam. If successful, the victim is vulnerable to having their PayPal account hijacked, their credit card credentials used to make fraudulent purchases and their identity stolen.
MailGuard have identified and successfully blocked this spam email attack through both cloud email and web services.
Here is a screenshot of the type of email to watch out for:
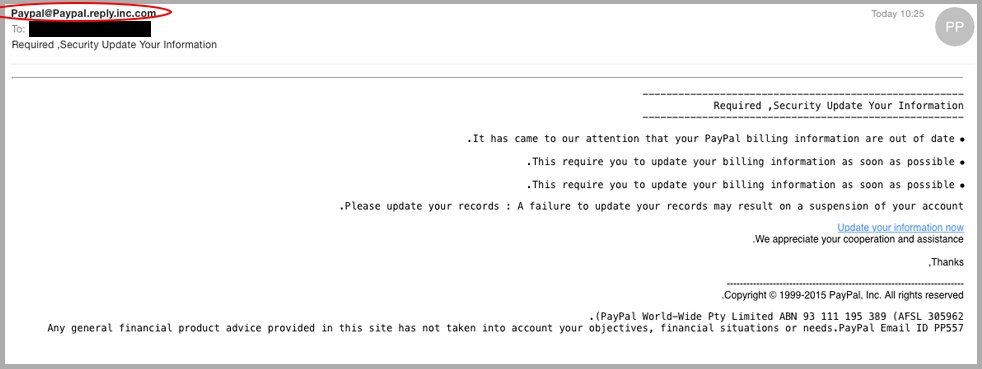
As you can see in the example above, the email appears to originate from an official PayPal sender address, ‘Paypal@paypal.reply.inc.com’. This particular scam has reversed the direction of its text in its attempt to bypass email content scanners.
This particular variation provides instruction to the recipient to update their billing information which is now out of date, or risk suspension of their account.
The email itself is poorly written, and this is an obvious giveaway of its inauthenticity.
Upon clicking the ‘update your information now’ hyperlink, the recipient is directed to the following landing page.
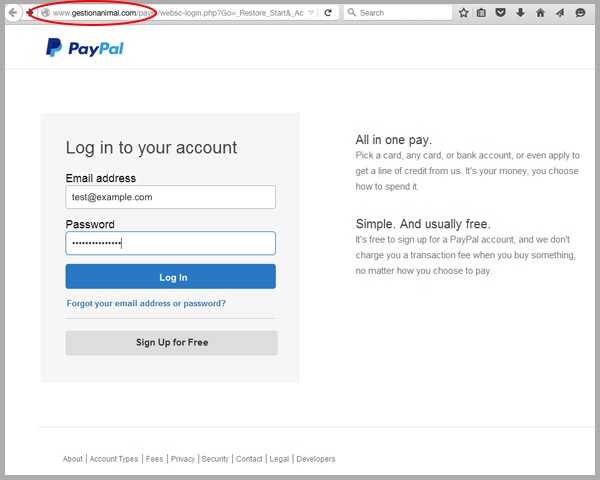
This is an exact replica of the official PayPal login page – besides the unofficial URL highlighted in the website address field, ‘www.gestionanimal.com’ above.
Upon entering their details in the above landing page, the user is directed to the following landing page.
At this point, the user has left their account vulnerable to infiltration handing their PayPal login credentials over to the cybercriminal.
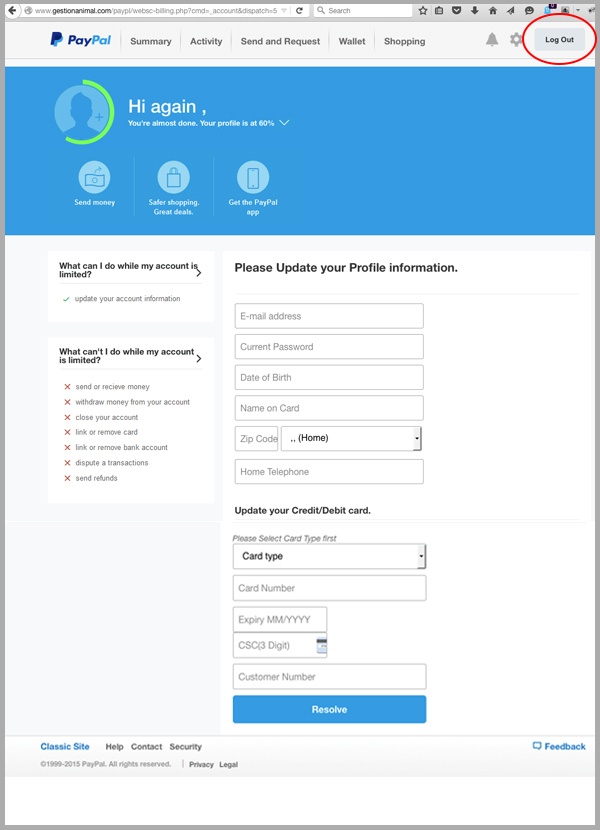
The second part of this scam, requires the user to enter more personal details. The information in the left hand sidebar reinforces the necessity of verifying the information requested in the form to regain privileges for their account.
As you can see in the top right corner, the form further convinces the victim with a ‘log out’ option.
Upon submitting the form, the user is directed to the final part of this elaborate scam. The victim has provided personal information that can be sold to telemarketers, as well as credit card details which can be used by the cyber criminals that orchestrated this attack.
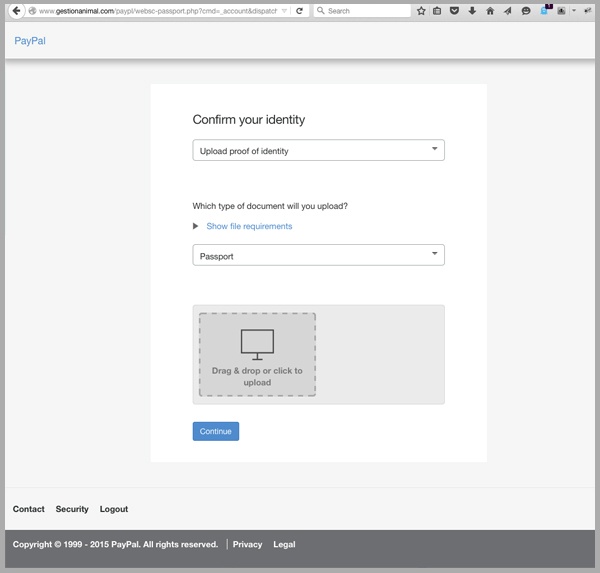
The user is required to upload a final document of authenticity to complete the verification process.
Cyber criminals specifically rely upon the brand of well-known organisations because they know that people have a sense of familiarity and trust when they receive email correspondence from these companies. For this reason, email recipients are more likely to fall for the scam and share their personal information or passwords which criminals can then use for their own financial gain.
As a precaution, we urge you to delete emails that:
- Appear to be from a legitimate company and are not addressed to you by name or are written in poor English.
- Require you to click a link in the email body to verify your identity.
- Have an unusual request that you would not expect to receive from the official purported sender.
Educating staff and employing cloud-based email and web filtering is your first and best line of defence. Compliment this multilayered defence with on premise antivirus, anti-malware and anti-spyware solutions. This will go a long way to mitigating the risk from a wide range of email scams.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







