MailGuard have successfully identified and blocked an email malware scam circulated by cyber criminals impersonating DHL today.
This outbreak has been widely distributed alerting the email recipient of a package which has been supposedly dispatched to be delivered to them.
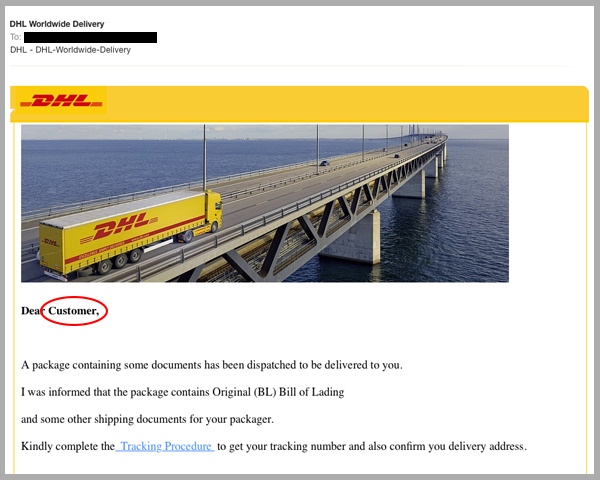
As you can see in the screenshot above, this email appears to originate from DHL. It requests the recipient “complete the tracking procedure” in order to receive their tracking number and confirm their delivery address.
Upon clicking the ‘tracking procedure’ hyperlink, the victim is directed to a landing page which immediately prompts them to download a ‘.COM’ file.
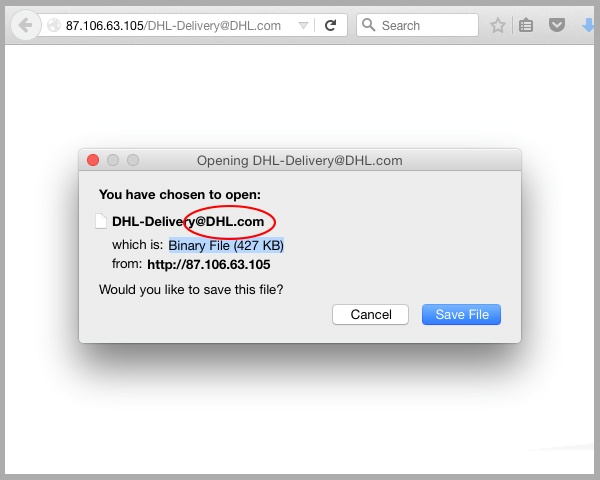
For those not familiar with the .COM file name extension, it is a simple, lightweight executable file.
There is nothing malicious about the COM extension, however, this scammer’s plan to trick the email recipient involves exploiting the name collision between the .com command file and .com TLD website address.
Unwary recipients that download the attachment expect to access the ‘DHL.com’ website, but instead run the malicious binary file. As a result, they give the cybercriminal permission to do whatever they please with their machine.
Whilst malware attached to emails can be stopped effectively by email filters, this variation of scam emails bypasses filters by indirectly delivering malware via a redirected URL.
High pressure businesses can be left exposed to scams like this as they can easily overlook insignificant features like the ‘from’ sender address. This simple oversight is what spammers exploit, it only takes a moment of inattention or a lack of vigilance to be infiltrated.
To find out more about the $500 billion worth of damage cyber criminals cause annually, click here.
As a precaution, we urge you not to click links within emails that:
- Are not addressed to you by name, have poor English or omit personal details that a legitimate sender would include (e.g. – tracking ID).
- Are from businesses that you were not expecting to hear from.
- Ask you to download any files, namely with an .exe file extension, or in this case, a .com extension.
- Take you to a landing page or website that does not have the legitimate URL of the company the email is purporting to be sent from
Educating staff and employing cloud-based email and web filtering is your first and best line of defence. Compliment this multilayered defence with on premise antivirus, anti-malware and anti-spyware solutions. This will go a long way to mitigating the risk from a wide range of email scams
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







