MailGuard have identified and successfully blocked a recent run of email phishing attacks purporting to be from PayPal targeting PayPal users.
If these targeted attacks prove successful, the victim is vulnerable to having their PayPal account hijacked, their credit card credentials used to make fraudulent purchases and their identity stolen.
Here are some screenshots of two variations to watch out for:
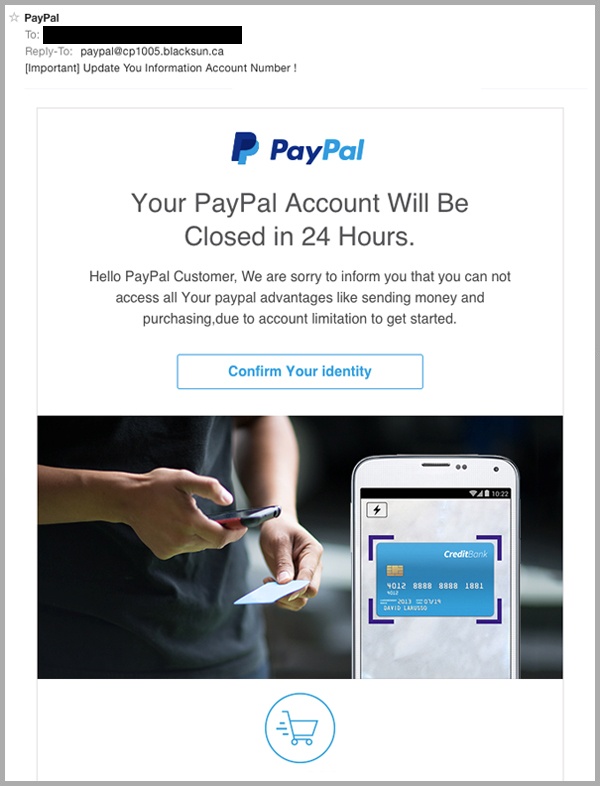
As you can see, the email originates from the sender address, ‘paypal@cp1005.blacksun.ca’, and requires the recipient to confirm their identity in order to avoid having their account closed in 24 hours.
As this particular variation has poor grammar, is impersonal and is obviously sent via an unofficial sender address; it’s fairly easy to determine its inauthenticity.
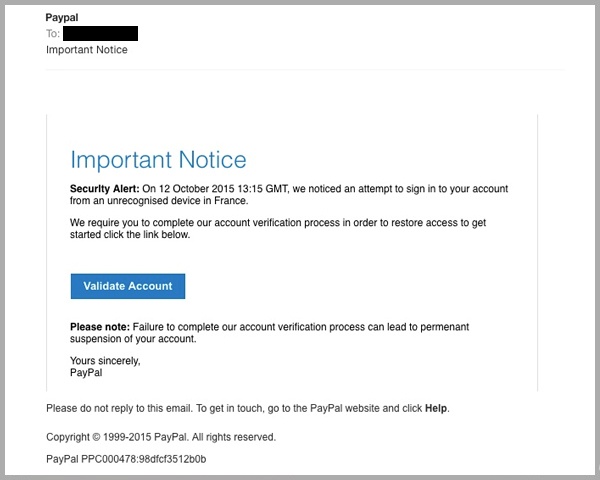
As you can see, variation two is more sophisticated.
The sender, purporting to be “PayPal”, alerts the recipient of an “Important Notice”, in which an unrecognised device has supposedly been used to log in to their PayPal account from an unusual location.
The logical flow of this scam makes sense, as the recipient is required to “Validate [their] Account” in order to restore access.
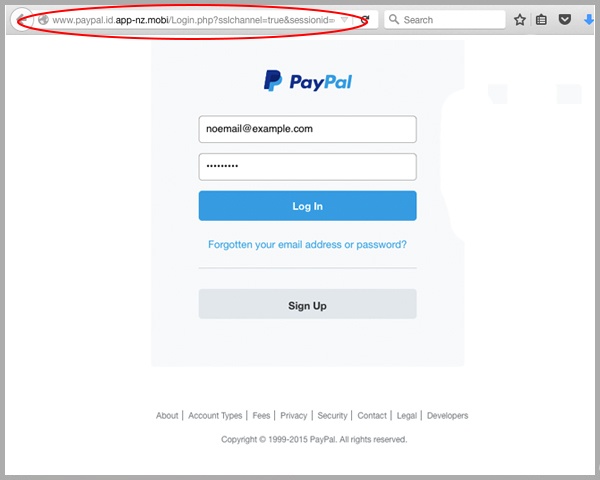
Upon clicking the “Validate Account” button above, the victim is directed to an exact replica of the PayPal login page, besides the unofficial URL highlighted in the website address field above, www.paypal.id.app-nz.mobi.
Upon entering and submitting their details via this fraudulent login page, the user is directed to the following landing page.
At this point, the user has left their account vulnerable to infiltration handing their PayPal login credentials over to the cybercriminal, but there’s more bad news to come.
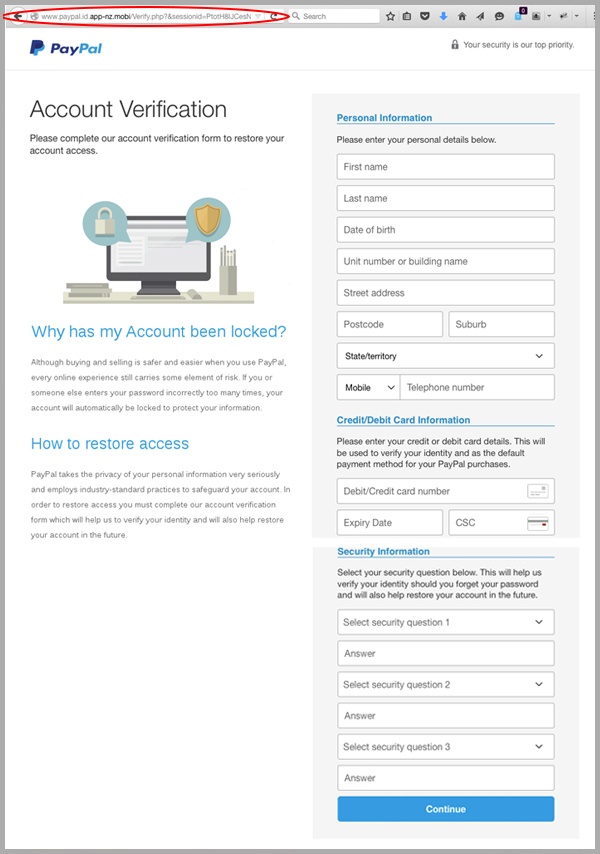
As you can see above, this is a very detailed fake account verification process.
The cybercriminals intend to lure the victim into completing the entire form to gain access to:
- Their PayPal account and any associated accounts that share the same username and password combination.
- Residential information which can be sold to telemarketers, or segmented by other cyber criminals into lists that be targeted when orchestrating future attacks.
- Their credit/debit card information to be used for fraudulent online (and offline) purchases.
- Security information which can be used to fraudulently gain access to a number of related accounts (bank accounts, government issued accounts).
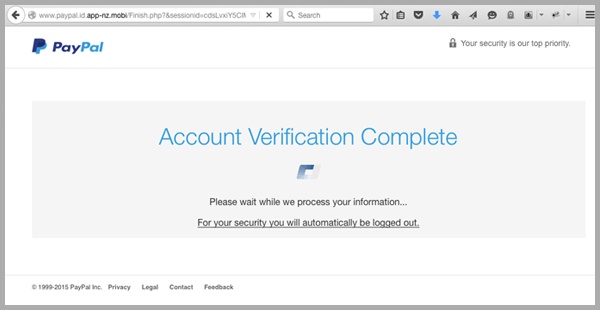
Upon completing and submitting this final form, the victim’s details are processed via a fake “Account Verification Complete” page.
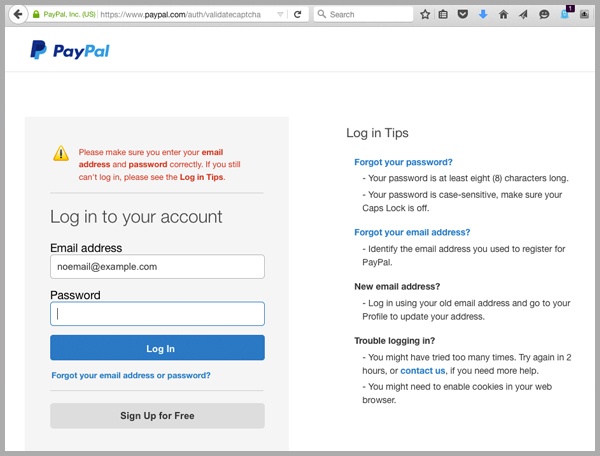
They are then redirected to a legitimate PayPal landing page led to believe that there may have been a bug in their failure to verify their account. They are prompted to log in again, none the wiser.
- As a precaution, we urge you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from.
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from. If you are ever unsure of an email that requires you to log into your account, head to the official website of the purported company to access your account as precaution.
PayPal users have been hit particularly hard by zero day phishing threats, here is another variation we have reported on to remain vigilant against.
National Cybersecurity Awareness Month kicked off earlier last week - the initiative is designed to create a culture of cybersecurity at work. Here is some further information via Naked Security on how to identify and defend your network against email phishing attacks.
Educating staff and employing cloud-based email and web filtering is your first and best line of defence. Compliment this multilayered defence with on premise antivirus, anti-malware and anti-spyware solutions. This will go a long way to mitigating the risk from a wide range of email scams.
Keep up to date on the latest email scams by subscribing to MailGuard’s weekly update or follow us on social media.







