Another fake Google phishing email is currently in circulation, manipulating readers into surrendering access to their email accounts.
MailGuard first blocked this threat yesterday afternoon - 20 hours later, only one other reputable security provider – from a list of 67 – was recognising it as being malicious.
In a similar way to another recent Google scam, the scammers leverage Google’s online storage platform, Google Drive, in order to persuade victims into giving away their email username and password details.
A sample of the email you should look out for is shown below:
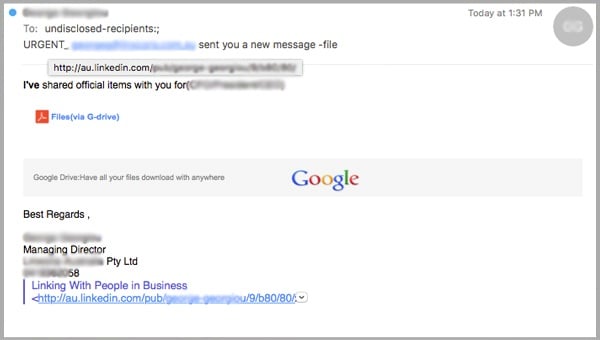
The Google phishing email originates from a named sender, whose identity we’ve hidden to protect them, but we’ll call him Simon.
Simon’s email account has been hacked into by the cyber criminal – he is likely to have received the same Google Drive phishing email recently and clicked through, surrendering his username and password details.
By gaining access to Simon’s account, the scammer has then been able to distribute spam on his behalf, sending this Google scam to the contacts in his address book, purporting to be Simon.
As Simon’s address book contacts are likely to be friends, acquaintance or colleagues, they are more likely to trust the email’s legitimacy, making the scam more successful.
A detailed email signature includes his full name, company, job title, phone number, and even a direct link to his LinkedIn profile, all of which the cyber criminals has garnered by hacking into his email account.
As you can see, the email invites the recipient to open a file which has been shared by ‘Simon’ using Google Drive, the online storage platform.
Once the reader has clicked on the file, they are then taken to a landing page which invites them to sign in using their email username and password details – in the background is a blurred image of the ‘file’ that the reader is supposedly going to gain access to:
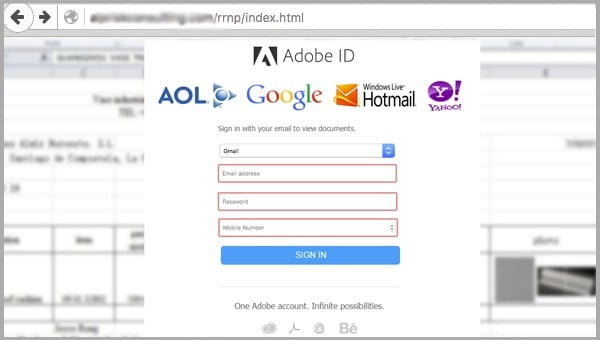
The URL in the address bar bears no reference to Google, although we’ve had to blank it out as it’s a legitimate third-party web domain that the cyber criminal has hacked into.
The user is given the opportunity to sign in using a number of different email providers, including AOL, Gmail and Hotmail, something which Google Drive would not normally allow you to do.
Once the reader has submitted their details and clicked “Sign in”, these details are then captured automatically by the cyber criminal, and the user is directed to a blank page, where the scam then ends.
The scammer now has access to the reader’s email account, which they can use to distribute the scam further and gain access to key information used to steal their identity.
How to recognise phishing emails
You can reduce the likelihood of being impacted by phishing emails like this Google scam by being wary of content which asks you to view documents out of the blue, especially where the user doesn’t explain their purpose or subject.
Make sure you study the URL in the landing page – in this case it bears no relation to Google, so is clearly a scam.
Also be on the lookout for other tell-tale signs of phishing scams, especially where the sender allows you to do things not normally allowed – for example being able to log-in using details from multiple email providers – a typical approach used to widen their phishing net.
You can stop phishing emails from getting into your inbox in the first place by implementing cloud-based email filtering technology, which will successfully protect your business from damage.
While the majority of other security providers are still yet to block this Google phishing scam, MailGuard’s cloud technology successfully blocked it immediately, in real-time.
If you’re experiencing problems, you can speak to a cloud security specialist on 1300 30 44 30 or email expert@mailguard.com.au
Keep up to date with email scams affecting your business by subscribing to MailGuard’s weekly update.







