A Google Docs phishing scam has been successfully blocked by MailGuard’s email filtering software, following another similar recent attack.
This email phishing scam takes advantage of the reader’s familiarity with the Google brand, inviting them to surrender their email account details and open themselves up to identity theft.
Here is a screenshot of the type of email to watch out for:
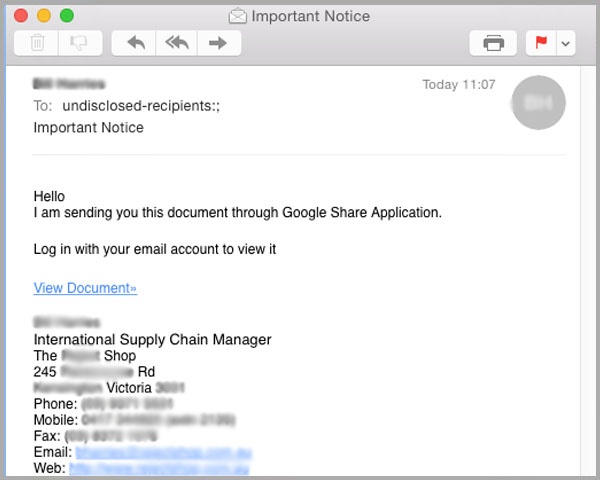
In the example above the email originates from a named sender (we’ve blanked out their details to protect their identity, but let’s call him ‘Rob’).
Rob’s email account appears to have been compromised – it’s likely that he recently received the same Google phishing email from someone within his address book whose account was also recently hacked.
Rob is likely to have fallen for the scam and surrendered his email account details, allowing the scammer to distribute spam using his email account including those known to him in his address book.
When Rob's contacts receive this email they are likely to trust its content – being a friend, acquaintance or colleague.
The apparent legitimacy of the Google phishing email is improved by a detailed signature, providing his full name, job title, address, telephone number and website details which the spammer is likely to have garnered through unauthorised access to his account.
The email content encourages readers to view an enclosed document, accessed through ‘Google Share Application’.
Clicking on the blue ‘View Document’ hyperlink takes the reader to a phishing website, which looks like a legitimate Google login screen, shown below:
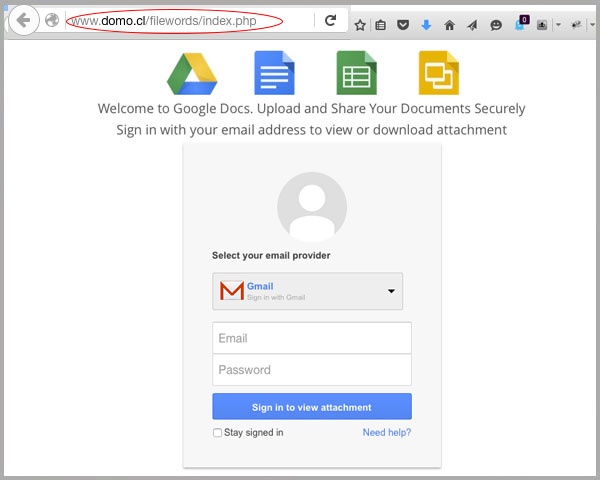
More vigilant readers would notice the illegitimate URL in the address bar, which has no direct reference to Google.
The user is then asked to sign in order to download the document, and is given the option of providing credentials of alternative webmail providers including Hotmail and Yahoo.
Again, more vigilant recipients might know that a legitimate Google site would not allow you to access Google Docs without using a Gmail user account, thereby alerting them to the scam.
Once the user has selected their email provider, entered their details and clicked the blue “Sign in to view attachment” button, they are then taken to a verification landing page, show below.
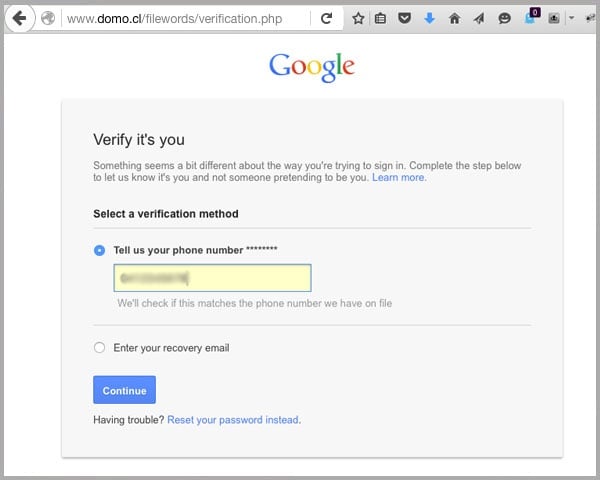
This verification page is a direct replica of Google’s official credential verification page, again strengthening the legitimacy of this online phishing scam.
Here the user is directed to provide their phone number or recovery email address, before pressing ‘Continue’.
The recipient is finally redirected to the Google+ homepage – increasing the campaign's authenticity further – but never has the opportunity to view the document they were originally promised.
In the meantime, the scammer now has access to the user’s webmail username and password, telephone number or recovery email address, giving full access to their email account, which they can then use to access confidential information.
It’s also likely that their account will be used to distribute this Google phishing email to a wider range of targets, while making them part of other new spam scams.
How to prevent phishing attacks
- Be wary of emails which invite you to view unexplained documents – you’d normally expect a friend or colleague to describe why they want you to view something, and what’s enclosed.
- Study the URL - you should be able to immediately identify this scam with a quick check of the URL of the fake Google landing pages.
- Use common sense - this Google phishing email scam offers a dropdown selection of email service providers before providing access to a secure Google document. You’d never be able to sign into a Hotmail account through a Google login page, would you?
You can find out more tips for identifying fake emails here.
Educating staff and employing cloud-based email filtering and web filtering, complimented by multilayered defences including desktop antivirus, anti-malware and anti-spyware will go a long way to protecting you from a wide range of phishing emails, as well as web-borne malware attacks.
Keep up to date with email scams affecting your business by subscribing to MailGuard’s weekly update.







