Organisations have again been the target of a number of spear phishing attacks this week, which MailGuard has successfully blocked.
Spear phishing attacks have grown rapidly recently, manipulating members of staff into making huge wire fund transfers to cyber criminals by purporting to be a known colleague.
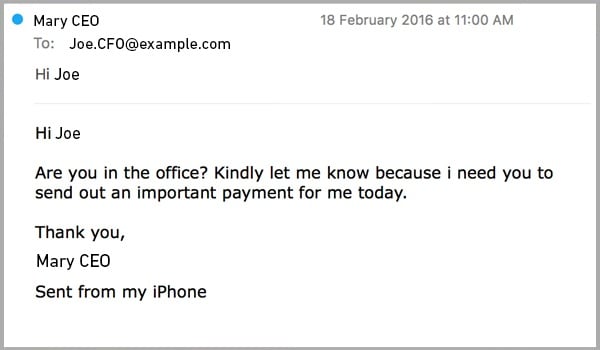
Below is an example of a spear phishing email we’ve seen this week:
In the examples provided, we’ve changed the recipient and ‘sender’ details to protect their identity, but as you can see, the email appears to come from the CEO, asking the CFO to make an urgent payment.
With the ever-increasing availability of personal and work-related information online, including social media use, cyber criminals are able to identify members within organisations within the finance or accounts team, who might normally make payments, and senior members of staff who they are likely to respond to quickly.
By successfully forging the “header from” address in the email settings, the cyber criminal is able to make the email appear to come from the organisation's CEO; they will often also forge a businesses’ email signature to make the email seem more legitimate too.
Another example of a spear phishing email we blocked this week is shown below:
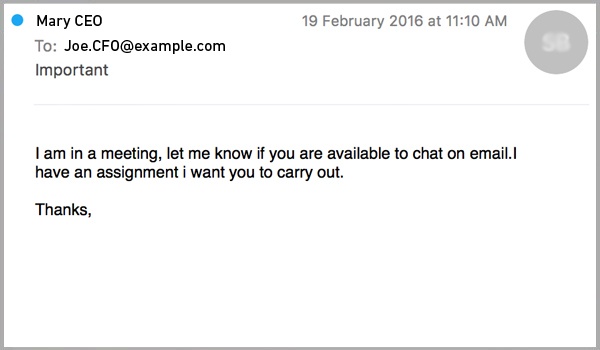
Again the premise is similar – the cyber criminal uses social engineering techniques to create a sense of urgency, making the recipient act quickly.
However this time they don’t immediately mention the need for a payment to be made in their initial email, but attempt to ‘hook’ the recipient into further private conversation, where their ‘assignment’ will be further revealed.
In the third example we’ve seen this week, shown below, we see the cyber criminal being even coyer:
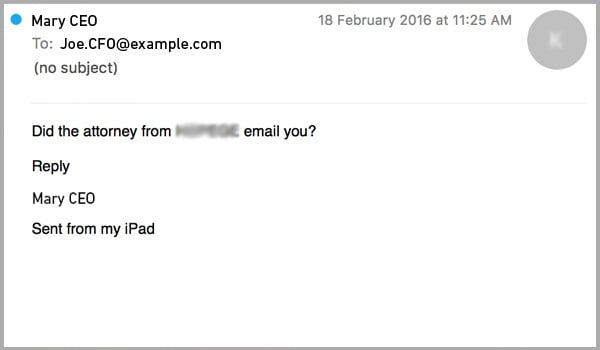
Here he tries to lure the recipient into conversation by invoking an inquisitive response. For example, the recipient might respond saying “No I haven’t heard from him, why?”, to which the cyber criminal might respond:
“He wanted us to bring forward a payment that’s owing on our account, would you be able to process it for me?”.
The cyber criminal will then provide a fake invoice or just the named bank account with which to transfer the money, and once the transaction’s been processed, that’s it – it’s both untraceable and irrecoverable.
In Australia, there have been spear phishing examples where staff members have transferred values of around $1.5m into cyber-criminals’ bank accounts.
Spear phishing statistics show that more than 91% of enterprises are now reporting incidents, affecting organisations in over 80 countries worldwide, according to the FBI.
Protecting against spear phishing attacks
With the sophistication of attacks increasing every day, it’s really important that your business takes additional steps to protect itself.
It’s important that you train staff to:
- Immediately be wary of emails requesting something out of the ordinary, even if the email appears to originate from a known colleague
- Be particularly wary of wire fund transfer requests, especially if they ask you to transfer money into foreign bank accounts
- Always call the person in question to clarify their request – but avoid using the number in the signature of the email, as this is likely to have been forged using the cyber-criminals details.
By investing in a premium email filtering solution, you can effectively identify and block a range of spear phishing emails before they get into your inbox.
Premium providers carefully analyse the tactics used by cyber criminals in spear phishing attacks, implementing rules which reduce the likelihood of these emails from appearing in front of staff.
Sign up below to our weekly scam updates, which will include our new spear phishing guide, coming soon, giving you all the information you’ll need to identify and defend against a spear phishing attack.







