Using business documents, including contracts, legal documents and finance records, as trojan horses to deliver cyber-attacks continues to be a popular technique among cybercriminals looking to trick users.
MailGuard has intercepted a phishing email impersonating popular file-sharing service, WeTransfer.
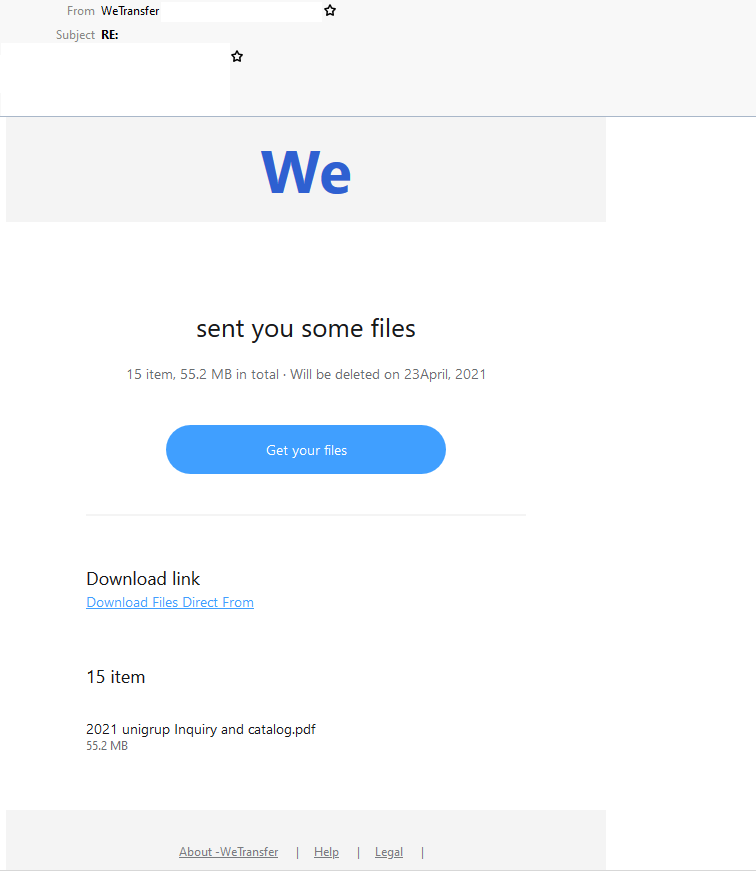
Masquerading as a file-sharing alert, the email uses a display name of ‘WeTransfer’. However, the domain used in the sender address provided in the ‘From:’ field doesn’t belong to the company – a red flag pointing to the email’s illegitimacy. The email actually originates from a rather generic domain registered by Tucows. The email body informs recipients that they have been sent some files in the form of a .PDF. A link is provided to download the files, along with a few details such as their size and file name. Recipients are also informed that the files will be ‘deleted on 23April, 2021’.
Here’s what the email looks like:
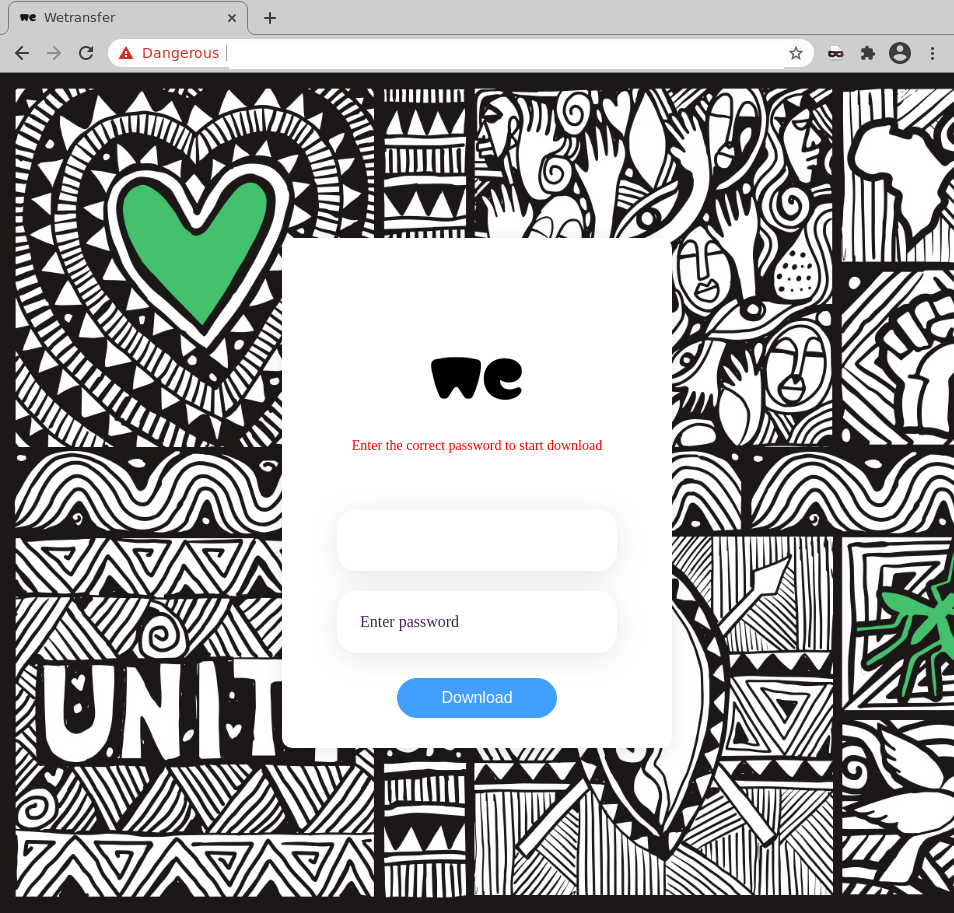
Unsuspecting recipients who click on the link are led to a login page, asking for the user’s username and password. This page employs multiple branding elements belonging to WeTransfer, including its logo. However, the domain used in the page’s URL doesn’t belong to the company. This is actually a phishing page that appears to be a compromised website. It is registered with GoDaddy and hosted using Amazon AWS.
Here’s a screenshot of the page:
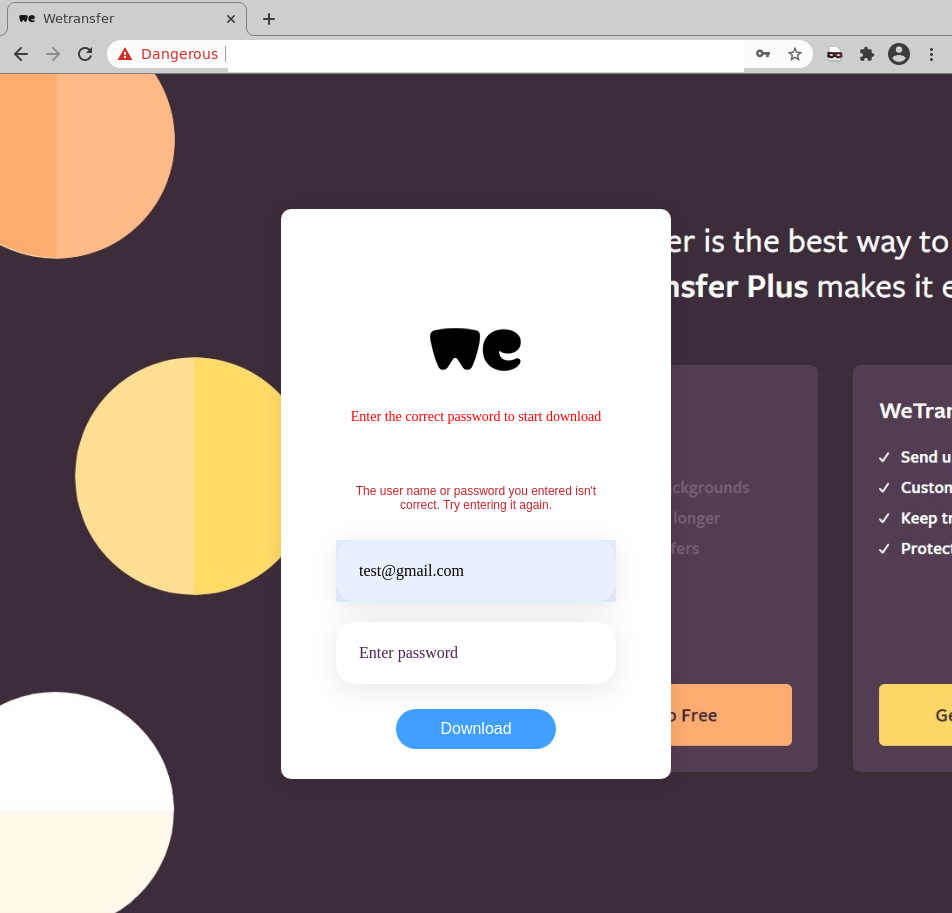
Upon ‘logging in’ and clicking on the link to ‘download file’, users’ credentials are harvested by the cybercriminals behind the scam. Users are then shown a response stating the password entered is incorrect, as per the below:
We strongly advise all recipients to delete these emails immediately without clicking on any links. Please share this alert with your social media network to help us spread the word around this email scam.
Cybercriminals frequently exploit the branding of global companies like WeTransfer in their scams, because their good reputation lulls victims into a false sense of security, and with such a large number of users they are an easy and attractive target. In addition, using a file-sharing notification to trick users is another trick employed by cybercriminals to avoid detection. With more employees working remotely since the COVID-10 pandemic, it’s common for professionals to share confidential business documents with one another via email, so notifications like this one aren’t likely to raise too much suspicion.
Several techniques have been employed in this particular email scam to convince recipients of its legitimacy, including the usage of high-quality graphical elements in the phishing page, such as WeTransfer’s branding & logo. Cybercriminals have also incorporated screenshots taken from an actual WeTransfer page that rotate through on the background of the phishing page. All this serves to elicit a more confident response from recipients who think they are, in fact, viewing a document from the popular file-sharing service.
This email also attempts to intrigue; telling the recipient that a new file has arrived creates a sense of curiosity. In addition, by including details like file size and the email address of the sender, the email boosts its credibility, motivating recipients to think there actually is a legitimate file being sent by someone. Plus, the presence of a file expiry date sparks urgency, encouraging the recipient to click on the provided link right away, distracting them from checking the sending address of the email and looking out for any other errors.
However, eagle-eyed recipients would notice several red flags that point to the email’s illegitimacy. For example, the email doesn’t address the recipient directly, and that the email contains awkward spacing and formatting errors.
WeTransfer lists the following advice in its support page:
“We'll never request the following information from you, and we'll never contact you out of the blue in order to:
- confirm your email address or other account credentials such as passwords
- ask you to download a transfer from a download link
- provide your full card number, or other payment details
- we don't provide phone support, so we will never ever call you about WeTransfer.
For any questions about emails, or if you think you have received a phishing/suspicious email, please contact our Support team to report it. Make sure to include the email in question as an attachment, or forward it.”
As a precaution, MailGuard urges you not to click links within emails that:
- Are not addressed to you by name.
- Appear to be from a legitimate company but use poor English, or omit personal details that a legitimate sender would include.
- Are from businesses that you were not expecting to hear from, and
- Take you to a landing page or website that is not the legitimate URL of the company the email is purporting to be sent from.
One email is all that it takes
All that it takes to break into your business is a cleverly-worded email message. If scammers can trick one person in your company into clicking on a malicious link they can gain access to your data.
For a few dollars per staff member per month, you can protect your business with MailGuard's predictive and advanced email security.
Talk to a solution consultant at MailGuard today about securing your company's network.
Why not stay up-to-date with MailGuard's latest blog posts by subscribing to free updates? Subscribe to weekly updates by clicking on the button below.







